下载地址:Prime (2021): 2 ~ VulnHub
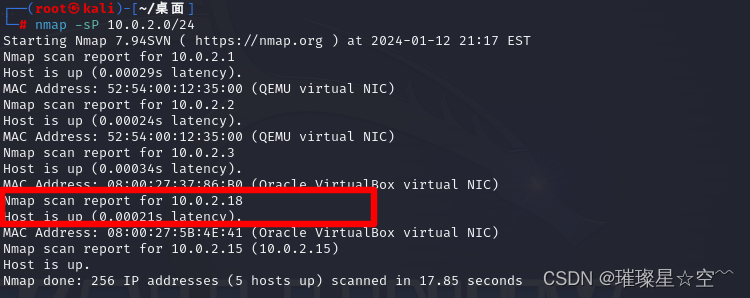
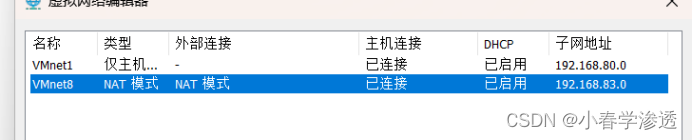
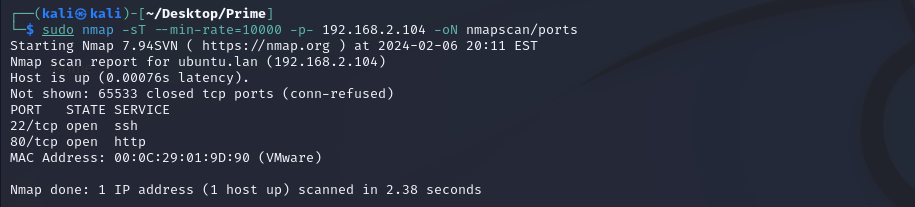
主机发现

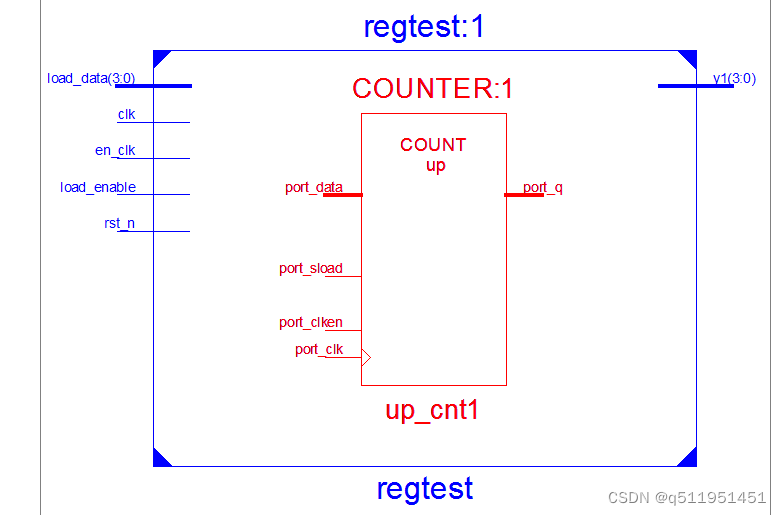
目标145
端口扫描

端口服务扫描


漏洞扫描


先去看一下80

扫目录

发现点不一样的
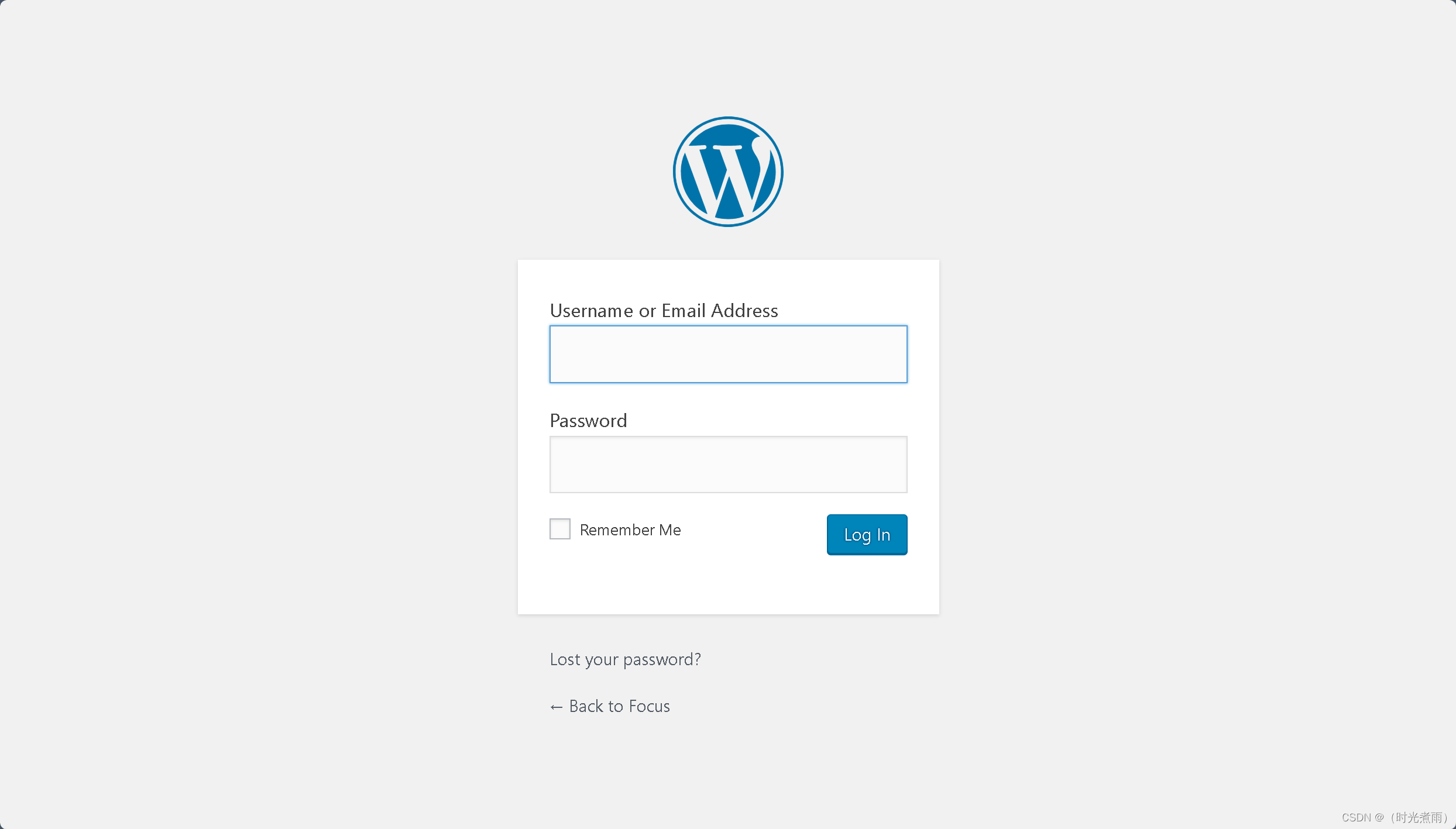
Wordpress(记住还是要用api)


好洞出来了看看利用方法


成了,这边没什么线索了。去另外一个web看看

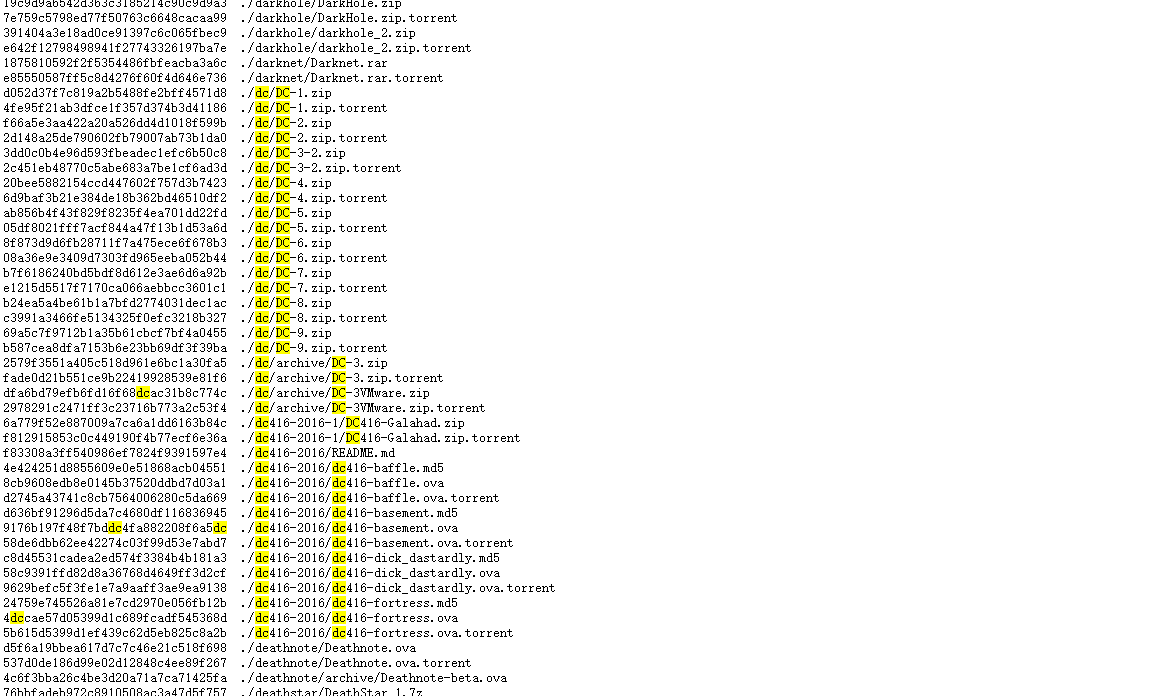
看看文件一个一个看吧


在uploads里面


一句话木马

反弹shell


写入成功

包含shell

Smb去看一下,一直没用,肯定有用



连

直接ssh密钥生成



远程登入

免密登入成功


啥也没有


构建
新的文件上传就可以



进容器

结束


![[<span style='color:red;'>Vulnhub</span><span style='color:red;'>靶机</span>] DriftingBlues: <span style='color:red;'>2</span>](https://img-blog.csdnimg.cn/20602181a98c4db6ad45166bd74993a0.png)

![[<span style='color:red;'>VulnHub</span><span style='color:red;'>靶机</span>渗透] Kioptrix1.<span style='color:red;'>2</span>](https://img-blog.csdnimg.cn/direct/0139ef298e064bdaa7a170ab9d14668a.png)


















![[Verilog] 设计方法和设计流程](https://img-blog.csdnimg.cn/direct/eac6daee28624849bf54c0c879c15a5b.png)









![[Verilog] Verilog 简介](https://img-blog.csdnimg.cn/direct/a4c3303d1b87416097961c0132421c2b.png)