@(Nginx)
使用acme.sh 签发SSL证书
背景:
域名服务商: 阿里云
SSL证书使用场景: Nginx ,Tomcat
安装acme.sh
国内由于墙的问题,建议用gitee的镜像库克隆
mkdir /usr/local/acme
cd /usr/local/acme
git clone https://gitee.com/neilpang/acme.sh.git
cd acme.sh
./acme.sh --install -m 你有有效邮箱
安装成功后显示以下内容:
[Fri Jan 26 11:25:33 CST 2024] It is recommended to install socat first.
[Fri Jan 26 11:25:33 CST 2024] We use socat for standalone server if you use standalone mode.
[Fri Jan 26 11:25:33 CST 2024] If you don't use standalone mode, just ignore this warning.
[Fri Jan 26 11:25:33 CST 2024] Installing to /root/.acme.sh
[Fri Jan 26 11:25:33 CST 2024] Installed to /root/.acme.sh/acme.sh
[Fri Jan 26 11:25:33 CST 2024] Installing alias to '/root/.bashrc'
[Fri Jan 26 11:25:33 CST 2024] OK, Close and reopen your terminal to start using acme.sh
[Fri Jan 26 11:25:33 CST 2024] Installing alias to '/root/.cshrc'
[Fri Jan 26 11:25:34 CST 2024] Installing alias to '/root/.tcshrc'
[Fri Jan 26 11:25:34 CST 2024] Installing cron job
[Fri Jan 26 11:25:34 CST 2024] Good, bash is found, so change the shebang to use bash as preferred.
[Fri Jan 26 11:25:35 CST 2024] OK
[root@nginx-20200324 acme.sh]# source ~/.bashrc
指定默认的签发商
指定默认的签发商为:Let’s Encrypt
acme.sh --set-default-ca --server letsencrypt
修改后的响应
[Fri Jan 26 11:29:12 CST 2024] Changed default CA to: https://acme-v02.api.letsencrypt.org/directory
配置阿里云DNS API
在申请SSL证书时,需要验证对该域名的所有权,可以是通过指定域名对应的网站目录的方式,也可以通过指定DNS API的方式。建议使用DNS API方式比用本地服务方式更方便;
阿里云配置
申请DNS 所有权的RAM子账号
不建议使用主账号,风险较高。
操作流程如下:
访问:https://ram.console.aliyun.com/users
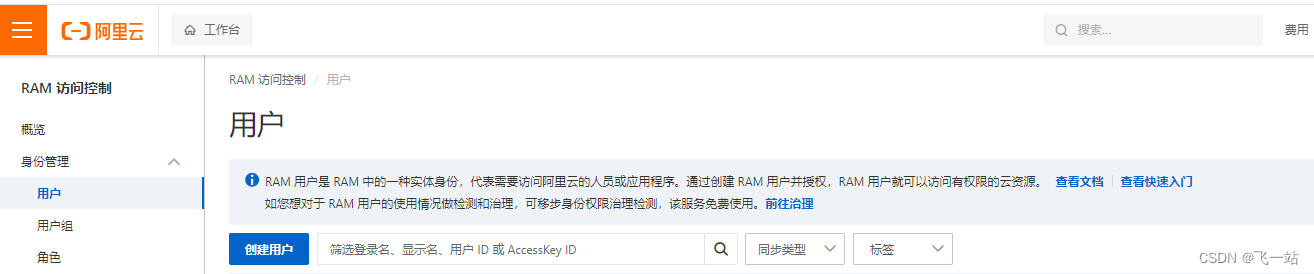
点击创建用户,填写登录用户名和显示名称,勾选Open API的调用访问

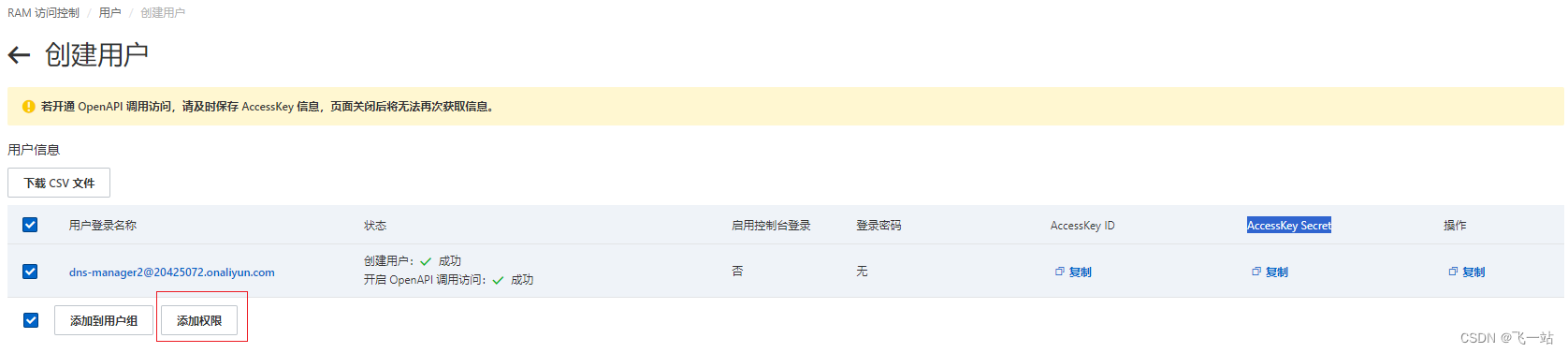
完成安全验证:

保存好用户的Access Key ID 和 AccessKey Secret

点击添加权限
选择指定资源,输入DNS 关键字过滤
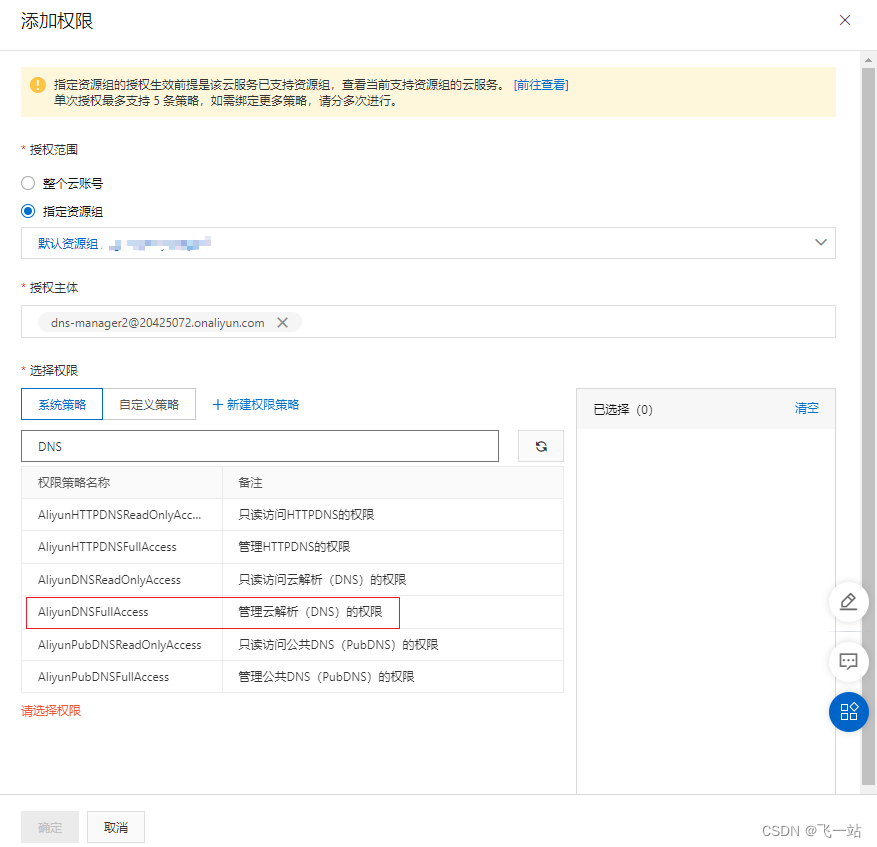
选择AliyunDNSFullAccess 管理云解析(DNS)的权限
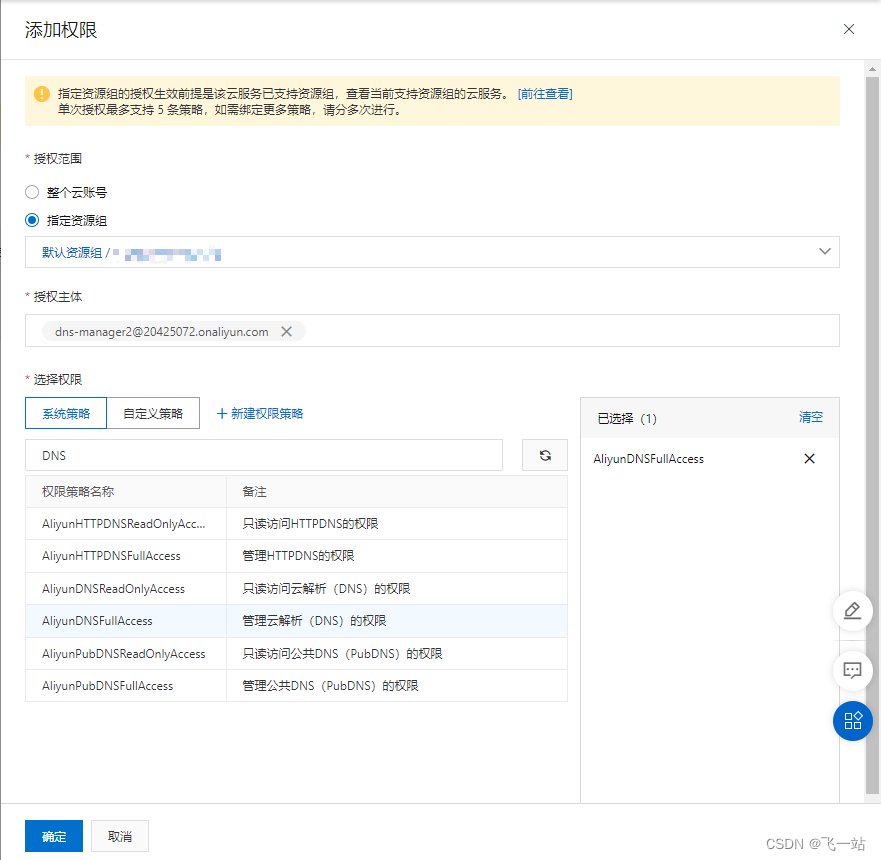
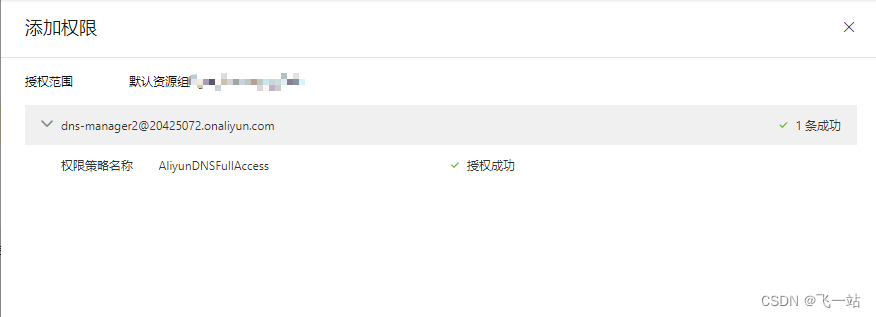
点击确定完成授权
在安装了acme.sh的服务设置阿里云API的环境变量
echo "export Ali_Key='前面保存的Access Key ID'" >> /etc/profile.d/acme_aliyun_env.sh
echo "export Ali_Secret='前面保存的AccessKey Secret'" >> /etc/profile.d/acme_aliyun_env.sh
# 使更改生效
source /etc/profile.d/acme_aliyun_env.sh
注意不要写成了
ALI_KEY和ALI_SECRET,大小写是区分的。具体可以查看/root/.acme.sh/dnsapi/dns_ali.sh这个脚本
检测环境变量是否设置好了
echo $Ali_Key
echo $Ali_Secret
如果正确显示了你设置的API Access Key ID 和 AccessKey Secret,则说明环境变量设置好了。
申请证书并安装到Nginx的证书目录下
申请证书
acme.sh --issue -d 需要申请证书的域名 --dns dns_ali
申请成功后的效果:
[Fri Jan 26 16:36:00 CST 2024] Using CA: https://acme-v02.api.letsencrypt.org/directory
[Fri Jan 26 16:36:00 CST 2024] Creating domain key
[Fri Jan 26 16:36:00 CST 2024] The domain key is here: /root/.acme.sh/需要申请证书的域名/需要申请证书的域名.key
[Fri Jan 26 16:36:00 CST 2024] Single domain='需要申请证书的域名'
[Fri Jan 26 16:36:00 CST 2024] Getting domain auth token for each domain
[Fri Jan 26 16:36:05 CST 2024] Getting webroot for domain='需要申请证书的域名'
[Fri Jan 26 16:36:05 CST 2024] Adding txt value: xxxxxxxxxx for domain: _acme-challenge.需要申请证书的域名
[Fri Jan 26 16:36:12 CST 2024] The txt record is added: Success.
[Fri Jan 26 16:36:12 CST 2024] Let's check each DNS record now. Sleep 20 seconds first.
[Fri Jan 26 16:36:33 CST 2024] You can use '--dnssleep' to disable public dns checks.
[Fri Jan 26 16:36:33 CST 2024] See: https://github.com/acmesh-official/acme.sh/wiki/dnscheck
[Fri Jan 26 16:36:33 CST 2024] Checking 需要申请证书的域名 for _acme-challenge.需要申请证书的域名
[Fri Jan 26 16:36:36 CST 2024] Domain 需要申请证书的域名 '_acme-challenge.需要申请证书的域名' success.
[Fri Jan 26 16:36:36 CST 2024] All success, let's return
[Fri Jan 26 16:36:36 CST 2024] Verifying: 需要申请证书的域名
[Fri Jan 26 16:36:38 CST 2024] Pending, The CA is processing your order, please just wait. (1/30)
[Fri Jan 26 16:36:42 CST 2024] Pending, The CA is processing your order, please just wait. (2/30)
[Fri Jan 26 16:36:47 CST 2024] Success
[Fri Jan 26 16:36:47 CST 2024] Removing DNS records.
[Fri Jan 26 16:36:47 CST 2024] Removing txt: xxxxxxxxxx for domain: _acme-challenge.需要申请证书的域名
[Fri Jan 26 16:36:55 CST 2024] Removed: Success
[Fri Jan 26 16:36:55 CST 2024] Verify finished, start to sign.
[Fri Jan 26 16:36:55 CST 2024] Lets finalize the order.
[Fri Jan 26 16:36:55 CST 2024] Le_OrderFinalize='https://acme-v02.api.letsencrypt.org/acme/finalize/xxxxxxxxxx '
[Fri Jan 26 16:36:58 CST 2024] Downloading cert.
[Fri Jan 26 16:36:58 CST 2024] Le_LinkCert='https://acme-v02.api.letsencrypt.org/acme/cert/xxxxxxxxxx '
[Fri Jan 26 16:36:59 CST 2024] Cert success.
-----BEGIN CERTIFICATE-----
xxxxxxxxxx =
-----END CERTIFICATE-----
[Fri Jan 26 16:36:59 CST 2024] Your cert is in: /root/.acme.sh/需要申请证书的域名/需要申请证书的域名.cer
[Fri Jan 26 16:36:59 CST 2024] Your cert key is in: /root/.acme.sh/需要申请证书的域名/需要申请证书的域名.key
[Fri Jan 26 16:36:59 CST 2024] The intermediate CA cert is in: /root/.acme.sh/需要申请证书的域名/ca.cer
[Fri Jan 26 16:36:59 CST 2024] And the full chain certs is there: /root/.acme.sh/需要申请证书的域名/fullchain.cer
安装证书
acme.sh --install-cert -d 需要申请证书的域名 \
--key-file /usr/share/nginx/cert/需要申请证书的域名.key \
--fullchain-file /usr/share/nginx/cert/需要申请证书的域名.crt \
--ca-file /usr/share/nginx/cert/需要申请证书的域名.ca.crt
当然这里还可以补一个nginx reload 的参数,但我个人觉得没必要,nginx统一reload会更好。
修改Nginx 的配置
#需要申请证书的域名HTTPS 配置
server{
#监听的443端口并开启SSL
listen 443 ssl;
#域名可以有多个,用空格隔开
server_name 需要申请证书的域名;
#acme.sh 安装的证书路径
ssl_certificate /usr/share/nginx/cert/需要申请证书的域名.crt;
ssl_certificate_key /usr/share/nginx/cert/需要申请证书的域名.key;
ssl_trusted_certificate /usr/share/nginx/cert/需要申请证书的域名.crt;
#缓存有效期
ssl_session_timeout 30m;
#可选的加密算法,顺序很重要,越靠前的优先级越高.
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:ECDHE:ECDH:AES:HIGH:!NULL:!aNULL:!MD5:!ADH:!RC4;
#安全链接可选的加密协议
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
ssl_prefer_server_ciphers on;
#根目录
location = / {
#直接访问根目录,不支持
return 404;
}
#代理app
location ^~ /app/ {
# 反向代理到 https://实际主机的域名:445 端口
proxy_pass https://实际主机的域名:445;
#传入ip
proxy_set_header Host $http_host;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Port $server_port;
# 支持cros
if ($request_method = 'OPTIONS') {
add_header Access-Control-Allow-Origin $http_origin;
add_header Access-Control-Allow-Credentials true;
add_header Access-Control-Allow-Headers *;
add_header Access-Control-Allow-Methods *;
add_header Access-Control-Max-Age 1728000;
return 204;
}
}
}
修改完配置后,验证配置有效后,重新加载配置或者重启Nginx
# 校验配置
nginx -t
# 重启
systemctl restart nginx
自动续签
acme.sh 安装好后,默认会启动一个每日定时任务去自动续签证书,并且会自动执行申请证书后的安装证书的命令。
# 显示自动续签的定时任务
crontab -l
#定时任务配置如下:
34 0 * * * "/root/.acme.sh"/acme.sh --cron --home "/root/.acme.sh" > /dev/null
备注
#手动执行自动续签的定时任务
acme.sh --cron -f
#开启自动升级(国内就别开了,是从github 升级的,拉不下来)
acme.sh --upgrade --auto-upgrade
#关闭自动升级
acme.sh --upgrade --auto-upgrade 0
如果需要pfx 的证书,可以使用以下命令转换,目前只能生成到默认目录,没找到参数修改这个输出目录。
#转换为pfx证书 并保存到/root/.acme.sh/申请证书的域名/申请证书的域名.pfx
acme.sh --toPkcs -d 申请证书的域名 --password 自定义的密码
# 显示当前申请的证书信息
acme.sh --list
一些异常
短时间内准对同一个域名频繁申请证书会触发下面这个异常:
Create new order error. Le_OrderFinalize not found. {
"type": "urn:ietf:params:acme:error:rateLimited",
"detail": "Error creating new order :: too many certificates (5) already issued for this exact set of domains in the last 168 hours: 申请证书的域名, retry after 2024-01-27T14:54:19Z: see https://letsencrypt.org/docs/duplicate-certificate-limit/",
"status": 429
}
使用本地模式,但有没有配置域名80端口对应本地Nginx目录时的异常:
[root@nginx-20200324 letsencrypt]# acme.sh --issue -d 申请证书的域名 -w /var/www/letsencrypt
[Fri Jan 26 13:32:21 CST 2024] Using CA: https://acme-v02.api.letsencrypt.org/directory
[Fri Jan 26 13:32:21 CST 2024] Creating domain key
[Fri Jan 26 13:32:21 CST 2024] The domain key is here: /root/.acme.sh/申请证书的域名/申请证书的域名.key
[Fri Jan 26 13:32:21 CST 2024] Single domain='申请证书的域名'
[Fri Jan 26 13:32:21 CST 2024] Getting domain auth token for each domain
[Fri Jan 26 13:32:26 CST 2024] Getting webroot for domain='申请证书的域名'
[Fri Jan 26 13:32:26 CST 2024] Verifying: 申请证书的域名
[Fri Jan 26 13:32:28 CST 2024] Pending, The CA is processing your order, please just wait. (1/30)
[Fri Jan 26 13:32:32 CST 2024] 申请证书的域名:Verify error:112.124.202.116: Invalid response from http://申请证书的域名/.well-known/acme-challenge/z__-xxxxxxxxx: 404
[Fri Jan 26 13:32:32 CST 2024] Please add '--debug' or '--log' to check more details.
[Fri Jan 26 13:32:32 CST 2024] See: https://github.com/acmesh-official/acme.sh/wiki/How-to-debug-acme.sh