how2heap是由shellphish团队制作的堆利用教程,介绍了多种堆利用技术,后续系列实验我们就通过这个教程来学习。环境可参见从零开始配置pwn环境:从零开始配置pwn环境:从零开始配置pwn环境:优化pwn虚拟机配置支持libc等指令-CSDN博客
1.fastbins的overlapping_chunks攻击
这是一个简单的堆块重叠问题,首先申请 3 个 chunk
这三个 chunk 分别申请到了:
p1:0x603010
p2:0x603110
p3:0x603210
给他们分别填充"1""2""3"
free 掉 p2
p2 被放到 unsorted bin 中
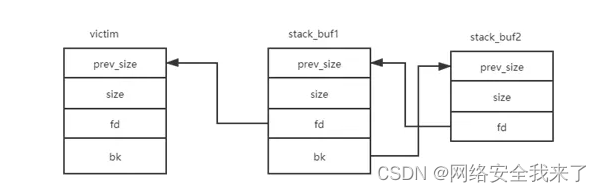
现在假设有一个堆溢出漏洞,可以覆盖 p2
为了保证堆块稳定性,我们至少需要让 prev_inuse 为 1,确保 p1 不会被认为是空闲的堆块
我们将 p2 的大小设置为 385, 这样的话我们就能用 376 大小的空间
现在让我们分配另一个块,其大小等于块p2注入大小的数据大小
malloc 将会把前面 free 的 p2 分配给我们(p2 的 size 已经被改掉了)
p4 分配在 0x603110 到 0x603288 这一区域
p3 从 0x603210 到 0x603288
p4 应该与 p3 重叠,在这种情况下 p4 包括所有 p3
这时候通过编辑 p4 就可以修改 p3 的内容,修改 p3 也可以修改 p4 的内容
2.overlapping_chunks演示程序
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <stdint.h>
int main(int argc , char* argv[]){
intptr_t *p1,*p2,*p3,*p4;
fprintf(stderr, "这是一个简单的堆块重叠问题,首先申请 3 个 chunk\n");
p1 = malloc(0x100 - 8);
p2 = malloc(0x100 - 8);
p3 = malloc(0x80 - 8);
fprintf(stderr, "这三个 chunk 分别申请到了:\np1:%p\np2:%p\np3:%p\n给他们分别填充\"1\"\"2\"\"3\"\n\n", p1, p2, p3);
memset(p1, '1', 0x100 - 8);
memset(p2, '2', 0x100 - 8);
memset(p3, '3', 0x80 - 8);
fprintf(stderr, "free 掉 p2\n");
free(p2);
fprintf(stderr, "p2 被放到 unsorted bin 中\n");
fprintf(stderr, "现在假设有一个堆溢出漏洞,可以覆盖 p2\n");
fprintf(stderr, "为了保证堆块稳定性,我们至少需要让 prev_inuse 为 1,确保 p1 不会被认为是空闲的堆块\n");
int evil_chunk_size = 0x181;
int evil_region_size = 0x180 - 8;
fprintf(stderr, "我们将 p2 的大小设置为 %d, 这样的话我们就能用 %d 大小的空间\n",evil_chunk_size, evil_region_size);
*(p2-1) = evil_chunk_size; // 覆盖 p2 的 size
fprintf(stderr, "\n现在让我们分配另一个块,其大小等于块p2注入大小的数据大小\n");
fprintf(stderr, "malloc 将会把前面 free 的 p2 分配给我们(p2 的 size 已经被改掉了)\n");
p4 = malloc(evil_region_size);
fprintf(stderr, "\np4 分配在 %p 到 %p 这一区域\n", (char *)p4, (char *)p4+evil_region_size);
fprintf(stderr, "p3 从 %p 到 %p\n", (char *)p3, (char *)p3+0x80-8);
fprintf(stderr, "p4 应该与 p3 重叠,在这种情况下 p4 包括所有 p3\n");
fprintf(stderr, "这时候通过编辑 p4 就可以修改 p3 的内容,修改 p3 也可以修改 p4 的内容\n\n");
fprintf(stderr, "接下来验证一下,现在 p3 与 p4:\n");
fprintf(stderr, "p4 = %s\n", (char *)p4+0x10);
fprintf(stderr, "p3 = %s\n", (char *)p3+0x10);
fprintf(stderr, "\n如果我们使用 memset(p4, '4', %d), 将会:\n", evil_region_size);
memset(p4, '4', evil_region_size);
fprintf(stderr, "p4 = %s\n", (char *)p4+0x10);
fprintf(stderr, "p3 = %s\n", (char *)p3+0x10);
fprintf(stderr, "\n那么之后再 memset(p3, '3', 80), 将会:\n");
memset(p3, '3', 80);
fprintf(stderr, "p4 = %s\n", (char *)p4+0x10);
fprintf(stderr, "p3 = %s\n", (char *)p3+0x10);
} 3.调试overlapping_chunks
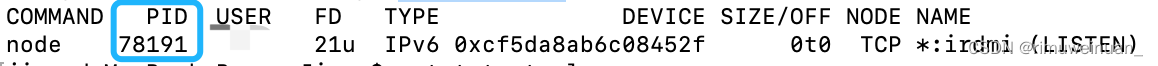
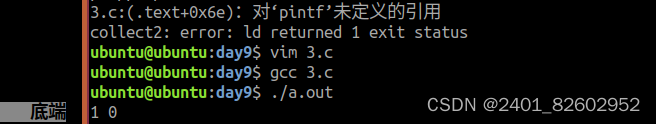
3.1 获得可执行程序
gcc -g overlapping_chunks.c -o overlapping_chunks
3.2 第一次调试程序
root@pwn_test1604:/ctf/work/how2heap# gcc -g overlapping_chunks.c -o overlapping_chunks
root@pwn_test1604:/ctf/work/how2heap# ll
total 232
drwxr-xr-x 2 1000 1000 4096 Feb 12 01:24 ./
drwxr-xr-x 12 1000 1000 4096 Feb 8 13:06 ../
-rwxr-xr-x 1 root root 11168 Feb 9 02:26 fastbin_dup*
-rw-r--r-- 1 1000 1000 1383 Feb 9 02:25 fastbin_dup.c
-rwxr-xr-x 1 root root 11176 Feb 10 03:42 fastbin_dup_consolidate*
-rw-r--r-- 1 1000 1000 957 Feb 10 03:27 fastbin_dup_consolidate.c
-rwxr-xr-x 1 root root 15432 Feb 9 04:05 fastbin_dup_into_stack*
-rw-r--r-- 1 1000 1000 2124 Feb 9 03:52 fastbin_dup_into_stack.c
-rwx--x--x 1 1000 1000 15224 Feb 8 13:26 first_fit*
-rwxr-xr-x 1 root root 21408 Feb 8 15:02 first_fit1*
-rw-r--r-- 1 1000 1000 1591 Feb 8 13:16 first_fit.c
-rw------- 1 root root 12944 Feb 12 01:13 .gdb_history
-rwxr-xr-x 1 root root 15744 Feb 11 13:15 house_of_lore*
-rw-r--r-- 1 1000 1000 2794 Feb 11 13:15 house_of_lore.c
-rwxr-xr-x 1 root root 11240 Feb 11 03:43 house_of_spirit*
-rw-r--r-- 1 1000 1000 1575 Feb 11 03:43 house_of_spirit.c
-rwxr-xr-x 1 root root 15512 Feb 12 01:24 overlapping_chunks*
-rw-r--r-- 1 1000 1000 2929 Feb 12 01:23 overlapping_chunks.c
-rwxr-xr-x 1 root root 15624 Feb 11 04:37 poison_null_byte*
-rw-r--r-- 1 1000 1000 2853 Feb 11 04:36 poison_null_byte.c
-rwxr-xr-x 1 root root 10176 Feb 8 15:20 uaf*
-rw-r--r-- 1 1000 1000 1023 Feb 8 15:19 uaf.c
-rwxr-xr-x 1 root root 15544 Feb 10 05:39 unsafe_unlink*
-rw-r--r-- 1 1000 1000 2965 Feb 10 05:39 unsafe_unlink.c
root@pwn_test1604:/ctf/work/how2heap# gdb ./overlapping_chunks
GNU gdb (Ubuntu 7.11.1-0ubuntu1~16.5) 7.11.1
Copyright (C) 2016 Free Software Foundation, Inc.
License GPLv3+: GNU GPL version 3 or later <http://gnu.org/licenses/gpl.html>
This is free software: you are free to change and redistribute it.
There is NO WARRANTY, to the extent permitted by law. Type "show copying"
and "show warranty" for details.
This GDB was configured as "x86_64-linux-gnu".
Type "show configuration" for configuration details.
For bug reporting instructions, please see:
<http://www.gnu.org/software/gdb/bugs/>.
Find the GDB manual and other documentation resources online at:
<http://www.gnu.org/software/gdb/documentation/>.
For help, type "help".
Type "apropos word" to search for commands related to "word"...
pwndbg: loaded 171 commands. Type pwndbg [filter] for a list.
pwndbg: created $rebase, $ida gdb functions (can be used with print/break)
Reading symbols from ./overlapping_chunks...done.
pwndbg> r
Starting program: /ctf/work/how2heap/overlapping_chunks
这是一个简单的堆块重叠问题,首先申请 3 个 chunk
这三个 chunk 分别申请到了:
p1:0x603010
p2:0x603110
p3:0x603210
给他们分别填充"1""2""3"
free 掉 p2
p2 被放到 unsorted bin 中
现在假设有一个堆溢出漏洞,可以覆盖 p2
为了保证堆块稳定性,我们至少需要让 prev_inuse 为 1,确保 p1 不会被认为是空闲的堆块
我们将 p2 的大小设置为 385, 这样的话我们就能用 376 大小的空间
现在让我们分配另一个块,其大小等于块p2注入大小的数据大小
malloc 将会把前面 free 的 p2 分配给我们(p2 的 size 已经被改掉了)
p4 分配在 0x603110 到 0x603288 这一区域
p3 从 0x603210 到 0x603288
p4 应该与 p3 重叠,在这种情况下 p4 包括所有 p3
这时候通过编辑 p4 就可以修改 p3 的内容,修改 p3 也可以修改 p4 的内容
接下来验证一下,现在 p3 与 p4:
p4 = 22222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222
p3 = 33333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333�
如果我们使用 memset(p4, '4', 376), 将会:
p4 = 444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444�
p3 = 44444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444�
那么之后再 memset(p3, '3', 80), 将会:
p4 = 444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444333333333333333333333333333333333333333333333333333333333333333333333333333333334444444444444444444444444444444444444444�
p3 = 33333333333333333333333333333333333333333333333333333333333333334444444444444444444444444444444444444444�
[Inferior 1 (process 114) exited normally]
pwndbg>
3.3 第二次调试程序
3.3.1 设置断点第14行并走起
这个比较简单,就是堆块重叠的问题。通过一个溢出漏洞,改写unsorted bin 中空闲堆块的size,改变下一次malloc可以返回的堆块大小。
直接动手调试,首先申请三个堆块。
pwndbg> b 14
Breakpoint 2 at 0x4006dd: file overlapping_chunks.c, line 14.
pwndbg> c
Continuing.
这是一个简单的堆块重叠问题,首先申请 3 个 chunk
Breakpoint 2, main (argc=1, argv=0x7fffffffe6a8) at overlapping_chunks.c:14
14 fprintf(stderr, "这三个 chunk 分别申请到了:\np1:%p\np2:%p\np3:%p\n给他们分别填充\"1\"\"2\"\"3\"\n\n", p1, p2, p3);
LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
───────────────────────────────────────────────────────────────────────────────────────────────────[ REGISTERS ]───────────────────────────────────────────────────────────────────────────────────────────────────
RAX 0x603210 ◂— 0x0
RBX 0x0
RCX 0x7ffff7dd1b20 (main_arena) ◂— 0x100000000
RDX 0x603210 ◂— 0x0
RDI 0x0
RSI 0x603280 ◂— 0x0
R8 0x603000 ◂— 0x0
R9 0xd
R10 0x7ffff7dd1b78 (main_arena+88) —▸ 0x603280 ◂— 0x0
R11 0x0
R12 0x400590 (_start) ◂— xor ebp, ebp
R13 0x7fffffffe6a0 ◂— 0x1
R14 0x0
R15 0x0
RBP 0x7fffffffe5c0 —▸ 0x400a40 (__libc_csu_init) ◂— push r15
RSP 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
RIP 0x4006dd (main+87) ◂— mov rax, qword ptr [rip + 0x20197c]
────────────────────────────────────────────────────────────────────────────────────────────────────[ DISASM ]─────────────────────────────────────────────────────────────────────────────────────────────────────
► 0x4006dd <main+87> mov rax, qword ptr [rip + 0x20197c] <0x602060>
0x4006e4 <main+94> mov rsi, qword ptr [rbp - 0x10]
0x4006e8 <main+98> mov rcx, qword ptr [rbp - 0x18]
0x4006ec <main+102> mov rdx, qword ptr [rbp - 0x20]
0x4006f0 <main+106> mov r8, rsi
0x4006f3 <main+109> mov esi, 0x400b10
0x4006f8 <main+114> mov rdi, rax
0x4006fb <main+117> mov eax, 0
0x400700 <main+122> call fprintf@plt <0x400550>
0x400705 <main+127> mov rax, qword ptr [rbp - 0x20]
0x400709 <main+131> mov edx, 0xf8
─────────────────────────────────────────────────────────────────────────────────────────────────[ SOURCE (CODE) ]─────────────────────────────────────────────────────────────────────────────────────────────────
In file: /ctf/work/how2heap/overlapping_chunks.c
9 fprintf(stderr, "这是一个简单的堆块重叠问题,首先申请 3 个 chunk\n");
10
11 p1 = malloc(0x100 - 8);
12 p2 = malloc(0x100 - 8);
13 p3 = malloc(0x80 - 8);
► 14 fprintf(stderr, "这三个 chunk 分别申请到了:\np1:%p\np2:%p\np3:%p\n给他们分别填充\"1\"\"2\"\"3\"\n\n", p1, p2, p3);
15
16 memset(p1, '1', 0x100 - 8);
17 memset(p2, '2', 0x100 - 8);
18 memset(p3, '3', 0x80 - 8);
19
─────────────────────────────────────────────────────────────────────────────────────────────────────[ STACK ]─────────────────────────────────────────────────────────────────────────────────────────────────────
00:0000│ rsp 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
01:0008│ 0x7fffffffe588 ◂— 0x100400a8d
02:0010│ 0x7fffffffe590 ◂— 0x0
... ↓
04:0020│ 0x7fffffffe5a0 —▸ 0x603010 ◂— 0x0
05:0028│ 0x7fffffffe5a8 —▸ 0x603110 ◂— 0x0
06:0030│ 0x7fffffffe5b0 —▸ 0x603210 ◂— 0x0
07:0038│ 0x7fffffffe5b8 ◂— 0x0
───────────────────────────────────────────────────────────────────────────────────────────────────[ BACKTRACE ]───────────────────────────────────────────────────────────────────────────────────────────────────
► f 0 4006dd main+87
f 1 7ffff7a2d830 __libc_start_main+240
Breakpoint /ctf/work/how2heap/overlapping_chunks.c:14
pwndbg> n
这三个 chunk 分别申请到了:
p1:0x603010
p2:0x603110
p3:0x603210
给他们分别填充"1""2""3"
16 memset(p1, '1', 0x100 - 8);
LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
───────────────────────────────────────────────────────────────────────────────────────────────────[ REGISTERS ]───────────────────────────────────────────────────────────────────────────────────────────────────
RAX 0x6e
RBX 0x0
RCX 0x7ffff7b042c0 (__write_nocancel+7) ◂— cmp rax, -0xfff
RDX 0x7ffff7dd3770 (_IO_stdfile_2_lock) ◂— 0x0
RDI 0x2
RSI 0x7fffffffbef0 ◂— 0xb8e489b8e499bfe8
R8 0x7ffff7feb700 ◂— 0x7ffff7feb700
R9 0x6e
R10 0x0
R11 0x246
R12 0x400590 (_start) ◂— xor ebp, ebp
R13 0x7fffffffe6a0 ◂— 0x1
R14 0x0
R15 0x0
RBP 0x7fffffffe5c0 —▸ 0x400a40 (__libc_csu_init) ◂— push r15
RSP 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
RIP 0x400705 (main+127) ◂— mov rax, qword ptr [rbp - 0x20]
────────────────────────────────────────────────────────────────────────────────────────────────────[ DISASM ]─────────────────────────────────────────────────────────────────────────────────────────────────────
0x4006f0 <main+106> mov r8, rsi
0x4006f3 <main+109> mov esi, 0x400b10
0x4006f8 <main+114> mov rdi, rax
0x4006fb <main+117> mov eax, 0
0x400700 <main+122> call fprintf@plt <0x400550>
► 0x400705 <main+127> mov rax, qword ptr [rbp - 0x20]
0x400709 <main+131> mov edx, 0xf8
0x40070e <main+136> mov esi, 0x31
0x400713 <main+141> mov rdi, rax
0x400716 <main+144> call memset@plt <0x400530>
0x40071b <main+149> mov rax, qword ptr [rbp - 0x18]
─────────────────────────────────────────────────────────────────────────────────────────────────[ SOURCE (CODE) ]─────────────────────────────────────────────────────────────────────────────────────────────────
In file: /ctf/work/how2heap/overlapping_chunks.c
11 p1 = malloc(0x100 - 8);
12 p2 = malloc(0x100 - 8);
13 p3 = malloc(0x80 - 8);
14 fprintf(stderr, "这三个 chunk 分别申请到了:\np1:%p\np2:%p\np3:%p\n给他们分别填充\"1\"\"2\"\"3\"\n\n", p1, p2, p3);
15
► 16 memset(p1, '1', 0x100 - 8);
17 memset(p2, '2', 0x100 - 8);
18 memset(p3, '3', 0x80 - 8);
19
20 fprintf(stderr, "free 掉 p2\n");
21 free(p2);
─────────────────────────────────────────────────────────────────────────────────────────────────────[ STACK ]─────────────────────────────────────────────────────────────────────────────────────────────────────
00:0000│ rsp 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
01:0008│ 0x7fffffffe588 ◂— 0x100400a8d
02:0010│ 0x7fffffffe590 ◂— 0x0
... ↓
04:0020│ 0x7fffffffe5a0 —▸ 0x603010 ◂— 0x0
05:0028│ 0x7fffffffe5a8 —▸ 0x603110 ◂— 0x0
06:0030│ 0x7fffffffe5b0 —▸ 0x603210 ◂— 0x0
07:0038│ 0x7fffffffe5b8 ◂— 0x0
───────────────────────────────────────────────────────────────────────────────────────────────────[ BACKTRACE ]───────────────────────────────────────────────────────────────────────────────────────────────────
► f 0 400705 main+127
f 1 7ffff7a2d830 __libc_start_main+240
pwndbg> parseheap
addr prev size status fd bk
0x603000 0x0 0x100 Used None None
0x603100 0x0 0x100 Used None None
0x603200 0x0 0x80 Used None None
pwndbg>
3.3.2 设置断点第22行并走起
接着free掉p2,这时候p2被放到unsorted bin中。
pwndbg> b 22
Breakpoint 3 at 0x400771: file overlapping_chunks.c, line 22.
pwndbg> c
Continuing.
free 掉 p2
Breakpoint 3, main (argc=1, argv=0x7fffffffe6a8) at overlapping_chunks.c:22
22 fprintf(stderr, "p2 被放到 unsorted bin 中\n");
LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
───────────────────────────────────────────────────────────────────────────────────────────────────[ REGISTERS ]───────────────────────────────────────────────────────────────────────────────────────────────────
RAX 0x1
RBX 0x0
RCX 0x7ffff7b042c0 (__write_nocancel+7) ◂— cmp rax, -0xfff
RDX 0x0
RDI 0x7ffff7dd1b20 (main_arena) ◂— 0x100000000
RSI 0x0
R8 0xc
R9 0x1
R10 0x8b8
R11 0x7ffff7a914f0 (free) ◂— push r13
R12 0x400590 (_start) ◂— xor ebp, ebp
R13 0x7fffffffe6a0 ◂— 0x1
R14 0x0
R15 0x0
RBP 0x7fffffffe5c0 —▸ 0x400a40 (__libc_csu_init) ◂— push r15
RSP 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
RIP 0x400771 (main+235) ◂— mov rax, qword ptr [rip + 0x2018e8]
────────────────────────────────────────────────────────────────────────────────────────────────────[ DISASM ]─────────────────────────────────────────────────────────────────────────────────────────────────────
► 0x400771 <main+235> mov rax, qword ptr [rip + 0x2018e8] <0x602060>
0x400778 <main+242> mov rcx, rax
0x40077b <main+245> mov edx, 0x1e
0x400780 <main+250> mov esi, 1
0x400785 <main+255> mov edi, 0x400b80
0x40078a <main+260> call fwrite@plt <0x400570>
0x40078f <main+265> mov rax, qword ptr [rip + 0x2018ca] <0x602060>
0x400796 <main+272> mov rcx, rax
0x400799 <main+275> mov edx, 0x37
0x40079e <main+280> mov esi, 1
0x4007a3 <main+285> mov edi, 0x400ba0
─────────────────────────────────────────────────────────────────────────────────────────────────[ SOURCE (CODE) ]─────────────────────────────────────────────────────────────────────────────────────────────────
In file: /ctf/work/how2heap/overlapping_chunks.c
17 memset(p2, '2', 0x100 - 8);
18 memset(p3, '3', 0x80 - 8);
19
20 fprintf(stderr, "free 掉 p2\n");
21 free(p2);
► 22 fprintf(stderr, "p2 被放到 unsorted bin 中\n");
23
24 fprintf(stderr, "现在假设有一个堆溢出漏洞,可以覆盖 p2\n");
25 fprintf(stderr, "为了保证堆块稳定性,我们至少需要让 prev_inuse 为 1,确保 p1 不会被认为是空闲的堆块\n");
26
27 int evil_chunk_size = 0x181;
─────────────────────────────────────────────────────────────────────────────────────────────────────[ STACK ]─────────────────────────────────────────────────────────────────────────────────────────────────────
00:0000│ rsp 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
01:0008│ 0x7fffffffe588 ◂— 0x100400a8d
02:0010│ 0x7fffffffe590 ◂— 0x0
... ↓
04:0020│ 0x7fffffffe5a0 —▸ 0x603010 ◂— 0x3131313131313131 ('11111111')
05:0028│ 0x7fffffffe5a8 —▸ 0x603110 —▸ 0x7ffff7dd1b78 (main_arena+88) —▸ 0x603280 ◂— 0x3333333333333333 ('33333333')
06:0030│ 0x7fffffffe5b0 —▸ 0x603210 ◂— 0x3333333333333333 ('33333333')
07:0038│ 0x7fffffffe5b8 ◂— 0x0
───────────────────────────────────────────────────────────────────────────────────────────────────[ BACKTRACE ]───────────────────────────────────────────────────────────────────────────────────────────────────
► f 0 400771 main+235
f 1 7ffff7a2d830 __libc_start_main+240
Breakpoint /ctf/work/how2heap/overlapping_chunks.c:22
pwndbg> biin
Undefined command: "biin". Try "help".
pwndbg> bins
fastbins
0x20: 0x0
0x30: 0x0
0x40: 0x0
0x50: 0x0
0x60: 0x0
0x70: 0x0
0x80: 0x0
unsortedbin
all: 0x603100 —▸ 0x7ffff7dd1b78 (main_arena+88) ◂— 0x603100
smallbins
empty
largebins
empty
pwndbg>
pwndbg> bins
fastbins
0x20: 0x0
0x30: 0x0
0x40: 0x0
0x50: 0x0
0x60: 0x0
0x70: 0x0
0x80: 0x0
unsortedbin
all: 0x603100 —▸ 0x7ffff7dd1b78 (main_arena+88) ◂— 0x603100
smallbins
empty
largebins
empty
3.3.3 设置断点第39行并走起
然后把p2的size改成0x180,这时候就把p3给包含进去了。
pwndbg> c
Continuing.
我们将 p2 的大小设置为 385, 这样的话我们就能用 376 大小的空间
Breakpoint 5, main (argc=1, argv=0x7fffffffe6a8) at overlapping_chunks.c:31
31 *(p2-1) = evil_chunk_size; // 覆盖 p2 的 size
LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
───────────────────────────────────────────────────────────────────────────────────────────────────[ REGISTERS ]───────────────────────────────────────────────────────────────────────────────────────────────────
RAX 0x55
RBX 0x0
RCX 0x7ffff7b042c0 (__write_nocancel+7) ◂— cmp rax, -0xfff
RDX 0x7ffff7dd3770 (_IO_stdfile_2_lock) ◂— 0x0
RDI 0x2
RSI 0x7fffffffbef0 ◂— 0xb0e5acbbe49188e6
R8 0x7ffff7feb700 ◂— 0x7ffff7feb700
R9 0x55
R10 0x0
R11 0x246
R12 0x400590 (_start) ◂— xor ebp, ebp
R13 0x7fffffffe6a0 ◂— 0x1
R14 0x0
R15 0x0
RBP 0x7fffffffe5c0 —▸ 0x400a40 (__libc_csu_init) ◂— push r15
RSP 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
RIP 0x4007f8 (main+370) ◂— mov rax, qword ptr [rbp - 0x18]
────────────────────────────────────────────────────────────────────────────────────────────────────[ DISASM ]─────────────────────────────────────────────────────────────────────────────────────────────────────
0x4007e3 <main+349> mov edx, dword ptr [rbp - 0x28]
0x4007e6 <main+352> mov esi, 0x400c50
0x4007eb <main+357> mov rdi, rax
0x4007ee <main+360> mov eax, 0
0x4007f3 <main+365> call fprintf@plt <0x400550>
► 0x4007f8 <main+370> mov rax, qword ptr [rbp - 0x18]
0x4007fc <main+374> lea rdx, [rax - 8]
0x400800 <main+378> mov eax, dword ptr [rbp - 0x28]
0x400803 <main+381> cdqe
0x400805 <main+383> mov qword ptr [rdx], rax
0x400808 <main+386> mov rax, qword ptr [rip + 0x201851] <0x602060>
─────────────────────────────────────────────────────────────────────────────────────────────────[ SOURCE (CODE) ]─────────────────────────────────────────────────────────────────────────────────────────────────
In file: /ctf/work/how2heap/overlapping_chunks.c
26
27 int evil_chunk_size = 0x181;
28 int evil_region_size = 0x180 - 8;
29 fprintf(stderr, "我们将 p2 的大小设置为 %d, 这样的话我们就能用 %d 大小的空间\n",evil_chunk_size, evil_region_size);
30
► 31 *(p2-1) = evil_chunk_size; // 覆盖 p2 的 size
32
33 fprintf(stderr, "\n现在让我们分配另一个块,其大小等于块p2注入大小的数据大小\n");
34 fprintf(stderr, "malloc 将会把前面 free 的 p2 分配给我们(p2 的 size 已经被改掉了)\n");
35 p4 = malloc(evil_region_size);
36
─────────────────────────────────────────────────────────────────────────────────────────────────────[ STACK ]─────────────────────────────────────────────────────────────────────────────────────────────────────
00:0000│ rsp 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
01:0008│ 0x7fffffffe588 ◂— 0x100400a8d
02:0010│ 0x7fffffffe590 ◂— 0x0
03:0018│ 0x7fffffffe598 ◂— 0x17800000181
04:0020│ 0x7fffffffe5a0 —▸ 0x603010 ◂— 0x3131313131313131 ('11111111')
05:0028│ 0x7fffffffe5a8 —▸ 0x603110 —▸ 0x7ffff7dd1b78 (main_arena+88) —▸ 0x603280 ◂— 0x3333333333333333 ('33333333')
06:0030│ 0x7fffffffe5b0 —▸ 0x603210 ◂— 0x3333333333333333 ('33333333')
07:0038│ 0x7fffffffe5b8 ◂— 0x0
───────────────────────────────────────────────────────────────────────────────────────────────────[ BACKTRACE ]───────────────────────────────────────────────────────────────────────────────────────────────────
► f 0 4007f8 main+370
f 1 7ffff7a2d830 __libc_start_main+240
Breakpoint /ctf/work/how2heap/overlapping_chunks.c:30
pwndbg> n
33 fprintf(stderr, "\n现在让我们分配另一个块,其大小等于块p2注入大小的数据大小\n");
LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
───────────────────────────────────────────────────────────────────────────────────────────────────[ REGISTERS ]───────────────────────────────────────────────────────────────────────────────────────────────────
RAX 0x181
RBX 0x0
RCX 0x7ffff7b042c0 (__write_nocancel+7) ◂— cmp rax, -0xfff
RDX 0x603108 ◂— 0x181
RDI 0x2
RSI 0x7fffffffbef0 ◂— 0xb0e5acbbe49188e6
R8 0x7ffff7feb700 ◂— 0x7ffff7feb700
R9 0x55
R10 0x0
R11 0x246
R12 0x400590 (_start) ◂— xor ebp, ebp
R13 0x7fffffffe6a0 ◂— 0x1
R14 0x0
R15 0x0
RBP 0x7fffffffe5c0 —▸ 0x400a40 (__libc_csu_init) ◂— push r15
RSP 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
RIP 0x400808 (main+386) ◂— mov rax, qword ptr [rip + 0x201851]
────────────────────────────────────────────────────────────────────────────────────────────────────[ DISASM ]─────────────────────────────────────────────────────────────────────────────────────────────────────
0x4007f8 <main+370> mov rax, qword ptr [rbp - 0x18]
0x4007fc <main+374> lea rdx, [rax - 8]
0x400800 <main+378> mov eax, dword ptr [rbp - 0x28]
0x400803 <main+381> cdqe
0x400805 <main+383> mov qword ptr [rdx], rax
► 0x400808 <main+386> mov rax, qword ptr [rip + 0x201851] <0x602060>
0x40080f <main+393> mov rcx, rax
0x400812 <main+396> mov edx, 0x55
0x400817 <main+401> mov esi, 1
0x40081c <main+406> mov edi, 0x400ca8
0x400821 <main+411> call fwrite@plt <0x400570>
─────────────────────────────────────────────────────────────────────────────────────────────────[ SOURCE (CODE) ]─────────────────────────────────────────────────────────────────────────────────────────────────
In file: /ctf/work/how2heap/overlapping_chunks.c
28 int evil_region_size = 0x180 - 8;
29 fprintf(stderr, "我们将 p2 的大小设置为 %d, 这样的话我们就能用 %d 大小的空间\n",evil_chunk_size, evil_region_size);
30
31 *(p2-1) = evil_chunk_size; // 覆盖 p2 的 size
32
► 33 fprintf(stderr, "\n现在让我们分配另一个块,其大小等于块p2注入大小的数据大小\n");
34 fprintf(stderr, "malloc 将会把前面 free 的 p2 分配给我们(p2 的 size 已经被改掉了)\n");
35 p4 = malloc(evil_region_size);
36
37 fprintf(stderr, "\np4 分配在 %p 到 %p 这一区域\n", (char *)p4, (char *)p4+evil_region_size);
38 fprintf(stderr, "p3 从 %p 到 %p\n", (char *)p3, (char *)p3+0x80-8);
─────────────────────────────────────────────────────────────────────────────────────────────────────[ STACK ]─────────────────────────────────────────────────────────────────────────────────────────────────────
00:0000│ rsp 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
01:0008│ 0x7fffffffe588 ◂— 0x100400a8d
02:0010│ 0x7fffffffe590 ◂— 0x0
03:0018│ 0x7fffffffe598 ◂— 0x17800000181
04:0020│ 0x7fffffffe5a0 —▸ 0x603010 ◂— 0x3131313131313131 ('11111111')
05:0028│ 0x7fffffffe5a8 —▸ 0x603110 —▸ 0x7ffff7dd1b78 (main_arena+88) —▸ 0x603280 ◂— 0x3333333333333333 ('33333333')
06:0030│ 0x7fffffffe5b0 —▸ 0x603210 ◂— 0x3333333333333333 ('33333333')
07:0038│ 0x7fffffffe5b8 ◂— 0x0
───────────────────────────────────────────────────────────────────────────────────────────────────[ BACKTRACE ]───────────────────────────────────────────────────────────────────────────────────────────────────
► f 0 400808 main+386
f 1 7ffff7a2d830 __libc_start_main+240
pwndbg> p p3
$1 = (intptr_t *) 0x603210
pwndbg> x/10gx 0x603210
0x603210: 0x3333333333333333 0x3333333333333333
0x603220: 0x3333333333333333 0x3333333333333333
0x603230: 0x3333333333333333 0x3333333333333333
0x603240: 0x3333333333333333 0x3333333333333333
0x603250: 0x3333333333333333 0x3333333333333333
pwndbg> p p2
$2 = (intptr_t *) 0x603110
pwndbg> bins
fastbins
0x20: 0x0
0x30: 0x0
0x40: 0x0
0x50: 0x0
0x60: 0x0
0x70: 0x0
0x80: 0x0
unsortedbin
all: 0x603100 —▸ 0x7ffff7dd1b78 (main_arena+88) ◂— 0x603100
smallbins
empty
largebins
empty
pwndbg> x/10gx 0x7ffff7dd1b78
0x7ffff7dd1b78 <main_arena+88>: 0x0000000000603280 0x0000000000000000
0x7ffff7dd1b88 <main_arena+104>: 0x0000000000603100 0x0000000000603100
0x7ffff7dd1b98 <main_arena+120>: 0x00007ffff7dd1b88 0x00007ffff7dd1b88
0x7ffff7dd1ba8 <main_arena+136>: 0x00007ffff7dd1b98 0x00007ffff7dd1b98
0x7ffff7dd1bb8 <main_arena+152>: 0x00007ffff7dd1ba8 0x00007ffff7dd1ba8
pwndbg> parseheap
addr prev size status fd bk
0x603000 0x0 0x100 Used None None
0x603100 0x3131313131313131 0x180 Used None None
pwndbg> x/10gx 0x603110
0x603110: 0x00007ffff7dd1b78 0x00007ffff7dd1b78
0x603120: 0x3232323232323232 0x3232323232323232
0x603130: 0x3232323232323232 0x3232323232323232
pwndbg> p p3
$1 = (intptr_t *) 0x603210
pwndbg> p p2
$2 = (intptr_t *) 0x603110
pwndbg> bins
fastbins
0x20: 0x0
0x30: 0x0
0x40: 0x0
0x50: 0x0
0x60: 0x0
0x70: 0x0
0x80: 0x0
unsortedbin
all: 0x603100 —▸ 0x7ffff7dd1b78 (main_arena+88) ◂— 0x603100
smallbins
empty
largebins
empty
pwndbg> parseheap
addr prev size status fd bk
0x603000 0x0 0x100 Used None None
0x603100 0x3131313131313131 0x180 Used None None
p2->fd
pwndbg> x/10gx 0x603110
0x603110: 0x00007ffff7dd1b78 0x00007ffff7dd1b78
p2->bk
pwndbg> x/10gx 0x603110
0x603110: 0x00007ffff7dd1b78 0x00007ffff7dd1b78
pwndbg> x/10gx 0x603110
0x603110: 0x00007ffff7dd1b78 0x00007ffff7dd1b78
0x603120: 0x3232323232323232 0x3232323232323232
0x603130: 0x3232323232323232 0x3232323232323232
0x603140: 0x3232323232323232 0x3232323232323232
0x603150: 0x3232323232323232 0x3232323232323232
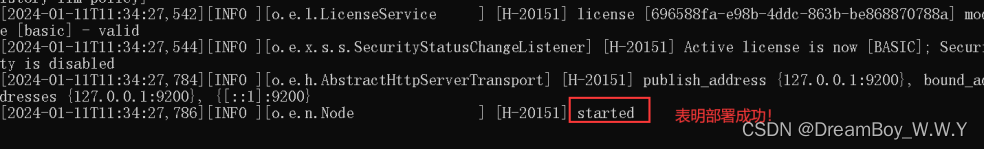
3.3.4 设置断点第52行并走起
然后再去申请一块大小为0x180的堆块p4,就能够编辑p4,就可以修改p3的内容,编辑p3也可以修改p4的内容。
pwndbg> b 51
Breakpoint 10 at 0x4009b6: file overlapping_chunks.c, line 51.
pwndbg> c
Continuing.
p3 = 44444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444�
Breakpoint 10, main (argc=1, argv=0x7fffffffe6a8) at overlapping_chunks.c:52
52 fprintf(stderr, "\n那么之后再 memset(p3, '3', 80), 将会:\n");
LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
───────────────────────────────────────────────────────────────────────────────────────────────────[ REGISTERS ]───────────────────────────────────────────────────────────────────────────────────────────────────
RAX 0x71
RBX 0x0
RCX 0x7ffff7b042c0 (__write_nocancel+7) ◂— cmp rax, -0xfff
RDX 0x7ffff7dd3770 (_IO_stdfile_2_lock) ◂— 0x0
RDI 0x2
RSI 0x7fffffffbef0 ◂— 0x343434203d203370 ('p3 = 444')
R8 0x7ffff7feb700 ◂— 0x7ffff7feb700
R9 0x71
R10 0x6b
R11 0x246
R12 0x400590 (_start) ◂— xor ebp, ebp
R13 0x7fffffffe6a0 ◂— 0x1
R14 0x0
R15 0x0
RBP 0x7fffffffe5c0 —▸ 0x400a40 (__libc_csu_init) ◂— push r15
RSP 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
RIP 0x4009b6 (main+816) ◂— mov rax, qword ptr [rip + 0x2016a3]
────────────────────────────────────────────────────────────────────────────────────────────────────[ DISASM ]─────────────────────────────────────────────────────────────────────────────────────────────────────
► 0x4009b6 <main+816> mov rax, qword ptr [rip + 0x2016a3] <0x602060>
0x4009bd <main+823> mov rcx, rax
0x4009c0 <main+826> mov edx, 0x2e
0x4009c5 <main+831> mov esi, 1
0x4009ca <main+836> mov edi, 0x400eb0
0x4009cf <main+841> call fwrite@plt <0x400570>
0x4009d4 <main+846> mov rax, qword ptr [rbp - 0x10]
0x4009d8 <main+850> mov edx, 0x50
0x4009dd <main+855> mov esi, 0x33
0x4009e2 <main+860> mov rdi, rax
0x4009e5 <main+863> call memset@plt <0x400530>
─────────────────────────────────────────────────────────────────────────────────────────────────[ SOURCE (CODE) ]─────────────────────────────────────────────────────────────────────────────────────────────────
In file: /ctf/work/how2heap/overlapping_chunks.c
47 fprintf(stderr, "\n如果我们使用 memset(p4, '4', %d), 将会:\n", evil_region_size);
48 memset(p4, '4', evil_region_size);
49 fprintf(stderr, "p4 = %s\n", (char *)p4+0x10);
50 fprintf(stderr, "p3 = %s\n", (char *)p3+0x10);
51
► 52 fprintf(stderr, "\n那么之后再 memset(p3, '3', 80), 将会:\n");
53 memset(p3, '3', 80);
54 fprintf(stderr, "p4 = %s\n", (char *)p4+0x10);
55 fprintf(stderr, "p3 = %s\n", (char *)p3+0x10);
56 }
─────────────────────────────────────────────────────────────────────────────────────────────────────[ STACK ]─────────────────────────────────────────────────────────────────────────────────────────────────────
00:0000│ rsp 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
01:0008│ 0x7fffffffe588 ◂— 0x100400a8d
02:0010│ 0x7fffffffe590 ◂— 0x0
03:0018│ 0x7fffffffe598 ◂— 0x17800000181
04:0020│ 0x7fffffffe5a0 —▸ 0x603010 ◂— 0x3131313131313131 ('11111111')
05:0028│ 0x7fffffffe5a8 —▸ 0x603110 ◂— 0x3434343434343434 ('44444444')
06:0030│ 0x7fffffffe5b0 —▸ 0x603210 ◂— 0x3434343434343434 ('44444444')
07:0038│ 0x7fffffffe5b8 —▸ 0x603110 ◂— 0x3434343434343434 ('44444444')
───────────────────────────────────────────────────────────────────────────────────────────────────[ BACKTRACE ]───────────────────────────────────────────────────────────────────────────────────────────────────
► f 0 4009b6 main+816
f 1 7ffff7a2d830 __libc_start_main+240
Breakpoint /ctf/work/how2heap/overlapping_chunks.c:51
pwndbg> parseheap
addr prev size status fd bk
0x603000 0x0 0x100 Used None None
0x603100 0x3131313131313131 0x180 Used None None
pwndbg> p p3
$3 = (intptr_t *) 0x603210
pwndbg> x/20gx 0x603210
0x603210: 0x3434343434343434 0x3434343434343434
0x603220: 0x3434343434343434 0x3434343434343434
0x603230: 0x3434343434343434 0x3434343434343434
0x603240: 0x3434343434343434 0x3434343434343434
0x603250: 0x3434343434343434 0x3434343434343434
0x603260: 0x3434343434343434 0x3434343434343434
0x603270: 0x3434343434343434 0x3434343434343434
0x603280: 0x3434343434343434 0x0000000000020d81
0x603290: 0x0000000000000000 0x0000000000000000
0x6032a0: 0x0000000000000000 0x0000000000000000
pwndbg> p p4
$4 = (intptr_t *) 0x603110
pwndbg> x/80gx 0x603110
0x603110: 0x3434343434343434 0x3434343434343434
0x603120: 0x3434343434343434 0x3434343434343434
0x603130: 0x3434343434343434 0x3434343434343434
0x603140: 0x3434343434343434 0x3434343434343434
0x603150: 0x3434343434343434 0x3434343434343434
0x603160: 0x3434343434343434 0x3434343434343434
0x603170: 0x3434343434343434 0x3434343434343434
0x603180: 0x3434343434343434 0x3434343434343434
0x603190: 0x3434343434343434 0x3434343434343434
0x6031a0: 0x3434343434343434 0x3434343434343434
0x6031b0: 0x3434343434343434 0x3434343434343434
0x6031c0: 0x3434343434343434 0x3434343434343434
0x6031d0: 0x3434343434343434 0x3434343434343434
0x6031e0: 0x3434343434343434 0x3434343434343434
0x6031f0: 0x3434343434343434 0x3434343434343434
0x603200: 0x3434343434343434 0x3434343434343434
0x603210: 0x3434343434343434 0x3434343434343434
0x603220: 0x3434343434343434 0x3434343434343434
0x603230: 0x3434343434343434 0x3434343434343434
0x603240: 0x3434343434343434 0x3434343434343434
0x603250: 0x3434343434343434 0x3434343434343434
0x603260: 0x3434343434343434 0x3434343434343434
0x603270: 0x3434343434343434 0x3434343434343434
0x603280: 0x3434343434343434 0x0000000000020d81
0x603290: 0x0000000000000000 0x0000000000000000
0x6032a0: 0x0000000000000000 0x0000000000000000
0x6032b0: 0x0000000000000000 0x0000000000000000
0x6032c0: 0x0000000000000000 0x0000000000000000
0x6032d0: 0x0000000000000000 0x0000000000000000
0x6032e0: 0x0000000000000000 0x0000000000000000
0x6032f0: 0x0000000000000000 0x0000000000000000
0x603300: 0x0000000000000000 0x0000000000000000
0x603310: 0x0000000000000000 0x0000000000000000
0x603320: 0x0000000000000000 0x0000000000000000
0x603330: 0x0000000000000000 0x0000000000000000
0x603340: 0x0000000000000000 0x0000000000000000
0x603350: 0x0000000000000000 0x0000000000000000
0x603360: 0x0000000000000000 0x0000000000000000
0x603370: 0x0000000000000000 0x0000000000000000
0x603380: 0x0000000000000000 0x0000000000000000
pwndbg>
接下来验证一下,现在 p3 与 p4:
p4 = 22222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222222
p3 = 33333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333�
如果我们使用 memset(p4, '4', 376), 将会:
p4 = 444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444�
p3 = 44444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444�
3.3.5 设置断点第54行并走起
pwndbg> b 54
Breakpoint 12 at 0x4009ea: file overlapping_chunks.c, line 54.
pwndbg> c
Continuing.
那么之后再 memset(p3, '3', 80), 将会:
Breakpoint 12, main (argc=1, argv=0x7fffffffe6a8) at overlapping_chunks.c:54
54 fprintf(stderr, "p4 = %s\n", (char *)p4+0x10);
LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
───────────────────────────────────────────────────────────────────────────────────────────────────[ REGISTERS ]───────────────────────────────────────────────────────────────────────────────────────────────────
RAX 0x603210 ◂— 0x3333333333333333 ('33333333')
RBX 0x0
RCX 0x7ffff7b042c0 (__write_nocancel+7) ◂— cmp rax, -0xfff
RDX 0x50
RDI 0x603210 ◂— 0x3333333333333333 ('33333333')
RSI 0x603260 ◂— 0x3434343434343434 ('44444444')
R8 0x2e
R9 0x7ffff7dd2540 (_IO_2_1_stderr_) ◂— 0xfbad2887
R10 0x1
R11 0x246
R12 0x400590 (_start) ◂— xor ebp, ebp
R13 0x7fffffffe6a0 ◂— 0x1
R14 0x0
R15 0x0
RBP 0x7fffffffe5c0 —▸ 0x400a40 (__libc_csu_init) ◂— push r15
RSP 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
RIP 0x4009ea (main+868) ◂— mov rax, qword ptr [rbp - 8]
────────────────────────────────────────────────────────────────────────────────────────────────────[ DISASM ]─────────────────────────────────────────────────────────────────────────────────────────────────────
0x4009d4 <main+846> mov rax, qword ptr [rbp - 0x10]
0x4009d8 <main+850> mov edx, 0x50
0x4009dd <main+855> mov esi, 0x33
0x4009e2 <main+860> mov rdi, rax
0x4009e5 <main+863> call memset@plt <0x400530>
► 0x4009ea <main+868> mov rax, qword ptr [rbp - 8]
0x4009ee <main+872> lea rdx, [rax + 0x10]
0x4009f2 <main+876> mov rax, qword ptr [rip + 0x201667] <0x602060>
0x4009f9 <main+883> mov esi, 0x400e63
0x4009fe <main+888> mov rdi, rax
0x400a01 <main+891> mov eax, 0
─────────────────────────────────────────────────────────────────────────────────────────────────[ SOURCE (CODE) ]─────────────────────────────────────────────────────────────────────────────────────────────────
In file: /ctf/work/how2heap/overlapping_chunks.c
49 fprintf(stderr, "p4 = %s\n", (char *)p4+0x10);
50 fprintf(stderr, "p3 = %s\n", (char *)p3+0x10);
51
52 fprintf(stderr, "\n那么之后再 memset(p3, '3', 80), 将会:\n");
53 memset(p3, '3', 80);
► 54 fprintf(stderr, "p4 = %s\n", (char *)p4+0x10);
55 fprintf(stderr, "p3 = %s\n", (char *)p3+0x10);
56 }
─────────────────────────────────────────────────────────────────────────────────────────────────────[ STACK ]─────────────────────────────────────────────────────────────────────────────────────────────────────
00:0000│ rsp 0x7fffffffe580 —▸ 0x7fffffffe6a8 —▸ 0x7fffffffe8d1 ◂— '/ctf/work/how2heap/overlapping_chunks'
01:0008│ 0x7fffffffe588 ◂— 0x100400a8d
02:0010│ 0x7fffffffe590 ◂— 0x0
03:0018│ 0x7fffffffe598 ◂— 0x17800000181
04:0020│ 0x7fffffffe5a0 —▸ 0x603010 ◂— 0x3131313131313131 ('11111111')
05:0028│ 0x7fffffffe5a8 —▸ 0x603110 ◂— 0x3434343434343434 ('44444444')
06:0030│ 0x7fffffffe5b0 —▸ 0x603210 ◂— 0x3333333333333333 ('33333333')
07:0038│ 0x7fffffffe5b8 —▸ 0x603110 ◂— 0x3434343434343434 ('44444444')
───────────────────────────────────────────────────────────────────────────────────────────────────[ BACKTRACE ]───────────────────────────────────────────────────────────────────────────────────────────────────
► f 0 4009ea main+868
f 1 7ffff7a2d830 __libc_start_main+240
Breakpoint /ctf/work/how2heap/overlapping_chunks.c:54
pwndbg> p p3
$5 = (intptr_t *) 0x603210
pwndbg> x/80gx 0x603210
0x603210: 0x3333333333333333 0x3333333333333333
0x603220: 0x3333333333333333 0x3333333333333333
0x603230: 0x3333333333333333 0x3333333333333333
0x603240: 0x3333333333333333 0x3333333333333333
0x603250: 0x3333333333333333 0x3333333333333333
0x603260: 0x3434343434343434 0x3434343434343434
0x603270: 0x3434343434343434 0x3434343434343434
0x603280: 0x3434343434343434 0x0000000000020d81
0x603290: 0x0000000000000000 0x0000000000000000
0x6032a0: 0x0000000000000000 0x0000000000000000
0x6032b0: 0x0000000000000000 0x0000000000000000
0x6032c0: 0x0000000000000000 0x0000000000000000
0x6032d0: 0x0000000000000000 0x0000000000000000
0x6032e0: 0x0000000000000000 0x0000000000000000
0x6032f0: 0x0000000000000000 0x0000000000000000
0x603300: 0x0000000000000000 0x0000000000000000
0x603310: 0x0000000000000000 0x0000000000000000
0x603320: 0x0000000000000000 0x0000000000000000
0x603330: 0x0000000000000000 0x0000000000000000
0x603340: 0x0000000000000000 0x0000000000000000
0x603350: 0x0000000000000000 0x0000000000000000
0x603360: 0x0000000000000000 0x0000000000000000
0x603370: 0x0000000000000000 0x0000000000000000
0x603380: 0x0000000000000000 0x0000000000000000
0x603390: 0x0000000000000000 0x0000000000000000
0x6033a0: 0x0000000000000000 0x0000000000000000
0x6033b0: 0x0000000000000000 0x0000000000000000
0x6033c0: 0x0000000000000000 0x0000000000000000
0x6033d0: 0x0000000000000000 0x0000000000000000
0x6033e0: 0x0000000000000000 0x0000000000000000
0x6033f0: 0x0000000000000000 0x0000000000000000
0x603400: 0x0000000000000000 0x0000000000000000
0x603410: 0x0000000000000000 0x0000000000000000
0x603420: 0x0000000000000000 0x0000000000000000
0x603430: 0x0000000000000000 0x0000000000000000
0x603440: 0x0000000000000000 0x0000000000000000
0x603450: 0x0000000000000000 0x0000000000000000
0x603460: 0x0000000000000000 0x0000000000000000
0x603470: 0x0000000000000000 0x0000000000000000
0x603480: 0x0000000000000000 0x0000000000000000
pwndbg> p p4
$6 = (intptr_t *) 0x603110
pwndbg> x/80gx 0x603110
0x603110: 0x3434343434343434 0x3434343434343434
0x603120: 0x3434343434343434 0x3434343434343434
0x603130: 0x3434343434343434 0x3434343434343434
0x603140: 0x3434343434343434 0x3434343434343434
0x603150: 0x3434343434343434 0x3434343434343434
0x603160: 0x3434343434343434 0x3434343434343434
0x603170: 0x3434343434343434 0x3434343434343434
0x603180: 0x3434343434343434 0x3434343434343434
0x603190: 0x3434343434343434 0x3434343434343434
0x6031a0: 0x3434343434343434 0x3434343434343434
0x6031b0: 0x3434343434343434 0x3434343434343434
0x6031c0: 0x3434343434343434 0x3434343434343434
0x6031d0: 0x3434343434343434 0x3434343434343434
0x6031e0: 0x3434343434343434 0x3434343434343434
0x6031f0: 0x3434343434343434 0x3434343434343434
0x603200: 0x3434343434343434 0x3434343434343434
0x603210: 0x3333333333333333 0x3333333333333333
0x603220: 0x3333333333333333 0x3333333333333333
0x603230: 0x3333333333333333 0x3333333333333333
0x603240: 0x3333333333333333 0x3333333333333333
0x603250: 0x3333333333333333 0x3333333333333333
0x603260: 0x3434343434343434 0x3434343434343434
0x603270: 0x3434343434343434 0x3434343434343434
0x603280: 0x3434343434343434 0x0000000000020d81
0x603290: 0x0000000000000000 0x0000000000000000
0x6032a0: 0x0000000000000000 0x0000000000000000
0x6032b0: 0x0000000000000000 0x0000000000000000
0x6032c0: 0x0000000000000000 0x0000000000000000
0x6032d0: 0x0000000000000000 0x0000000000000000
0x6032e0: 0x0000000000000000 0x0000000000000000
0x6032f0: 0x0000000000000000 0x0000000000000000
0x603300: 0x0000000000000000 0x0000000000000000
0x603310: 0x0000000000000000 0x0000000000000000
0x603320: 0x0000000000000000 0x0000000000000000
0x603330: 0x0000000000000000 0x0000000000000000
0x603340: 0x0000000000000000 0x0000000000000000
0x603350: 0x0000000000000000 0x0000000000000000
0x603360: 0x0000000000000000 0x0000000000000000
0x603370: 0x0000000000000000 0x0000000000000000
0x603380: 0x0000000000000000 0x0000000000000000
pwndbg>
那么之后再 memset(p3, '3', 80), 将会:
p4 = 444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444444333333333333333333333333333333333333333333333333333333333333333333333333333333334444444444444444444444444444444444444444�
p3 = 33333333333333333333333333333333333333333333333333333333333333334444444444444444444444444444444444444444�