一、前言
本次flask开发实战中,会用到2款防火墙配置文件,分别是华为和华三品牌防火墙;在解析处理数据之前,首先需要了解下配置文本中都有哪些数据,知己知彼才能愉快的玩耍呀。但实际生产中,防火墙规则数量比较多,且包含各类复杂异常数据,解析起来通常需要多轮调试才行。所以为了方便简化测试介绍,对其中华为配置文件模拟了几组有代表性的规则内容,作为基础数据,完成整个测试。
二、配置文件内容介绍
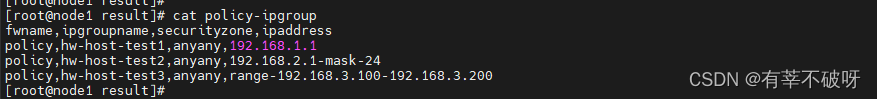
地址组信息格式样式:
#单地址的
ip address-set hw-host-test1 type object
address 0 192.168.1.1#带掩码的
ip address-set hw-host-test2 type object
address 0 192.168.2.1 mask 24#地址范围区间的
ip address-set hw-host-test3 type object
address 0 range 192.168.3.100 192.168.3.200
内容中,如果配置了地址组,address-set字段后带着是地址组名称,地址组下地址的形式就会分为单地址、连续地址区间范围、地址掩码几种情况
服务端口组格式样式:
#单端口的
ip service-set hw-port-test1 type object
service 0 protocol tcp source-port 0 to 65535 destination-port 80
# 连续端口的
ip service-set hw-port-test2 type object
service 0 protocol tcp source-port 0 to 65535 destination-port 20000 to 30000#多端口的
ip service-set hw-port-test3 type object
service 0 protocol tcp source-port 0 to 65535 destination-port 9300
service 1 protocol tcp source-port 0 to 65535 destination-port 9400
service 2 protocol tcp source-port 0 to 65535 destination-port 9500
rule策略规则格式样式:
###
rule name hw-rule-test1
source-zone IT
destination-zone TEST
source-address 10.10.10.10 mask 255.255.255.252
source-address address-set hw-host-test1
destination-address address-set hw-host-test2
service hw-port-test1
action permit
其中rule name表示规则名称、source-zone/dest-zone代表安全域(非必填字段)、source-address代表源地址(几种填写方式)、destination-address目标地址、service(端口组名称)
三、配置文件整体测试数据
#单地址的
ip address-set hw-host-test1 type object
address 0 192.168.1.1#带掩码的
ip address-set hw-host-test2 type object
address 0 192.168.2.1 mask 24#地址范围区间的
ip address-set hw-host-test3 type object
address 0 range 192.168.3.100 192.168.3.200#单端口的
ip service-set hw-port-test1 type object
service 0 protocol tcp source-port 0 to 65535 destination-port 80
# 连续端口的
ip service-set hw-port-test2 type object
service 0 protocol tcp source-port 0 to 65535 destination-port 20000 to 30000#多端口的
ip service-set hw-port-test3 type object
service 0 protocol tcp source-port 0 to 65535 destination-port 9300
service 1 protocol tcp source-port 0 to 65535 destination-port 9400
service 2 protocol tcp source-port 0 to 65535 destination-port 9500###规则
rule name hw-rule-test1
source-zone IT
destination-zone TEST
source-address 10.10.10.10 mask 255.255.255.252
source-address address-set hw-host-test1
destination-address address-set hw-host-test2
service hw-port-test1
action permitrule name hw-rule-test2
source-zone TEST
destination-zone IT
source-address 11.11.11.11 mask 255.255.255.255
source-address address-set hw-host-test3
destination-address address-set 22.22.22.22
service hw-port-test2
action permitrule name hw-rule-test3
source-zone TEST
destination-zone IT
source-address address-set hw-host-test2
destination-address address-set hw-host-test1
destination-address 11.11.11.0 mask 255.255.255.0
service hw-port-test3
action permit
拿到配置文件内容,弄清楚内容格式后,就可以开始考虑我们最终想解析成的数据是什么样式的,再根据这个要求编写具体解析程序,完成解析工作,这里只是简单展示测试数据内容,实际生产使用的防火墙规则情况会比这个复杂,但基本原理一样,只需要逐步分类清楚即可。



























![[Windows] Win11 常用快捷键](https://img-blog.csdnimg.cn/direct/92c43d82792e4bdabc115870e8324f06.jpeg#pic_center)