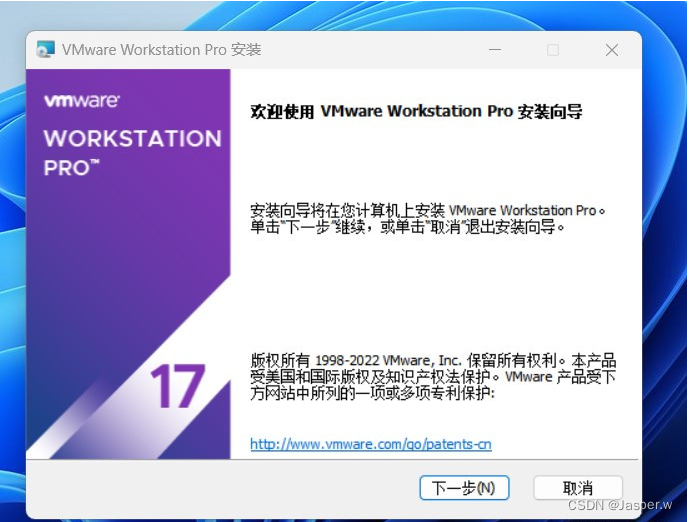
在 VMware 虚拟机上安装黑苹果(Hackintosh):免费 macOS ISO 镜像下载及安装教程
当涉及在 VMware 虚拟机上安装黑苹果(Hackintosh)时,有两种主要方法:
- 使用
macOS iso镜像安装。 - 使用
OpenCore作引导程序安装。
本文重点介绍使用 macOS ISO 黑苹果镜像的安装方法,并提供免费的 macOS Monterey (12.7) 系统镜像资源下载链接。
从设置 VMware 到安装过程,一步步指导安装黑苹果,让你轻松体验 macOS 虚拟化环境。
OpenCore 的使用方式,请参考:https://dortania.github.io/OpenCore-Install-Guide/
解锁工具 csdn:
https://download.csdn.net/download/cheungxiongwei/88639281?spm=1001.2014.3001.5503
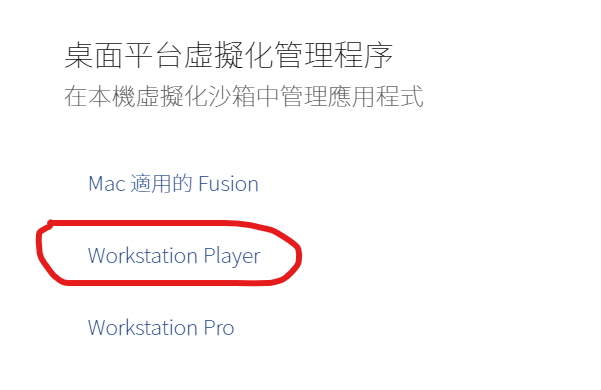
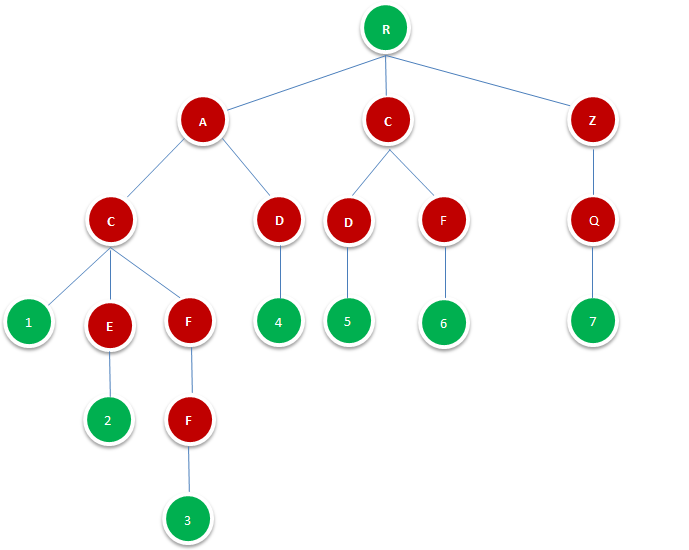
VMware 虚拟机解锁 macOS 安装选项
Monterey (12.7) 镜像资源下载:zip压缩分卷合集,全部下载下来,解压即可。
注意:还有一个关键 Monterey.zip 文件,在审核中,审核通过后放出。
https://download.csdn.net/download/cheungxiongwei/88639037?spm=1001.2014.3001.5503
https://download.csdn.net/download/cheungxiongwei/88639076?spm=1001.2014.3001.5503
https://download.csdn.net/download/cheungxiongwei/88639196?spm=1001.2014.3001.5503
https://download.csdn.net/download/cheungxiongwei/88639202?spm=1001.2014.3001.5503
https://download.csdn.net/download/cheungxiongwei/88639210?spm=1001.2014.3001.5503
https://download.csdn.net/download/cheungxiongwei/88639215?spm=1001.2014.3001.5503
https://download.csdn.net/download/cheungxiongwei/88639220?spm=1001.2014.3001.5503
https://download.csdn.net/download/cheungxiongwei/88639227?spm=1001.2014.3001.5503
https://download.csdn.net/download/cheungxiongwei/88639234?spm=1001.2014.3001.5503
https://download.csdn.net/download/cheungxiongwei/88639253?spm=1001.2014.3001.5503
https://download.csdn.net/download/cheungxiongwei/88639260?spm=1001.2014.3001.5503
https://download.csdn.net/download/cheungxiongwei/88639270?spm=1001.2014.3001.5503
VMware macOS

为了让 VMware 可以创建 macOS 虚拟机,需要下载 unlock.exe 工具, 并以管理员权限运行 unlock.exe 工具,给 VMware 打上 macOS 补丁。
下载地址:从 https://github.com/DrDonk/unlocker 下载 unlocker 工具。

unlock.exe 工具输出内容如下:
Unlocker 4.2.7 for VMware Workstation/Player
============================================
VMware is installed at: C:\Program Files (x86)\VMware\VMware Workstation\
VMware version: 20800274
Stopping VMware services and tasks...
Stopping service VMUSBArbService
Stopping service VMAuthdService
Stopping service VmwareAutostartService
Stopping task vmware-tray.exe
Installing unlock patches
Patching...
Patching C:\Program Files (x86)\VMware\VMware Workstation\vmwarebase.dll
C:\Program Files (x86)\VMware\VMware Workstation\vmwarebase.dll -> C:\Users\root\Downloads\unlocker427\backup\17.0.0.20800274\vmwarebase.dll
Flag patched @ offset: 0x004e85e0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e8620 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e8660 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e86a0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e86e0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e8720 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e8760 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e87a0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e87e0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e8820 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e8860 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e88a0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e88e0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e8920 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e8960 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e89a0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e89e0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x004e8a20 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e1a0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e1e0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e220 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e260 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e2a0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e2e0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e320 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e360 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e3a0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e3e0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e420 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e460 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e4a0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e4e0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e520 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e560 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e5a0 Flag: 0x3e -> 0x3f
Flag patched @ offset: 0x0059e5e0 Flag: 0x3e -> 0x3f
Patched 36 flags
Patching C:\Program Files (x86)\VMware\VMware Workstation\x64\vmware-vmx.exe
C:\Program Files (x86)\VMware\VMware Workstation\x64\vmware-vmx.exe -> C:\Users\root\Downloads\unlocker427\backup\17.0.0.20800274\vmware-vmx.exe
appleSMCTableV0 (smc.version = '0')
File Offset : 0x00cd6300
Keys Address : 0x140cd7b20
Public Keys : 0x00f0/0240
Private Keys : 0x00f2/0242
Table Offset : 0x00cd6320
Getting +LKS:
0x00cd6368 +LKS 01 flag 0x90 0x1401f8ec0 07
Patching OSK0:
0x00cda6a0 OSK0 32 ch8* 0x80 0x1401f8f40 0000000000000000000000000000000000000000000000000000000000000000
0x00cda6a0 OSK0 32 ch8* 0x80 0x1401f8ec0 6f757268617264776f726b62797468657365776f72647367756172646564706c
Patching OSK1:
0x00cda6e8 OSK1 32 ch8* 0x80 0x1401f8f40 0000000000000000000000000000000000000000000000000000000000000000
0x00cda6e8 OSK1 32 ch8* 0x80 0x1401f8ec0 65617365646f6e74737465616c2863294170706c65436f6d7075746572496e63
appleSMCTableV1 (smc.version = '1')
File Offset : 0x00cda730
Keys Address : 0x140cdbf50
Public Keys : 0x01b0/0432
Private Keys : 0x01b4/0436
Table Offset : 0x00cda750
Getting +LKS:
0x00cda828 +LKS 01 flag 0x90 0x1401f8ec0 01
Patching OSK0:
0x00ce2160 OSK0 32 ch8* 0x90 0x1401f8f40 0000000000000000000000000000000000000000000000000000000000000000
0x00ce2160 OSK0 32 ch8* 0x90 0x1401f8ec0 6f757268617264776f726b62797468657365776f72647367756172646564706c
Patching OSK1:
0x00ce21a8 OSK1 32 ch8* 0x90 0x1401f8f40 0000000000000000000000000000000000000000000000000000000000000000
0x00ce21a8 OSK1 32 ch8* 0x90 0x1401f8ec0 65617365646f6e74737465616c2863294170706c65436f6d7075746572496e63
Patching C:\Program Files (x86)\VMware\VMware Workstation\x64\vmware-vmx-debug.exe
C:\Program Files (x86)\VMware\VMware Workstation\x64\vmware-vmx-debug.exe -> C:\Users\root\Downloads\unlocker427\backup\17.0.0.20800274\vmware-vmx-debug.exe
appleSMCTableV0 (smc.version = '0')
File Offset : 0x00f99010
Keys Address : 0x140f9ac30
Public Keys : 0x00f0/0240
Private Keys : 0x00f2/0242
Table Offset : 0x00f99030
Getting +LKS:
0x00f99078 +LKS 01 flag 0x90 0x140273520 07
Patching OSK0:
0x00f9d3b0 OSK0 32 ch8* 0x80 0x1402736f0 0000000000000000000000000000000000000000000000000000000000000000
0x00f9d3b0 OSK0 32 ch8* 0x80 0x140273520 6f757268617264776f726b62797468657365776f72647367756172646564706c
Patching OSK1:
0x00f9d3f8 OSK1 32 ch8* 0x80 0x1402736f0 0000000000000000000000000000000000000000000000000000000000000000
0x00f9d3f8 OSK1 32 ch8* 0x80 0x140273520 65617365646f6e74737465616c2863294170706c65436f6d7075746572496e63
appleSMCTableV1 (smc.version = '1')
File Offset : 0x00f9d440
Keys Address : 0x140f9f060
Public Keys : 0x01b0/0432
Private Keys : 0x01b4/0436
Table Offset : 0x00f9d460
Getting +LKS:
0x00f9d538 +LKS 01 flag 0x90 0x140273520 01
Patching OSK0:
0x00fa4e70 OSK0 32 ch8* 0x90 0x1402736f0 0000000000000000000000000000000000000000000000000000000000000000
0x00fa4e70 OSK0 32 ch8* 0x90 0x140273520 6f757268617264776f726b62797468657365776f72647367756172646564706c
Patching OSK1:
0x00fa4eb8 OSK1 32 ch8* 0x90 0x1402736f0 0000000000000000000000000000000000000000000000000000000000000000
0x00fa4eb8 OSK1 32 ch8* 0x90 0x140273520 65617365646f6e74737465616c2863294170706c65436f6d7075746572496e63
Patching C:\Program Files (x86)\VMware\VMware Workstation\x64\vmware-vmx-stats.exe
C:\Program Files (x86)\VMware\VMware Workstation\x64\vmware-vmx-stats.exe -> C:\Users\root\Downloads\unlocker427\backup\17.0.0.20800274\vmware-vmx-stats.exe
appleSMCTableV0 (smc.version = '0')
File Offset : 0x00d32a30
Keys Address : 0x140d34a50
Public Keys : 0x00f0/0240
Private Keys : 0x00f2/0242
Table Offset : 0x00d32a50
Getting +LKS:
0x00d32a98 +LKS 01 flag 0x90 0x140208340 07
Patching OSK0:
0x00d36dd0 OSK0 32 ch8* 0x80 0x1402083c0 0000000000000000000000000000000000000000000000000000000000000000
0x00d36dd0 OSK0 32 ch8* 0x80 0x140208340 6f757268617264776f726b62797468657365776f72647367756172646564706c
Patching OSK1:
0x00d36e18 OSK1 32 ch8* 0x80 0x1402083c0 0000000000000000000000000000000000000000000000000000000000000000
0x00d36e18 OSK1 32 ch8* 0x80 0x140208340 65617365646f6e74737465616c2863294170706c65436f6d7075746572496e63
appleSMCTableV1 (smc.version = '1')
File Offset : 0x00d36e60
Keys Address : 0x140d38e80
Public Keys : 0x01b0/0432
Private Keys : 0x01b4/0436
Table Offset : 0x00d36e80
Getting +LKS:
0x00d36f58 +LKS 01 flag 0x90 0x140208340 01
Patching OSK0:
0x00d3e890 OSK0 32 ch8* 0x90 0x1402083c0 0000000000000000000000000000000000000000000000000000000000000000
0x00d3e890 OSK0 32 ch8* 0x90 0x140208340 6f757268617264776f726b62797468657365776f72647367756172646564706c
Patching OSK1:
0x00d3e8d8 OSK1 32 ch8* 0x90 0x1402083c0 0000000000000000000000000000000000000000000000000000000000000000
0x00d3e8d8 OSK1 32 ch8* 0x90 0x140208340 65617365646f6e74737465616c2863294170706c65436f6d7075746572496e63
Patching Complete!
Copying VMware Tools...
C:\Users\root\Downloads\unlocker427\iso\darwinPre15.iso -> C:\Program Files (x86)\VMware\VMware Workstation\darwinPre15.iso
C:\Users\root\Downloads\unlocker427\iso\darwin.iso -> C:\Program Files (x86)\VMware\VMware Workstation\darwin.iso
Starting VMware services and tasks...
Starting service VMAuthdService
Starting service VMUSBArbService
Starting service VmwareAutostartService
Starting task C:\Program Files (x86)\VMware\VMware Workstation\vmware-tray.exe
Press Enter key to continue...
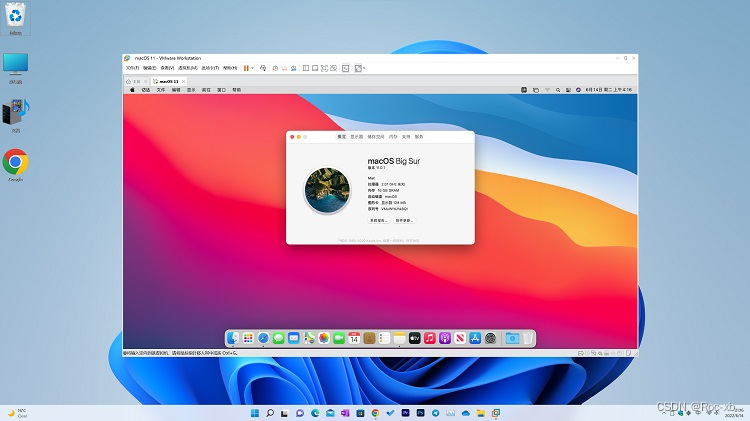
现在可以打开 VMware 虚拟机软件,就可以创建 macOS 虚拟机了。

使用 macOS iso 系统镜像安装
在执行该步骤之前,确保 VMware 已解锁成功。
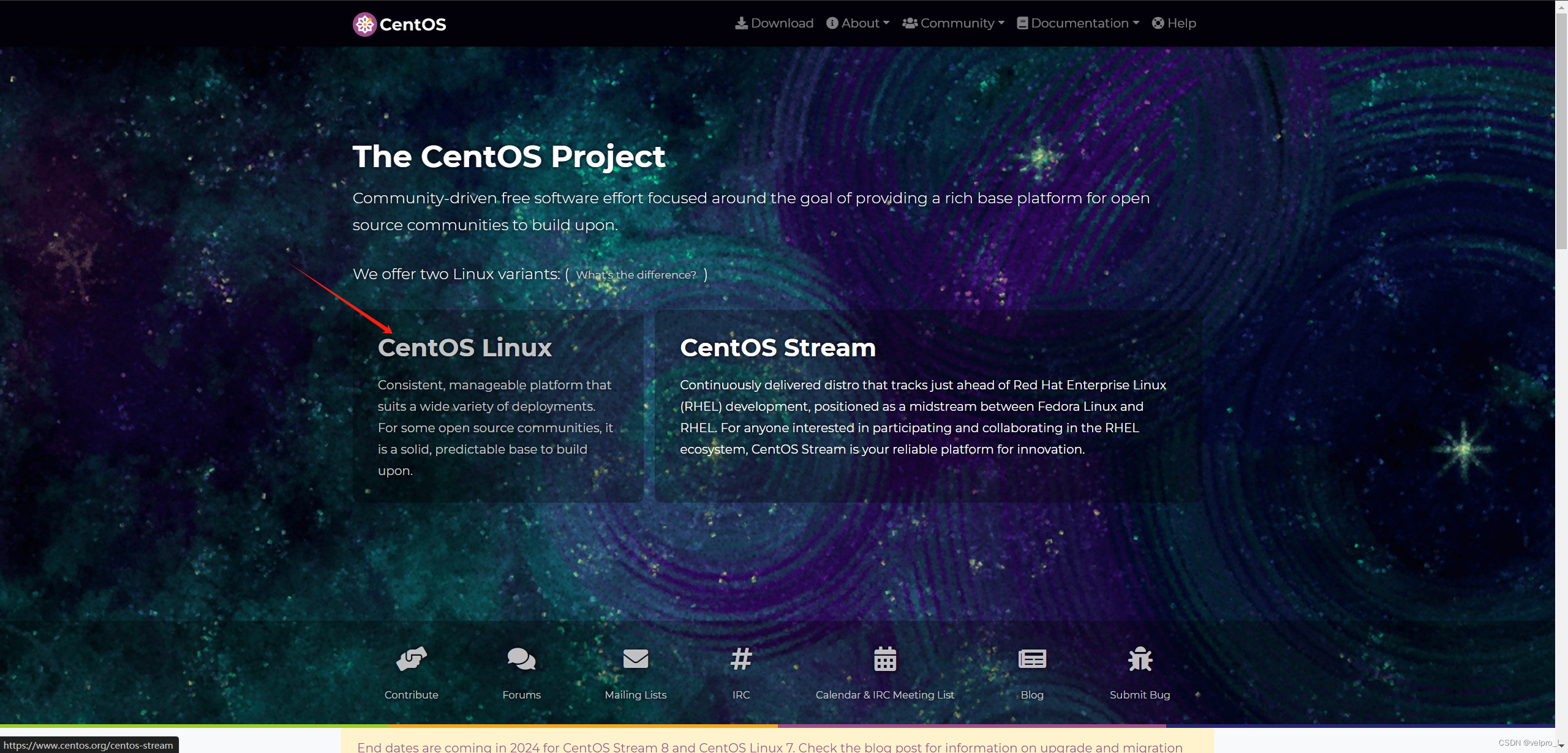
下载 macOS 系统镜像
创建 macOS 虚拟机
这里选择 macOS 12

选择 macOS Monterey (12.7) 镜像,提示以下内容:

这是因为你使用的是 AMD CPU (注:intel CPU 直接安装就行,不用添加下面内容,当然可以也添加产品型号),此时关闭虚拟机,然后编辑 macOS 12 虚拟机 macOS 12.vmx 配置文件。
为了在 AMD CPU 上安装该系统,需要在文件末尾添加以下内容:
cpuid.0.eax = "0000:0000:0000:0000:0000:0000:0000:1011"
cpuid.0.ebx = "0111:0101:0110:1110:0110:0101:0100:0111"
cpuid.0.ecx = "0110:1100:0110:0101:0111:0100:0110:1110"
cpuid.0.edx = "0100:1001:0110:0101:0110:1110:0110:1001"
cpuid.1.eax = "0000:0000:0000:0001:0000:0110:0111:0001"
cpuid.1.ebx = "0000:0010:0000:0001:0000:1000:0000:0000"
cpuid.1.ecx = "1000:0010:1001:1000:0010:0010:0000:0011"
cpuid.1.edx = "0000:0111:1000:1011:1111:1011:1111:1111"
vhv.enable = "FALSE"
vpmc.enable = "FALSE"
vvtd.enable = "FALSE"
Note: 确保 vmx 配置文件中,不存在重复的键
[非必须选项] 当然也可以继续添加以下内容,给系统镜像自定义产品型号,例如 iMac 、MacBookPro 等。
iMac
hw.model = "iMac20,2"
board-id = "Mac-AF89B6D9451A490B"
MacBookPro
hw.model = "MacBookPro16,4"
board-id = "Mac-A61BADE1FDAD7B05"
具体对应关系表格如下:
MacBook Pro
| Model Identifier | Machine Model | Board ID |
|---|---|---|
| MacBookPro16,4 | (16-inch, AMD Radeon Pro 5600M) | Mac-A61BADE1FDAD7B05 |
| MacBookPro16,3 | (13-inch 2020) | Mac-5F9802EFE386AA28 |
| MacBookPro16,2 | (13-inch 2020) | Mac-E7203C0F68AA0004 |
iMac
| Model Identifier | Machine Model | Board ID |
|---|---|---|
| iMac20,2 | (Retina 5K, 27-Inch, 2020) | Mac-AF89B6D9451A490B |



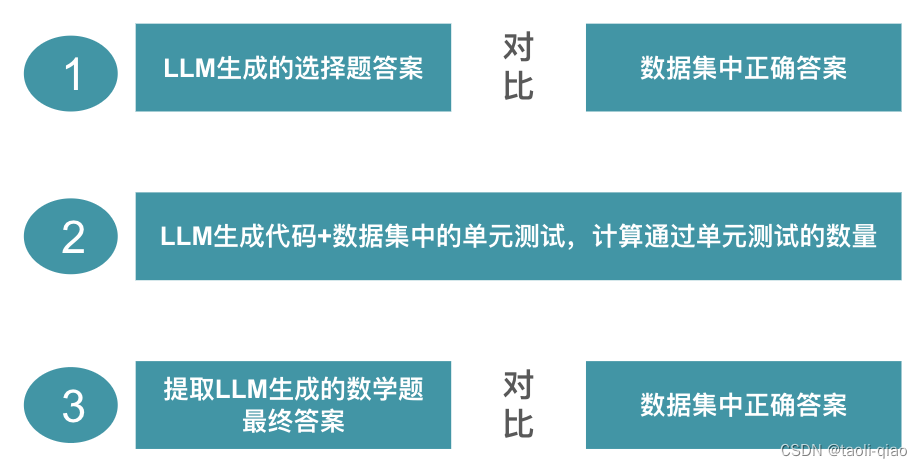
使用 OpenCore 做引导程序安装

上图 macOS Sonoma 14.1 是使用 OpenCore 的方式这些安装.
安装时需要注意以下问题:
创建虚拟机时,选择使用现有虚拟磁盘,然后选择 OpenCore 核心引导文件。

确保 OpenCore 引导程序文件使用 SATA 0:0 启动。
然后添加第二个硬盘,添加 mac iso 系统镜像,启动虚拟机安装即可。