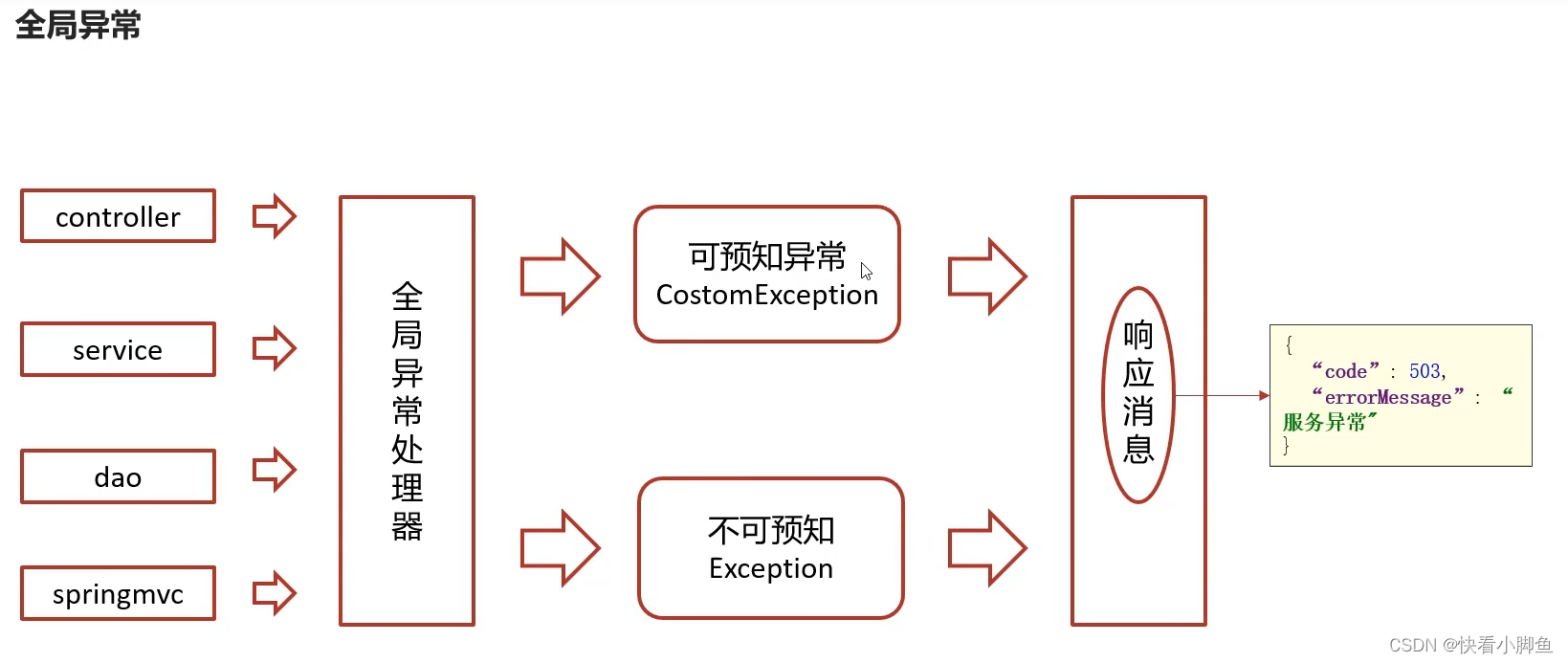
打开看看还是有花指令
解除后首先pass1是解maze,好像又是三维的

x是+25,也就是向下跳五层,注意是立体的
得到 passwd1: ddwwxxssxaxwwaasasyywwdd
接着往下看
有一个加密函数
IDA逆向常用宏定义_lodword-CSDN博客
unsigned __int64 __fastcall sub_C22(const char *a1, __int64 a2)
{
__int64 v2; // rax
char v3; // cc
int v4; // edx
int v5; // eax
int v6; // eax
int v7; // eax
int v9; // [rsp+14h] [rbp-24Ch]
int v10; // [rsp+18h] [rbp-248h]
int v11; // [rsp+1Ch] [rbp-244h]
int v12; // [rsp+20h] [rbp-240h]
int v13; // [rsp+24h] [rbp-23Ch]
int v14; // [rsp+28h] [rbp-238h]
int v15; // [rsp+2Ch] [rbp-234h]
const char *v16; // [rsp+48h] [rbp-218h]
int v17[130]; // [rsp+50h] [rbp-210h] BYREF
unsigned __int64 v18; // [rsp+258h] [rbp-8h]
v18 = __readfsqword(0x28u);
qmemcpy(v17, &unk_1740, 0x200uLL);
v10 = 3;
v9 = 0;
v12 = 0;
v13 = 0;
v14 = strlen(a1);
v16 = a1;
while ( 1 )
{
v15 = 0;
if ( v12 < v14 )
break;
LABEL_7:
if ( v12 >= v14 )
goto LABEL_8;
}
do
{
if ( a1[v12] != 25 )
break;
++v12;
++v15;
}
while ( v12 < v14 );
if ( v12 != v14 )
{
++v12;
goto LABEL_7;
}
LABEL_8:
v2 = 0LL;
while ( 1 )
{
v3 = (*(_DWORD *)v2 + 1 < 0) ^ __OFADD__(1, *(_DWORD *)v2) | (*(_DWORD *)v2 == -1);
++*(_DWORD *)v2;
if ( v3 )
break;
v10 -= v17[*v16] == 64;
v4 = v17[*v16] & 0x3F;
v2 = v4 | (unsigned int)(v9 << 6);
v9 = v4 | (v9 << 6);
LOBYTE(v2) = ++v11 == 4;
if ( v11 == 4 )
{
v11 = 0;
if ( v10 )
{
v5 = v13++;
v2 = v5 + a2;
*(_BYTE *)v2 = BYTE2(v9);
}
if ( v10 > 1 )
{
v6 = v13++;
v2 = v6 + a2;
*(_BYTE *)v2 = BYTE1(v9);
}
if ( v10 > 2 )
{
v7 = v13++;
v2 = v7 + a2;
*(_BYTE *)v2 = v9;
}
}
++v16;
--v14;
}
return __readfsqword(0x28u) ^ v18;
}
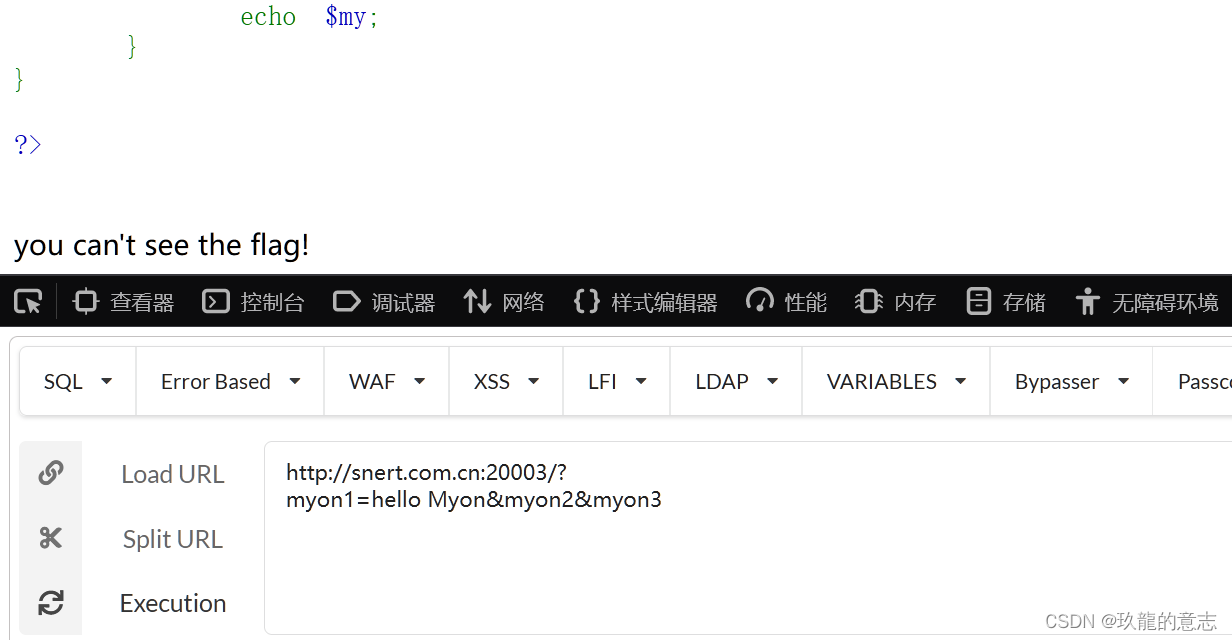
也就是将input2的每四位改成三位给v18,然后v18再与v8="sctf_9102"进行比较
v8有9位,可知input2有16位。(好像真的是base64)
提取出数据,写爆破脚本。(C快一些)
enc='sctf_9102'
for i in range(len(enc)):
print(hex(ord(enc[i]))[2:],end='')先改成字节。
#include <iostream>
using namespace std;
int main() {
int str[3] = { 0x736374,0x665f39,0x313032 };
int data[128] = {
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x3E, 0x7F, 0x7F, 0x7F, 0x3F,
0x34, 0x35, 0x36, 0x37, 0x38, 0x39, 0x3A, 0x3B,
0x3C, 0x3D, 0x7F, 0x7F, 0x7F, 0x40, 0x7F, 0x7F,
0x7F, 0x00, 0x01, 0x02, 0x03, 0x04, 0x05, 0x06,
0x07, 0x08, 0x09, 0x0A, 0x0B, 0x0C, 0x0D, 0x0E,
0x0F, 0x10, 0x11, 0x12, 0x13, 0x14, 0x15, 0x16,
0x17, 0x18, 0x19, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x1A, 0x1B, 0x1C, 0x1D, 0x1E, 0x1F, 0x20,
0x21, 0x22, 0x23, 0x24, 0x25, 0x26, 0x27, 0x28,
0x29, 0x2A, 0x2B, 0x2C, 0x2D, 0x2E, 0x2F, 0x30,
0x31, 0x32, 0x33, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F
};
int i0, i1, i2, i3, i4, final;
for (i0 = 0; i0 < 3; i0++) {
for (i1 = 32; i1 < 128; i1++) {
for (i2 = 32; i2 < 128; i2++) {
for (i3 = 32; i3 < 128; i3++) {
for (i4 = 32; i4 < 128; i4++) {
final = (((((data[i1] << 6) | data[i2]) << 6) | data[i3]) << 6) | data[i4];
//i5 = (((((data[i1] << 6) | data[i2]) << 6) | data[i3]) << 6) | data[i4];
if (final == str[i0]) {
printf("第%d组:%c%c%c%c\n", i0 + 1, i1, i2, i3, i4);
}
}
}
}
}
}
return 0;
}第1组:c2N0
第2组:Zl85
第3组:MS=y
第3组:MT=y
第3组:MTAy
第三组有多个解可以先动调来确定,是MTAY
第三部分:
__int64 __fastcall sub_FFA(char *a1)
{
int v2; // [rsp+18h] [rbp-158h]
int i; // [rsp+18h] [rbp-158h]
int v4; // [rsp+1Ch] [rbp-154h]
unsigned int v5; // [rsp+24h] [rbp-14Ch]
unsigned int v6; // [rsp+28h] [rbp-148h]
unsigned int v7; // [rsp+2Ch] [rbp-144h]
int v8[16]; // [rsp+30h] [rbp-140h]
int v9[16]; // [rsp+70h] [rbp-100h]
int v10[26]; // [rsp+B0h] [rbp-C0h]
unsigned int v11; // [rsp+118h] [rbp-58h]
unsigned int v12; // [rsp+11Ch] [rbp-54h]
unsigned int v13; // [rsp+120h] [rbp-50h]
unsigned int v14; // [rsp+124h] [rbp-4Ch]
unsigned __int64 v15; // [rsp+168h] [rbp-8h]
v15 = __readfsqword(0x28u);
v8[0] = 190;
v8[1] = 4;
v8[2] = 6;
v8[3] = 128;
v8[4] = 197;
v8[5] = 175;
v8[6] = 118;
v8[7] = 71;
v8[8] = 159;
v8[9] = 204;
v8[10] = 64;
v8[11] = 31;
v8[12] = 216;
v8[13] = 191;
v8[14] = 146;
v8[15] = 239;
v5 = (a1[6] << 8) | (a1[5] << 16) | (a1[4] << 24) | a1[7];
v6 = (a1[10] << 8) | (a1[9] << 16) | (a1[8] << 24) | a1[11];
v7 = (a1[14] << 8) | (a1[13] << 16) | (a1[12] << 24) | a1[15];
v4 = 0;
v2 = 4;
v10[0] = byteswap((a1[2] << 8) | (a1[1] << 16) | (*a1 << 24) | a1[3]);
v10[1] = byteswap(v5);
v10[2] = byteswap(v6);
v10[3] = byteswap(v7);
do
{
v10[v2] = sub_143B(v10[v4], v10[v4 + 1], v10[v4 + 2], v10[v4 + 3]);
++v4;
++v2;
}
while ( v2 <= 29 );
v9[0] = HIBYTE(v11);
v9[1] = BYTE2(v11);
v9[2] = BYTE1(v11);
v9[3] = v11;
v9[4] = HIBYTE(v12);
v9[5] = BYTE2(v12);
v9[6] = BYTE1(v12);
v9[7] = v12;
v9[8] = HIBYTE(v13);
v9[9] = BYTE2(v13);
v9[10] = BYTE1(v13);
v9[11] = v13;
v9[12] = HIBYTE(v14);
v9[13] = BYTE2(v14);
v9[14] = BYTE1(v14);
v9[15] = v14;
for ( i = 0; i <= 15; ++i )
{
if ( v9[i] != v8[i] )
return 0xFFFFFFFFLL;
}
return 1LL;
}它的v_output原始ida分析出来的是独立的变量,双击进去按下*调整为同一个数组,然后按下y定义为下图这样的变量(int v_output[32])


- 其中
__ROL4__是循环左移 - byte3、byte2、byte1分别表示获取第几个byte,hibyte表示获取最高位的byte
取输入值作为下标从表中取值再组合。(循环移位宏)循环左右移不同位之后再异或取值。最后一点位运算和宏还需要再研究研究。
说是对称加密,可以直接逆
#include"stdio.h"
#include"string.h"
#define ROL(x, r) (((x) << (r)) | ((x) >> (32 - (r))))
#define ROR(x, r) (((x) >> (r)) | ((x) << (32 - (r))))
unsigned int a[288] = {0x0D6, 0x90, 0x0E9, 0x0FE, 0x0CC, 0x0E1, 0x3D, 0x0B7, 0x16, 0x0B6, 0x14, 0x0C2, 0x28, 0x0FB, 0x2C, 0x5, 0x2B, 0x67, 0x9A, 0x76, 0x2A, 0x0BE, 0x4, 0x0C3, 0x0AA, 0x44, 0x13, 0x26, 0x49, 0x86, 0x6, 0x99, 0x9C, 0x42, 0x50, 0x0F4, 0x91, 0x0EF, 0x98, 0x7A, 0x33, 0x54, 0x0B, 0x43, 0x0ED, 0x0CF, 0x0AC, 0x62, 0x0E4, 0x0B3, 0x1C, 0x0A9, 0x0C9, 0x8, 0x0E8, 0x95, 0x80, 0x0DF, 0x94, 0x0FA, 0x75, 0x8F, 0x3F, 0x0A6, 0x47, 0x7, 0x0A7, 0x0FC, 0x0F3, 0x73, 0x17, 0x0BA, 0x83, 0x59, 0x3C, 0x19, 0x0E6, 0x85, 0x4F, 0x0A8, 0x68, 0x6B, 0x81, 0x0B2, 0x71, 0x64, 0x0DA, 0x8B, 0x0F8, 0x0EB, 0x0F, 0x4B, 0x70, 0x56, 0x9D, 0x35, 0x1E, 0x24, 0x0E, 0x5E, 0x63, 0x58, 0x0D1, 0x0A2, 0x25, 0x22, 0x7C, 0x3B, 0x1, 0x21, 0x78, 0x87, 0x0D4, 0x0, 0x46, 0x57, 0x9F, 0x0D3, 0x27, 0x52, 0x4C, 0x36, 0x2, 0x0E7, 0x0A0, 0x0C4, 0x0C8, 0x9E, 0x0EA, 0x0BF, 0x8A, 0x0D2, 0x40, 0x0C7, 0x38, 0x0B5, 0x0A3, 0x0F7, 0x0F2, 0x0CE, 0x0F9, 0x61, 0x15, 0x0A1, 0x0E0, 0x0AE, 0x5D, 0x0A4, 0x9B, 0x34, 0x1A, 0x55, 0x0AD, 0x93, 0x32, 0x30, 0x0F5, 0x8C, 0x0B1, 0x0E3, 0x1D, 0x0F6, 0x0E2, 0x2E, 0x82, 0x66, 0x0CA, 0x60, 0x0C0, 0x29, 0x23, 0x0AB, 0x0D, 0x53, 0x4E, 0x6F, 0x0D5, 0x0DB, 0x37, 0x45, 0x0DE, 0x0FD, 0x8E, 0x2F, 0x3, 0x0FF, 0x6A, 0x72, 0x6D, 0x6C, 0x5B, 0x51, 0x8D, 0x1B, 0x0AF, 0x92, 0x0BB, 0x0DD, 0x0BC, 0x7F, 0x11, 0x0D9, 0x5C, 0x41, 0x1F, 0x10, 0x5A, 0x0D8, 0x0A, 0x0C1, 0x31, 0x88, 0x0A5, 0x0CD, 0x7B, 0x0BD, 0x2D, 0x74, 0x0D0, 0x12, 0x0B8, 0x0E5, 0x0B4, 0x0B0, 0x89, 0x69, 0x97, 0x4A, 0x0C, 0x96, 0x77, 0x7E, 0x65, 0x0B9, 0x0F1, 0x9, 0x0C5, 0x6E, 0x0C6, 0x84, 0x18, 0x0F0, 0x7D, 0x0EC, 0x3A, 0x0DC, 0x4D, 0x20, 0x79, 0x0EE, 0x5F, 0x3E, 0x0D7, 0x0CB, 0x39, 0x48, 0x0C6, 0x0BA, 0x0B1, 0x0A3, 0x50, 0x33, 0x0AA, 0x56, 0x97, 0x91, 0x7D, 0x67, 0x0DC, 0x22, 0x70, 0x0B2, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0};
unsigned int foo2(unsigned int a1)
{
unsigned v1;
unsigned char byte[4];
byte[0] = a1&0xff;
byte[1] = (a1>>8)&0xff;
byte[2] = (a1>>16)&0xff;
byte[3] = (a1>>24)&0xff;
v1 = (a[byte[0]])|(a[byte[1]]<<8)|(a[byte[2]]<<16)|(a[byte[3]]<<24);
return ROL(v1,12)^ROL(v1,8)^ROR(v1,2)^ROR(v1,6);
}
unsigned int foo(unsigned int a1, unsigned int a2, unsigned int a3, unsigned int a4)
{
return a1 ^ foo2(a2^a3^a4);
}
int main()
{
unsigned int tmp[30] = {0};
unsigned int cipher[4] = {0xBE040680, 0xC5AF7647, 0x9FCC401F, 0xD8BF92EF};
memcpy(tmp+26,cipher,16);
for(int i = 25;i>=0;i--)
tmp[i] = foo(tmp[i+4],tmp[i+1],tmp[i+2],tmp[i+3]);
tmp[4] = 0;
printf("%sn",(char *)tmp);
return 0;
}
// fl4g_is_s0_ug1y!
![[<span style='color:red;'>SUCTF</span> <span style='color:red;'>2019</span>]CheckIn1](https://img-blog.csdnimg.cn/direct/433178fb00bc49a584b1f1d6f86c0ac7.png)
![BUUCTF---web---[<span style='color:red;'>SUCTF</span> <span style='color:red;'>2019</span>]CheckIn](https://img-blog.csdnimg.cn/direct/30d3b31d920e4182a16c3bbda6562c24.png)
![[<span style='color:red;'>SUCTF</span> <span style='color:red;'>2018</span>]MultiSQL MYSQL 预处理写](https://img-blog.csdnimg.cn/direct/faa88705bec049728e8381057531e9f1.png)
![web:[<span style='color:red;'>SUCTF</span> <span style='color:red;'>2019</span>]CheckIn(一句话木马,.user.ini)](https://img-blog.csdnimg.cn/direct/3c650b6641be489c83efcefa0f98c25d.png)
![练习 9 Web [<span style='color:red;'>SUCTF</span> <span style='color:red;'>2019</span>]CheckIn (未拿到flag)](https://img-blog.csdnimg.cn/direct/9f5bfe78261f45cf826ba6814ecc52f5.png)