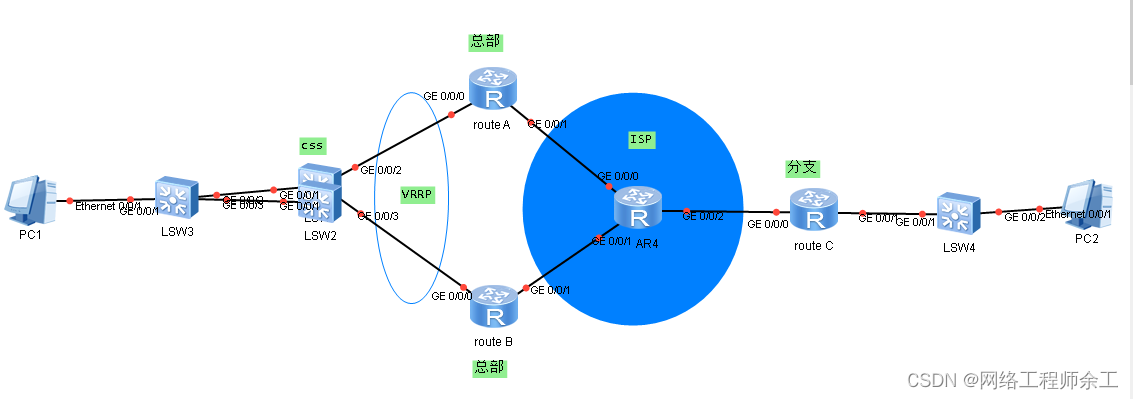
1、总部采用双AR出口冗余备份方式,保证设备级的可靠性。分支部署一台AR路由器做出口。
2、总部核心交换机采用两台交换机做堆叠,保证设备级的可靠性。
3、总部接入交换机与核心交换机之间以及核心交换机与出口路由器之间采用Eth-Trunk方式组网,保证链路级的可靠性。
4、总部每个部门业务划分到一个VLAN中,部门间的业务在核心交换机CORE上通过VLANIF三层互通。
5、总部核心交换机作为用户及服务器网关,部署DHCP Server为用户分配IP地址。
6、总部两个出口路由器之间部署VRRP,保证可靠性。
7、总部和分支之间通过Internet构建IPSec VPN进行私网互通,同时保证数据传输的安全性。
8、总两两台AR上各配一个vpn策略分别和分支对联,分支要配两个vpn方案,并同时引用到一个安全策略中,再在接口上调用策略。
重要地方:
1、vrrp关键配置
[RouterA] interface Eth-Trunk 1.100
[RouterA-Eth-Trunk1.100] vrrp vrid 1 virtual-ip 10.10.100.1
[RouterA-Eth-Trunk1.100] vrrp vrid 1 priority 150
[RouterA-Eth-Trunk1.100] vrrp vrid 1 track interface GigabitEthernet1/0/0 reduced 60
[RouterA-Eth-Trunk1.100] quit
//为了防止RouterA的上行链路中断的时候数据流发送至VRRP的Master以后不能继续上行,配置VRRP的状态和RouterA的上行口进行联动,保证RouterA上行链路中断的时候VRRP状态迅速倒换。
2、核心指向vrrp虚拟网关
[CORE] ip route-static 0.0.0.0 0.0.0.0 10.10.100.1
3、NAT配置
[RouterA] acl 3000
[RouterA-acl-adv-3000] rule 5 deny ip source 10.10.10.0 0.0.0.255 destination 10.10.200.0 0.0.0.255 //需要IPSec保护的数据流
[RouterA-acl-adv-3000] rule 10 deny ip source 10.10.20.0 0.0.0.255 destination 10.10.200.0 0.0.0.255
[RouterA-acl-adv-3000] rule 15 permit ip source 10.10.10.0 0.0.0.255 //需要进行NAT转换的数据流
[RouterA-acl-adv-3000] quit
//对于华为AR3200系列路由器,如果接口上同时配置了IPSec和NAT,则先执行NAT。所以为了避免把IPSec保护的数据流进行NAT转换,需要NAT引用的ACL规则deny掉需要IPSec保护的数据流,即对“IPSec感兴趣的数据流”做NAT豁免。
4、IKE对等体
[RouterA] ike peer vpn v1
[RouterA-ike-peer-vpn] pre-shared-key cipher huawei123
[RouterA-ike-peer-vpn] ike-proposal 5
[RouterA-ike-peer-vpn] dpd type periodic //配置周期性对等体存活检测
[RouterA-ike-peer-vpn] dpd idle-time 10 //设置对等体存活检测空闲时间为10秒
[RouterA-ike-peer-vpn] remote-address 203.10.1.2
[RouterA-ike-peer-vpn] quit
[RouterB] ike peer vpn v1
[RouterB-ike-peer-vpn] pre-shared-key cipher huawei123
[RouterB-ike-peer-vpn] ike-proposal 5
[RouterB-ike-peer-vpn] dpd type periodic
[RouterB-ike-peer-vpn] dpd idle-time 10
[RouterB-ike-peer-vpn] remote-address 203.10.1.2
[RouterB-ike-peer-vpn] quit
分支:
[RouterC] ike peer vpnr1 v1
[RouterC-ike-peer-vpnr1] pre-shared-key cipher huawei123
[RouterC-ike-peer-vpnr1] ike-proposal 5
[RouterC-ike-peer-vpnr1] dpd type periodic
[RouterC-ike-peer-vpnr1] dpd idle-time 10
[RouterC-ike-peer-vpnr1] remote-address 202.10.1.2
[RouterC-ike-peer-vpnr1] quit
[RouterC] ike peer vpnr2 v1
[RouterC-ike-peer-vpnr2] pre-shared-key cipher huawei123
[RouterC-ike-peer-vpnr2] ike-proposal 5
[RouterC-ike-peer-vpnr2] dpd type periodic
[RouterC-ike-peer-vpnr2] dpd idle-time 10
[RouterC-ike-peer-vpnr2] remote-address 202.10.2.2
[RouterC-ike-peer-vpnr2] quit
[RouterC] ipsec policy ipsec_vpn 10 isakmp
[RouterC-ipsec-policy-isakmp-ipsec_vpn-10] security acl 3001
[RouterC-ipsec-policy-isakmp-ipsec_vpn-10] ike-peer vpnr1
[RouterC-ipsec-policy-isakmp-ipsec_vpn-10] proposal tran1
[RouterC-ipsec-policy-isakmp-ipsec_vpn-10] quit
[RouterC] ipsec policy ipsec_vpn 20 isakmp
[RouterC-ipsec-policy-isakmp-ipsec_vpn-20] security acl 3001
[RouterC-ipsec-policy-isakmp-ipsec_vpn-20] ike-peer vpnr2
[RouterC-ipsec-policy-isakmp-ipsec_vpn-20] proposal tran1
[RouterC-ipsec-policy-isakmp-ipsec_vpn-20] quit
[RouterC] interface GigabitEthernet1/0/0
[RouterC-GigabitEthernet1/0/0] ipsec policy ipsec_vpn
[RouterC-GigabitEthernet1/0/0] quit





























![[C#]OpenCvSharp实现Yolov8 Face Landmarks 人脸关键点检测](https://img-blog.csdnimg.cn/direct/cc80c574c93a40bb9dd79cd2cb8527a3.jpeg)